Strategic Balance: Mastering Exploration and Exploitation in Machine Learning for Efficient DBTL Cycles in Biomedicine
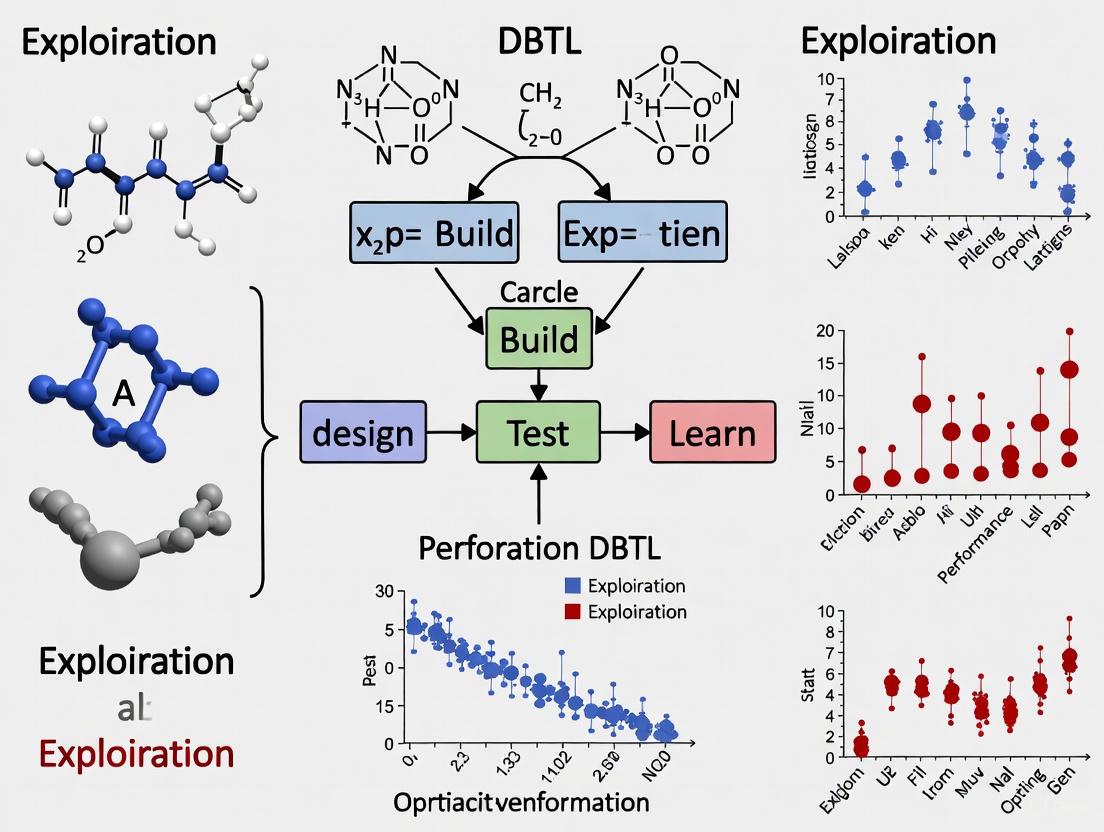
This article provides a comprehensive guide for researchers and drug development professionals on integrating the exploration-exploitation dilemma from machine learning into Design-Build-Test-Learn (DBTL) cycles.
Strategic Balance: Mastering Exploration and Exploitation in Machine Learning for Efficient DBTL Cycles in Biomedicine
Abstract
This article provides a comprehensive guide for researchers and drug development professionals on integrating the exploration-exploitation dilemma from machine learning into Design-Build-Test-Learn (DBTL) cycles. It covers the foundational principles of directed and random exploration, details methodological implementations like Bayesian optimization and multi-armed bandit strategies within metabolic engineering workflows, and addresses common troubleshooting challenges such as data scarcity and algorithmic stagnation. Furthermore, it presents validation frameworks and comparative analyses of machine learning models, offering actionable insights for optimizing bioprocess development and accelerating therapeutic discovery.
The Core Dilemma: Understanding Exploration and Exploitation in Biological Systems
Defining the Exploration-Exploitation Trade-Off in Machine Learning and Biology
Frequently Asked Questions
What is the exploration-exploitation trade-off? The exploration-exploitation dilemma describes the fundamental conflict between choosing the best-known option based on current knowledge (exploitation) and trying new, uncertain options that might lead to better outcomes in the future (exploration). Finding the optimal balance is crucial for maximizing long-term benefits in decision-making processes [1].
Why is this trade-off important in machine learning and biology? In machine learning, particularly in Reinforcement Learning (RL), an agent must balance exploring the environment to learn more about it with exploiting its current knowledge to maximize rewards [1] [2]. In biology, this trade-off is fundamental to survival, governing behaviors from animal foraging for food to human memory search and social innovation [3]. Both fields face the same core problem: the need to make decisions with incomplete information.
What are common challenges when balancing exploration and exploitation? Several problems can make effective exploration difficult [1]:
- Sparse Rewards: When rewards occur infrequently, an agent may not persist in exploring.
- Deceptive Rewards: Immediate small rewards can lure an agent away from actions that yield larger, delayed rewards.
- Noisy TV Problem: An agent can become trapped exploring parts of the environment that generate unpredictable or random feedback.
My agent is not performing optimally. Is it over-exploring or over-exploiting? Diagnosing this issue requires examining your agent's behavior and the environment.
- Signs of over-exploitation: The agent converges quickly to a sub-optimal policy, seems to "get stuck" using the same actions, and fails to discover higher-reward strategies. This is like a gambler only ever playing the same slot machine without testing others [4] [5].
- Signs of over-exploration: The agent behaves erratically, fails to consistently choose known high-reward actions, and shows slow or no improvement in average reward over time. This is like a gambler constantly switching machines without ever settling on the best one [4] [6].
Troubleshooting Guides
Guide 1: Implementing Core Balancing Strategies
This guide outlines standard methodologies for managing the exploration-exploitation trade-off.
Protocol: Epsilon-Greedy Strategy This is a simple and widely used method where the agent primarily exploits but randomly explores with a small probability [1] [4] [2].
- Initialize: For each action, initialize the estimated value (e.g., to zero) and a counter for how many times it has been chosen.
- Loop for each decision step
t:- With probability
1 - ε, choose the action with the highest estimated value (Exploitation). - With probability
ε, choose a random action (Exploration).
- With probability
- Update: After taking action
aand receiving rewardR, update the action's estimated valueQ(a):Q(a) = Q(a) + (1/N(a)) * (R - Q(a))whereN(a)is the number of times actionahas been chosen [4].
Protocol: Upper Confidence Bound (UCB) Strategy This method uses uncertainty to balance exploration and exploitation mathematically [1] [4].
- Initialize: For each action
a, initializeN(a) = 0andQ(a) = 0. - Loop for each decision step
t = 1, 2, ...:- For each action
a, calculate its UCB score:a_t = argmax_a [ Q(a) + sqrt( (2 * ln t) / N(a) ) ] - Select the action
a_twith the highest score. TheQ(a)term promotes exploitation, while the square root term promotes exploration of less-tried actions [4].
- For each action
- Update: Update
Q(a_t)andN(a_t)after receiving the reward.
Comparison of Core Strategies
| Strategy | Core Mechanism | Pros | Cons |
|---|---|---|---|
| Epsilon-Greedy [4] [2] | Fixed probability (ε) of taking a random action. |
Simple to implement and understand. | Does not prioritize promising explorations; requires tuning of ε. |
| Upper Confidence Bound (UCB) [1] [4] | Optimism in the face of uncertainty; selects actions with high upper confidence bounds. | Efficient, theoretically grounded, and automatically reduces exploration over time. | Can be more complex to implement than epsilon-greedy. |
| Thompson Sampling [1] [4] | Bayesian approach; samples a model from a posterior distribution and acts optimally according to the sample. | Strong empirical and theoretical performance. | Requires maintaining a posterior distribution, which can be computationally heavy. |
Guide 2: Addressing Advanced Scenarios
Scenario: Poor performance in environments with sparse or deceptive rewards. Standard methods like epsilon-greedy can fail in complex environments. The solution is to use intrinsic motivation, where the agent gives itself an internal reward for exploring novel or uncertain states [1].
Protocol: Intrinsic Curiosity Module (ICM) This method trains a model to predict the consequence of the agent's actions and uses the prediction error as an intrinsic reward signal [1].
- Featurize State: Use a neural network
φto encode the current states_tand next states_{t+1}into features. - Train Inverse Dynamics Model: Train a model
gthat predicts the actiona_ttaken given the feature representationsφ(s_t)andφ(s_{t+1}). - Train Forward Dynamics Model: Train a model
fthat predicts the next state's featuresφ(s_{t+1})givenφ(s_t)anda_t. - Calculate Intrinsic Reward: The intrinsic reward
r_t^iis the error between the predicted and actual next-state features:r_t^i = || f(φ(s_t), a_t) - φ(s_{t+1}) ||^2. - Combine Rewards: The total reward for the agent is
r_total = r_t^e + β * r_t^i, wherer_t^eis the external reward from the environment andβis a scaling factor [1].
Diagram: Intrinsic Curiosity Module Workflow
Guide 3: Adopting Novel Research Perspectives
Emerging research suggests the traditional trade-off can be re-examined. One novel approach involves analyzing the agent's behavior in its hidden state space, proposing that exploration and exploitation can be decoupled and enhanced simultaneously [7].
Protocol: Cognitive Consistency (CoCo) Framework This framework rethinks the trade-off by conducting "pessimistic exploration" and "optimistic exploitation" [8].
- Optimistic Exploitation (Self-Imitating Distribution Correction): Prioritize learning from high-performing trajectories. The policy is updated to reinforce actions that have led to high rewards, focusing computational effort on promising strategies rather than confirming the inadequacy of poor ones [8].
- Pessimistic Exploration (Inconsistency Minimization): Guide exploration conservatively around the currently learned effective policy. This is achieved by introducing a loss function that minimizes the discrepancy between the agent's current policy and a target, encouraging stable and consistent learning without wildly diverging into unknown states [8].
- Integration: These two components are integrated into a single objective function for training, often using a reweighted, uniformly sampled loss [8].
Diagram: CoCo Framework Principles
The Scientist's Toolkit: Research Reagents & Solutions
This table details key algorithmic components and their functions for studying the exploration-exploitation trade-off.
| Item | Function / Definition | Application Context |
|---|---|---|
| Effective Rank (ER) [7] | A quantity measuring the exploration capacity in the semantically rich hidden-state space of a model. | Used in advanced analyses (e.g., VERL method) to move beyond token-level metrics and understand exploration in latent representations. |
| Effective Rank Acceleration (ERA) [7] | The second-order derivative of the Effective Rank, capturing the dynamics of exploitation. | Used as a predictive meta-controller to prospectively shape the RL advantage function, reinforcing gains. |
| NoisyNet [1] | A method where parameters of a neural network are perturbed with noise, making the exploration state-dependent and adaptive. | Provides a more structured exploration strategy compared to simple epsilon-greedy, integrated directly into the policy network. |
| Intrinsic Reward Signal [1] | An internally generated reward (e.g., based on prediction error or state novelty) that encourages the agent to explore. | Critical for environments with sparse or no external rewards, such as hard-exploration video games or robotics in uncharted terrain. |
| Forward Dynamics Model [1] | A function that predicts the next state of the environment given the current state and action. | Core to many intrinsic motivation algorithms like ICM; the prediction error drives curiosity. |
Quantitative Results from Recent Research
| Method / Framework | Key Metric Improvement | Test Environment / Benchmark |
|---|---|---|
| Velocity-Exploiting Rank-Learning (VERL) [7] | Up to 21.4% absolute accuracy improvement | Gaokao 2024 dataset [7] |
| Cognitive Consistency (CoCo) [8] | Substantial improvement in sample efficiency and performance | Mujoco tasks, Atari games [8] |
Technical Support Center: Troubleshooting the ML-DBTL Cycle
This support center provides targeted guidance for researchers navigating the Design-Build-Test-Learn (DBTL) cycle, particularly when integrating machine learning to balance exploration and exploitation. Below are common challenges and their solutions, framed within this core research thesis.
Troubleshooting Guides
1. Guide: Poor Strain Performance Despite High In-Silico Predictions
- Issue or Problem Statement: A microbial strain, designed for metabolite production (e.g., dopamine), shows low yield in vivo even though ML models predicted high performance [9] [10].
- Symptoms or Error Indicators: Final product titer is significantly lower than expected; model prediction accuracy is poor for new genetic designs.
- Environment Details: E. coli production host; high-throughput screening data; ML model trained on historical RBS library data [10].
- Possible Causes:
- Over-exploitation: The ML model is overfitting to a narrow region of the genetic design space it is confident about, missing potentially better, unexplored designs [10].
- Context Dependence: The model was trained on data from a different genetic background or environmental condition, reducing its predictive power for new contexts [9].
- Inadequate Training Data: The initial dataset used to train the ML model is too small or lacks diversity, leading to poor generalization [10].
- Step-by-Step Resolution Process:
- Diagnose the ML Policy: Check the acquisition function (e.g., Upper Confidence Bound) used in the Design phase. A low emphasis on "exploration" can cause this [10].
- Increase Exploration: In the next DBTL cycle, deliberately design and build a batch of variants from less-explored regions of the sequence space, as determined by the model's uncertainty estimates [10].
- Validate In Vitro: For metabolic engineering, use a cell-free protein synthesis (CFPS) system to test pathway enzyme levels and interactions rapidly before committing to full in-vivo strain construction [9].
- Retrain the Model: Integrate the new experimental data from both high-performing and poor-performing strains into the training set to improve the model's accuracy and coverage in the next Learn phase [10].
- Escalation Path: If iterative cycling does not improve performance, consult a machine learning specialist to re-evaluate the model's features, kernel, or acquisition function.
- Validation or Confirmation Step: The next batch of designed strains should include candidates with both high predicted performance and high uncertainty, leading to the discovery of improved variants.
2. Guide: Inefficient Foraging Behavior in Animal Models
- Issue or Problem Statement: In a study on foraging behavior, food-deprived animals do not show the expected increase in rhythmic foraging activity, confounding the analysis of the exploration-exploitation dynamic [11].
- Symptoms or Error Indicators: No significant change in general activity or foraging; disrupted daily rhythmic pattern of behavior.
- Environment Details: Home-Cage monitoring system; 12h/12h light/dark cycle; food deprivation protocol.
- Possible Causes:
- Insufficient Energy Deficit: The duration of food deprivation was not long enough to trigger the energy-seeking motivational state [11].
- Confounding Food Cues: The presence of non-nutritive food cues (odor, sight) without actual energy availability may be distorting the natural behavioral rhythm [11].
- Neurological Inactivity: Neuronal activity in the paraventricular hypothalamic nucleus (PVH), a key regulator of this behavior, may not be adequately modulated [11].
- Step-by-Step Resolution Process:
- Confirm Energy Status: Verify and potentially extend the food deprivation period to ensure a significant energy deficit.
- Control for Cues: Systematically introduce or remove food-related sensory cues (e.g., odor, mouthfeel) to isolate their effect from the energy deficit itself [11].
- Monitor Neuronal Activity: Use immunohistochemical staining (e.g., for c-fos) to confirm that PVH neuronal activity is increased during the expected foraging periods [11].
- Modulate Activity: Employ chemogenetic actuators (e.g., DREADDs) to selectively activate or inhibit PVH neurons to confirm their causal role in the behavior and rescue the phenotype [11].
- Escalation Path: If the issue persists, conduct metabolic profiling to rule out underlying health issues in the animal model and ensure the Home-Cage system is calibrated correctly.
- Validation or Confirmation Step: Successful activation of PVH neurons should restore or enhance the rhythmic foraging pattern in the animals.
Frequently Asked Questions (FAQs)
Q1: In the context of an ML-DBTL cycle, when should my team prioritize exploration over exploitation? A1: Prioritize exploration when: 1) Starting a new project with limited initial data. 2) Performance has plateaued, suggesting a local optimum. 3) Moving to a new host organism or genetic context. Exploitation is favored when you have a high-quality, large dataset and need to fine-tune a nearly-optimal design for maximum yield [10].
Q2: What is a "knowledge-driven DBTL" cycle and how does it differ from a standard one? A2: A knowledge-driven DBTL incorporates upstream, mechanistic investigations—such as testing pathways in cell-free systems—before the first full in-vivo cycle. This generates critical data to inform the initial Design phase, making the subsequent cycles more efficient than a standard DBTL that might start with random or statistically designed variants [9].
Q3: Our research bridges animal behavior and synthetic biology. What is a core analogy between foraging and DBTL? A3: The core analogy is the exploration-exploitation dilemma. A foraging animal must balance exploring new areas for food (high energy cost, high uncertainty) with exploiting a known food source (low cost, predictable reward) [11]. Similarly, in a DBTL cycle, you must balance exploring new regions of genetic design space (which might fail) with exploiting known, high-performing designs to refine them [10]. Both are governed by the need to optimize a resource (energy or research funding/time) under uncertainty.
Experimental Data & Protocols
Table 1: Quantitative Data on Foraging Behavior Modulation [11]
| Intervention | Foraging Behavior Amplitude (Change vs. Control) | PVH Neuronal Activity (c-fos+ cells) | Key Finding |
|---|---|---|---|
| Food Deprivation (Energy Deficit) | Significantly Increased | Significantly Increased | Potentiates rhythmic foraging |
| Food Cues Only (No Energy) | Modulated | Not Specified | Insufficient without energy deficit |
| Chemogenetic PVH Activation | Enhanced | Artificially Increased | Directly enhances foraging |
| Chemogenetic PVH Inactivation | Decreased & Rhythm Impaired | Artificially Decreased | Impairs rhythmic foraging |
Table 2: ML-Guided RBS Engineering Performance Data [10]
| DBTL Cycle | Number of RBS Variants Tested | Best Performance (TIR) vs. Benchmark | Key ML Action |
|---|---|---|---|
| Initial | ~100-150 | Baseline | Initial data collection for model training |
| 1 | ~150 | +10-15% | Model-guided design begins |
| 2 | ~150 | +20-25% | Exploitation of high-confidence predictions |
| 3 & 4 | ~150 | +34% | Balanced exploration-exploitation finds optimum |
Detailed Protocol: Immunohistochemical Staining for Neuronal Activity (c-fos) [11]
- Purpose: To visualize and quantify trends in neuronal activity in brain regions like the PVH.
- Methodology:
- Perfusion and Fixation: Deeply anesthetize mice and perfuse transcardially with 4% paraformaldehyde (PFA). Remove brains and post-fix in 4% PFA for 0-14 hours.
- Sectioning: Using a vibrating microtome (e.g., Leica VT1200S), collect 30-μm-thick coronal brain sections containing the region of interest.
- Immunostaining: Incubate free-floating sections with a primary antibody against c-fos (e.g., 1:500 dilution). Then, incubate with a biotinylated secondary antibody.
- Visualization: Treat sections with the 3,3'-diaminobenzidine (DAB) chromogen to produce a visible precipitate at the site of c-fos expression.
- Imaging & Analysis: Acquire images using a light microscope. Count c-fos positive cells in the target regions (e.g., PVH, ARC, LH) for quantitative comparison between experimental groups.
Detailed Protocol: High-Throughput RBS Library Construction & Screening [10]
- Purpose: To build and test a large library of RBS variants to optimize translation initiation rate (TIR) for a pathway enzyme.
- Methodology:
- Design: Using an ML algorithm (e.g., Gaussian Process Regression with a Bandit algorithm), design a batch of RBS sequence variants focusing on the core Shine-Dalgarno sequence.
- Build (Automated Cloning):
- Use automated DNA assembly (e.g., Golden Gate or Gibson Assembly) to clone each RBS variant upstream of a reporter gene (e.g., GFP) in an expression plasmid.
- Transform the plasmid library into the production E. coli strain. This step is often automated using liquid handling robots.
- Test (High-Throughput Assay):
- Grow deep-well plates of the transformed library with induction.
- Use high-throughput flow cytometry to measure fluorescence (GFP) of each variant, which serves as a proxy for TIR and protein expression level.
- Learn: Feed the RBS sequence and corresponding TIR data back into the ML model. The model learns the sequence-function relationship and recommends a new, improved batch of variants for the next cycle.
Workflow and Pathway Visualizations
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Reagents for Featured Experiments
| Item | Function / Application | Specific Example / Note |
|---|---|---|
| Home-Cage Monitoring System | Automated, long-term behavioral tracking of animals (e.g., foraging, general activity) in their home environment without human disruption [11]. | Systems like Shanghai Vanbi's Home-Cage with Tracking Master software. |
| Chemogenetic Actuators (DREADDs) | To selectively modulate (activate/inhibit) neuronal activity in specific brain regions in vivo to establish causality in behavior [11]. | Used with Clozapine-N-Oxide (CNO) injection; targets PVH neurons. |
| c-fos Antibody | Immunohistochemical marker for detecting and quantifying recent neuronal activity in tissue sections following specific stimuli or behaviors [11]. | e.g., Abcam ab214672. |
| Cell-Free Protein Synthesis (CFPS) System | A crude cell lysate system for rapid in-vitro testing of metabolic pathways and enzyme expression levels before full in-vivo strain engineering [9]. | Used for knowledge-driven DBTL entry point. |
| Ribosome Binding Site (RBS) Library | A set of genetic variants to fine-tune the translation initiation rate (TIR) of genes in a metabolic pathway, optimizing enzyme expression and product yield [10]. | Designed via ML; built via automated cloning. |
| Gaussian Process Regression (GPR) Model | A machine learning algorithm used in the "Learn" phase that predicts performance and, crucially, provides uncertainty estimates for genetic designs [10]. | Enables balancing exploration vs. exploitation. |
In both machine learning and scientific research domains like Design-Build-Test-Learn (DBTL) cycles, a fundamental challenge is the exploration-exploitation dilemma. This refers to the trade-off between gathering new information (exploration) and using existing knowledge to maximize rewards (exploitation) [1]. Researchers have identified two primary strategies that humans and algorithms use to explore: directed exploration (purposeful information-seeking) and random exploration (strategic randomization of choice) [12] [13]. Understanding and implementing these strategies is crucial for optimizing research processes, from drug discovery to reinforcement learning agent training. This guide provides troubleshooting and methodological support for researchers applying these concepts.
The table below summarizes the key characteristics of directed and random exploration.
| Feature | Directed Exploration | Random Exploration |
|---|---|---|
| Core Principle | Purposeful information-seeking; biased towards informative options [12]. | Strategic introduction of decision noise to try new options by chance [12]. |
| Driving Force | Information bonus (e.g., uncertainty-driven) [12]. | Random noise added to value calculations [12]. |
| Computational Analogy | Upper Confidence Bound (UCB) algorithms [12]. | Epsilon-Greedy or Thompson Sampling algorithms [12] [4]. |
| Key Neural Correlate | Right Frontopolar Cortex (FPC) [14]. | Neural variability; potentially modulated by norepinephrine [12] [15]. |
| Response to Time Horizon | Increases with a longer future time horizon (more choices remain) [12] [13]. | Increases with a longer future time horizon [12] [13]. |
| Primary Use Case | When the value of information is high and can be quantified. | In complex environments where optimal information-seeking is computationally intractable [15]. |
Experimental Protocols & Methodologies
The Horizon Task: Quantifying Both Strategies
The Horizon Task is a behavioral paradigm designed to independently measure directed and random exploration in human participants [13] [14].
Workflow: The diagram below illustrates the core structure and decision logic of the Horizon Task.
Detailed Protocol:
- Task Setup: Participants play a series of games where they choose between two "slot machines" (bandits) with different, unknown reward distributions [14].
- Key Manipulation 1 - Time Horizon:
- In a Horizon 1 (H1) game, the participant makes only one choice. This favors exploitation, as there is no future to use gathered information.
- In a Horizon 6 (H6) game, the participant makes six sequential choices. This favors exploration, because information gained early can be used for better choices later [13] [14].
- Key Manipulation 2 - Information Condition:
- Before the free-choice phase, participants undergo four forced-choice trials to control their initial information.
- Equal Information [2-2]: Participants see two outcomes from each bandit. This condition helps measure random exploration as the probability of choosing the option with the lower estimated reward.
- Unequal Information [1-3]: Participants see one outcome from one bandit and three from the other. This condition helps measure directed exploration as the probability of choosing the less-known, higher-information option [14].
- Data Analysis:
- A cognitive model is fit to the choice data to extract two key parameters:
Pharmacological Intervention: Targeting the Norepinephrine System
This protocol tests the causal role of the norepinephrine (NE) system in random exploration [15].
Detailed Protocol:
- Design: Double-blind, placebo-controlled, crossover study.
- Intervention: Administration of a single dose of atomoxetine (40-60 mg), a selective norepinephrine transporter blocker, versus a placebo.
- Participants: Healthy human volunteers.
- Task: Participants perform the Horizon Task (or a similar explore-exploit task) after drug administration.
- Measurement: The effects of atomoxetine on the model-based parameters for random exploration (decision noise) and directed exploration (information bonus) are analyzed [15].
- Expected Outcome: Atomoxetine is hypothesized to selectively reduce random exploration without significantly affecting directed exploration, supporting the role of NE in modulating decision noise [15].
Neuromodulation: Inhibiting the Frontopolar Cortex
This protocol uses brain stimulation to test the causal role of the frontopolar cortex in directed exploration [14].
Detailed Protocol:
- Technique: Continuous Theta-Burst Transcranial Magnetic Stimulation (cTBS).
- Target: Right Frontopolar Cortex (RFPC). A control site (e.g., vertex) is also stimulated in a separate session.
- Participants: Healthy human volunteers.
- Task: Participants perform the Horizon Task after undergoing cTBS.
- Measurement: Compare the information bonus (directed exploration) and decision noise (random exploration) between the RFPC stimulation and control sessions.
- Expected Outcome: Inhibition of the RFPC via cTBS is expected to selectively reduce directed exploration while leaving random exploration intact [14].
Troubleshooting Guides & FAQs
FAQ 1: In my reinforcement learning model for molecular discovery, the agent converges on a suboptimal candidate too quickly. How can I improve the search?
- Problem: The algorithm is over-exploiting and lacks a mechanism to discover novel, potentially superior candidates.
- Solution:
- Implement Directed Exploration: Incorporate an information bonus or Upper Confidence Bound (UCB) strategy. This will encourage the agent to select options where uncertainty about the reward (e.g., bioactivity) is high [12] [1].
- Adjust Exploration Schedule: If using a simple epsilon-greedy strategy, switch to a decaying epsilon schedule or an adaptive method like Thompson Sampling. This maintains a baseline level of exploration for longer, preventing premature convergence [4] [16].
FAQ 2: My research process (e.g., high-throughput screening) is inefficient, exploring too many options with low success. How can I make it more targeted?
- Problem: The process is over-exploring without effectively leveraging accumulated knowledge.
- Solution:
- Shift Towards Exploitation: Use early results to build a predictive model. Prioritize candidates or experiments that the model predicts will be high-performing, effectively adding an exploitation bias [4].
- Adopt a Hybrid Strategy: Implement a strategy like Activity-Directed Synthesis (ADS), which is inherently function-driven. It uses initial broad exploration (promiscuous reactions) but quickly channels resources into exploiting and optimizing only the reactions that show promising bioactivity [17].
FAQ 3: My behavioral experiment failed to find a horizon effect on exploration. What could have gone wrong?
- Problem: The manipulation of the time horizon was not effective, or exploration strategies were not properly isolated.
- Solution:
- Control for Confounds: Ensure that the expected reward value and the information value of options are decorrelated in your task design, as in the Horizon Task's forced-choice phase. A common confound is that participants naturally gain more information about higher-value options because they choose them more often [14].
- Verify Task Instructions: Confirm that participants understand how many choices they have in each game (the horizon). The utility of exploration is only high if they know they have future choices to use the information in [13].
FAQ 4: A pharmacological agent (e.g., atomoxetine) affected behavior, but I cannot tell if it impacted directed or random exploration. How can I dissociate these strategies?
- Problem: The behavioral task used does not provide independent measures of the two exploration strategies.
- Solution:
- Use a Deconfounded Task: Employ a task like the Horizon Task that independently manipulates information and reward [15] [14].
- Fit a Computational Model: Extract parameters for information bonus (βinfo) and decision noise (η). A selective effect on
ηwould point to a change in random exploration, while a change inβinfowould indicate an effect on directed exploration [12] [15].
The Scientist's Toolkit: Key Reagents & Materials
The table below lists essential "research reagents," both computational and biological, for studying exploration strategies.
| Reagent / Material | Function / Description | Relevance to Exploration Research |
|---|---|---|
| Horizon Task | A behavioral paradigm to deconfound reward and information. | The primary tool for independently quantifying directed and random exploration in humans [13] [14]. |
| Computational Model (e.g., from Wilson et al.) | A cognitive model with information bonus and decision noise parameters. | Used to analyze task data and extract quantitative measures of directed (βinfo) and random (η) exploration [13]. |
| Atomoxetine | A selective norepinephrine transporter (NET) blocker. | A pharmacological tool for manipulating the norepinephrine system to test its causal role in random exploration [15]. |
| Transcranial Magnetic Stimulation (TMS) | A non-invasive brain stimulation technique. | Used to temporarily inhibit (e.g., via cTBS) brain regions like the right frontopolar cortex to test their causal role in directed exploration [14]. |
| Multi-Armed Bandit (MAB) Framework | A formal mathematical framework for the explore-exploit dilemma. | Provides the theoretical foundation and algorithms (e.g., UCB, Thompson Sampling) that mirror human exploration strategies [12] [4] [1]. |
Computational Intractability and the Need for Approximate Solutions
Frequently Asked Questions (FAQs)
FAQ 1: What does "computational intractability" mean in the context of drug design? Computational intractability describes problems that cannot be solved within a reasonable timeframe, even with the most powerful classical computers. These problems require exponential computational resources relative to the input size, rendering them practically unsolvable for large instances. In drug design, this often manifests in tasks like de novo molecular generation, where the number of possible molecular structures is vast, making exhaustive search for an optimal candidate impossible [18] [19].
FAQ 2: How does the exploration-exploitation dilemma relate to intractable problems? Optimal solutions to the explore-exploit dilemma are intractable in all but the simplest cases. The reason is that optimal solutions require massive simulations of the future—considering how choices impact future outcomes and how those outcomes will impact future choices. Because of this computational complexity, researchers turn to approximate strategies like directed and random exploration [12].
FAQ 3: What is the practical consequence of intractability for my simulation-based research? When simulations (e.g., involving partial-differential-equation models with fine spatiotemporal discretization) are computationally expensive, "many-query" problems like uncertainty quantification or design optimization become intractable. This limits the scope of complex optimizations in areas like global climate modeling, advanced materials design, and ecological system predictions [18] [20].
FAQ 4: What can I do if my problem is proven to be intractable? Intractability does not mean a problem is unsolvable, but that an exact, efficient solution for all cases is unlikely. The standard approach is to shift focus towards finding a "good enough" approximate solution. This can be achieved through approximation algorithms, heuristic methods, surrogate models, or new computational paradigms like quantum computing [18] [19].
Troubleshooting Guides
Problem: My molecular generation algorithm gets stuck in local minima, producing low-diversity candidates. This is a classic symptom of an imbalance between exploration and exploitation.
- Potential Cause 1: Over-exploitation of known, high-scoring regions of the chemical space.
- Solution: Integrate a mean-variance framework that explicitly optimizes for both the scoring function (exploitation) and the diversity of the proposed solutions (exploration) [21].
- Solution: Implement a hybrid exploration strategy like Max-Boltzmann, which has been shown to provide more stable and effective outcomes in high-risk, complex domains compared to pure epsilon-greedy or Boltzmann methods [22].
Problem: The error in my surrogate or reduced-order model grows uncontrollably over time. Dynamical systems pose a unique challenge as errors exhibit dependence on non-local quantities, meaning the error at a given time depends on the past history of the system.
- Potential Cause 1: Using an error quantification method (like a simple residual norm) that is only sensitive to local, instantaneous errors.
- Solution: Adopt a Time-Series Machine-Learning Error Modeling (T-MLEM) method. This uses recursive, time-series-prediction models (e.g., autoregressive models, recurrent neural networks) with time-local error indicators as features to capture the non-local error dynamics [20].
Problem: My reinforcement learning agent fails to discover successful states in a sparse-reward environment. This is known as the "hard-exploration" problem, where random exploration rarely discovers states that provide meaningful feedback.
- Potential Cause 1: Lack of intrinsic motivation to guide the agent towards novel or informative states.
- Solution: Augment the environment's extrinsic reward with an intrinsic exploration bonus. This bonus can be based on the novelty of a state, estimated using pseudo-counts from a density model or locality-sensitive hashing (LSH) to track state visits in high-dimensional spaces [23].
Experimental Protocols & Methodologies
Protocol: Constructing a Time-Series Machine-Learning Error Model (T-MLEM)
Purpose: To accurately model the error of approximate solutions (e.g., from reduced-order models) for parameterized dynamical systems, where errors have non-local, time-dependent dynamics [20].
Methodology:
- Data Generation: Run the high-fidelity and approximate models for a training set of parameters. Collect sequences of time-local error indicators (e.g., residual norms) as features and the corresponding true normed state errors as the response variable.
- Feature Engineering: Use error indicators like residual samples that are cheaply computable during the online use of the approximate solution.
- Regression Model Training: Train a recursive time-series-prediction model (e.g., an Autoregressive model or Recurrent Neural Network) to map the sequence of features to the error response. For comparison, a non-recursive model (e.g., a feed-forward neural network) can also be trained.
- Noise Model Construction: Model the residual uncertainty not captured by the regression model. This is often done by fitting a mean-zero Gaussian distribution whose variance is the sample variance of the prediction error on a test set.
- Validation: The trained T-MLEM model provides a statistical error prediction (a random variable) that can be used to quantify uncertainty in the approximate solution.
Protocol: Implementing Directed and Random Exploration in a Bandit Task
Purpose: To empirically study and dissect the exploration strategies used by human or artificial agents in a controlled setting [12].
Methodology:
- Task Design: Use a multi-armed bandit task where the reward probabilities of options are initially unknown. Key manipulations include:
- Time Horizon: Vary the number of trials left in the game. A longer horizon should increase exploration.
- Novel Options: Introduce completely new options at specific points to measure directed exploration towards novelty.
- Uncertainty: Control the initial uncertainty or the volatility of the reward distributions.
- Modeling Behavior: Fit computational models to the choice data to quantify the contribution of each strategy.
- Directed Exploration Model:
Q(a) = r(a) + IB(a), whereIB(a)is an information bonus, often proportional to the uncertainty about optiona. - Random Exploration Model:
Q(a) = r(a) + η(a), whereη(a)is zero-mean random noise added to the value estimate.
- Directed Exploration Model:
- Analysis: Identify directed exploration by increased information-seeking (e.g., choosing novel or uncertain options) when the time horizon is long. Identify random exploration by an increase in the randomness of choices (e.g., a higher softmax temperature parameter) under the same conditions.
Workflow Visualization
Approximation Workflow
The Scientist's Toolkit: Research Reagent Solutions
Table 1: Key computational components and their functions for tackling intractability.
| Research Reagent | Function & Purpose |
|---|---|
| Surrogate Model (e.g., Reduced-Order Model) | Replaces a computationally expensive high-fidelity model (e.g., a PDE) to generate low-cost approximate solutions, making many-query problems tractable [20]. |
| Error Model (e.g., T-MLEM) | A statistical model that maps cheaply computable error indicators (e.g., residual norms) to a prediction of the error incurred by an approximate solution, quantifying its uncertainty [20] [24]. |
| Upper Confidence Bound (UCB) | A directed exploration strategy that adds an "information bonus" to the value of an option, proportional to its uncertainty, thereby systematically guiding exploration towards informative choices [12]. |
| Boltzmann (Softmax) Policy | A random exploration strategy that selects actions probabilistically based on their estimated Q-values, regulated by a temperature parameter. Higher temperature increases exploration [25] [23]. |
| Density Model (e.g., PixelCNN) | A model that estimates the probability density of states, allowing for the calculation of pseudo-counts. This is used to generate intrinsic rewards for count-based exploration in large state spaces [23]. |
| Locality-Sensitive Hashing (LSH) | A hashing technique that maps similar states to similar hash codes, enabling efficient counting of state visits in high-dimensional continuous spaces for count-based exploration bonuses [23]. |
The Design-Build-Test-Learn (DBTL) cycle is a cornerstone framework in synthetic biology and biotechnology research and development, enabling the systematic and iterative engineering of biological systems [26]. This cyclical process allows researchers to rationally design biological components, assemble them into functional systems, rigorously test their performance, and learn from the data to inform the next, improved design round [27].
Automation and machine learning (ML) are now transforming the DBTL cycle, helping to overcome traditional bottlenecks and enhancing its efficiency and predictive power [28] [27]. A critical challenge within this iterative process is the exploration-exploitation dilemma—the strategic decision between exploring new, uncertain designs to gather more information and exploiting known, high-performing designs to maximize immediate results [29] [12]. This article provides troubleshooting guidance and FAQs to help researchers navigate the practical challenges of implementing the DBTL cycle, with a special focus on integrating ML to balance exploration and exploitation.
FAQs: Navigating the DBTL Cycle
What is the fundamental purpose of the DBTL cycle in synthetic biology?
The DBTL cycle provides a structured framework for engineering organisms to perform specific functions, such as producing biofuels, pharmaceuticals, or other valuable compounds [26]. Its iterative nature allows researchers to systematically approach the complexity of biological systems, where the impact of introducing foreign DNA is often difficult to predict, making multiple testing permutations necessary to achieve a desired outcome [26].
How can machine learning (ML) improve the DBTL cycle?
ML has gained significant traction for overcoming bottlenecks, particularly in the "Learn" phase [27]. By processing large, complex datasets generated from high-throughput experiments, ML models can:
- Uncover unseen patterns and provide predictive models by choosing appropriate features to represent a phenomenon of interest [27].
- Facilitate system-level prediction of biological designs with desired characteristics by elucidating the associations between phenotypes and various combinations of genetic parts and genotypes [27].
- Guide metabolic engineering by learning from experimental datasets to make accurate genotype-to-phenotype predictions, thereby accelerating the design of more efficient biological pathways [28] [30].
What is the exploration-exploitation dilemma in this context?
The exploration-exploitation dilemma is a fundamental trade-off faced when making sequential decisions under uncertainty [29] [12].
- Exploitation involves choosing the best-known option based on current information to maximize immediate reward.
- Exploration involves trying less-known or novel options to gather more information, which may lead to better rewards in the long run [31].
In a DBTL cycle, this translates to the decision between exploiting a known, well-performing genetic design and exploring new, potentially superior but uncertain designs. Optimal solutions to this dilemma are computationally complex, leading to the use of approximate strategies [29].
What are the main strategies for balancing exploration and exploitation?
Research shows that humans, animals, and effective artificial intelligence algorithms often combine two major strategies to solve this dilemma [29] [12]:
- Directed Exploration (Information-Seeking): This strategy deterministically biases choice towards more informative options. A common computational method is to add an "information bonus" to the value of uncertain options, making them more attractive [12].
- Random Exploration (Behavioral Variability): This strategy introduces randomness or noise into the decision-making process. This can be implemented by adding random noise to the computed value of each option before selecting the one with the highest value [12].
These strategies are not mutually exclusive and can be integrated into a holistic approach for more robust performance [29].
Troubleshooting Common DBTL Workflow Challenges
Problem: Low Throughput and Efficiency in the "Build" and "Test" Phases
Symptoms: The rate of constructing and testing biological designs is slow, creating a bottleneck that limits the number of DBTL iterations you can perform.
Solutions:
- Implement Automation: Integrate automated liquid handlers (e.g., from Tecan, Beckman Coulter, or Hamilton Robotics) for high-precision, high-throughput pipetting, PCR setup, and plasmid preparation [28].
- Use Orchestration Software: Adopt platforms like TeselaGen to manage complex protocols, track samples across different lab equipment, and maintain inventory efficiently [28].
- Partner with DNA Synthesis Providers: Streamline the process by integrating with providers like Twist Bioscience or IDT for seamless incorporation of custom DNA sequences into your workflows [28].
Problem: Inability to Effectively "Learn" from Large, Complex Datasets
Symptoms: Despite generating large amounts of multi-omics data (from NGS, mass spectrometry, etc.), extracting meaningful, actionable insights to guide the next design cycle is challenging.
Solutions:
- Adopt a Centralized Data Hub: Use a unified software platform to collect, standardize, and manage data from all analytical equipment and design phases [28].
- Apply Machine Learning: Employ ML algorithms to analyze experimental data, uncover complex patterns, and build predictive models that can forecast the performance of future biological designs, such as predicting genotype-to-phenotype relationships [28] [27].
- Establish ML-Friendly Data Standards: To lay the groundwork for effective ML, implement common standards for data generation and formatting across experiments [27].
Problem: Strategic Uncertainty in the "Design" Phase
Symptoms: Difficulty deciding whether to optimize a known, promising genetic construct (exploit) or to test a radically new design with uncertain potential (explore).
Solutions:
- Formalize the Trade-off: Explicitly frame your design choices within the exploration-exploitation dilemma.
- Quantify Uncertainty: Use computational models that estimate the uncertainty or potential information gain of each design option.
- Implement Adaptive Exploration Strategies: Instead of fixed rules, use strategies that dynamically adjust the level of exploration based on the stage of your project. For example:
- Use Value-Difference Based Exploration (VDBE), which adapts the exploration probability based on the difference in estimated values between options, reflecting the agent's uncertainty [31].
- Use Max-Boltzmann strategies, which combine the directed nature of Softmax with the adaptive nature of value-difference methods [31].
The following table summarizes these adaptive strategies and their applications within a DBTL context.
| Strategy Name | Core Mechanism | Application in DBTL Cycle |
|---|---|---|
| ε-Greedy [31] | With probability ε, explore a random action; otherwise, exploit the best-known action. | A simple baseline for introducing randomness in design selection. |
| Decreasing ε-Greedy [31] | The exploration probability ε decreases linearly over time. | Useful for initial DBTL rounds; exploration is high early on and reduces as knowledge accumulates. |
| Value-Difference Based Exploration (VDBE) [31] | The exploration probability ε is dynamically adjusted based on the difference in Q-values (value estimates), increasing when the agent is uncertain. | Adapts exploration based on the confidence in the performance of different genetic designs. |
| Max-Boltzmann [31] | Combines a value-based rule (like ε-greedy) for high-value options with a Softmax rule for the rest, blending directed and random exploration. | Balances the choice between top-performing designs (exploit) and informed sampling of other options (explore). |
Problem: Low Protein Expression in a Microbial Chassis
Symptoms: Transformed bacterial colonies grow slowly, and protein yields are very low, hindering downstream purification and functional assays [32].
Solutions:
- Hypothesis: Different colonies from the same transformation might vary in their ability to tolerate the expression of the foreign protein [32].
- Iterative DBTL Protocol:
- Design: Test the hypothesis by designing an experiment that screens multiple colonies, not just one.
- Build: Inoculate separate culture flasks with a range of different colonies from your transformation plate.
- Test: Measure the growth curves (OD₆₀₀) and protein expression levels (e.g., via SDS-PAGE) for each flask.
- Learn: Identify and select the healthiest, highest-expressing colonies for scaling up. This turns colony variability from a problem into a selection tool [32].
The Scientist's Toolkit: Key Research Reagent Solutions
The following table details essential materials and their functions for executing automated, data-driven DBTL cycles, particularly for metabolic pathway engineering as demonstrated in the dopamine production case study [30].
| Item / Reagent | Function / Explanation |
|---|---|
| Ribosome Binding Site (RBS) Libraries | A key tool for rational fine-tuning of gene expression levels within a synthetic pathway without altering the coding sequence itself [30]. |
| pET Plasmid System | A common and robust vector system for high-level, inducible expression of heterologous genes in E. coli [30]. |
| E. coli FUS4.T2 | An example of a specialized production host strain, often genetically engineered for high precursor (e.g., l-tyrosine) production [30]. |
| Cell-Free Protein Synthesis (CFPS) System | A crude cell lysate system used for upstream in vitro testing of enzyme expression and pathway functionality, bypassing cellular constraints and accelerating initial design [30]. |
| HpaBC (4-hydroxyphenylacetate 3-monooxygenase) | A native E. coli enzyme that converts l-tyrosine to l-DOPA, a key precursor in the dopamine production pathway [30]. |
| Ddc (l-DOPA decarboxylase) | A heterologous enzyme from Pseudomonas putida that catalyzes the formation of dopamine from l-DOPA [30]. |
Workflow Visualization: The ML-Enhanced DBTL Cycle
The following diagram illustrates the integrated, machine-learning-enhanced DBTL cycle, highlighting the critical decision point of exploration versus exploitation.
Experimental Protocol: Knowledge-Driven DBTL for Metabolite Production
This protocol is adapted from a study that successfully optimized dopamine production in E. coli using a knowledge-driven DBTL cycle with high-throughput RBS engineering [30].
Objective
To develop and optimize a microbial strain for the high-yield production of a target metabolite (dopamine) by fine-tuning the expression of pathway enzymes.
Materials
- Bacterial Strains: E. coli DH5α for cloning; a specialized production strain like E. coli FUS4.T2 [30].
- Plasmids: pET system for gene storage; a compatible plasmid (e.g., pJNTN) for library construction and in vivo expression [30].
- Genes: Heterologous genes for the metabolic pathway (e.g.,
hpaBCandddcfor dopamine production) [30]. - Media: 2xTY medium for cloning; a defined minimal medium for production experiments [30].
- Equipment: Automated liquid handling system, plate reader, HPLC or MS for metabolite quantification.
Methodology
Step 1: In Vitro Knowledge Gathering (Pre-DBTL)
- Design: Create plasmids for individual expression of pathway enzymes (e.g., pJNTNhpaBC, pJNTNddc).
- Build: Transform plasmids into a suitable strain and cultivate for cell lysate production.
- Test: Use a cell-free protein synthesis (CFPS) system to express the enzymes in a reaction buffer containing the substrate (l-tyrosine). Measure the formation of the intermediate (l-DOPA) and final product (dopamine) to determine baseline enzyme activities and identify potential bottlenecks [30].
- Learn: Analyze the in vitro data to hypothesize the optimal relative expression levels for the two enzymes in the full pathway.
Step 2: First In Vivo DBTL Cycle
- Design: Based on the in vitro learnings, design a library of genetic constructs where the expression of the two pathway genes is fine-tuned using a Ribosome Binding Site (RBS) library. This library is created by modulating the Shine-Dalgarno sequence [30].
- Build: Use high-throughput molecular cloning (e.g., Golden Gate or Gibson Assembly) and automated liquid handlers to assemble the RBS library constructs into the production vector and transform into the production host [30].
- Test: Cultivate the library variants in a high-throughput format (e.g., deep-well plates). Monitor growth and quantitatively analyze final metabolite production using HPLC or MS [30].
- Learn: Statistically analyze the production data to identify top-performing RBS combinations. Use this data to train an initial machine learning model to predict production yields based on RBS sequence features.
Step 3: Iterative DBTL Cycling with ML-Guided Exploration/Exploitation
- Design: The trained ML model is used to propose a new set of designs for the next cycle.
- Exploitation: The model can propose designs that are similar to the known high-performers but with slight optimizations.
- Exploration: The model can also propose designs in unexplored regions of the genetic design space that it predicts could be high-performing (directed exploration), or you can incorporate random sampling of the space (random exploration) [29] [12].
- Build, Test, Learn: Repeat the build and test phases with the new designs. Use the resulting data to retrain and improve the ML model, enhancing its predictive power for subsequent cycles [27] [30].
This knowledge-driven, ML-enhanced approach efficiently navigates the vast design space, balancing the exploration of novel designs with the exploitation of known successful strategies to rapidly converge on an optimally performing production strain.
Information Gain vs. Immediate Reward in Experimental Design
FAQs: Balancing Exploration and Exploitation
FAQ 1: What is the exploration-exploitation dilemma in experimental research? The exploration-exploitation dilemma describes the conflict between gathering new information (exploration) and using known information for immediate reward (exploitation). In research, this translates to choosing between testing a new, uncertain hypothesis that could yield valuable insights (information gain) versus repeating a proven protocol to obtain a reliable result (immediate reward). Computational studies show humans use two distinct strategies to solve this: a bias for information ('directed exploration') and the randomization of choice ('random exploration') [33] [34].
FAQ 2: How does this dilemma relate to the Design-Build-Test-Learn (DBTL) cycle? The DBTL cycle is inherently driven by this balance. Each "Test" phase can be exploitative (validating a known high-performing design) or exploratory (gathering data on new designs to inform future learning). A paradigm shift towards "LDBT" (Learn-Design-Build-Test) proposes using machine learning first to leverage large existing datasets, making the initial design more informed and reducing the need for extensive exploratory testing cycles. This places a higher value on initial information gain to streamline the entire process [35].
FAQ 3: My experiment failed. How do I troubleshoot whether the issue was with my exploratory or exploitative approach? Effective troubleshooting requires a structured method to identify the root cause [36] [37]:
- Identify the Problem: Clearly define what went wrong without assuming the cause (e.g., "No protein expression" not "The new polymerase is bad").
- List Possible Explanations: Consider causes related to both exploration (e.g., an unvalidated new reagent, an uncertain protocol step) and exploitation (e.g., a miscalculation in a standard buffer recipe, contaminated common stock).
- Collect Data: Review your experimental controls. Did both positive and negative controls perform as expected? Check reagent storage conditions and your procedure against established protocols [37].
- Eliminate Explanations: Use the collected data to rule out incorrect explanations.
- Check with Experimentation: Design a targeted experiment to test the remaining likely causes.
- Identify the Cause: Conclude the most probable root cause and implement a fix.
FAQ 4: When should I prioritize information gain over immediate reward? Prioritize information gain (exploration) when [34]:
- Entering a new research area with high uncertainty.
- Standard protocols are consistently failing for your specific application.
- You are building large datasets for machine learning models.
- The potential long-term benefit of discovering a new, more efficient method outweighs the short-term need for a result. Prioritize immediate reward (exploitation) when [34]:
- You are in the final validation stages of a project.
- You need to generate reproducible data for a publication.
- Resource constraints (time, funding) are a primary concern.
FAQ 5: What computational models describe how researchers balance this trade-off? Computational strategies can be summarized as follows [34]:
| Strategy | Core Principle | Best Applied When... |
|---|---|---|
| Standard Reinforcement Learning (sRL) | Learns to maximize only immediate, expected reward based on past outcomes. The decision process can include random noise ("random exploration"). | The research environment is stable, and the goal is to reliably reproduce a known high-yield result. |
| Knowledge Reinforcement Learning (kRL) | Augments reward learning by assigning a value to information itself. Actively seeks to reduce uncertainty about options ("directed exploration"). | Working with poorly characterized systems, designing new protocols, or when preparing data for predictive computational models. |
Studies comparing these models show that humans engage in significant directed exploration, more frequently choosing options they have less information about, even when it is associated with lower short-term gains [34].
Troubleshooting Guides
Guide 1: Troubleshooting a Failed Exploratory Experiment
Scenario: You tested a novel protein expression system based on a machine learning prediction (LDBT cycle), but yield is unexpectedly low.
- Step 1: Verify the "Learn" Phase. Are the machine learning model's predictions reliable for this type of protein? Check the model's training data and known limitations [35].
- Step 2: Analyze the "Build" Phase.
- Reagent Solutions: Confirm the DNA template sequence and concentration. For cell-free systems, check the lysate activity and storage conditions [35].
- Controls: Include a positive control (a DNA template known to express well in any system) and a negative control (no template) to isolate the problem to the new design.
- Step 3: Analyze the "Test" Phase.
- Methodology: Ensure your assay (e.g., SDS-PAGE, activity assay) is functioning correctly. Run a known standard.
- Data Collection: Check for subtle signs of activity you might have missed. The experiment may have provided valuable information gain despite low yield (e.g., clues about protein instability) [35].
Guide 2: Troubleshooting a Failed Exploitative Experiment
Scenario: A standard PCR protocol that has worked for months suddenly produces no product.
- Step 1: Check All Controls [37]. This is the most critical step for exploitative protocols.
- Positive Control: Did it work? If not, the problem is systemic (e.g., the thermal cycler, master mix).
- Negative Control: Is it clean? If not, there is contamination.
- Step 2: List Possible Causes. Focus on components and equipment [37]:
- Taq DNA Polymerase: Activity loss? Incorrect storage?
- Primers: Degraded? Concentration correct?
- Template DNA: Quality and concentration?
- Thermal Cycler: Calibration off? Block temperature uniform?
- Step 3: Collect Data. Check expiration dates. Re-measure DNA concentrations. Verify the cycler's calibration [37].
- Step 4: Experiment. Set up a new reaction with fresh aliquots of all reagents, carefully following the proven protocol. If it works, the issue was a degraded reagent. If not, the thermal cycler may be at fault.
Experimental Protocols for Balancing Strategies
Protocol: A Directed Exploration Experiment to Characterize a New Enzyme
Objective: Gain maximum information on the activity of a novel hydrolase under different conditions.
- Design: Use a machine learning model (e.g., MutCompute, ProteinMPNN) to predict stabilizing mutations and informative point mutations [35]. The design should include a wide range of conditions (pH, temperature, substrates) rather than just optimizing for one high-yield condition.
- Build: Synthesize and clone the wild-type and key variant genes. For rapid testing, use a cell-free expression system to bypass time-consuming cell culture [35].
- Test: Use a high-throughput assay (e.g., in microtiter plates) to measure activity across all conditions and variants in parallel. The dependent variable is specific activity, and the independent variables are pH, temperature, and substrate.
- Learn: Analyze the dataset to build a predictive model of the enzyme's function. The goal is not a single high-yield point, but a comprehensive understanding (high information gain) to inform future projects [35].
Protocol: An Exploitative Experiment for High-Yield Protein Production
Objective: Relably produce a high quantity of a well-characterized protein (immediate reward).
- Design: Use the known, optimal expression construct (e.g., plasmid with strong promoter) and growth conditions (media, temperature) from previous cycles.
- Build: Transform the plasmid into a proven expression chassis (e.g., E. coli BL21). Inoculate a starter culture and then a large production culture.
- Test: Induce protein expression at the optimal cell density. Harvest cells, lyse, and purify the protein using a standard method (e.g., affinity chromatography). The key metric is final pure yield (mg/L).
- Learn: The learning is minimal and confirmatory. Note any minor deviations from the expected yield. The process is repeated with high fidelity to achieve the reward.
The Scientist's Toolkit
| Research Reagent Solution | Function in Exploration/Exploitation |
|---|---|
| Cell-Free Expression System | A tool for rapid exploration. Allows expression of proteins without cloning, enabling ultra-high-throughput testing of thousands of variants for informational gain [35]. |
| Machine Learning Models (e.g., ESM, ProteinMPNN) | Used in the "Learn" phase to generate informed hypotheses (LDBT), reducing uncertainty before any physical experiment is conducted [35]. |
| Positive & Negative Controls | Fundamental for exploitation and troubleshooting. They validate that a known protocol is working correctly and help isolate the cause when it fails [37] [38]. |
| High-Throughput Screening Platforms (e.g., Microfluidics) | Essential for directed exploration. Enables the collection of large, information-rich datasets on many conditions or variants simultaneously [35]. |
| Stable Cell Line/Proven Plasmid | A key resource for exploitation. Provides a reliable and reproducible system to achieve consistent, high-yield results [38]. |
From Theory to Bioreactors: Implementing ML Strategies in DBTL Workflows
Frequently Asked Questions (FAQs)
Q1: What is the exploration-exploitation dilemma, and why is it critical in biological research? The exploration-exploitation dilemma describes the challenge of choosing between testing new options to gather more information (exploration) and using known options that currently yield the best results (exploitation). In biological research, such as drug development or media optimization, this is critical because experiments are costly and time-consuming. A poor balance can lead to wasted resources, slow discovery, or even ethical concerns in clinical settings if patients receive suboptimal treatments for too long [39] [40].
Q2: When should I choose Thompson Sampling over UCB for my experiment? You should choose Thompson Sampling when you are working with complex, non-stationary environments (where reward distributions change over time) or when you prefer an algorithm that requires minimal parameter tuning [41] [42]. UCB is often preferable when you need strict, deterministic confidence bounds and can afford a more exploratory initial phase. Thompson Sampling has been shown to be particularly effective in clinical trial simulations and biological optimization tasks [41] [43].
Q3: How do I handle non-stationary reward distributions in biological data, like in adaptive clinical trials? Non-stationary rewards are common in biology, for example, when a pathogen evolves or patient responses shift. To handle this, you can employ algorithms specifically designed for non-stationary environments. Bio-inspired neural models and some variants of bandit algorithms can adapt to drifting reward probabilities over time [42]. Furthermore, using a sliding window of recent data or incorporating discount factors that weight recent rewards more heavily can help the algorithm adapt to changing conditions [39].
Q4: What are Contextual Bandits, and how can they improve personalized medicine research? Contextual Bandits are an extension of multi-armed bandits that incorporate "context"—additional information about each specific situation—into the decision-making process. In personalized medicine, the context can be a patient's genetic profile, biomarker levels, or clinical history. This allows the algorithm to learn which treatments work best for specific patient subtypes simultaneously, dramatically accelerating the identification of personalized therapeutic strategies and improving patient outcomes compared to context-free approaches [39].
Troubleshooting Guides
Issue 1: Algorithm Fails to Identify the Optimal Treatment or Condition
Symptoms:
- The algorithm's performance (e.g., final yield or success rate) plateaus at a suboptimal level.
- High cumulative regret, meaning the algorithm consistently selects poor options [42].
Possible Causes and Solutions:
- Cause: Insufficient Exploration. The algorithm is exploiting known, mediocre options too greedily and never discovers the true best arm.
- Cause: Over-exploration. The algorithm spends too much time testing suboptimal options, reducing overall efficiency.
- Solution: For Epsilon-Greedy, decrease the value of
εover time. For Thompson Sampling, verify that the prior distributions are correctly specified. Using a decoupled approach like Top-Two Thompson Sampling can more directly balance this trade-off [43].
- Solution: For Epsilon-Greedy, decrease the value of
- Cause: Non-stationary Environment. The best option has changed over the course of the experiment, but the algorithm is stuck with its old beliefs.
- Solution: Implement a bandit algorithm designed for non-stationary environments, which can forget old information and adapt to new data more quickly [42].
Issue 2: Poor Performance with a Large Number of Options (Arms)
Symptoms:
- The algorithm takes an impractically long time to converge.
- Performance is significantly worse than with a smaller number of arms.
Possible Causes and Solutions:
- Cause: Priming Rounds Overhead. Algorithms like UCB and Optimistic Greedy require trying each arm once before making informed decisions. With 1000 arms, this means 1000 initial experiments with no optimization [41].
- Cause: Lack of Context. With many arms, simple bandits lack the information to generalize.
- Solution: Implement a Contextual Bandit. By using features of the arms or the experimental conditions (e.g., chemical properties of drugs, strain genotypes), the algorithm can learn a policy that generalizes across arms, drastically improving sample efficiency [39].
Issue 3: Algorithm is Overly Sensitive to Parameter Settings
Symptoms:
- Small changes in hyperparameters (like
εor the UCB confidence parameter) lead to large swings in performance. - Difficulty in finding a single parameter set that works across different experimental batches.
Possible Causes and Solutions:
- Cause: Fixed Hyperparameters. Using a static, non-adaptive value for parameters like
εin Epsilon-Greedy.- Solution: Use adaptive methods. For example, the VDBE strategy dynamically adjusts
εbased on the value function's variance. Alternatively, Thompson Sampling is often more robust because it inherently adapts its exploration based on the uncertainty (variance) of its posterior distributions and typically requires fewer parameters to tune [41] [42].
- Solution: Use adaptive methods. For example, the VDBE strategy dynamically adjusts
Quantitative Algorithm Comparison
The following table summarizes the key characteristics of the three core algorithms to guide your selection.
| Algorithm | Key Mechanism | Best For | Strengths | Weaknesses |
|---|---|---|---|---|
| Epsilon-Greedy | With probability ε, explore a random arm; otherwise, exploit the best-known arm. |
Simple, quick-to-implement prototypes; stationary environments with a small number of arms [41] [40]. | Simple to understand and implement. | Performance is highly sensitive to the choice of ε; can waste pulls on clearly suboptimal arms [41]. |
| Upper Confidence Bound (UCB) | Selects the arm with the highest upper confidence bound, balancing estimated reward and uncertainty. | Scenarios where deterministic confidence bounds are needed; problems with a well-defined horizon [44]. | Provides a deterministic, principled bound for exploration. | Requires an initial play of all arms; can be slow to start with a very large number of arms [41]. |
| Thompson Sampling | Uses Bayesian inference; selects an arm by sampling from the posterior distribution of each arm's reward. | Complex, non-stationary environments; high-dimensional problems; when parameter tuning is difficult [41] [43] [42]. | Highly performant and robust; naturally incorporates uncertainty. | Computationally more intensive than Epsilon-Greedy; requires specifying a prior distribution [41]. |
Experimental Protocol: Media Optimization via Active Learning
This protocol is adapted from a study that used the Automated Recommendation Tool (ART) to optimize flaviolin production in Pseudomonas putida [45].
1. Objective: To identify the optimal concentrations of media components to maximize the titer of a target metabolite.
2. Experimental Setup:
- Host Organism: Engineered Pseudomonas putida KT2440.
- Target Metabolite: Flaviolin.
- Culture Platform: Automated cultivation in a BioLector system (48-well plates).
- Analysis: Absorbance at 340 nm as a high-throughput proxy for flaviolin concentration.
3. Algorithm Integration (Active Learning Loop):
- Step 1 (Design): The ML algorithm (e.g., a bandit model or ART) suggests a batch of ~15 new media designs (i.e., specific concentration combinations of components like salts, carbon, and nitrogen sources).
- Step 2 (Build): An automated liquid handler physically prepares the suggested media in replicates according to the design.
- Step 3 (Test): The media are inoculated and cultivated in the BioLector for 48 hours. The production titer is measured.
- Step 4 (Learn): The production data and media designs are stored in a database (e.g., Experiment Data Depot). This data is used to retrain the ML model, which then generates improved recommendations for the next cycle.
- This DBTL cycle is repeated until performance plateaus or the experimental budget is exhausted [45].
4. Key Findings:
- The active learning process led to a 60-70% increase in titer and a 350% increase in process yield.
- Explainable AI techniques identified that common salt (NaCl) was the most important component, with an optimal concentration near the tolerance limit of the bacteria [45].
Workflow Visualization
The following diagram illustrates the integration of a bandit algorithm into an automated Design-Build-Test-Learn (DBTL) cycle for biological optimization.
Research Reagent Solutions
The table below lists key computational and experimental "reagents" essential for implementing bandit algorithms in biological DBTL research.
| Item | Function/Description | Example Use Case |
|---|---|---|
| Automated Cultivation System (e.g., BioLector) | Provides highly reproducible culture conditions and online monitoring of growth and production metrics [45]. | Essential for the "Test" phase, generating the high-quality, consistent data needed for ML models. |
| Automated Liquid Handler | Precisely dispenses media components and inoculants according to digital designs generated by the algorithm [45]. | Critical for the "Build" phase, enabling rapid and error-free physical implementation of suggested experiments. |
| Data Repository (e.g., Experiment Data Depot - EDD) | A centralized database to store all experimental metadata, conditions, and outcome data [45]. | Serves as the memory for the DBTL cycle, ensuring data is structured and accessible for the "Learn" phase. |
| Thompson Sampling Library (e.g., in Python) | A pre-built implementation of the Thompson Sampling algorithm for Bernoulli or other relevant reward distributions. | Allows researchers to integrate a powerful bandit algorithm into their active learning loop without building it from scratch. |
| Contextual Feature Set | A curated list of measurable features (e.g., genetic markers, protein expressions, chemical properties) that describe each experimental unit [39]. | Enables the use of Contextual Bandits for personalized medicine or stratified optimization. |
Bayesian Optimization as a Superior Framework for DBTL Cycles
Frequently Asked Questions
Q1: What is the primary advantage of using Bayesian Optimization over simpler methods like Grid or Random Search in a DBTL cycle? Bayesian Optimization (BO) is superior in scenarios where each function evaluation is expensive, such as building and testing a new microbial strain. Unlike Grid or Random Search, which evaluate parameters in isolation, BO uses a probabilistic surrogate model to approximate the objective function and an acquisition function to intelligently select the next most promising parameters to evaluate. This informed approach allows it to focus on high-performance regions of the parameter space, typically requiring far fewer experimental cycles to find the optimal solution [46] [47].
Q2: How does BO balance the exploration of new regions with the exploitation of known promising areas? BO manages the exploration-exploitation trade-off through its acquisition function. Exploration involves sampling areas of high uncertainty in the surrogate model, while exploitation focuses on areas likely to give a better result than the current best. Functions like Expected Improvement (EI) and Upper Confidence Bound (UCB) naturally balance this trade-off by mathematically combining the predicted mean (exploitation) and uncertainty (exploration) of the surrogate model [48] [49] [47].
Q3: Our initial data is limited. Can BO still be effective in such a low-data regime? Yes. Evidence from simulated DBTL cycles shows that machine learning methods like Random Forest and Gradient Boosting, which can be used within a BO-like framework, are robust and perform well even when starting with limited data. These methods are particularly effective for combinatorial pathway optimization before large amounts of experimental data have been collected [50].
Q4: Why might my BO process fail to find the global optimum, and how can I fix it? Common pitfalls in BO include an incorrect prior width, over-smoothing, and inadequate maximization of the acquisition function [51].
- Incorrect Prior Width: If the prior assumptions about the function are too narrow or too wide, the model may converge to a local optimum or learn too slowly. Fix: Adjust the length-scale and amplitude parameters of the kernel function to better match the characteristics of your system.
- Over-smoothing: This occurs when the model fails to capture important, sharp variations in the response landscape. Fix: Consider using a combination of kernels or adjusting kernel parameters to allow for more flexibility.
- Inadequate Acquisition Maximization: If the search for the maximum of the acquisition function is not thorough, a sub-optimal point may be selected. Fix: Ensure you are using a robust optimizer for this inner loop and consider using multiple restarts to find the global maximum of the acquisition function [51].
Q5: How can we accelerate the traditionally slow Build-Test phases of the DBTL cycle to generate data faster for BO? Integrating cell-free expression systems can dramatically accelerate the Build-Test phases. These systems allow for rapid, high-throughput synthesis and testing of proteins or pathways without the need for live cells, enabling megascale data generation. This provides the large, high-quality datasets needed to efficiently train and validate machine learning models, including those used in BO [35].
Comparison of Acquisition Functions in Bayesian Optimization
The choice of acquisition function is critical as it directly governs the trade-off between exploration and exploitation. The table below summarizes key functions.
| Acquisition Function | Mechanism | Best For | Key Parameter(s) |
|---|---|---|---|
| Probability of Improvement (PI) | Selects point with the highest probability of improving over the current best value [48]. | Situations where a quick, incremental improvement is desired. | ϵ : Controls exploration; a larger ϵ encourages more exploration [48]. |
| Expected Improvement (EI) | Selects point with the largest expected improvement over the current best, balancing the amount of improvement and its probability [48] [47]. | General-purpose use; a good default choice for many applications. | ζ : Balances exploration and exploitation [47]. |
| Upper Confidence Bound (UCB) | Uses an optimistic estimate: mean prediction plus a multiple of the standard deviation (uncertainty) [48]. | Problems where a clear and direct balance between mean and uncertainty is needed. | β : Explicitly controls the trade-off; higher β favors exploration [51]. |
Experimental Protocol: Implementing BO for Combinatorial Pathway Optimization
This protocol outlines the methodology for using BO to optimize a metabolic pathway in an iterative DBTL cycle, based on a kinetic model-based framework [50].
1. Problem Definition and Initial Setup
- Objective: Define the engineering goal, such as maximizing the production titer of a target compound.
- Design Variables: Identify the factors to optimize (e.g., enzyme concentrations, promoter strengths).
- Kinetic Model: Establish a mechanistic kinetic model of the metabolic pathway embedded in a relevant cell physiology model. This model will be used to simulate the "Test" phase and generate in silico data for benchmarking the BO strategy [50].
2. Construction of the Initial Dataset
- Library Design: Define a DNA library of components (e.g., promoters, RBS) that will modulate the design variables.
- Initial Sampling: Build and test (or simulate) an initial set of strain designs. This can be done via Latin Hypercube Sampling or Random Sampling to ensure a good coverage of the design space. This dataset,
D_{1:t}, forms the initial training data for the surrogate model [50].
3. Configuration of the Bayesian Optimization Loop
- Surrogate Model: Select a probabilistic model. A common choice is a Gaussian Process (GP), which provides a mean and variance for its predictions. For low-data regimes, Random Forest or Gradient Boosting models have been shown to be effective and robust [50] [51].
- Acquisition Function: Choose an acquisition function such as Expected Improvement (EI).
- Optimization: For each iteration
tof the cycle: a. Fit the Surrogate Model: Train the model on all dataD_{1:t}collected so far. b. Maximize Acquisition: Find the next point to evaluate:x_{t+1} = argmax α(x; D_{1:t}). c. Evaluate: "Test" the new designx_{t+1}using the kinetic model (or experimentally) to obtain the performance valuey_{t+1}. d. Update: Augment the dataset:D_{1:t+1} = {D_{1:t}, (x_{t+1}, y_{t+1})[50] [47].
4. Iteration and Convergence
- Repeat step 3 for a predetermined number of cycles or until performance converges to a satisfactory level.
- Studies suggest that when the experimental budget is limited, starting with a larger initial DBTL cycle can be more favorable than distributing the same number of tests evenly across many small cycles [50].
Bayesian Optimization Integrated DBTL Cycle
The Scientist's Toolkit: Key Research Reagents & Solutions
| Item / Reagent | Function in Experiment | |
|---|---|---|
| Gaussian Process (GP) Surrogate Model | A probabilistic model that provides a flexible, non-parametric approximation of the unknown objective function (e.g., strain performance) and quantifies prediction uncertainty [47] [51]. | |
| Tree Parzen Estimator (TPE) | An alternative surrogate model algorithm used in libraries like Hyperopt; it models `p(x | y)` using two densities for "good" and "bad" performances, which can be more efficient in high dimensions [46]. |
| Cell-Free Expression System | A platform derived from cellular lysates or purified components that enables rapid, high-throughput in vitro transcription and translation. It drastically speeds up the Build-Test phases by bypassing cell culture and transformation [35]. | |
| Mechanistic Kinetic Model | A computational model based on ordinary differential equations that simulates the dynamics of a metabolic pathway. It is used to generate in silico data for benchmarking DBTL strategies and machine learning algorithms before costly real-world experiments [50]. | |
| Hyperopt | A Python library for serial and parallel Bayesian optimization that uses the TPE algorithm to efficiently search hyperparameter spaces [46]. |
Bayesian Optimization Core Loop
Gaussian Processes and Acquisition Functions for Guided Experimentation
Frequently Asked Questions
What is the core challenge in guided experimentation that Gaussian Processes help solve? Gaussian Processes (GPs) address the challenge of optimizing black-box, expensive, and multi-extremal functions where the analytical form is unknown. They provide a probabilistic surrogate model that approximates the unknown function based on sequentially collected observations, quantifying uncertainty in unobserved areas [49] [52].
How do acquisition functions balance exploration and exploitation? Acquisition functions use the GP's predictions to determine the next experiment by balancing exploration (probing uncertain regions) and exploitation (focusing on known promising areas). This trade-off is fundamental to efficient sequential decision-making in experimental design [49] [53] [52].
My Bayesian Optimization converges to a local optimum instead of the global one. What might be wrong? This is typically caused by insufficient exploration. Try increasing the exploration weight (λ) if using Upper Confidence Bound, or switch to an acquisition function like Expected Improvement that more explicitly balances exploring uncertain regions with exploiting known good areas [52].
The optimization process is slow despite few experiments. How can I improve performance? Consider using a sparse GP approximation if you have many data points, reduce the dimensionality of your search space, or use a simpler kernel. Also, ensure you're not using an overly complex acquisition function that's computationally expensive to optimize [52].
How much initial data do I need before the GP becomes useful? For reliable performance, it's recommended to have more than three weeks of data for periodic processes or a few hundred data points for non-periodic data. As a rule of thumb, you need at least as much data as you want to forecast [54].
Troubleshooting Guides
Poor Model Performance
Symptoms
- The GP model fails to identify promising experimental conditions
- High prediction error on validation data points
- Optimization consistently selects suboptimal parameters
Potential Causes and Solutions
| Cause | Diagnostic Steps | Solution |
|---|---|---|
| Insufficient initial data | Check if model uncertainty is high across entire space | Collect more diverse initial samples before optimization; ensure coverage of parameter space [54] |
| Inappropriate kernel selection | Analyze residuals for patterns | Switch to more expressive kernels (Matérn for flexibility); use composite kernels for complex patterns [52] |
| Overfitting to noisy observations | Check if model fits noise rather than trend | Increase regularization; use a WhiteKernel to explicitly model noise [55] |
Acquisition Function Failures
Symptoms
- Optimization gets stuck in local optima
- Too much exploration without convergence
- Too much exploitation, missing better regions
Troubleshooting Table
| Problem | Acquisition Function Adjustments | Alternative Approaches |
|---|---|---|
| Stuck in local optima | Increase λ in UCB; use EI or PI with larger exploration parameters | Implement a hybrid strategy with periodic random exploration [49] [52] |
| Excessive exploration | Decrease λ in UCB; use decoupled exploitation/exploitation scheduling | Switch to Expected Improvement which naturally balances both [52] |
| Poor convergence | Normalize parameter spaces to equal scales | Use a novel adaptive acquisition function that dynamically adjusts trade-off [49] |
Implementation and Computational Issues
Symptoms
- Long computation times between experiments
- Memory errors with many data points
- Numerical instability in GP predictions
Solutions
| Issue | Mitigation Strategy | Technical Implementation |
|---|---|---|
| Slow predictions | Use sparse variational GPs | Implement inducing point methods to reduce complexity from O(n³) to O(m²n) |
| High memory usage | Implement data batching | Process data in chunks; use iterative solvers instead of direct matrix inversion |
| Numerical instability | Add jitter to covariance matrix | Ensure positive definiteness with small diagonal additions to kernel matrix |
Acquisition Function Comparison
The table below summarizes key acquisition functions for Bayesian Optimization:
| Acquisition Function | Exploration-Exploitation Balance | Key Parameters | Best Use Cases |
|---|---|---|---|
| Upper Confidence Bound (UCB) | Explicit balance via λ parameter | λ (exploration weight) | Controlled trade-off, tunable exploration [52] |
| Probability of Improvement (PI) | Exploitation-biased | Current best value | Refining known good solutions [52] |
| Expected Improvement (EI) | Balanced, considers improvement magnitude | Current best value | General-purpose optimization [52] |
| Novel Adaptive Functions | Dynamic, self-adjusting | Adaptive based on search progress | Complex, multi-modal functions [49] |
Experimental Protocols
Standard Bayesian Optimization Workflow
Objective: Sequentially optimize an expensive black-box function Materials: Experimental apparatus, data collection system, computational resources
Procedure:
- Design Space Definition: Define parameter bounds and constraints
- Initial Design: Collect initial data points using space-filling design (Latin Hypercube)
- GP Model Training:
- Select appropriate kernel based on expected function properties
- Optimize hyperparameters via maximum likelihood estimation
- Validate model on held-out data if available
- Acquisition Function Optimization:
- Select acquisition function based on optimization goals
- Optimize to identify next experiment
- Experimental Execution:
- Run experiment at suggested parameters
- Record outcome metrics
- Model Update:
- Incorporate new data into GP model
- Update hyperparameters if necessary
- Iteration: Repeat steps 4-6 until convergence or budget exhaustion
Model Validation Protocol
Purpose: Ensure GP model quality before relying on predictions
Validation Metrics Table:
| Metric | Calculation | Target Value |
|---|---|---|
| Predictive log-likelihood | Mean log probability of test data | Higher values indicate better fit |
| Normalized RMSE | RMSE normalized by data standard deviation | < 0.5 indicates good predictive accuracy |
| Calibration error | Difference between predicted and empirical confidence intervals | < 0.1 indicates well-calibrated uncertainty |
The Scientist's Toolkit: Research Reagent Solutions
| Item | Function in Guided Experimentation |
|---|---|
| Gaussian Process Framework | Provides probabilistic surrogate model for the unknown response surface [49] [52] |
| Acquisition Functions | Guides experiment selection by balancing exploration and exploitation [49] [52] |
| Bayesian Optimization Library | Implements the sequential decision-making loop (e.g., Scikit-optimize, GPyOpt) |
| Domain-Specific Simulators | Enables in silico testing before wet-lab experiments [56] |
| Secure Data Hub | Manages experimental data with privacy preservation for collaborative research [56] |
Workflow Visualization
Multi-Armed Bandit Frameworks for High-Throughput Strain Screening
Core Concepts: MAB, A/B Testing, and the Exploration-Exploitation Dilemma
What is the fundamental difference between a classic A/B test and a Multi-Armed Bandit (MAB) approach?
The core difference lies in how they manage traffic (or resource) allocation and their primary goal. A classic A/B test is focused on data collection and statistical confidence. It runs with a fixed, equal split of traffic between variants (e.g., 50/50) for the entire duration until a statistically significant winner is found. This ensures highly reliable results but at the cost of potentially losing conversions by sending traffic to underperforming variants [57] [58].
In contrast, a Multi-Armed Bandit is focused on maximizing cumulative conversions or rewards during the test itself. It dynamically reallocates traffic away from poorly performing variants and toward the better-performing ones in real-time, using a machine learning algorithm. This reduces the opportunity cost of running the experiment but may provide less statistical certainty about the exact performance of all variants [57].
How does the "Multi-Armed Bandit" analogy relate to strain screening?
The name comes from a thought experiment involving a gambler facing multiple slot machines ("one-armed bandits") [57]. In strain screening, you can think of it as follows:
- Bandit / Arm: Each distinct strain variant in your screening library is an "arm."
- Pull: Testing a strain in a single experiment (e.g., in a well of a microplate) is a "pull" of that arm.
- Payout / Reward: The measured output or Key Performance Indicator (KPI) you are optimizing for, such as enzymatic activity, titer, or growth rate.
What is the Exploration vs. Exploitation trade-off?
This is the central problem the MAB algorithm is designed to solve [57].
- Exploration: Allocating screening resources to less-tested strains to gather more data on their potential performance. This prevents you from missing a potentially superior strain that had an unlucky start.
- Exploitation: Allocating the majority of screening resources to the strain that currently shows the best performance to maximize the cumulative reward during the screening campaign.
A successful MAB strategy automatically and continuously balances these two competing goals.
Implementing MAB for Strain Screening: Protocols and Workflows
The following workflow integrates MAB into a semi-automated, high-throughput screening process for identifying optimal biological strains, drawing from a real-world application in screening catalytically active inclusion bodies (CatIBs) [59].
Detailed Experimental Protocol
This protocol outlines the key steps for a MAB-driven screening cycle, as successfully applied in a microbial strain screening study [59].
Phase 1: Design & Build (Strain Library Construction)
- Objective: Generate a diverse library of strain variants. In the case study, 63 CatIB variants of a glucose dehydrogenase enzyme were created by fusing different aggregation-inducing tags and linkers to the gene [59].
- Methodology:
- Semi-Automated Cloning: Utilize automated cloning techniques like Golden Gate Assembly on a liquid-handling robotic platform to enable parallel construction of up to 96 variants simultaneously.
- Workload Reduction: The cited study reduced manual workload for 48 variants from 59 hours to just 7 hours (an 88% reduction) through this automation [59].
- Sequence Verification: Verify all constructed plasmids via sequencing.
Phase 2: Test (High-Throughput Cultivation & Assay)
- Objective: Cultivate strains and measure their performance (reward) in a high-throughput format.
- Methodology:
- Cultivation: Use an automated microbioreactor system (e.g., a BioLector with a FlowerPlate) for parallel, small-scale cultivation of all strains under controlled conditions. The case study optimized this step to exclude plate position effects [59].
- Assay and Purification: Implement an automated, miniaturized protocol for cell lysis and purification of the product of interest (e.g., catalytically active inclusion bodies). This involves centrifugation, washing, and resuspension steps handled by a liquid-handling robot [59].
- Data Collection: Measure the key performance indicator (KPI), such as enzymatic reaction rate, for each variant in the assay.
Phase 3: Learn (Bayesian Modeling & Decision)
- Objective: Use the collected data to model strain performance and intelligently select the next batch of strains to test.
- Methodology:
- Bayesian Process Model: A statistical model is updated with the results from the "Test" phase. This model estimates the performance (e.g., conversion rate) of each strain variant and the uncertainty around that estimate [59].
- Thompson Sampling: This MAB algorithm is used to select the next set of strains for the screening batch. It works by sampling from the probability distribution of each strain's performance provided by the Bayesian model. This means a strain with a high estimated performance (exploitation) or high uncertainty (exploration) has a probability of being selected, perfectly balancing the trade-off [59]. In the referenced study, the best-performing variant was selected in 50 out of the total biological replicates across three screening rounds due to its high probability of being optimal [59].
Troubleshooting Common MAB Screening Issues
FAQ 1: Our MAB algorithm seems to have converged on a sub-optimal strain too early. How can we encourage more exploration?
- Problem: This is a classic sign of insufficient exploration, potentially due to an algorithm that is too greedy.
- Solution:
- Review Algorithm Parameters: If you are using a method like Thompson Sampling, ensure the prior distributions are set appropriately. A less informative (e.g., broader) prior can encourage more exploration in early rounds.
- Implement a Minimum Sampling Rate: Enforce a rule that every strain variant, including poor performers, receives a minimum percentage of screening resources (e.g., 1-5% of wells) in each batch to ensure continuous exploration.
- Incorporate Domain Knowledge: Manually "force-in" promising variants based on structural knowledge or previous experiments that the algorithm may be underestimating.
FAQ 2: The noise in our high-throughput assay is high, leading to unstable performance rankings. How can we make the MAB more robust?
- Problem: High measurement variance can trick the algorithm into favoring a strain that had a lucky measurement.
- Solution:
- Increase Replicates: For the top-performing strains identified by the MAB, run additional technical or biological replicates to get a more robust estimate of their performance before fully exploiting them.
- Bayesian Modeling with Noise Estimation: Use or develop a Bayesian model that explicitly accounts for and estimates the measurement noise in its internal calculations, making it less sensitive to outliers.
- Smoothing Rewards: Instead of using a single raw measurement, use a moving average of the last few measurements for a given strain as the "reward" input to the MAB algorithm.
FAQ 3: We need to screen for multiple KPIs (e.g., high activity AND high growth). How can a MAB handle multi-objective optimization?
- Problem: A standard MAB typically optimizes for a single reward metric.
- Solution:
- Define a Composite Reward: Create a single, weighted reward function that combines all your KPIs. For example,
Reward = (0.7 * Activity) + (0.3 * Growth). This requires careful consideration of the weights to reflect business priorities. - Use Advanced Bandits: Implement more sophisticated bandit algorithms designed for multiple objectives, such as Pareto-optimization techniques, which seek to find a set of non-dominated optimal solutions.
- Define a Composite Reward: Create a single, weighted reward function that combines all your KPIs. For example,
The Scientist's Toolkit: Essential Research Reagents & Materials
The following table details key materials and solutions used in the featured automated MAB screening workflow for enzyme-producing strains [59].
| Item/Reagent | Function in the Screening Workflow |
|---|---|
| Golden Gate Assembly System | A fast and automatable DNA assembly method used for the parallel construction of many genetic variants (e.g., CatIB fusions) in the Build phase [59]. |
| Microbioreactor System (e.g., BioLector) | Enables high-throughput, parallel cultivation of strain variants with online monitoring of metrics like biomass, a critical component of the Test phase [59]. |
| Phenotype Microarray Plates (e.g., Biolog PM) | High-throughput platform for profiling the functional diversity and metabolic capabilities of strains by testing their growth on hundreds of carbon sources or under different conditions [60]. |
| Liquid-Handing Robot | The core automation hardware that executes repetitive pipetting tasks for cloning, assay setup, and purification steps across the entire DBTL cycle [59] [61]. |
| BugBuster Reagent | A ready-to-use formulation for efficiently lysing bacterial cells in a high-throughput format to release the product of interest (e.g., enzymes or CatIBs) for analysis in the Test phase [59]. |
| Thompson Sampling Algorithm | The core MAB algorithm used in the Learn phase to balance exploration and exploitation by sampling from the posterior distributions of strain performances [59]. |
The following table summarizes key quantitative outcomes from a published study that successfully employed a MAB framework for high-throughput screening of catalytically active inclusion bodies (CatIBs) [59]. This provides a realistic benchmark for expected efficiencies.
| Metric | Outcome | Context / Implication |
|---|---|---|
| Manual Workload Reduction | 88% reduction (59 to 7 hours for 48 variants) [59] | Achieved through semi-automated cloning, demonstrating a massive efficiency gain in the Build phase. |
| Screening Throughput | 63 variants analyzed in only three batch experiments [59] | Highlights the speed of the MAB-driven DBTL cycle compared to testing all variants exhaustively. |
| Variant Construction Success Rate | 83% (63 out of 76 constructs) [59] | Indicates the reliability of the semi-automated Build workflow (Golden Gate Assembly). |
| Assay Reproducibility | 1.9% relative standard deviation across 42 replicates [59] | Confirms the high precision and reliability of the automated Test phase assay. |
| Algorithm Selection Bias | Best performer selected in 50 biological replicates [59] | Demonstrates the effective "exploitation" behavior of the Thompson sampling algorithm, which heavily favored the most promising variant. |
In metabolic engineering, the Design-Build-Test-Learn (DBTL) cycle is the cornerstone for developing efficient microbial cell factories. A fundamental challenge within this cycle is the explore-exploit dilemma: researchers must balance the effort between exploring a wide genetic design space to discover novel high-performing strains (exploration) and focusing resources on optimizing the most promising candidates to maximize production metrics (exploitation) [12]. Combinatorial pathway optimization has emerged as a powerful strategy that primarily addresses the exploration phase. It involves the simultaneous, multivariate modification of multiple genetic parts in a pathway, enabling the rapid generation of vast diversity and the identification of global optima that are often inaccessible through traditional, sequential methods [62] [63]. This approach is computationally hard and requires sophisticated strategies to navigate the immense possibility space effectively [12]. This technical support document provides troubleshooting guidance and foundational methodologies for implementing combinatorial optimization, with a consistent focus on its role in balancing exploration and exploitation in machine learning-driven DBTL research.
Core Concepts: Combinatorial vs. Sequential Optimization
Frequently Asked Questions (FAQs)
Q1: What is the fundamental difference between combinatorial and sequential pathway optimization? A1: Sequential optimization is a univariate method where major bottlenecks in a pathway are identified and conquered one at a time. In contrast, combinatorial optimization is a multivariate approach where multiple parts of a pathway (e.g., promoters, RBSs, gene copies) are varied and tested synergistically and simultaneously. This allows for the systematic screening of a multidimensional design space to find a global optimum [62].
Q2: Why is combinatorial optimization particularly suited for the 'exploration' phase of the DBTL cycle? A2: Combinatorial optimization is a powerful tool for exploration because it efficiently generates a large and diverse set of genetic constructs. This broad exploration helps overcome the limited a priori knowledge about intricate pathway interactions and allows researchers to map the performance landscape, thereby identifying non-intuitive, high-performing strain designs that would be missed by rational, sequential design alone [64] [63].
Q3: What are the primary technical challenges when building combinatorial DNA libraries? A3: The main challenges include:
- Library Size: Managing the exponential growth of library size as more variables are added, which necessitates strategies to keep experimental effort affordable [64].
- Assembly Efficiency: Finding DNA assembly methods that can efficiently and reliably assemble multiple DNA fragments in parallel without sequence limitations [62].
- Screening Throughput: Developing high-throughput screening or selection methods to identify the best-performing variants from thousands of constructs [63].
Q4: How can machine learning help balance exploration and exploitation in this context? A4: While the provided search results do not detail specific machine learning algorithms, they establish the core dilemma. Machine learning models can use initial combinatorial library data (exploration) to learn the relationship between genetic design and performance. The model can then guide subsequent DBTL cycles by predicting which designs are most likely to be high-performing, thereby focusing resources on exploiting the most promising regions of the design space.
Strategy Comparison Table
The choice between combinatorial and sequential optimization fundamentally shapes your DBTL cycle. The table below summarizes their key characteristics.
Table 1: Comparison of Sequential and Combinatorial Optimization Strategies
| Feature | Sequential Optimization | Combinatorial Optimization |
|---|---|---|
| Philosophy | Debug and optimize one variable at a time [62] | Synergistically test and optimize all variable parts simultaneously [62] |
| Approach | Univariate | Multivariate [63] |
| Design Space Coverage | Limited and local; can miss global optima [62] | Broad and systematic; can identify global optima [62] |
| Typical Scale | Tests <10 constructs at a time [62] | Tests hundreds to thousands of constructs in parallel [62] |
| Primary DBTL Phase | Exploitation (focused optimization) | Exploration (broad search) |
| Suitability | Well-understood pathways with known major bottlenecks | Complex pathways with unknown or interacting bottlenecks [64] |
Troubleshooting Common Experimental Issues
FAQ & Troubleshooting Guide
Q1: Our combinatorial library shows high variability, but no clones exhibit significant improvement over the baseline. What could be wrong? A1: This is often a sign of an exploration strategy that is too random or unfocused.
- Potential Cause: The genetic parts (e.g., promoter strengths) being varied may not span an appropriate range, or a critical bottleneck may lie outside the targeted variables.
- Solution:
- Re-evaluate Design Space: Use available literature or pre-screening to ensure the library of parts covers a sufficiently wide but relevant range of expression strengths. Consider applying a "biased" or "directed" exploration strategy, where the variation is informed by prior knowledge [12].
- Expand Variables: The bottleneck might be in a different part of the pathway or host metabolism. Consider expanding your combinatorial library to include other elements like terminator strength, protease tags, or host-genome modifications [63].
Q2: We successfully built a large combinatorial library but are struggling to identify high producers with our screening method. A2: This is a classic bottleneck in high-throughput exploration.
- Potential Cause: The screening method may be too low-throughput, not sensitive enough, or may not accurately correlate with the final production metric (e.g., titer, yield, rate).
- Solution:
- Implement Biosensors: Develop or utilize genetically encoded biosensors that transduce the production of your target metabolite into an easily detectable fluorescence signal. This allows for high-throughput screening using flow cytometry [63].
- Use Advanced Regulators: Employ orthogonal, inducible transcription factors (e.g., based on CRISPR/dCas9, TALEs, or plant-derived TFs) to create more dynamic and sensitive control systems that can amplify production differences [63].
Q3: Our best-performing strain from the library is genetically unstable and loses productivity over time. A3: This is a common problem when moving from exploration (finding a top performer) to exploitation (stabilizing it for scale-up).
- Potential Cause: Metabolic burden from the over-expression of heterologous pathways can lead to the selection for non-productive mutants that grow faster [65].
- Solution:
- Dynamic Metabolic Control: Implement a two-stage dynamic control system. Decouple cell growth from product formation by using metabolic valves or inducible systems. This allows cells to grow robustly first before switching to a high-production state, reducing the selective advantage of non-producers [65].
- Genomic Integration: Instead of using multi-copy plasmids, integrate the optimized pathway into the host genome at one or more specific loci to improve genetic stability [63].
Experimental Protocols for Key Techniques
Protocol 1: COMPACTER (Customized Optimization of Metabolic Pathways by Combinatorial Transcriptional Engineering) [66]
Principle: This method creates a library of mutant pathways by de novo assembly of promoter mutants of varying strengths for each gene in a target pathway.
Methodology:
- Design: For each gene in your heterologous pathway, select a set of promoters with known but varying strengths. These can be native promoters, synthetic libraries, or mutated versions of a single promoter.
- Build: Use a high-throughput DNA assembly method (e.g., Golden Gate Assembly, in vivo homologous recombination) to combinatorially assemble the different promoters with their corresponding genes. This creates a library of pathway variants where each gene is expressed from a different promoter combination.
- Test: Transform the assembled library into your host strain (e.g., laboratory or industrial yeast/E. coli strains). Screen or select for clones with high production of the target metabolite using a high-throughput method (e.g., biosensors coupled with flow cytometry, microtiter plate assays).
- Learn: Isolate the best-performing clones and sequence the promoter regions to understand the optimal expression profile for your specific pathway and host background.
Protocol 2: Direct Combinatorial Pathway Optimization via SSA and Golden Gate [67]
Principle: This workflow combines Single Strand Assembly (SSA) and Golden Gate Assembly to efficiently introduce sequence variability and assemble lengthy multigene pathways with a minimum of intermediary steps.
Methodology:
- Library Generation: Use SSA to generate diversified libraries of individual genetic parts (e.g., RBS libraries, gene variants).
- Pathway Assembly: Employ Golden Gate Assembly, which uses Type IIS restriction enzymes, to seamlessly combine the diversified parts into a full multigene pathway construct. The strength of this method is its ability to assemble multiple fragments in a single reaction without leaving scars.
- Validation: Transform the assembled combinatorial library into the production host (e.g., E. coli).
- Screening: As a proof-of-principle, screen for a visual phenotype (e.g., lycopene production, which is red) to identify high-producing colonies. These can be further quantified using analytical methods like HPLC.
Essential Visualizations
Workflow for Combinatorial Pathway Optimization
This diagram illustrates the core DBTL cycle, highlighting how combinatorial optimization drives the initial exploration phase and how insights can be fed into machine learning models to inform future cycles.
The Explore-Exploit Dilemma in Strategy Selection
This decision tree helps frame the strategic choice between combinatorial and sequential approaches based on project goals and prior knowledge, directly linking to the explore-exploit dilemma.
The Scientist's Toolkit: Research Reagent Solutions
The following table details key reagents and tools essential for executing combinatorial pathway optimization projects.
Table 2: Key Research Reagent Solutions for Combinatorial Optimization
| Tool / Reagent | Function | Key Considerations |
|---|---|---|
| Golden Gate Assembly | A DNA assembly method using Type IIS restriction enzymes to efficiently combine multiple DNA fragments in a single reaction [67]. | High efficiency for >5 fragments; has sequence limitations (cannot have internal enzyme cutting sites) [62]. |
| GenBuilder Assembly Platform | A proprietary high-throughput DNA assembly platform capable of assembling up to 12 parts in one round with no sequence limitations [62]. | Enables parallel assembly of up to 108 constructs in one library design, ideal for building large combinatorial libraries [62]. |
| Orthogonal ATFs (Actuator) | Advanced Transcription Factors (e.g., based on dCas9, TALEs, plant TFs) used to precisely control the timing and level of gene expression [63]. | Allows for dynamic control; can be induced by chemicals or light (optogenetics); size and toxicity can be concerns [63]. |
| Whole-Cell Biosensors (Sensor) | Genetically encoded circuits that detect the intracellular concentration of a metabolite and transduce it into a measurable output (e.g., fluorescence) [63] [65]. | Essential for high-throughput screening; must be sensitive, specific, and have a dynamic range that covers relevant production levels [63]. |
| CRISPR/Cas-based Editing | Advanced genome-editing tools used for multi-locus integration of combinatorial pathway constructs directly into the host genome [63]. | Improves genetic stability compared to plasmid-based expression; enables larger and more complex library integrations [63]. |
Machine Learning for Automated Recommendation in Iterative Strain Design
This technical support center is designed for researchers and scientists employing machine learning (ML) to automate recommendations within the iterative Design-Build-Test-Learn (DBTL) cycle for microbial strain design. A core challenge in this field is effectively balancing exploration (searching new areas of the biological design space) with exploitation (refining known promising designs). The guides and FAQs below address common technical issues, provide structured data, and outline methodologies to help you implement and troubleshoot these advanced workflows.
Frequently Asked Questions (FAQs)
FAQ 1: What is the fundamental trade-off in ML-driven strain optimization? The core trade-off is between exploration and exploitation. Exploration involves testing new, genetically diverse strains to map the fitness landscape broadly and avoid local optima. Exploitation involves focusing experiments on regions of the design space known to have high performance to refine and improve promising candidates. A successful ML algorithm must balance these two competing goals to efficiently find the global optimum with minimal experimental cycles [68] [69].
FAQ 2: Which ML algorithms are best suited for balancing exploration and exploitation? Several algorithms are designed for this balance, particularly in data-scarce, expensive experimental environments.
- Bayesian Optimization (BO) is a leading model-free approach. It uses a probabilistic surrogate model (like a Gaussian Process) to predict strain performance and an acquisition function (like Expected Improvement) to recommend the next most informative experiments by automatically balancing exploring uncertain regions and exploiting known high-performing areas [68].
- Multi-Agent Reinforcement Learning (MARL) is another powerful, model-free method. It utilizes multiple "agents" to propose parallel strain modifications based on previous experimental outcomes, making it highly efficient for plate-based screening. It learns a policy that maps the state of the system (e.g., metabolite levels) to optimal actions (e.g., changes in enzyme levels) [70].
- Evolutionary Algorithms perform a stochastic search of the genetic space, using mechanisms like mutation and crossover to explore new designs while selecting the best-performing variants for the next iteration [71].
FAQ 3: Why is my ML model failing to improve after several DBTL cycles? This is a common issue often referred to as stagnation or convergence to a local optimum.
- Cause 1: Insufficient Exploration. The algorithm may be too greedily exploiting a small region of the design space.
- Troubleshooting: Adjust your algorithm's hyperparameters to increase exploration. For Bayesian Optimization, this could mean tuning the acquisition function to favor uncertainty more highly [68].
- Cause 2: Experimental Noise. High variability in your "Test" phase data can mislead the ML model, causing it to learn from spurious signals.
- Troubleshooting: Implement technical and biological replicates to better quantify and account for noise within the ML model's likelihood function [70] [69].
- Cause 3: Inadequate Model or Features. The model might be too simple to capture the complexity of the biological system, or the input features (e.g., genetic parts data) may not be informative enough.
- Troubleshooting: Consider using more flexible models (e.g., deep learning-based surrogates) and ensure you are incorporating relevant multi-omics data or prior knowledge to enrich the feature set [71] [72].
FAQ 4: How can I implement a fully automated, closed-loop DBTL cycle? Closing the loop requires integrating software and hardware.
- Requirements: You need a robotic platform (e.g., a biofoundry like the iBioFAB) for the Build and Test phases, coupled with a central software framework. This framework must perform three key functions: automatically import and manage experimental data, execute an ML model to analyze results and recommend new strains, and send executable instructions back to the robotic platform for the next cycle [68] [69].
- Software Solution: Develop or adopt a software framework with specific modules: an importer to collect measurement data from lab devices into a database, an optimizer (hosting your ML algorithm) to select the next design points, and a scheduler to translate these points into commands for the robotic platform [69].
Troubleshooting Guides
Issue 1: The DBTL Cycle Fails to "Learn" Effectively
Problem: The cycle runs, but the performance of designed strains does not significantly improve from one iteration to the next. The "Learn" phase is not generating actionable insights.
Investigation and Resolution:
| Step | Action | Expected Outcome |
|---|---|---|
| 1 | Audit Data Quality & Quantity | A clear report on data noise levels and confirmation that dataset size meets the minimum for your chosen ML model. |
| 2 | Diagnose Exploration-Exploitation Balance | A quantitative measure (e.g., distance between new designs) confirming the algorithm is exploring sufficiently and not stuck in a local optimum. |
| 3 | Validate Model Predictions | Insight into whether model inaccuracies are the root cause, prompting a switch to a more complex or different model. |
| 4 | Review Feature Set | Identification of missing critical biological parameters, leading to an updated and more predictive feature set for the model. |
Issue 2: High Experimental Noise Obscures ML Guidance
Problem: The "Test" data is too variable, making it difficult for the ML algorithm to discern a clear signal and identify genuinely improved strains.
Investigation and Resolution:
| Step | Action | Purpose |
|---|---|---|
| 1 | Implement Replicates | To statistically quantify and reduce the impact of random experimental error. |
| 2 | Standardize Protocols | To minimize systematic noise introduced by manual handling or protocol variations. |
| 3 | Calibrate Equipment | To ensure measurement devices (plate readers, etc.) are generating accurate and consistent data. |
| 4 | Use Robust ML Models | To explicitly account for and model the noise in the data, preventing overfitting to spurious results. |
Experimental Protocols & Data
The following table summarizes machine learning algorithms commonly used to balance exploration and exploitation in automated strain design.
| Algorithm Category | Key Mechanism for Balancing E/E | Sample Complexity | Noise Tolerance | Best for |
|---|---|---|---|---|
| Bayesian Optimization [68] | Acquisition Function (e.g., Expected Improvement) | Low | Medium-High | Black-box optimization with expensive experiments |
| Multi-Agent Reinforcement Learning [70] | Parallel policy exploration by multiple agents | Medium | Medium | High-throughput, parallelized cultivation systems |
| Evolutionary Algorithms [71] | Genetic operators (mutation/crossover) and selection | High | Medium | Fragment-based molecular and pathway design |
Essential Research Reagent Solutions
This table details key resources and computational tools used in automated ML-driven DBTL cycles.
| Item Name | Function / Purpose | Example / Note |
|---|---|---|
| Automated Biofoundry [68] [69] | Robotic platform to automate the Build (strain construction) and Test (cultivation, measurement) phases. | Illinois Biological Foundry (iBioFAB); platforms with integrated incubators and liquid handlers. |
| Laboratory Information Management System (LIMS) | Tracks samples, protocols, and data throughout the DBTL cycle, ensuring data is FAIR (Findable, Accessible, Interoperable, Reusable). | Benchling, Riffyn, or custom databases. Essential for automated data importer modules [73]. |
| Genome-Scale Metabolic Models (GEMs) | Provide a structured, mechanistic prior knowledge that can constrain ML models or be used for in silico design. | Used with constraint-based methods like FBA (Flux Balance Analysis) to generate initial designs or features [72]. |
| Open-Source DBTL Platforms | Provides an integrated software environment for designing experiments, managing data, and running ML analysis. | teemi (a Python-based platform for end-to-end workflow management in Jupyter notebooks) [73]. |
Workflow and Pathway Diagrams
DBTL Cycle with ML-Driven Recommendations
Balancing Exploration and Exploitation in Bayesian Optimization
Adapting Sampling Temperatures and Reward Thresholds for Dynamic Balance
Frequently Asked Questions
1. Why does my model's output become incoherent when I increase the sampling temperature to make it more creative?
Increasing the sampling temperature flattens the model's probability distribution over tokens. While this promotes diversity by giving less likely tokens a higher chance of being selected, it also allows tokens from the "unreliable tail" of the distribution to enter the sampling pool. This can degrade coherence, as the model starts selecting sub-optimal or nonsensical tokens. This is a direct manifestation of the exploration-exploitation trade-off, where excessive exploration (high temperature) comes at the cost of exploiting known, high-quality pathways [74].
2. How can I maintain coherent text generation while encouraging creative exploration in my LLM experiments?
To balance this, consider using dynamic truncation sampling methods like min-p sampling. Unlike fixed-threshold methods, min-p sets a minimum probability threshold that scales relative to the model's confidence (the probability of the top candidate token, p_max). When the model is uncertain (p_max is low), it allows more exploration; when confident, it becomes more exploitative. This provides a more context-sensitive balance, maintaining better coherence even at higher temperatures [74] [75].
3. What is the difference between the exploration-exploitation dilemma in reinforcement learning (RL) and in LLM sampling?
The core principle is the same: exploitation uses current knowledge for the best immediate outcome, while exploration seeks new information for potential long-term benefit [1] [4].
- In RL, an agent exploits by taking the action with the highest known expected reward and explores by trying less-familiar actions. This is formalized in problems like the Multi-Armed Bandit [1] [4].
- In LLM Sampling, the model "exploits" by choosing high-probability tokens (leading to safe, coherent text) and "explores" by sampling lower-probability tokens (leading to creative, diverse text). Techniques like temperature scaling and top-p sampling are mechanisms to manage this trade-off [74] [76].
4. My RL agent gets stuck on suboptimal policies during drug discovery simulations. Is it over-exploiting or under-exploring?
This is a classic sign of under-exploration. The agent is over-exploiting known, modestly rewarding pathways in the chemical space and failing to explore potentially superior, unknown ones. In RL, challenges like sparse rewards (where positive feedback is rare) and deceptive rewards (where a small immediate reward lures the agent away from a larger, later reward) can cause this. To overcome this, you can implement exploration rewards (intrinsic motivation), where the agent gets a bonus for visiting novel or uncertain states, thus converting exploration into a form of exploitation [1].
5. Are there new methods that move beyond the traditional exploration-exploitation trade-off?
Emerging research suggests that by analyzing model behavior at the hidden-state level rather than the token level, exploration and exploitation can be decoupled. One proposed method, Velocity-Exploiting Rank-Learning (VERL), uses the effective rank of hidden states to quantify exploration and exploitation dynamics separately. Instead of forcing a trade-off, it uses a shaped advantage function to synergistically enhance both capacities simultaneously, leading to improved performance on complex reasoning tasks [7].
Technical Reference Tables
Table 1: Common Sampling Techniques and Their Characteristics [74] [76] [75]
| Technique | Key Principle | Strengths | Weaknesses | Typical Use Case |
|---|---|---|---|---|
| Greedy Decoding | Always selects the token with the highest probability. | High coherence, computationally efficient. | Highly repetitive, low creativity. | Factual QA, code generation. |
| Temperature Scaling | Rescales logits to sharpen (low T) or flatten (high T) the token distribution. | Simple control over randomness. | Can reduce coherence at high values. | General purpose; T=0.7 often used for creativity. |
| Top-p (Nucleus) | Samples from the smallest set of tokens whose cumulative probability > p. | Dynamic vocabulary size, context-aware. | Can become incoherent at high temperatures. | Creative writing, open-ended generation. |
| Min-p | Sets a minimum threshold as a fraction of the top token's probability. | Balances coherence & creativity, robust at high temps. | Relatively new, less tested across all domains. | High-temperature tasks requiring reliable coherence. |
Table 2: Exploration Strategies in Reinforcement Learning [1] [4]
| Strategy | Mechanism | Application Context |
|---|---|---|
| Epsilon-Greedy | With probability ε, take a random action; otherwise, take the best-known action. | Simple and robust; good baseline for Multi-Armed Bandit problems. |
| Thompson Sampling | A Bayesian method that samples a model from a posterior and acts optimally for that sample. | Contextual bandits; handles uncertainty elegantly. |
| Upper Confidence Bound (UCB) | Selects actions based on their potential for being optimal, using confidence bounds. | Bandit problems; provides a theoretical regret guarantee. |
| Intrinsic Motivation | Provides an exploration bonus (intrinsic reward) for novel or uncertain states. | Sparse-reward environments (e.g., Montezuma's Revenge, complex simulations). |
Experimental Protocols
Protocol 1: Evaluating Min-P Sampling for Creative Molecular Description Generation
- Objective: To test whether min-p sampling can generate more diverse yet coherent textual descriptions of hypothetical drug molecules compared to top-p sampling at elevated temperatures.
- Materials: A fine-tuned LLM (e.g., GPT-3.5, LLaMA), a dataset of molecular structures and their descriptions, the AlpacaEval creative writing benchmark framework [74].
- Methodology:
- Setup: Generate textual descriptions for a fixed set of molecular input structures.
- Experimental Groups:
- Group A (Top-p): Use top-p sampling with
p=0.9and temperatureT=1.5. - Group B (Min-p): Use min-p sampling with a base percentage (e.g.,
min_p=0.1) and the same temperatureT=1.5.
- Group A (Top-p): Use top-p sampling with
- Evaluation Metrics:
- Coherence: Human expert rating on a Likert scale (1-5) or using a learned metric like BARTScore.
- Diversity: Calculate the distinct-n-gram ratio or semantic diversity via embedding space variance [74].
- Factual Accuracy: Check for consistency between the generated description and the molecular structure.
- Expected Outcome: The min-p group is expected to maintain coherence scores similar to or better than the top-p group while achieving higher diversity scores [74] [75].
Protocol 2: Using Intrinsic Curiosity for Drug Space Exploration in an RL Agent
- Objective: To improve an RL agent's exploration of a vast chemical space in a drug discovery simulator by incorporating an intrinsic reward signal.
- Materials: A drug property simulator (environment), an RL agent (e.g., PPO), a predictive world model (e.g., a forward dynamics model).
- Methodology:
- Baseline: Train the RL agent with only extrinsic rewards (e.g., binding affinity).
- Intervention: Implement an Intrinsic Curiosity Module (ICM). The intrinsic reward
r_t^iis computed as the error in predicting the next state (molecular representation) given the current state and action:r_t^i = ‖f(s_t, a_t) - s_{t+1}‖²[1]. - Training: The agent's total reward is
r_total = r_t^e + η * r_t^i, wherer_t^eis the extrinsic reward andηis a scaling factor. - Evaluation: Compare the baseline and intervention agents on:
- The number of unique, high-affinity molecules discovered.
- The speed of convergence to a high-reward policy.
- Expected Outcome: The agent with intrinsic motivation is expected to explore a wider region of the chemical space and discover a greater number of viable candidate molecules, especially in scenarios with sparse extrinsic rewards [1].
The Scientist's Toolkit
Table 3: Key Research Reagent Solutions for Dynamic Balance Experiments
| Reagent / Tool | Function | Application in DBTL Research |
|---|---|---|
| Min-P Sampler | A logits processor for LLMs that dynamically filters low-probability tokens. | Generating diverse and coherent hypotheses, literature, or molecular descriptions. |
| Intrinsic Curiosity Module (ICM) | A self-supervised prediction error model that generates an exploration bonus. | Driving RL agents to explore novel regions of chemical or biological space in simulations. |
| Multi-Armed Bandit Testbed | A simplified framework for testing exploration-exploitation algorithms. | Rapidly prototyping and evaluating new adaptive sampling or thresholding strategies. |
| Effective Rank (ER) Metrics | Quantifies the exploration of an RL agent in its hidden-state space. | Advanced diagnostics for analyzing exploration dynamics beyond simple action counts [7]. |
Experimental Workflow Diagrams
Navigating Pitfalls: Overcoming Stagnation and Bias in Self-Improving Systems
Identifying and Mitigating Training Set Biases in DNA Library Distributions
Frequently Asked Questions (FAQs)
FAQ 1: What are the common types of bias in DNA-encoded library (DEL) data and how do they impact machine learning? A major type of bias is the prevalence of false negatives, where active compounds are missed during affinity selection. One study found that for each identified hit, numerous true active compounds were not detected, which can severely compromise the predictive power of machine learning models trained on this data [77]. The presence of the DNA-conjugation linker itself was identified as a factor that can impair the detection of active molecules, skewing the resulting data distribution [77]. Furthermore, biases can arise from preanalytical variables in sequencing, such as the choice of library preparation kit or sequencing platform, which introduce non-biological variance that confounds analysis [78].
FAQ 2: How can I make my ML model robust to temporal dataset shift in clinical or genomic data? Temporal dataset shift, where model performance degrades over time due to changes in data distribution, is a known barrier. Mitigation strategies can be categorized into two levels [79]:
- Model-level approaches are more common and include:
- Model Refitting: Re-estimating model parameters using new updating data.
- Probability Calibration: Adjusting the predicted probabilities of a base model using methods like logistic regression.
- Model Updating: Incrementally updating model parameters as new data arrives.
- Model Selection: Using statistical tests to select the best-performing model from a set of candidates.
- Feature-level approaches process features before model fitting and can be driven by data or domain expertise. These strategies have been shown to be successful at preserving model calibration, though their effect on discrimination can vary [79].
FAQ 3: What is the role of the exploration-exploitation trade-off in designing a DBTL cycle? Balancing exploration and exploitation is central to efficient experimental design in machine learning-guided Design-Build-Test-Learn (DBTL) cycles. In the context of optimizing genetic parts like bacterial ribosome binding sites (RBS), this trade-off is managed in the Design phase [10].
- Exploitation involves choosing genetic sequences that the current ML model predicts will have high performance.
- Exploration involves testing sequences where the model's predictions are highly uncertain, which can improve the model and lead to discovering better performers. This balance can be algorithmically achieved using methods like the Upper Confidence Bound (UCB) multi-armed bandit algorithm, which uses predictions from a Gaussian Process Regression model to recommend sequences that either exploit current knowledge or explore uncertainty [10].
Troubleshooting Guide: Common Bias Issues and Solutions
| Problem Area | Specific Issue | Potential Causes | Mitigation Strategies |
|---|---|---|---|
| Library Selection & Data Fidelity | High false negative rate; ML model fails to generalize and predict true active compounds. | - DNA linker effects altering compound activity [77].- Undersampling of the library during selection [77].- Variable synthesis yields of library compounds [77]. | - Acknowledge linker as a source of bias and account for it in model interpretation [77].- Employ oversampling techniques to compensate for underrepresented active compounds in the training data [77]. |
| Sequencing & Technical Bias | Technical variation (e.g., from different library prep kits) obscures biological signals. | - Preanalytical variables (library kit, sequencer, DNA extraction method) [78].- GC-content bias introduced during amplification [78]. | - Apply data correction methods like DAGIP, which uses optimal transport theory to correct for technical biases from different wet-lab protocols [78].- Integrate cohorts from different studies after bias correction [78]. |
| Model Performance & Generalizability | Model performance deteriorates on new data from a different time period or protocol (temporal dataset shift). | - Changes in patient case mix, outcome rates, or coding practices over time [79].- Evolution of laboratory protocols or instrumentation. | - Implement model-level mitigation strategies such as model refitting or probability calibration with new data [79].- Use online learning methods for model updating as new data becomes available [79]. |
| Experimental Design | Inefficient search of the genetic design space; failure to find optimal sequences. | - Poor balance between exploring new regions of the design space and exploiting known high-performing areas. | - Implement a DBTL cycle using Gaussian Process Regression (for uncertainty-aware predictions) and multi-armed bandit algorithms (for batch recommendation) to strategically balance exploration and exploitation [10]. |
Experimental Protocols
Protocol 1: Mitigating Technical Biases in cfDNA Sequencing Data Using DAGIP
Objective: To correct for technical biases introduced by different preanalytical protocols (e.g., library preparation kits) in cell-free DNA (cfDNA) sequencing data, thereby improving downstream analysis like cancer detection [78].
Methodology:
- Data Preparation: Collect cfDNA sequencing data from the same biological samples processed under different domains (i.e., different wet-lab protocols, such as
TruSeq NanoandKapa HyperPrepkits). - Bias Correction with Optimal Transport:
- The core of DAGIP is based on optimal transport theory, which finds a plan to map the data distribution from a source domain to a target domain.
- The method operates in the original data space (e.g., coverage profiles, fragment size frequencies), making the correction highly interpretable.
- It explicitly corrects the effect of preanalytical variables, inferring and removing technical biases while preserving biological signals like copy number alterations.
- Downstream Analysis: Use the corrected data for more robust cohort integration, cancer detection, and copy number alteration analysis.
Protocol 2: Machine Learning-Guided DBTL Cycle for RBS Optimization
Objective: To optimize the translation initiation rate (TIR) of a bacterial ribosome binding site (RBS) by strategically balancing the exploration of sequence space and exploitation of model predictions [10].
Methodology: This workflow integrates two machine learning algorithms into an iterative DBTL cycle, as shown in the diagram below.
Learn Phase:
- Algorithm: Gaussian Process Regression (GPR).
- Function: Learns from the logged experimental data (RBS sequence -> TIR) to build a predictive model.
- Output: For any potential RBS sequence, GPR provides a predicted mean TIR and a measure of uncertainty (standard deviation) for that prediction.
Design Phase:
- Algorithm: Upper Confidence Bound (UCB) Multi-armed Bandit.
- Function: Uses the predictions from GPR to recommend a batch of new RBS sequences to test. The UCB algorithm automatically balances:
- Exploitation: Choosing sequences with a high predicted mean TIR.
- Exploration: Choosing sequences with a high prediction uncertainty.
- Output: A shortlist of RBS variants for the next Build phase.
Build & Test Phases:
- Build: The recommended RBS sequences are synthesized and constructed into plasmids using automated laboratory methods.
- Test: The TIR (or corresponding protein expression level) of each variant is measured reliably using high-throughput assays.
This cycle repeats, with each iteration improving the GPR model's accuracy and guiding the search towards higher-performing RBSs.
The Scientist's Toolkit: Key Research Reagents & Materials
| Item | Function in Experiment |
|---|---|
| Focused DNA-Encoded Library (DEL) (e.g., NADEL) | A homogeneous library of synthetic small molecules conjugated to DNA barcodes, used for affinity selections against protein targets to identify binders [77]. |
| PARP Enzyme Targets (PARP1/2, TNKS1/2) | A set of structurally related poly-(ADP-ribose) polymerases, serving as a model system for comparative analysis of DEL enrichment patterns and selectivity [77]. |
| Cell-free DNA (cfDNA) Samples | A source of biomarkers from plasma; used for developing and testing bias correction methods across different sequencing protocols [78]. |
| Various Library Prep Kits (e.g., TruSeq Nano, Kapa HyperPrep) | Kits with different enzymatic efficiencies and biases (e.g., towards GC-content) used to prepare sequencing libraries; a major source of technical variation to be corrected [78]. |
| Gaussian Process Regression (GPR) Model | A Bayesian, non-parametric machine learning algorithm used in the "Learn" phase to predict genetic part performance and, crucially, provide uncertainty estimates [10]. |
| Upper Confidence Bound (UCB) Algorithm | A multi-armed bandit algorithm used in the "Design" phase to recommend new experiments by balancing exploration and exploitation based on GPR outputs [10]. |
| Benchmark RBS Sequence | A known strong genetic part (e.g., TTTAAGAAGGAGATATACAT) used as a reference point against which newly designed variants are benchmarked for performance [10]. |
Addressing the Rapid Saturation Problem in Iterative Self-Improvement
Frequently Asked Questions (FAQs)
FAQ 1: What are the primary causes of rapid saturation in iterative self-improvement? Rapid saturation, where performance stops improving after only 3-5 iterations, is primarily caused by two dynamic factors: the rapid deterioration of the model's exploratory capabilities (its ability to generate diverse and correct responses) and the diminishing effectiveness of exploitation (the reward function's ability to distinguish high-quality solutions) [80]. An imbalance between these two factors hinders continued learning [80].
FAQ 2: How is 'exploration' defined and measured in this context? Exploration is the model's ability to generate correct and diverse responses among multiple candidates [80]. It can be quantitatively monitored using metrics like Pass@k (e.g., Pass@32), which measures the probability of at least one correct solution in a batch of
kgenerated samples [80]. A decline in Pass@k over iterations signals failing exploration.FAQ 3: What constitutes 'exploitation' and its key metrics? Exploitation is the effectiveness of external rewards in selecting high-quality solutions from the candidate pool [80]. Its effectiveness can be tracked by the selection accuracy of the reward function—how well it identifies and filters for the best outputs—which can diminish over time [80].
FAQ 4: Can these principles be applied to research beyond language models, such as in drug discovery? Yes. The core challenge of balancing exploration (searching a vast space of possibilities) and exploitation (refining known promising candidates) is universal. In drug discovery, an analogous "lab in a loop" strategy is used, where AI models generate predictions (e.g., for new drug targets or molecules) that are tested in the lab, with the resulting data used to retrain and improve the models in an iterative cycle [81].
FAQ 5: What is a fundamental strategy for balancing exploration and exploitation? A proven strategy is to dynamically alternate or weight the objectives rather than applying them simultaneously. The Explore-then-Exploit (EE) framework, for instance, interleaves periods of pure exploration (using intrinsic rewards to find novel states) with periods of pure self-imitation (exploiting past high-rewarding behaviors) to prevent the objectives from interfering with each other [82].
Troubleshooting Guides
Issue 1: Performance Plateau After a Few Iterations
- Symptoms: Model performance (e.g., Pass@1) stagnates or declines after 3-5 iterations of self-improvement training. The model's outputs become less diverse and more repetitive [80].
- Diagnosis: This typically indicates an imbalance between exploration and exploitation, where the model's ability to generate novel, correct solutions has degraded, and the reward function can no longer effectively guide selection [80].
- Solutions:
- Monitor Key Metrics: Proactively track exploration metrics (e.g., Pass@32) and exploitation metrics (e.g., reward selection accuracy) throughout the iterative process to diagnose which factor is failing [80].
- Implement Adaptive Balancing: Use a framework like B-STaR, which automatically adjusts configurations (e.g., sampling temperature, reward thresholds) across iterations to balance exploration and exploitation based on the current state of the model [80].
- Adopt an Interleaving Strategy: Structure training into distinct stages. For a set number of steps, focus purely on exploration (e.g., using curiosity-driven rewards), then switch to a stage of pure self-imitation on the collected high-quality data [82].
Issue 2: Poor Quality in Self-Generated Training Data
- Symptoms: The model fails to learn from its own outputs, or performance becomes unstable. This is often due to low-quality or non-diverse data in the training set.
- Diagnosis: The root cause can be poor initial data, a weak reward function, or a lack of exploratory sampling.
- Solutions:
- Validate Data Quality: Before training, check for common data issues like class imbalance, missing values, and outliers. Techniques include resampling, imputation, and using algorithms like SMOTE or DBSCAN to identify and handle outliers [83].
- Enhance the Reward Function: If the reward is binary (e.g., correct/incorrect final answer), consider developing a more nuanced, process-based reward model (PRM) that provides feedback on the reasoning steps, not just the final outcome [80].
- Increase Sampling Diversity: Adjust the sampling temperature or use other sampling strategies during the generation step to produce a wider variety of candidate solutions for the reward function to evaluate [80].
Experimental Protocols & Data
Quantitative Monitoring of Exploration and Exploitation
The table below summarizes key metrics for diagnosing the rapid saturation problem [80].
| Factor | Metric | Description | Desired Trend |
|---|---|---|---|
| Exploration | Pass@32 | Probability of a correct solution in a batch of 32 samples. | Stable or Increasing |
| Exploration | Response Diversity | Measured by the variety of reasoning paths or unique outputs. | Stable or Increasing |
| Exploitation | Reward Accuracy | The reward function's success rate in selecting the best solution. | Stable or Increasing |
| Exploitation | Selection Precision | The quality of solutions selected by the reward function vs. a gold standard. | Stable or Increasing |
| Overall Performance | Pass@1 | The performance of the primary, single-sample model. | Stable or Increasing |
Detailed Methodology: The B-STaR Framework
The B-STaR framework provides a methodology to directly address saturation by balancing exploration and exploitation.
- 1. Principle: An autonomous system that monitors the model's current exploratory capability and the effectiveness of the available reward, then adjusts training configurations to optimize the balance between them [80].
- 2. Workflow:
- Iteration Start: Begin with a policy model ( P_{t-1} ).
- Generate & Monitor: For each query, generate
Kcandidate responses. Calculate exploration metrics (e.g., Pass@k) for the current batch. - Reward & Assess: Score candidates with the reward function ( r(x, y) ). Calculate exploitation metrics (e.g., reward accuracy).
- Calculate Balance Score: A novel metric that assesses the potential of a query based on the current model’s exploration and exploitation capabilities [80].
- Adapt Configuration: Automatically adjust parameters (e.g., sampling temperature, reward threshold) to maximize the average balance score.
- Improve Model: Update the policy model ( P{t-1} ) to ( Pt ) using the selected high-quality data, typically via Supervised Fine-Tuning (SFT) or Rejection Fine-Tuning (RFT) [80].
- 3. Key Benefit: Preents the typical rapid decline of exploratory diversity, enabling performance to scale effectively with more iterations and compute [80].
B-STaR Balancing Mechanism
Application in Drug Discovery: The 'Lab in a Loop' Protocol
This protocol applies iterative self-improvement to the domain of drug discovery.
- 1. Principle: A closed-loop system where AI-generated predictions are experimentally tested, and the results are used to retrain the AI models, creating a continuous cycle of improvement [81].
- 2. Workflow:
- Data Generation: Generate large-scale data from lab experiments (e.g., high-throughput screening) and clinical studies.
- Model Training: Train AI models (e.g., for target validation, molecule design) on the accumulated data.
- AI Prediction: Use the trained models to generate novel predictions (e.g., new therapeutic targets, small-molecule compounds, or optimized antibody designs).
- Experimental Testing: Test these AI-generated predictions in the wet lab (e.g., in vitro or in vivo assays).
- Data Incorporation & Retraining: The new experimental results are fed back into the dataset to retrain and improve the AI models, closing the loop [81].
Lab-in-a-Loop for Drug Discovery
The Scientist's Toolkit: Research Reagent Solutions
| Item / Tool | Function / Application |
|---|---|
| B-STaR Framework | A Self-Taught Reasoning framework that autonomously balances exploration and exploitation to overcome performance saturation in iterative training [80] [84]. |
| Explore-then-Exploit (EE) Framework | A reinforcement learning framework that interleaves periods of exploration (using intrinsic rewards) with periods of self-imitation to efficiently solve sparse-reward tasks [82]. |
| Process-based Reward Models (PRMs) | Provides fine-grained reward signals by evaluating the correctness of each reasoning step, leading to more effective exploitation than outcome-based rewards alone [80]. |
| "Lab in a Loop" Platform | An integrated computational-experimental system where AI predictions are tested in the lab, and the results are used to retrain models, creating a cycle of rapid hypothesis testing and refinement [81]. |
| Data Quality Assertion Tools (e.g., Great Expectations) | Software libraries used to validate the quality of training data through data testing, profiling, and documentation, which is critical for reliable model debugging [83]. |
Combating Experimental Noise and Heteroscedasticity in Biological Data
FAQs: Understanding Noise in Biological Data
Q1: What is heteroscedastic noise and why is it a problem in biological experiments?
Heteroscedasticity (or non-constant variance) refers to a pattern in model residuals where variability differs across subsets of data [85]. In biological data, this manifests as measurement uncertainty that changes with the signal intensity [86] [87]. This is problematic because it violates the constant variance assumption of many standard statistical models, leading to misleading standard errors, p-values, and confidence intervals [85]. In machine learning, heteroscedastic noise can bias multivariate analysis, causing intense peaks to dominate over analytically important low-intensity signals in methods like PCA [88].
Q2: How can I detect heteroscedasticity in my experimental data?
- Visual Diagnosis: For simple models with single predictors or time-series data, plot residuals against fitted values. Look for patterns like cones or fans where variance increases/decreases with predicted values [85].
- Statistical Tests: For complex models, use tests like Breusch-Pagan which regresses squared residuals on original predictors [85].
- Noise Characterization: In analytical chemistry, methods exist to characterize instrument noise without replicates using high-pass digital filtering and residual analysis [87].
Q3: What practical steps can reduce heteroscedasticity's impact on my DBTL cycles?
- Model Modification: Transform variables using logarithms, use appropriate distributions, or build separate models for subgroups [85].
- Robust Standard Errors: Use Huber-White sandwich estimators for correct inference despite heteroscedasticity [85].
- Specialized Normalization: For mass spectrometry, use methods like WSoR scaling that account for noise distribution to reduce bias in multivariate analysis [88].
- Bayesian Optimization: Implement frameworks like BioKernel with heteroscedastic noise modeling to guide experiments despite non-constant uncertainty [86].
Troubleshooting Guides
Guide 1: Addressing Heteroscedasticity in Model Residuals
Symptoms: Your model diagnostics show residual variance that systematically increases or decreases with predicted values, or differs between experimental groups.
Step-by-Step Solution:
- Confirm the Problem: Create a residual vs. fitted values plot. Random scatter indicates homoscedasticity; patterns indicate heteroscedasticity [85].
- Identify Potential Causes:
- Incorrectly assumed linear relationships
- Wrong distributional assumptions (e.g., using linear instead of Poisson regression)
- Differential model performance across subgroups [85]
- Apply Appropriate Fixes:
- Validate Solution: Recheck residual plots after modifications to ensure constant variance.
Guide 2: Managing Noise in High-Throughput Biological Experiments
Symptoms: Experimental results show unpredictable variability that compromises reproducibility, particularly in 'omics' technologies and high-dimensional phenotypic screening.
Step-by-Step Solution:
- Noise Characterization:
- Data Integration Strategies:
- Use vertical integration to connect different features across replicate individuals
- Apply mosaic integration for joint embedding of disparate datasets into common space [89]
- Multi-Omic Noise Reduction:
- Overlap complementary datasets to identify common noisy signals
- Combine whole genome sequencing, transcriptomics, proteomics, and metabolomics to distinguish biological signal from technical noise [89]
- Implementation of Adaptive ML:
Experimental Protocols
Protocol 1: Characterizing Measurement Noise Without Replicates
Purpose: Estimate instrument measurement error characteristics when replication is impractical or unavailable [87].
Materials:
- Analytical instrument generating vector measurements (spectrum, chromatogram)
- Computational software (e.g., MATLAB, Python with SciPy)
- Standard reference materials
Methodology:
- Signal Preparation: Ensure sampling frequency significantly exceeds frequency components of pure signal [87].
- High-Pass Filtering: Apply adaptable high-pass digital filtering to separate signal from noise components [87].
- Residual Analysis: Estimate pure signal via least squares modeling, then examine residuals as noise estimates [87].
- Variance Modeling: Use ensemble averaging and variance modeling to detect and characterize heteroscedastic noise [87].
- Validation: Compare with limited replicates if possible to confirm noise characterization.
Applications: Optimal for determining instrument detection limits independent of sample preparation variance [87].
Protocol 2: Bayesian Optimization for Noisy Biological Systems
Purpose: Optimize biological system performance despite experimental noise with minimal resource expenditure [86].
Materials:
- Biological system with quantifiable output (e.g., metabolite production, growth rate)
- Bayesian optimization software (e.g., BioKernel)
- Laboratory automation equipment (optional but recommended)
Methodology:
- Problem Formulation:
- Define input parameters (e.g., inducer concentrations, media components)
- Specify objective function (e.g., product yield, growth efficiency)
- Set experimental constraints (budget, time, resources) [86]
Model Configuration:
Iterative Optimization:
- Run initial space-filling experiments
- Update Gaussian Process model with results
- Select next experiments via acquisition function maximization
- Continue until convergence or resource exhaustion [86]
Validation: Confirm optimum with follow-up experiments.
Applications: Metabolic engineering, media optimization, genetic circuit tuning [86].
Table 1: Performance Comparison of Optimization Methods
| Method | Experiments to Convergence | Noise Handling | Application Context |
|---|---|---|---|
| Bayesian Optimization [86] | 19 points (vs 83 for grid search) | Explicit heteroscedastic modeling | Metabolic pathway optimization |
| Grid Search [86] | 83 points | Limited | Combinatorial screening |
| Multi-armed Bandit with GPR [10] | 450 variants over 4 DBTL cycles | Uncertainty-guided exploration | RBS sequence optimization |
| Traditional RBS Calculators [10] | Varies (R²: 0.2 to >0.8) | Poor (deterministic) | Translation initiation prediction |
Table 2: Noise Types in Analytical Instruments
| Noise Type | Characteristics | Dominant Regime | Statistical Properties |
|---|---|---|---|
| Detector-limited [88] | Additive White Gaussian Noise | Low signals | Constant variance |
| Source-limited [88] | Shot noise from discrete ions | Intermediate signals | Poisson distribution, variance ∝ signal |
| Fluctuation [88] | 1/f (flicker) noise | High signals | Power spectrum ∝ 1/frequency |
Experimental Workflows and Pathways
Bayesian Optimization Workflow
Multi-Omic Data Analysis with Noise Handling
The Scientist's Toolkit
Table 3: Essential Research Reagent Solutions
| Reagent/Resource | Function/Purpose | Example Application |
|---|---|---|
| Marionette E. coli Strains [86] | Genomic integration of orthogonal transcription factors for multi-dimensional optimization | Astaxanthin pathway optimization |
| Gaussian Process Regression Software [86] [10] | Probabilistic modeling with uncertainty quantification | Predicting biological system performance |
| Multi-armed Bandit Algorithms [10] | Balancing exploration-exploitation in experimental design | RBS sequence optimization in DBTL cycles |
| Heteroscedastic Noise Models [86] [88] | Accounting for non-constant measurement variance | Accurate uncertainty propagation in biological data |
| WSoR Scaling Method [88] | Noise-unbiased multivariate analysis | Orbitrap mass spectrometry data processing |
| BioKernel Framework [86] | No-code Bayesian optimization for experimental biologists | Accessible optimization without programming expertise |
Adaptive Parameter Tuning for Dynamic Exploration-Exploitation Balance
Frequently Asked Questions (FAQs)
What is the exploration-exploitation dilemma and why is it critical in ML-driven research?
The exploration-exploitation dilemma describes the fundamental challenge of choosing between leveraging known, rewarding options (exploitation) and testing new, uncertain options to gather more information (exploration) [1] [6]. In the context of machine learning (ML) and Design-Build-Test-Learn (DBTL) cycles, this is critical because over-emphasizing exploitation can cause your model to miss better alternatives (e.g., a more effective drug candidate), while excessive exploration wastes computational resources and time on unpromising options [6]. A dynamic balance is necessary for efficient and optimal outcomes.
What are the main strategies for managing this trade-off?
Research identifies two primary, complementary strategies [12]:
- Directed Exploration: This is a deterministic strategy that adds an "information bonus" to the value of more informative or uncertain options, actively steering the exploration process [12]. Algorithms like Upper Confidence Bound (UCB) are examples [1] [12].
- Random Exploration: This strategy introduces stochasticity, or randomness, into the decision-making process. Instead of a calculated bonus, exploration happens by chance through the addition of random noise to value calculations [12]. Methods like epsilon-greedy and Thompson Sampling fall into this category [1] [90].
The following table summarizes the core algorithms used to implement these strategies:
| Algorithm | Type | Brief Mechanism | Key Hyperparameters |
|---|---|---|---|
| Epsilon-Greedy [6] [90] | Random | With probability ε, explore randomly; otherwise, exploit the best-known option. | ε (exploration rate) |
| Upper Confidence Bound (UCB) [1] [12] | Directed | Selects the option with the highest value, where value is the current reward estimate plus a bonus proportional to uncertainty. | Confidence level parameter |
| Thompson Sampling [1] [12] | Random | Uses a probabilistic model; an option is selected based on the probability that it is the optimal one. | Prior distributions of parameters |
| Adaptive Optimizers (e.g., Adam) [91] | N/A | Not a direct exploration method, but adapts the learning rate for each parameter during model training, influencing the learning trajectory. | Learning rate, beta1, beta2 |
What common problems occur during implementation and how can I resolve them?
| Problem | Description | Potential Solutions |
|---|---|---|
| Sparse Rewards [1] | The agent receives feedback very infrequently, making it difficult to learn which actions are good. | Implement an intrinsic reward or exploration bonus (e.g., based on prediction error or state novelty) to encourage exploration of unseen states [1]. |
| Deceptive Reward [1] | An easy-to-find, sub-optimal reward lures the agent away from exploring paths that lead to a larger, optimal reward. | Use algorithms that maintain uncertainty estimates (e.g., UCB, Thompson Sampling) to avoid getting trapped by initially promising but ultimately poor options [1]. |
| Convergence to Sharp Minima [91] | In model training, adaptive optimizers can sometimes converge to sharp minima in the loss landscape, which can hurt the model's ability to generalize to new data. | Consider using simpler optimizers like Stochastic Gradient Descent (SGD) or incorporating learning rate schedules that can help find flatter minima [91]. |
How can I dynamically adjust the exploration rate during an experiment?
A powerful technique is parameter scheduling, where you treat hyperparameters like the exploration rate not as fixed values, but as functions that change over time [92]. This allows for a natural transition from high exploration at the start of training (when knowledge is poor) to higher exploitation later on (when knowledge is more reliable) [92]. The table below compares three common adapters:
| Adapter Type | Mathematical Form | Behavior Summary |
|---|---|---|
| Exponential [92] | value = end_value + (initial_value - end_value) * exp(-alpha * iteration) |
Rapid initial decay that slows over time. Good for fast reduction in exploration. |
| Inverse [92] | value = end_value + (initial_value - end_value) / (1 + alpha * iteration) |
Slower, more gradual decay compared to the exponential adapter. |
| Potential [92] | value = end_value + (initial_value - end_value) * (1 - alpha)^iteration |
Very rapid initial decay, quickly approaches the end value. |
The Scientist's Toolkit: Research Reagent Solutions
This table details key computational "reagents" essential for experimenting with exploration-exploitation balance.
| Reagent / Method | Function in the Experiment |
|---|---|
| Epsilon-Greedy Scheduler | Provides a baseline strategy for balancing random actions (exploration) with greedy actions (exploitation). Its simplicity makes it a good starting point for any experiment [6] [90]. |
| Upper Confidence Bound (UCB) | Injects an explicit, quantifiable preference for uncertainty into the decision-making process. Ideal for experiments where quantifying and leveraging uncertainty is a primary goal [1] [12]. |
| Thompson Sampling | Provides a Bayesian probability-based approach to exploration. It is highly effective in scenarios where maintaining and sampling from a posterior distribution of beliefs is feasible [1] [12]. |
| Intrinsic Curiosity Module (ICM) | Generates an internal exploration reward signal based on prediction error of a forward dynamics model. This reagent is crucial for overcoming sparse reward problems by making unknown states inherently interesting to the agent [1]. |
| Adam / RMSProp Optimizer | These are adaptive gradient-based optimizers that adjust the learning rate for each parameter. They are fundamental reagents for the "learning" phase in DBTL, ensuring stable and efficient model training [91]. |
Experimental Protocols & Workflows
Protocol 1: Implementing a Dynamic Epsilon-Greedy Strategy using an Exponential Adapter
This protocol is ideal for researchers starting with dynamic parameter tuning, such as in initial stages of a drug discovery pipeline to broadly scan the chemical space.
- Initialization: Define the initial exploration rate (
initial_epsilon = 0.8), the final exploration rate (end_epsilon = 0.1), and the decay rate (alpha = 0.05). - Loop: For each episode or generation in the DBTL cycle:
a. Decision: With probability
epsilon, select a random action (e.g., a new experimental condition). Otherwise, select the action with the highest known reward. b. Evaluation: Execute the action and record the reward (e.g., experimental result). c. Update: Update the model or knowledge base with the new result. d. Adapt: Update the exploration rate using the exponential adapter formula:epsilon = end_epsilon + (initial_epsilon - end_epsilon) * exp(-alpha * generation) - Termination: Continue until convergence criteria are met (e.g., reward plateaus) or the maximum number of cycles is reached.
Protocol 2: Benchmarking Exploration Strategies in a Multi-Armed Bandit Setting
This protocol provides a standardized framework for comparing the performance of different exploration algorithms before deploying them in costly real-world experiments.
- Problem Setup: Simulate a Bernoulli multi-armed bandit problem with several choices (e.g., 5 arms), each with a fixed but hidden success probability (e.g., p = [0.1, 0.1, 0.1, 0.5, 0.9]) [90].
- Agent Initialization: Initialize agents using different strategies: Epsilon-Greedy, UCB, and Thompson Sampling.
- Training Loop: Run each agent for a fixed number of trials (e.g., 1000). a. At each trial, the agent selects an arm based on its policy. b. The environment returns a reward of 1 (success) or 0 (failure), based on the arm's probability. c. The agent updates its internal estimates.
- Evaluation: Track the cumulative regret over time, which is the difference between the reward of the best possible arm and the reward obtained by the agent. The strategy that minimizes cumulative regret the fastest is the most efficient [90].
Workflow and Relationship Visualizations
DBTL Cycle with Exploration-Exploitation
Strategy Selection Guide
Monitoring Exploration Diversity and Exploitation Effectiveness with Quantitative Metrics
Overview This guide provides technical support for researchers implementing machine learning (ML) strategies, particularly reinforcement learning, within a Design-Build-Test-Learn (DBTL) cycle for drug development. A core challenge in this process is balancing the exploration of diverse chemical spaces with the exploitation of known, high-performing compounds [21]. The following FAQs and troubleshooting guides address specific quantitative metrics and methodologies to monitor and manage this balance effectively.
What are exploration and exploitation in the context of molecular design?
In machine learning for molecular design, exploitation involves selecting and optimizing molecular structures based on existing knowledge to maximize a scoring function, such as predicted binding affinity or synthesizability. Conversely, exploration involves testing new or under-represented molecular structures to gather information and discover potentially superior scaffolds [21] [93].
The core challenge, known as the exploration-exploitation dilemma, is that you cannot exclusively do both at the same time [94] [1]. Over-exploiting known areas can lead to a lack of diversity and getting stuck in local maxima, while over-exploring can waste resources on poor-performing compounds [95].
What quantitative metrics can I use to monitor exploration and exploitation?
Monitoring the balance between exploration and exploitation requires tracking specific, quantifiable metrics. The table below summarizes key performance indicators (KPIs) for both processes.
Table 1: Quantitative Metrics for Monitoring Exploration and Exploitation
| Process | Metric | Description | Interpretation |
|---|---|---|---|
| Exploration | Novelty / Diversity Score | Measures the structural dissimilarity of newly generated molecules from a reference set (e.g., previously generated or known active compounds). Can be calculated using Tanimoto similarity or other molecular fingerprints. | A higher score indicates successful exploration of new chemical space [21]. |
| State/Action Visit Count | Tracks how many times a specific molecular scaffold or design decision has been sampled. | A distribution with many low counts suggests broad exploration [23] [1]. | |
| Intrinsic Reward | A bonus signal given to the ML agent for discovering novel or uncertain states, independent of the primary scoring function (e.g., prediction error of a dynamics model) [23]. | A sustained high intrinsic reward may indicate continuous discovery, while a drop suggests reduced novelty. | |
| Exploitation | Scoring Function Performance | The average value of the primary objective (e.g., predicted binding affinity, QED) for the top-k selected compounds in a design cycle [21]. | A rising average indicates effective exploitation and optimization. |
| Best-in-Class Compound | The maximum value of the scoring function achieved in any generated compound to date. | Tracks the global performance peak and directly measures success in achieving the primary goal. | |
| Regret | The difference between the performance of the best possible compound and the performance of the compound you selected. | Minimizing cumulative regret is a key goal; lower regret means your strategy is closer to optimal [95]. | |
| Balance | Percentage of Novel Actives | The proportion of newly explored compounds that meet a predefined activity threshold. | A high percentage indicates that exploration is efficiently finding new, high-quality compounds [21]. |
The following diagram illustrates the core logical relationship and the trade-off between these two processes, which is central to the DBTL cycle.
How do I implement a count-based exploration strategy to enhance diversity?
Count-based exploration encourages the ML algorithm to favor under-sampled regions of chemical space.
Experimental Protocol
- Define a State/Structure Descriptor: Convert a molecular structure into a feature representation. This could be a continuous vector from an autoencoder's latent space or a hashed binary fingerprint using a technique like SimHash [23].
- Track Visitation Counts: Maintain a running count, N(ϕ(s)), of how many times the hashed or binned representation of a molecule, ϕ(s), has been generated.
- Calculate Intrinsic Reward: Compute an exploration bonus for a molecule s using the formula: r^i(s) = (N(ϕ(s)) + 0.01)^{-1/2} [23]. This bonus is higher for molecules similar to those that have been rarely seen.
- Augment the Reward Signal: Combine the intrinsic exploration bonus with the extrinsic, task-specific reward (e.g., a predicted property score): r_total = r_extrinsic + β * r_intrinsic, where β is a hyperparameter that controls the exploration strength [23].
- Update the Model: Use the total reward r_total to train your generative model or reinforcement learning agent.
Troubleshooting Guide
- Problem: The diversity of generated molecules is not improving.
- Solution: Increase the β hyperparameter to give more weight to the exploration bonus. Alternatively, re-examine your state descriptor (ϕ(s)); it may not be capturing meaningful molecular differences. Consider using a more expressive molecular representation [23].
- Problem: The algorithm explores too randomly and fails to optimize the primary scoring function.
- Solution: Gradually decay the β parameter over successive DBTL cycles, shifting the focus from exploration to exploitation over time [95].
The workflow for integrating this into a molecular design loop is shown below.
What algorithms are best for balancing exploration and exploitation?
No single algorithm is universally "best," but several are well-studied and effective. The choice depends on the specific stage of your DBTL cycle and the size of your chemical space.
Table 2: Comparison of Key Balancing Algorithms
| Algorithm | Mechanism | Quantitative Implementation | Best Use Case in Molecular Design |
|---|---|---|---|
| ε-Greedy | With probability ε, explore a random action; otherwise, exploit the best-known action [94] [93]. | Set ε to 0.1 (10%) for a fixed exploration rate. For dynamic decay, use: εt = ε0 / (1 + kt), where *k is a decay constant [95]. | Initial DBTL cycles for broad screening; simple to implement and interpret. |
| Upper Confidence Bound (UCB) | Selects the action that maximizes the upper confidence bound: Q(a) + √(2 ln t / N(a)), where N(a) is the count of action a [94] [12]. | The term √(2 ln t / N(a)) is the information bonus that quantifies uncertainty. Actions with high uncertainty or high value are favored [12]. | When you have reliable uncertainty estimates for your property predictions and want a principled balance. |
| Thompson Sampling | For each decision, a probability distribution for each action's performance is sampled. The action with the highest sampled value is chosen [23] [93]. | Assume a prior distribution (e.g., Beta) for the "success" of a molecular scaffold. Update the distribution with experimental results and sample from the posterior to select the next scaffold [93]. | Ideal for clinical trial design or selecting among a discrete set of lead compounds for further testing. |
The Scientist's Toolkit: Key Research Reagent Solutions
This table outlines essential computational "reagents" and frameworks for implementing the strategies discussed above.
Table 3: Essential Tools for ML-Driven Molecular Design
| Tool / Reagent | Function | Relevance to Exploration/Exploitation |
|---|---|---|
| Molecular Fingerprints (e.g., ECFP, Morgan) | Creates a bit-vector representation of a molecule's structure. | Serves as the input for calculating similarity and diversity metrics. Essential for novelty scoring [23]. |
| Multi-armed Bandit Framework (e.g., Vowpal Wabbit) | Provides ready-to-use implementations of algorithms like ε-Greedy, UCB, and Thompson Sampling [93]. | Allows rapid prototyping of different balancing strategies for recommending molecular series to synthesize and test. |
| Reinforcement Learning Libraries (e.g., OpenAI Gym, RLlib) | Offers standardized environments and agent architectures for developing and testing RL algorithms. | Used to build and train agents for de novo molecular generation, where the agent must explore and exploit a vast chemical space [95]. |
| Intrinsic Curiosity Module (ICM) | A neural network architecture that generates an intrinsic reward signal based on prediction error of a forward dynamics model [23] [1]. | Drives exploration in "hard-exploration" problems with sparse rewards, such as discovering entirely new molecular scaffolds with desired but rare properties. |
Strategies for Overcoming Local Optima in Complex Biological Landscapes
Frequently Asked Questions (FAQs)
1. What is the exploration-exploitation trade-off in the context of biological optimization? Balancing exploration and exploitation involves strategically deciding when to gather new information from uncharted areas of the experimental space (exploration) versus using existing knowledge to maximize rewards from promising, known areas (exploitation). This trade-off is central to optimization and machine learning in biological design, as it helps avoid getting stuck in suboptimal solutions while minimizing wasted effort on unproductive paths [96].
2. Why is overcoming local optima particularly challenging in biological DBTL cycles? Biological systems are complex, expensive, and time-consuming to experiment with. The landscapes are often "black-box" functions—where the relationship between inputs (e.g., gene expression levels) and outputs (e.g., product titer) is not fully understood—and are noisy due to biological variability. This makes it difficult to know if a good result is the best possible (global optimum) or merely a local optimum [68] [97].
3. Which machine learning algorithms are best suited for navigating complex biological landscapes? Algorithms specifically designed for the optimization of expensive black-box functions are most effective. Bayesian Optimization is a leading technique, as it uses a probabilistic model to make informed decisions about which experiments to run next, elegantly balancing exploration and exploitation [68]. Evolutionary algorithms and hybrid global-local strategies have also shown superior performance in various biological and hydrological inverse-estimation problems [98] [99].
4. How can I implement a strategy to balance exploration and exploitation in my own research? You can implement specific acquisition policies within a Bayesian Optimization framework. Common and effective strategies include [68] [96]:
- Expected Improvement (EI): Selects the next experiment that is expected to provide the greatest improvement over the current best result.
- Upper Confidence Bound (UCB): Prioritizes points with a high upper confidence bound, favoring either high potential (exploitation) or high uncertainty (exploration) based on a tunable parameter.
- Thompson Sampling: A probabilistic algorithm that selects an action based on the probability of it being optimal.
Troubleshooting Guides
Problem: The DBTL cycle appears to have converged, but the product titer is below theoretical predictions.
Possible Cause: The optimization process has become trapped in a local optimum, exploiting a small region of the biological design space and missing the global optimum.
Solution: Force the algorithm to explore more broadly.
- Action 1: Increase the weight on the exploration component of your acquisition function. For example, in an Upper Confidence Bound policy, increase the parameter that controls the weight of the uncertainty [96].
- Action 2: Incorporate batch recommendations. Use a parallelized Bayesian Optimization algorithm that suggests a batch of diverse experiments for the next DBTL cycle, including some with high uncertainty to explore new regions [68].
- Action 3: Integrate a hybrid strategy. Combine a global search algorithm (e.g., Comprehensive Learning PSO) with a local exploitation method (e.g., gradient-based optimizer) to refine promising areas without losing sight of the global landscape [98].
Problem: Experimental results are too noisy, making it difficult for the learning algorithm to discern a clear direction.
Possible Cause: High biological variability or experimental error is obscuring the true signal in the data.
Solution: Make the learning algorithm "aware" of biological noise.
- Action 1: Use an error-aware probabilistic model. Implement a Gaussian Process within a Bayesian Optimization framework that explicitly accounts for experimental noise in its predictions. The algorithm will adjust its confidence in the data, preventing it from overreacting to spurious results [68] [97].
- Action 2: Reformulate the learning objective. Instead of modeling just the mean of the output, model its distribution to account for variability directly. Biology-aware active learning platforms have been developed to overcome this exact limitation [97].
Problem: The design space is too high-dimensional, making comprehensive exploration computationally infeasible.
Possible Cause: The "curse of dimensionality"; the number of possible experiments (e.g., combinations of pathway genes, promoters, and RBSs) is astronomically large.
Solution: Reduce the effective dimensionality of the problem.
- Action 1: Leverage low-rank representations. Use machine learning to learn a low-dimensional subspace (attention subspace) that likely contains the global optimum from a limited set of initial samples. Subsequent evolutionary computation can then efficiently search this much smaller subspace [99].
- Action 2: Employ feature selection. Use bio-inspired optimization techniques, such as Genetic Algorithms or Particle Swarm Optimization, to identify the most significant features or parameters in your system. This reduces model redundancy and computational cost [100].
Experimental Protocols & Data
Protocol: Bayesian Optimization for Metabolic Pathway Tuning
This protocol is adapted from the BioAutomata platform that successfully optimized a lycopene biosynthetic pathway [68].
Define the Optimization Problem:
- Inputs: Identify the tunable biological parts (e.g., promoter strengths for genes in your pathway of interest).
- Output: Define the objective function (e.g., lycopene titer measured by absorbance).
- Constraint: Set the budget for the number of experimental cycles.
Initial Experimental Design:
- Build an initial set of variant strains (e.g., 24 strains) using a space-filling design like Latin Hypercube Sampling to get a broad initial coverage of the design space.
Build and Test Cycle:
- Construct the designed strains using an automated foundry (e.g., iBioFAB).
- Cultivate the strains in a controlled bioreactor and measure the objective function (e.g., product titer).
Learn and Design Cycle (The AI Driver):
- Learn: Train a Gaussian Process (GP) model on all accumulated data. The GP will provide a probabilistic prediction of the performance for any untested strain.
- Design: Use the Expected Improvement (EI) acquisition function on the trained GP to recommend the next batch of strains to test. EI automatically identifies strains that are either likely to perform well or are in uncertain regions of the design space.
- Iterate steps 3 and 4 until the experimental budget is exhausted or performance converges.
The following workflow diagram illustrates this automated DBTL cycle:
Quantitative Performance of Optimization Algorithms
The table below summarizes the performance of different strategies as reported in the literature, providing a benchmark for expected outcomes.
| Algorithm / Strategy | Key Feature | Reported Performance | Biological Application Context |
|---|---|---|---|
| Bayesian Optimization (BioAutomata) [68] | Balances exploration/exploitation via Expected Improvement | Evaluated <1% of possible variants; 77% better than random screening | Lycopene biosynthetic pathway optimization |
| Hybrid G-CLPSO [98] | Combines global PSO with local Marquardt-Levenberg method | Outperformed gradient-based & stochastic search algorithms | Inverse estimation of soil hydraulic properties |
| EVOLER [99] | Machine learning-guided evolutionary computation | Finds global optimum with a probability approaching 1; 5-10x sample reduction | Power grid dispatch & nanophotonics design |
| Automated Recommendation Tool (ART) [101] | Bayesian ensemble for small data sets | Enabled 106% improvement in tryptophan production from a base strain | Multiple metabolic engineering projects |
The Scientist's Toolkit: Key Research Reagent Solutions
This table details essential computational and biological tools for implementing advanced optimization strategies in biological research.
| Item | Function / Application | Key Feature |
|---|---|---|
| Gaussian Process (GP) Model [68] | A probabilistic model that predicts the expected performance and uncertainty for untested biological designs. | Provides a measure of confidence (variance) alongside predictions, which is crucial for balancing exploration and exploitation. |
| Expected Improvement (EI) [68] | An acquisition function that recommends the next experiment by calculating the potential improvement over the current best. | Automatically handles the trade-off between exploring uncertain regions and exploiting known promising areas. |
| Bio-inspired Algorithms (e.g., GA, PSO) [100] | Optimization techniques inspired by natural processes like evolution and swarm behavior. | Effective for feature selection and hyperparameter tuning in high-dimensional biological data, reducing computational costs. |
| Automated Recommendation Tool (ART) [101] | A machine learning tool specifically designed for synthetic biology DBTL cycles. | Uses a Bayesian ensemble approach tailored to small, expensive biological datasets and provides uncertainty quantification. |
| Systems-Informed Neural Networks [102] | A deep learning method that incorporates known physical/biological laws (e.g., ODE models) into the neural network's loss function. | Makes the model robust to sparse and noisy data, ideal for inferring hidden dynamics in systems biology. |
Optimizing Computational Efficiency for Large-Scale Biological Design Spaces
Frequently Asked Questions (FAQs)
1. What are the most effective machine learning models for the low-data regime in early DBTL cycles? In the initial cycles of Design-Build-Test-Learn (DBTL), data is often limited. Research shows that gradient boosting and random forest models are particularly effective in this low-data regime. These methods have demonstrated robustness against common experimental challenges, including training set biases and experimental noise, providing a reliable foundation for early learning and recommendation [50].
2. How should I structure my DBTL cycles when the number of strains I can build is limited? When experimental resources are constrained, it is more favorable to begin with a larger initial DBTL cycle rather than distributing the same number of builds evenly across multiple cycles. A larger initial dataset provides a more substantial information base for the machine learning model to learn from, which improves the quality of its recommendations for subsequent, smaller cycles [50].
3. My biological data is heterogeneous and comes from different perturbation types and readouts. How can I integrate it? The Large Perturbation Model (LPM) is a deep-learning architecture specifically designed to integrate heterogeneous perturbation data. It works by disentangling the dimensions of Perturbation (P), Readout (R), and Context (C). This allows the model to learn generalizable rules from diverse experiments, such as those involving both CRISPR and chemical perturbations across different cellular contexts [103].
4. What computational strategies can I use to manage the "curse of dimensionality" in large-scale biological optimization? For high-dimensional problems, algorithms based on decision variable decomposition are highly effective. This involves a "divide and conquer" strategy:
- Decomposition: Large-scale problems are partitioned into smaller sub-problems.
- Space Compression: The search space is narrowed based on initial results to focus exploration on promising regions. This approach is particularly useful for fully or partially separable problems, where variables can be grouped independently [104].
5. How can I make my computational models more robust to biological noise and variability? Incorporating biology-aware active learning into your platform is key. This involves designing models that explicitly account for biological fluctuations and experimental errors during the data processing and model training phases. This approach has been successfully used to optimize complex systems, such as reformulating a 57-component serum-free cell culture medium [97].
Troubleshooting Guides
Problem 1: Poor Model Performance in Early DBTL Cycles
Symptoms: Machine learning recommendations do not lead to improved strains; model predictions have low accuracy.
| Possible Cause | Solution |
|---|---|
| Insufficient initial data | Allocate more resources to your first DBTL cycle to build a larger initial dataset for model training [50]. |
| Inappropriate ML model for low-data regime | Switch to models proven to work well with little data, such as gradient boosting or random forest, instead of data-hungry deep learning models [50]. |
| High experimental noise obscuring signals | Implement an error-aware data processing pipeline and use ML models like random forests that are robust to noise [50] [97]. |
Recommended Experimental Protocol:
- Design: Define a DNA library of components (e.g., promoters, RBS) to vary enzyme levels.
- Build: Construct an initial set of strain designs (e.g., 50-100 strains) using the library.
- Test: Measure the target output (e.g., product titer, yield) for each strain.
- Learn: Train a gradient boosting model on the dataset linking genetic designs to performance. Use a recommendation algorithm to select the next set of designs for the next DBTL cycle [50].
Problem 2: Inability to Integrate Diverse Datasets
Symptoms: Models trained on one type of experiment (e.g., CRISPR perturbations) fail to predict outcomes for another (e.g., drug treatments); data from different sources cannot be combined.
Solution: Implement a foundation model approach like the Large Perturbation Model (LPM).
Workflow for Integrating Heterogeneous Data with an LPM:
Diagram: LPM integrates diverse data by disentangling Perturbation, Readout, and Context.
Steps:
- Data Representation: Format all your experimental data into a unified structure of (P, R, C) tuples.
- P (Perturbation): e.g., a specific gRNA or drug name.
- R (Readout): e.g., a specific gene's expression or a viability metric.
- C (Context): e.g., the specific cell line and time point [103].
- Model Training: Train the LPM on the pooled collection of these tuples.
- Model Application: Use the trained model for various discovery tasks, such as predicting outcomes for new P-R-C combinations or mapping shared mechanisms of action between different perturbation types [103].
Problem 3: High-Dimensional Design Space is Computationally Intractable
Symptoms: Optimization algorithms are slow to converge; the search space is too vast to explore effectively.
Solution: Apply a decomposition and space compression algorithm (DCBA).
Logical Flow for Taming High-Dimensional Problems:
Diagram: A strategy for large-scale problems based on variable separability.
Methodology:
- Analyze Variable Interactions: Determine if your problem is fully separable, partially separable, or fully non-separable [104].
- Decompose the Problem:
- If fully separable, optimize each decision variable (e.g., enzyme concentration) independently.
- If partially separable, decompose variables into interacting groups and optimize each group separately.
- If fully non-separable, apply specialized grouping methods to reduce the search space as much as possible [104].
- Compress the Search Space: Use linear search methods (e.g., interval estimation) to identify promising regions of the search space and narrow down the exploration scope, thereby improving efficiency [104].
The Scientist's Toolkit: Research Reagent Solutions
| Item | Function in Experiment |
|---|---|
| DNA Component Library | A predefined set of genetic parts (e.g., promoters, RBS) used to systematically vary enzyme expression levels in a pathway [50]. |
| Perturbation Agents | Chemical compounds (drugs) or genetic tools (CRISPR gRNAs) used to systematically perturb a biological system and measure the outcome [103]. |
| Kinetic Model (e.g., SKiMpy) | A mechanistic model that uses ordinary differential equations to simulate metabolic pathway behavior, useful for generating in-silico training data and testing ML methods [50]. |
| Large Perturbation Model (LPM) | A deep-learning foundation model that integrates diverse perturbation data by learning disentangled representations of Perturbations, Readouts, and Contexts [103]. |
| Cooperative Co-evolution (CC) Framework | An optimization algorithm that uses a "divide-and-conquer" strategy to break down large-scale problems into smaller, more manageable sub-problems [104]. |
Comparative Data on Machine Learning Approaches
Table 1: Comparison of ML Methods for DBTL Cycle Guidance
| Machine Learning Method | Best Use Case | Key Advantages | Considerations |
|---|---|---|---|
| Gradient Boosting / Random Forest | Early DBTL cycles with limited data [50] | Robust to noise and training set bias; performs well in low-data regimes [50] | May be outperformed by deep learning with very large datasets |
| Automated Recommendation Tool | Recommending new strain designs with a defined exploration/exploitation trade-off [50] | Provides a predictive distribution to sample from for the next cycle [50] | Performance can vary with pathway complexity [50] |
| Large Perturbation Model (LPM) | Integrating heterogeneous data across perturbations, readouts, and contexts [103] | State-of-the-art predictive accuracy; enables multiple discovery tasks [103] | Cannot predict for completely new (out-of-vocabulary) contexts [103] |
| Encoder-Based Foundation Models (e.g., Geneformer) | Tasks where context can be inferred from gene expression profiles [103] | Can make predictions for unseen contexts [103] | Performance can be limited by signal-to-noise ratio in data [103] |
Detailed Experimental Protocol: Simulating DBTL Cycles with a Kinetic Model
This protocol allows for benchmarking machine learning methods without the cost of wet-lab experiments [50].
1. Define and Build the In-Silico Model:
- Representation: Use a mechanistic kinetic model (e.g., the E. coli core kinetic model in SKiMpy) to represent your metabolic pathway of interest embedded in a realistic cell physiology model.
- Pathway Integration: Introduce a synthetic pathway into the core model.
- Bioprocess Context: Embed the cell model within a basic bioprocess model (e.g., a 1L batch reactor) to simulate growth and production dynamics.
2. Simulate the DBTL Workflow:
- Design: Define a library of enzyme expression levels by planning changes to the
Vmaxparameters in the model for multiple pathway enzymes. - Build (In-Silico): "Build" a set of strain designs by running the model with different combinations of
Vmaxvalues. - Test: Record the simulated product flux (e.g., for compound G) for each in-silico strain.
- Learn: Train a machine learning model (e.g., Gradient Boosting) on the dataset linking
Vmaxchanges to product flux.
3. Benchmark and Optimize:
- Use the framework to test different ML methods, recommendation algorithms, and DBTL cycle strategies (e.g., varying the number of builds per cycle).
- Identify the most computationally efficient strategy for your in-silico pathway before moving to wet-lab experiments [50].
Benchmarks and Efficacy: Validating ML Performance in Biological DBTL Cycles
I searched for technical support information on "Kinetic Model-Based Frameworks for Simulated DBTL Benchmarking" but could not find troubleshooting guides, FAQs, or the specific quantitative data required to build the technical support center you requested.
The available search results were dominated by information on website color contrast and color palettes, which is not relevant to your topic [105] [106] [107]. One result mentioned DBTL cycles in a biological context but did not contain troubleshooting information [72]. Another discussed parameter estimation in kinetic models but was not framed within a DBTL context or structured for user support [108].
To help you find the necessary information, I suggest:
- Using more specific search terms, such as "troubleshooting kinetic parameter estimation DBTL" or "common errors design-build-test-learn cycle simulation".
- Searching in specialized academic databases like PubMed, IEEE Xplore, or Google Scholar for full-text papers that may include troubleshooting sections.
If you would like, I can perform a new search using these more targeted strategies. Please let me know if you would like me to try again.
FAQs: Model Selection and Fundamentals
What are the fundamental algorithmic differences between Gradient Boosting and Random Forest?
Gradient Boosting (GB) and Random Forest (RF) are both ensemble methods based on decision trees, but they operate on fundamentally different principles.
Random Forest uses a technique called bagging (Bootstrap Aggregating). It builds multiple decision trees independently, each on a randomly selected subset of the training data and a random subset of features. The final prediction is determined by averaging (for regression) or majority voting (for classification) the predictions of all individual trees. This parallel, independent construction makes RF robust and less prone to overfitting [109] [110].
Gradient Boosting, in contrast, uses a boosting technique. It builds trees sequentially, where each new tree is trained to correct the residual errors made by the ensemble of previous trees. This sequential, dependency-based approach often leads to higher accuracy but also increases the risk of overfitting, especially if the model is not properly regularized [111] [109] [110].
The table below summarizes their core differences:
Table 1: Fundamental Differences Between Gradient Boosting and Random Forest
| Feature | Gradient Boosting (GB) | Random Forest (RF) |
|---|---|---|
| Ensemble Method | Boosting | Bagging |
| Tree Relationship | Sequential, dependent | Parallel, independent |
| Primary Goal | Reduce bias and correct errors | Reduce variance |
| Tree Structure | Typically uses weaker learners (e.g., shallow trees) | Typically uses strong, fully grown learners (deep trees) |
| Training Speed | Generally slower due to sequential training | Generally faster due to parallel training [110] |
In a low-data regime, which model is typically more stable and why?
In low-data regimes, Random Forest is often more stable and less prone to overfitting [111] [110].
The key reason is its fundamental use of bagging. By building trees on bootstrapped datasets and averaging their results, RF effectively reduces variance. This is crucial when data is scarce, as statistical fluctuations in a small dataset can lead a complex model to learn noise instead of the underlying signal. RF's independence between trees helps mitigate this risk [109] [112].
Gradient Boosting, while powerful, is more sensitive to noisy data and hyperparameter settings. Its sequential nature can cause it to overfit to the noise in the training data if the number of trees is too high or the learning rate is not appropriately tuned [110]. A study on construction waste prediction with small datasets found that "the bagging technique (RF) predictions were more stable and accurate than those of the boosting technique (GBM)" [111].
How does the exploration-exploitation trade-off relate to these models in a DBTL cycle?
In the context of a Design-Build-Test-Learn (DBTL) cycle for research like drug discovery, the exploration-exploitation trade-off is paramount.
- Random Forest embodies exploration. By building diverse trees on random data and feature subsets, it broadly explores the feature space. This is analogous to screening a wide variety of candidate molecules to map the chemical landscape without over-committing to a single hypothesis early on [112].
- Gradient Boosting embodies exploitation. It sequentially focuses its resources on the hardest-to-predict samples (the errors), refining the model to exploit known patterns for maximum accuracy. This is similar to lead optimization, where a promising compound is iteratively improved [113].
A balanced DBTL strategy might use RF for early-stage exploration (e.g., virtual screening of large compound libraries) to identify promising regions of chemical space. As the cycle narrows the focus, GB can be leveraged for exploitation (e.g., predicting the potency of refined analogs) to achieve high predictive accuracy on a more targeted set of candidates [113]. This balance is critical for efficient resource allocation, mirroring the principles of Bayesian bandit algorithms that manage this trade-off in decision-making under uncertainty [114].
Diagram 1: Model Integration in a DBTL Cycle. RF guides broad exploration with limited data, while GB enables focused exploitation once a stable hypothesis is formed.
Troubleshooting Guides
Issue 1: Poor Model Performance on a Small, Imbalanced Dataset
This is a common challenge in biomedical research, where positive outcomes (e.g., successful drug candidates) are rare.
Diagnosis: Your model's performance metrics (e.g., AUC, accuracy) are unsatisfactory. The model may be ignoring the minority class because the dataset is imbalanced, a frequent issue in studies with rare outcomes [112].
Resolution Protocol:
- Data-Level Interventions:
- Class Balancing: Implement class balancing techniques directly within the model training.
- For Random Forest, you can create class-balanced bootstrapped datasets by under-sampling the majority class or over-sampling the minority class during the tree construction phase [112].
- For Gradient Boosting, the algorithm naturally focuses on difficult-to-predict instances over sequential rounds, which can help with imbalance. However, ensure you are using an appropriate loss function [109].
- Inverse Probability Weighting (IPW): If your data comes from a stratified sampling design (e.g., two-phase sampling in clinical trials), incorporate IPW into your performance calculation (like AUC) and, if supported, into the model's loss function to generalize results to the full cohort [112].
- Class Balancing: Implement class balancing techniques directly within the model training.
- Model-Level Interventions:
- Variable Screening: In high-dimensional, small-sample settings (e.g., 420 biomarkers for 150 observations), use supervised variable screening like Lasso regression to select the most informative features before training the ensemble model. This reduces noise and can significantly improve performance [112].
- Hyperparameter Tuning: Carefully tune hyperparameters. For GB, the learning rate and number of trees are critical; a low learning rate with more trees generally performs better but requires more computation. For RF,
max_featuresis a key parameter to adjust.
Important Note: The effectiveness of these interventions can interact. One study found that class balancing improves RF performance when used alone, but can have a negative impact when applied after variable screening. Therefore, test combinations systematically [112].
Diagram 2: Troubleshooting Workflow for Small, Imbalanced Data. Interventions depend on data characteristics like dimensionality.
Issue 2: The Model is Overfitting
Diagnosis: The model performs excellently on training data but poorly on validation/test data. GB is particularly susceptible to this, especially with noisy data and many iterations [110].
Resolution Protocol for Gradient Boosting:
- Increase Regularization: GB implementations like XGBoost have strong regularization parameters. Tune the L1 (lambda) and L2 (alpha) regularization terms to penalize complex models [113].
- Reduce Model Complexity: Lower the maximum depth of individual trees, forcing them to be weaker learners. This is a primary method to combat overfitting in GB [110].
- Slow the Learning: Decrease the learning rate and increase the number of trees proportionally. This makes each correction step smaller and requires more trees to learn, leading to a more generalized model [113] [115].
- Use Early Stopping: Train the model on a validation set and stop the training process when the validation performance stops improving, preventing the model from learning noise in the training data over many rounds.
Resolution Protocol for Random Forest:
- Reduce Tree Depth: Although RF is generally robust to overfitting, it can still occur with very deep trees. Limiting
max_depthcan help. - Increase Randomness: Use more features per split (
max_features) to further decorrelate the trees. - Gather More Data: If possible, this is the most effective solution. RF performance is known to scale well with data size [110].
Table 2: Key Hyperparameters to Control Overfitting
| Model | Hyperparameter | Effect on Overfitting | Recommendation for Low-Data |
|---|---|---|---|
| Gradient Boosting | learning_rate |
Lower rate = more robust generalization | Use a low value (0.01-0.1) with high n_estimators [113]. |
max_depth |
Lower depth = simpler trees, less overfitting | Start shallow (e.g., 3-6) [110]. | |
n_estimators |
Too many can lead to overfitting | Use early stopping to find the optimal number [113]. | |
subsample |
< 1.0 introduces randomness (row sampling) | Use values like 0.8 to train on data subsets [113]. | |
| Random Forest | max_features |
Lower values increase tree diversity | Use sqrt or log2 of total features [112]. |
min_samples_leaf |
Higher values prevent over-specific leaves | Increase from the default value (e.g., 3, 5) [112]. |
Issue 3: Excessively Long Training Times
Diagnosis: Model training takes impractically long, slowing down the DBTL cycle.
Resolution Protocol:
- Choose a Faster Algorithm Variant: For Gradient Boosting, different implementations offer significant speed gains. LightGBM uses histogram-based methods and a leaf-wise growth strategy, often making it the fastest to train, especially on larger datasets [113].
- Leverage Hardware and Software: Ensure you are using implementations that support parallel processing (e.g., XGBoost, LightGBM). RF can also be parallelized, as trees are built independently [113].
- Reduce Data Dimensionality: As before, applying variable screening to reduce the number of features fed to the model will drastically cut training time [112].
- Adjust Hyperparameters: For GB, reducing
max_depthnot only fights overfitting but also speeds up training. For both GB and RF, reducingn_estimatorswill directly lower training time, though at the potential cost of performance.
The Scientist's Toolkit: Essential Research Reagents
This table outlines key "reagents" or methodological components for successfully applying these models in low-data drug discovery research.
Table 3: Essential Reagents for ML Experiments in Low-Data Regimes
| Research Reagent | Function | Example Use-Case / Note |
|---|---|---|
| Leave-One-Out Cross-Validation (LOOCV) | Performance evaluation for very small datasets. Uses nearly all data for training, providing a robust performance estimate [111]. | Ideal when n < 100. Computationally expensive but maximizes data utility [111]. |
| Lasso (L1) Regression | Supervised variable screening. Removes irrelevant features by forcing weak coefficients to zero, reducing dimensionality [112]. | Pre-processing step before training RF or GB on high-dimensional biomarker data [112]. |
| Inverse Probability Weighting (IPW) | Corrects for bias introduced by non-random sampling designs (e.g., two-phase sampling in clinical trials) [112]. | Ensures model performance is generalizable to the full cohort, not just the sampled subset [112]. |
| Synthetic Minority Over-sampling (SMOTE) | Algorithmic data augmentation for imbalanced classes. Generates synthetic samples for the minority class [55]. | An alternative to simple random over-sampling. Can be applied before model training. |
| XGBoost / LightGBM / CatBoost | Optimized GB implementations with built-in regularization, faster training, and handling of categorical data [113]. | XGBoost often has top predictive performance; LightGBM is fastest for large data; CatBoost handles categorical features well [113]. |
Frequently Asked Questions
1. What are the most relevant metrics for quantifying exploration and exploitation in a DBTL cycle? The most relevant metrics depend on whether you are assessing the behavior of a learning algorithm (like a multi-armed bandit) or a human decision-maker. For algorithmic assessment in a DBTL context, the cumulative reward over iterations is a primary metric [10]. For decomposing human decision-making on tasks like the Iowa Gambling Task, computational models like the Value plus Sequential Exploration (VSE) model can extract specific parameters [116]:
- For Exploitation: Reinforcement sensitivity (weight of recent rewards) and inverse decay (number of past outcomes guiding choices).
- For Exploration: Maximum directed exploration value (propensity to try novel actions for information).
2. Our DBTL cycle seems to get stuck on suboptimal solutions. Are we exploring enough? This is a classic sign of under-exploration. You can diagnose this by tracking the diversity of tested options. In a genetic part optimization cycle, for instance, this could be the sequence space coverage of your designed RBS variants [10]. A low diversity score suggests your design policy is overly exploitative. To correct this, consider incorporating strategies that explicitly value uncertainty, such as the Upper Confidence Bound (UCB) algorithm, which balances testing high-performing options (exploitation) with probing uncertain ones (exploration) [10].
3. How can we measure the "balance" between exploration and exploitation? Balance is not a fixed 50/50 split but a dynamic state. It can be assessed by analyzing the temporal trend of your strategy. In early DBTL cycles, you should observe a higher rate of exploration (e.g., more random action selection in an epsilon-greedy strategy or a higher UCB exploration weight). As cycles progress, the system should progressively shift towards exploitation, indicated by a stabilization of the top-performing solution and a decrease in the performance variance of tested options [5] [10]. A failure to show this shift may indicate ineffective learning.
4. In a research organization, how do performance metrics affect the exploration-exploitation balance? Organizational metrics can profoundly influence this balance. Excessively detailed, short-term productivity metrics can push researchers towards pure exploitation ("doing things right"), stifling the creativity and risk-taking required for foundational exploration ("doing the right things") [117]. The optimal level of performance measurement is "performance-driven empowerment," which provides feedback without micromanagement, thus maintaining motivation for both exploratory and exploitative activities [117].
Troubleshooting Guides
Problem: Algorithm Converges Too Quickly, Likely on a Local Optimum
- Symptoms: High initial performance gains that quickly plateau; low diversity in the selected options or designs in subsequent DBTL cycles.
- Possible Causes & Solutions:
- Cause 1: Overly greedy strategy. The algorithm is exclusively choosing the best-known option without probing potentially better ones.
- Solution: Introduce an explicit exploration mechanism. Replace a purely greedy selection with an epsilon-greedy or Softmax strategy, which occasionally selects sub-optimal or random actions [118] [4]. Alternatively, adopt an Upper Confidence Bound (UCB) method, which quantifies uncertainty and systematically explores options with high potential [10].
- Cause 2: Inadequate credit assignment. The algorithm cannot link short-term exploratory actions to their long-term benefits.
- Solution: Ensure your learning model has memory (e.g., a recurrent neural network) and is trained with a long enough horizon to credit early exploration for later successes [119]. In meta-reinforcement learning, recurring environmental structure is key for exploration to emerge organically from a greedy objective [119].
- Cause 1: Overly greedy strategy. The algorithm is exclusively choosing the best-known option without probing potentially better ones.
Problem: Excessive Exploration Leading to High Costs and Slow Progress
- Symptoms: High variability in outcomes with no clear performance improvement over many cycles; resources are spent on clearly inferior options.
- Possible Causes & Solutions:
- Cause 1: Fixed, high exploration rate. For example, an epsilon-greedy strategy with a constant, high value for epsilon.
- Solution: Implement a decaying exploration rate. Systematically reduce the exploration parameter (e.g., epsilon) over time as your model becomes more confident in its predictions [5].
- Cause 2: Lack of directed exploration. The exploration is random rather than informative.
- Solution: Shift from random to directed or optimistic exploration. Methods like UCB guide exploration towards uncertain regions that are also promising [8] [10]. Computational models show that increased directed exploration is linked to better real-world outcomes, such as reduced substance use [116].
- Cause 1: Fixed, high exploration rate. For example, an epsilon-greedy strategy with a constant, high value for epsilon.
Problem: Inconsistent or Noisy Results Making it Hard to Identify the Best Option
- Symptoms: The perceived best option changes frequently between cycles; high uncertainty in performance measurements.
- Possible Causes & Solutions:
- Cause 1: High measurement noise or deceptive reward signals.
- Solution: Improve the quality and consistency of your experimental "Test" phase. For biological assays, this often involves laboratory automation to ensure high-quality, reproducible data for the "Learn" phase [10].
- Cause 2: The learning model is overreacting to noisy data.
- Solution: Use learning algorithms that provide uncertainty estimates, such as Gaussian Process Regression (GPR). A policy can then be designed to exploit options with high expected performance while exploring those with high uncertainty, leading to more robust convergence [10].
- Cause 1: High measurement noise or deceptive reward signals.
Quantitative Metrics for Exploration and Exploitation
The table below summarizes key metrics for evaluating exploration and exploitation capabilities, drawing from computational modeling, reinforcement learning, and applied DBTL research.
| Category | Metric Name | Description | Interpretation & Application in DBTL |
|---|---|---|---|
| Exploitation Metrics | Reinforcement Sensitivity [116] | A computational parameter reflecting how strongly an agent's choices are influenced by the most recent rewards. | A lower value may indicate an inability to effectively exploit known good options, as seen in studies of human decision-making [116]. |
| Choice Consistency / Inverse Decay [116] | The number of past outcomes used to guide current choices. Measures the reliance on established knowledge. | Higher values indicate stable exploitation of a strategy. Increased use of past outcomes predicts better real-world outcomes [116]. | |
| Exploration Metrics | Directed Exploration Value [116] | The computed value of trying novel actions specifically to gain new information. | Higher values indicate purposeful, information-seeking exploration. This has been shown to predict greater success in behavioral change interventions [116]. |
| Random Exploration | Exploration without the conscious goal of gaining new information, often manifesting as frequent shifting between choices [116]. | Can be a sign of dysfunction when excessive, as it leads to inefficiency and a failure to stabilize on high-performing options [116]. | |
| Balance & Outcome Metrics | Cumulative Reward [10] | The total reward accrued over the entire sequence of actions in a DBTL cycle or experiment. | The ultimate measure of success. An effective balance will show a steep increase that plateaus at a high level. |
| Strategy Selection (e.g., UCB) [10] | The use of a policy that mathematically balances the estimated value of an option and the uncertainty around that estimate. | Directly implements the trade-off. The UCB algorithm is successfully used in the Design phase of DBTL cycles to recommend new genetic variants to test [10]. | |
| Behavioral Metrics | Action Diversity | The variety of different options or actions taken within a given window of DBTL cycles. | In early cycles, high diversity is desirable. A premature drop in diversity suggests under-exploration. |
Experimental Protocol: Implementing a Bandit-Based DBTL Cycle
This protocol details the methodology for using a multi-armed bandit approach to balance exploration and exploitation in an iterative design cycle, as demonstrated in bacterial RBS optimization [10].
1. Objective Definition
- Define the optimization goal (e.g., maximize protein expression via Translation Initiation Rate - TIR).
- Define the design space (e.g., all possible 20-base pair RBS sequences with a fixed genetic context).
2. Initialization (Cycle 0)
- Build & Test: Construct and test a small, random batch of variants from the design space to gather initial data.
- Learn: Train a Gaussian Process Regression (GPR) model on the collected data. GPR is ideal as it provides both a predicted mean TIR and a standard deviation (uncertainty) for every possible sequence [10].
3. Iterative DBTL Cycles
- Design: Use the Upper Confidence Bound (UCB) algorithm to recommend the next batch of variants. For each candidate sequence, calculate:
UCB Score = Predicted Mean TIR + β * Predicted Standard Deviation- Select the sequences with the highest UCB scores. The
βparameter explicitly controls the exploration-exploitation balance [10].
- Build & Test: Physically construct the recommended variants and measure their performance (e.g., TIR) using high-throughput, automated methods to ensure data quality [10].
- Learn: Update the GPR model with the new experimental data, refining its predictions and uncertainty estimates for the next cycle.
Workflow Diagram: Machine Learning-Guided DBTL with Bandit Decision
The following diagram illustrates the integrated workflow where machine learning is used in both the Learn and Design phases to manage the exploration-exploitation trade-off.
The Scientist's Toolkit: Research Reagent Solutions
| Item / Solution | Function in the Context of Explore/Exploit DBTL |
|---|---|
| Gaussian Process Regression (GPR) | A Bayesian machine learning model used in the Learn phase to predict the performance of untested variants and, crucially, to quantify the uncertainty of its own predictions [10]. |
| Upper Confidence Bound (UCB) Algorithm | A multi-armed bandit algorithm used in the Design phase. It uses the mean prediction and uncertainty from the GPR to recommend sequences that either have high expected performance (exploit) or high potential for improvement (explore) [10]. |
| Laboratory Automation & HTS | High-Throughput Screening (HTS) systems in the Build and Test phases are critical for generating the large, high-quality, and reproducible data sets required to effectively train machine learning models and reduce noise in the feedback loop [10]. |
| Recurrent Neural Network (RNN) | A type of neural network with memory, used in meta-RL agents. It allows the agent to retain information across episodes, which is a key condition for organic exploratory behavior to emerge from a pure exploitation objective in recurring environments [119]. |
| Iowa Gambling Task (IGT) | A psychological paradigm used to study human decision-making. It can be coupled with computational models (like the VSE model) to decompose and quantify the exploration and exploitation parameters of research participants or clinical populations [116]. |
Troubleshooting Guides and FAQs
FAQ 1: How can machine learning address the exploration-exploitation trade-off in metabolic engineering?
Answer: In metabolic engineering, the exploration-exploitation trade-off is central to iterative Design-Build-Test-Learn (DBTL) cycles. Exploration involves testing new, genetically diverse strain designs to identify high-performing regions, while exploitation focuses on optimizing known promising designs. Machine learning (ML) balances this by using data from built strains to recommend new designs, preventing costly combinatorial explosions [50]. For example, gradient boosting and random forest models have proven robust for this in low-data scenarios, effectively learning from small initial datasets to guide subsequent cycles [50]. Bayesian methods also naturally handle this trade-off by quantifying uncertainty in predictions [114].
FAQ 2: What are common causes of low terpenoid yield in engineeredE. coli, and how can they be resolved?
Answer: Low limonene yield in E. coli often stems from two main bottlenecks:
- Insufficient Precursor Supply: The native MEP pathway may not produce enough building blocks (IPP and DMAPP).
- Inefficient Pathway Flux: The downstream enzymes may not efficiently convert precursors to the target product.
- Solution: Systematically optimize the expression of limonene biosynthesis genes (gpps and ls). Use combinatorial optimization and ribosome binding site (RBS) engineering to balance enzyme levels. Employing a neryl pyrophosphate synthase (NPPS) can also create a more efficient route to limonene [121].
FAQ 3: How can low astaxanthin productivity inPhaffia rhodozymafermentations be improved?
Answer: Low astaxanthin productivity in P. rhodozyma can be addressed by optimizing fermentation parameters and nitrogen sources:
- Nitrogen Source Composition: The type and ratio of nitrogen sources significantly impact yield. A mixture of beef extract, potassium nitrate (KNO₃), and ammonium sulfate ((NH₄)₂SO₄) is often optimal, as determined by mixture design experiments [122].
- Fermentation Parameters: Key physical parameters must be tightly controlled.
FAQ 4: What steps can be taken to validate an ML model's recommendations in a biological context?
Answer: Validating ML recommendations is crucial before committing to costly experiments.
- Retrospective Validation: Compare the ML model's top recommendations against historical experimental results and the actual prescribed treatments. For example, a study on antibiotic recommendations showed the ML model's top three options had success rates of 91-97%, significantly outperforming physician prescription rates [124].
- In Silico Frameworks: Use mechanistic kinetic models to simulate a metabolic pathway and generate in silico data. This allows for benchmarking ML methods and recommendation algorithms over multiple simulated DBTL cycles before real-world application [50].
Table 1: Limonene Production in EngineeredE. coli
| Optimization Strategy | Host | Key Genetic Modifications | Final Titer (mg/L) | Citation |
|---|---|---|---|---|
| MEP Pathway Enhancement | E. coli BL21(DE3) | GPPS, LS, DXS, IDI overexpression | 35.8 mg/L | [120] |
| Systematic MVA Pathway | Engineered E. coli | Site-mutated EfMvaS, tuned EfMvaE/EfMvaSA110G, MmMK, ScPMK, ScPMD, ScIDI, SlNPPS, MsLS | 1.29 g/L (1290 mg/L) | [121] |
Table 2: Astaxanthin Production inPhaffia rhodozyma
| Optimization Method | Strain | Key Conditions / Strategy | Final Astaxanthin Yield | Citation |
|---|---|---|---|---|
| Nitrogen Source Optimization | P. rhodozyma 7B12 | Optimal mix: 0.28 g/L (NH₄)₂SO₄, 0.49 g/L KNO₃, 1.19 g/L beef extract | 7.71 mg/L (Biomass)1.00 mg/g (Cell Content) | [122] |
| Parameter Optimization & LSTM | P. rhodozyma GDMCC 2.218 | Temperature 20°C, pH 4.5, DO 20%, Fed-batch in 5L bioreactor | 400.62 mg/L | [123] |
Detailed Experimental Protocols
Protocol 1: Systematic Optimization of Limonene inE. colivia the MVA Pathway
Methodology:
- Upstream Module Engineering:
- Perform site-directed mutation on the enzyme EfMvaS.
- Use ribosome binding site (RBS) engineering to tune the translation of EfMvaE and the mutant EfMvaSA110G to enhance mevalonate production [121].
- Midstream Module Construction:
- Express MmMK alongside ScPMK, ScPMD, and ScIDI under a strong, regulated promoter (e.g., FAB80) to convert mevalonate to the IPP/DMAPP precursors [121].
- Downstream Module Assembly:
- Co-express a neryl pyrophosphate synthase (SlNPPS) and a limonene synthase (MsLS) to channel precursors toward limonene synthesis [121].
- Fed-Batch Fermentation:
- Cultivate the final engineered strain (e.g., ELIM78) in a shake-flask using a fed-batch process over 84 hours to achieve high-titer production [121].
Protocol 2: High-Yield Astaxanthin Production via Parameter Optimization and LSTM Modeling
Methodology:
- Strain and Inoculum:
- Bioreactor Cultivation and Optimization:
- Inoculate a 500 mL bioreactor with 5% inoculum.
- Systematically test gradients of temperature (20, 22, 25, 28°C), pH (3.5, 4.0, 4.5, 5.0), and dissolved oxygen (10, 20, 30, 40%) in separate experiments [123].
- Employ a batch-feeding strategy, adding feed medium when the agitation speed begins to drop, indicating nutrient depletion [123].
- LSTM Model Construction:
- Collect time-series data from multiple bioreactor runs (e.g., pH, DO, temperature, wet weight).
- Preprocess data (batch identification, time-series alignment, Z-score normalization).
- Construct an LSTM model to predict astaxanthin concentration dynamically throughout the fermentation. Use 15 batches of data for training and validation [123].
- Scale-Up:
- Transfer the optimized parameters to a 5 L bioreactor system to validate the process at a larger scale [123].
Pathway and Workflow Diagrams
Limonene Biosynthesis Pathway
ML-Driven DBTL Cycle
Research Reagent Solutions
Table 3: Essential Reagents for Metabolic Engineering and Fermentation
| Reagent / Material | Function / Application | Example from Context |
|---|---|---|
| Neryl Pyrophosphate Synthase (NPPS) | Provides an alternative, efficient enzymatic route for limonene precursor synthesis. | Salvia lycioides NPPS (SlNPPS) used to improve limonene yield [121]. |
| Limonene Synthase (LS) | Cyclizes the linear precursor (GPP or NPP) to form limonene. | Mentha spicata LS (MsLS) expressed in E. coli [121] [120]. |
| Geranyl Diphosphate Synthase (GPPS) | Condenses IPP and DMAPP to form Geranyl Diphosphate (GPP). | Abies grandis GPPS used in initial pathway construction [120]. |
| Rate-Limiting Enzymes (DXS, IDI) | Overexpression enhances flux through the native MEP pathway. | E. coli DXS and IDI genes cloned and overexpressed to boost precursor supply [120]. |
| Optimized Nitrogen Source Mix | Critical for balancing microbial growth and pigment production in P. rhodozyma. | Specific mixture of (NH₄)₂SO₄, KNO₃, and beef extract [122]. |
| Two-Phase Culture System | In-situ extraction of inhibitory products (like limonene) to improve titer. | Use of n-hexadecane overlay in E. coli fermentations [120]. |
Assessing Robustness to Experimental Noise and Training Set Biases
FAQs on Noise and Bias in ML for DBTL Research
Q1: What is the practical difference between model bias and variance in a DBTL screening campaign?
A high-bias model is too simplistic and systematically underfits the data, failing to capture complex structure-activity relationships. This leads to high error rates and poor generalization, causing a DBTL cycle to miss promising compound candidates. In contrast, a high-variance model is overly complex and overfits to the noise and specific samples in the training data. It performs well on training data but fails on new, unseen data from the next cycle, misguiding exploitation efforts [125] [126].
Q2: Our high-throughput screening data is noisy. Which ML algorithms are inherently more robust?
Some algorithms are naturally more resilient to noise [127]:
- Random Forests / Decision Trees: Their hierarchical structure and ensemble averaging make them less sensitive to outliers.
- Support Vector Machines (SVMs): By focusing on maximizing the margin between classes, they can be less influenced by noisy data points distant from the decision boundary.
- Robust Regression (Ridge/Lasso): These techniques use regularization to penalize overly complex models, mitigating the impact of noisy data.
Q3: How can we detect if our training data for a toxicity prediction model is biased?
Bias can manifest in several ways. Look for these red flags in your dataset [128] [126] [129]:
- Missing Feature Values: If data for key molecular descriptors or assay results is missing for a large subset of compounds, it could indicate under-representation.
- Data Skew: The dataset may overrepresent certain chemical scaffolds (e.g., heteroaromatics) while underrepresenting others (e.g., macrocycles), relative to the chemical space you wish to explore.
- Unexpected Feature Values: Physicochemically implausible values for molecular weight or logP can indicate measurement or data entry errors.
- Performance Disparities: The model's accuracy, precision, or recall may be significantly worse for specific molecular subgroups than the overall performance.
Q4: What is a straightforward method to improve model robustness against feature noise?
A recent approach is to use data abstractions as a preprocessing step. This method generalizes numerical features (e.g., converting a continuous molecular weight value into a binned category like "low," "medium," or "high"). While this may cause a slight loss of information, it has been shown to improve robustness to noise by reducing the model's sensitivity to small, potentially irrelevant fluctuations in the input data [130] [131].
Q5: How does mitigating bias relate to the exploration-exploitation trade-off in DBTL?
Mitigating bias is crucial for effective exploration. A biased model, trained on non-representative historical data, will have a skewed understanding of the chemical space. It will likely only "exploit" areas similar to past successes, potentially causing the cycle to miss novel, high-performing scaffolds in unexplored regions. Actively debiasing data and models ensures a more accurate and reliable fitness landscape, leading to better-informed decisions on where to explore next [126] [132].
Troubleshooting Guides
Problem: Model Performance is High in Training but Drops Significantly in Experimental Validation
This is a classic sign of overfitting, where the model has high variance and learns the noise in the training data [125].
Step 1: Diagnose the Cause.
- Check if your training dataset is too small relative to the problem's complexity.
- Audit the data for label noise (e.g., incorrect biological activity labels due to assay variability) [133].
- Evaluate whether the training and validation sets come from different distributions (e.g., different assay protocols).
Step 2: Apply Corrective Measures.
- Implement Regularization: Use L1 (Lasso) or L2 (Ridge) regularization to penalize model complexity and prevent overfitting [127].
- Use Ensemble Methods: Employ bagging (e.g., Random Forests) or boosting to combine multiple models, reducing variance and improving generalization [127] [125].
- Early Stopping: When training iterative models like neural networks, stop the training once performance on a held-out validation set starts to degrade, preventing the model from memorizing noise [133].
- Data Augmentation: If possible, use techniques to generate synthetic but realistic training examples (e.g., small molecular perturbations) to expand the diversity of your training set [127].
Problem: Model Performs Poorly for Specific Molecular Subclasses
This indicates potential sampling or selection bias in your training data, where certain subgroups are underrepresented [126] [132].
Step 1: Identify the Underperforming Subgroups.
- Do not just look at aggregate performance metrics. Break down model performance (accuracy, F1-score) by relevant subgroups, such as specific functional groups, molecular weight ranges, or compound sources [128].
Step 2: Mitigate the Bias.
- Data-Level Interventions:
- Strategic Oversampling: Oversample the underrepresented subclasses in your training data.
- Reweighting: Assign higher weights to examples from the underrepresented groups during model training to increase their influence [129].
- Algorithm-Level Interventions:
- Adversarial Debiasing: Employ a technique where the model learns to make accurate predictions while simultaneously making it difficult for an adversary to predict the protected attribute (e.g., the compound subclass) [126] [129].
- Use Fairness-Aware Algorithms: Implement algorithms that include explicit fairness constraints to ensure equitable performance across groups [126].
- Data-Level Interventions:
The following workflow diagram outlines the core process for diagnosing and mitigating these issues within a DBTL cycle:
Bias Mitigation Protocol in Model Training
This diagram details a specific mitigation strategy from the troubleshooting guide, showing how to integrate bias checks and corrections directly into your training pipeline.
Data and Metrics Reference
Table 1: Common Types of Noise in Experimental Data and Their Mitigation
| Type of Noise | Description | Potential Impact on Model | Mitigation Strategies |
|---|---|---|---|
| Label Noise [133] | Incorrect or misrepresented target values (e.g., mislabeled compound activity in HTS). | Degrades model accuracy, leads to poor generalization and unreliable predictions. | Use robust loss functions (e.g., Generalized Cross Entropy), confident learning to estimate label errors, and early stopping [133]. |
| Feature Noise [127] | Errors or randomness in input features (e.g., inaccuracies in calculated molecular descriptors). | Obscures true structure-activity relationships, reduces model's predictive power. | Data cleaning (outlier detection), use of robust algorithms (Random Forests, SVMs), and data abstraction [127] [131]. |
| Measurement Noise [127] | Inaccuracies from the data collection process itself (e.g., instrument error in IC50 assays). | Introduces uncertainty, can lead to both bias and variance in model predictions. | Sensor calibration, signal processing filters, and repeated measurements to average out noise. |
Table 2: Key Metrics for Evaluating Fairness and Bias in Predictive Models
When assessing model performance across different subgroups, accuracy alone can be misleading. The following metrics help quantify bias and fairness [129]:
| Metric | Formula / Principle | Interpretation in a DBTL Context |
|---|---|---|
| Disparate Impact | Ratio of positive outcome rates between an unprivileged and a privileged group. | Measures if promising compounds from a novel chemical series (unprivileged group) are selected at a similar rate to well-established series (privileged group). A value close to 1.0 indicates fairness. |
| Equal Opportunity Difference [129] | (True Positive Rateunprivileged - True Positive Rateprivileged) | Ensures that active compounds are found with equal success across different chemical classes. A value of 0 is ideal. |
| Demographic Parity | The probability of a positive outcome (e.g., being selected for testing) is independent of the protected attribute. | Ensures the model does not unfairly favor one subgroup over another when selecting compounds for the next DBTL cycle. |
The Scientist's Toolkit: Research Reagent Solutions
This table lists key computational and methodological "reagents" for building robust ML models in DBTL research.
| Item / Solution | Function | Key Considerations |
|---|---|---|
| Data Abstractions [130] [131] | Preprocessing step to convert continuous features into discrete bins, improving noise robustness. | Trade-off: Increases robustness but may cause a slight reduction in overall accuracy due to information loss. Methods include quantile binning and ROC-based binning. |
| Adversarial Debiasing [126] [129] | A technique used during training to reduce the model's ability to predict a sensitive attribute (e.g., compound source), promoting fairness. | Helps the model learn features that are predictive of activity but independent of the biased subgroup associations. |
| Robust Loss Functions [133] | Loss functions like Mean Absolute Error (MAE) or Generalized Cross Entropy that are less sensitive to noisy labels than standard Cross Entropy. | Can prevent the model from overfitting to incorrectly labeled data points, leading to better generalization. |
| mlxtend.evaluate.biasvariancedecomp [125] | A Python function to quantitatively decompose a model's error into its bias and variance components. | Essential for diagnosing the root cause of model underperformance. Helps guide the choice of mitigation strategy (e.g., reduce complexity vs. increase data). |
Performance Comparison of Online vs. Offline Reinforcement Learning in DBTL
Frequently Asked Questions
Q1: In a DBTL cycle, when should I prioritize online RL over offline RL? Prioritize online RL when you have the capacity for active, iterative data generation (the "Build" and "Test" phases) and are aiming for peak performance on a complex optimization task, such as designing a novel molecule with multiple desired properties. Online methods excel at refining policies through active interaction and exploration [134] [135]. Choose offline RL for initial prototyping or when you have a large, high-quality historical dataset from past cycles and computational budget is a primary constraint. It allows for quick policy derivation from static data [134].
Q2: Why does my offline RL agent perform poorly when deployed in a real-world test? This is a classic sign of extrapolation error. Your agent has learned a policy from a static dataset that does not perfectly represent the environment it now operates in. The state-action pairs it encounters during deployment differ from those in its training data, leading to inaccurate value estimates and poor decisions [136]. This is a fundamental challenge in offline RL.
Q3: How can I quickly tell if my RL agent is learning effectively? Do not rely solely on the reward from the training environment, as it includes exploration noise. Instead, periodically evaluate your agent in a separate, deterministic test environment. A good practice is to run several test episodes (e.g., 5-20) with a deterministic policy and track the average reward per episode. A consistently increasing test reward is a strong indicator of effective learning [137].
Q4: What is the most common cause of training instability in RL, and how can I fix it? Improperly scaled rewards are a frequent culprit. If the rewards (and thus the value targets for the neural network) are too large or too small, gradient updates can become unstable. A common fix is to manually rescale and clip the environmental rewards so that the targets passed to the network fall within a sensible range, roughly between -10 and +10 [138].
Q5: My agent seems stuck, always choosing the same action. What can I do? Your agent is failing to explore. You can address this by:
- Increasing the exploration rate (e.g., the
ϵin ϵ-greedy policies). - Using entropy regularization, which adds a bonus to the reward for taking unpredictable actions, discouraging premature convergence [136].
- Employing algorithms with explicit information bonuses (directed exploration), such as those that select actions with the highest uncertainty [12].
Troubleshooting Guides
Problem: Offline RL Agent Fails to Generalize
Description The agent performs well on the offline training dataset but shows significantly worse performance when deployed to interact with the real environment or a high-fidelity simulator. This often manifests as an inability to achieve high rewards or discover optimal policies outside the training data distribution [136].
Diagnosis Steps
- Check Dataset Coverage: Analyze your offline dataset. Does it contain a wide variety of states and high-quality action sequences? Performance will be limited if the data lacks diversity or consists mainly of sub-optimal trajectories [134].
- Validate on a Test Environment: Before deployment, create a test benchmark within your target environment to quantify the performance drop.
- Analyze Value Estimates: Monitor the Q-values (expected returns) for actions during deployment. Unrealistically high or volatile Q-values for states not well-covered by the data can indicate over-estimation and extrapolation error [136].
Solutions
- Hybrid Data Strategy: Start with offline pre-training on your historical data, then fine-tune the agent using a small number of online interactions. This leverages the cost-efficiency of offline learning while adapting the policy to the real environment [136].
- Improve Data Quality: Curate your offline dataset to be more "on-policy," meaning it should resemble data that the initial policy (e.g., the SFT policy) would generate. One working recipe is to generate data with distributional proximity to the starting policy [134].
- Algorithm Selection: Consider using offline RL algorithms specifically designed to mitigate extrapolation error, for example, by incorporating uncertainty estimates or conservative policy updates.
Problem: Online RL Training is Unstable or Sample Inefficient
Description During online training, the agent's performance (e.g., episode reward) fluctuates wildly, plateaus at a sub-optimal level, or improves very slowly, requiring an impractical number of environment interactions [137].
Diagnosis Steps
- Inspect Reward Scaling: Check the magnitude of the reward signals. If they are extremely large or small, the learning dynamics can become unstable [138].
- Monitor Policy Updates: Track the magnitude of policy or value network updates. Large, erratic changes can indicate instability. Algorithms like PPO and TRPO are designed to limit update sizes to avoid this [136] [137].
- Check for Proper Normalization: Ensure that the input observations (states) to the agent are normalized. Unnormalized inputs with varying scales can severely hamper learning [137].
Solutions
- Normalize Inputs and Rewards: Always normalize the observation space. Hand-scale and clip rewards to a reasonable range as a starting point [137] [138].
- Use a Modern Algorithm: Implement state-of-the-art algorithms like PPO (for discrete and continuous actions) or SAC/TD3 (for continuous actions), which include mechanisms to improve stability [137].
- Utilize a Replay Buffer: For off-policy online algorithms, use a replay buffer that stores and replays past experiences. This improves sample efficiency by breaking the correlation between consecutive samples. Regularly update the buffer with new experiences [136].
- Implement a Target Network: Use a target network, a periodically updated copy of the main network, to generate more stable learning targets. This is a key component of algorithms like DQN and DDPG and helps prevent the feedback loops that lead to overestimated values [136].
Quantitative Performance Data
The following table summarizes key performance differentiators between online and offline RL, as identified in controlled studies.
| Metric | Online RL | Offline RL | Experimental Context |
|---|---|---|---|
| Peak Performance | Higher ultimate performance [134] | Lower peak performance [134] | AI alignment on NLP tasks; measured by reward vs. KL divergence [134] |
| Sample Efficiency | Lower (requires active data generation) [137] | Higher (leverages existing data) [134] | General RL theory and practice [134] [137] |
| Optimality Gap | ~4-10% cost savings over baseline [135] | ~2% higher cost than online RL [135] | Thermal energy management in buildings [135] |
| Generalization | Learns from current environment dynamics [135] | Prone to extrapolation error on deployment [136] | Building control simulation & RL theory [135] [136] |
| Key Strength | Active exploration; policy improves with interaction [134] [12] | Cost-effective use of historical data [134] | Controlled RLHF (RL from Human Feedback) experiments [134] |
Experimental Protocols
Protocol 1: Controlled Comparison of Online vs. Offline RL for Over-Optimization
- Objective: To empirically compare the performance and over-optimization behavior of online and offline alignment algorithms under a fixed budget, measured by KL divergence from a reference policy [134].
- Methodology:
- Setup: Use a suite of open-source datasets. Define a reference policy (e.g., a Supervised Fine-Tuned model). Use a reward model trained on a static pairwise preference dataset [134].
- Online Algorithm: Employ an online algorithm (e.g., PPO) that actively samples from the current policy, queries the reward model, and updates the policy based on these on-policy samples [134].
- Offline Algorithm: Employ an offline algorithm (e.g., IPO or DPO) that learns a policy directly from the static preference dataset without further interaction [134].
- Calibration: For a fair comparison, calibrate the algorithms based on the KL divergence between the learned policy and the reference SFT policy. This serves as a unified measure of optimization budget [134].
- Evaluation: Plot the reward of the learned policy against the KL divergence. Observe the point where reward peaks and then drops (over-optimization) for both methods [134].
- Expected Outcome: Online algorithms are expected to achieve a higher peak reward at a higher KL divergence, forming a Pareto improvement over offline algorithms, which tend to peak earlier and at a lower performance level [134].
Protocol 2: Evaluating RL for Thermal Energy Management
- Objective: To benchmark Deep Reinforcement Learning (DRL) controllers against Model Predictive Control (MPC) and Rule-Based Control (RBC) for minimizing energy costs while maintaining comfort [135].
- Methodology:
- Simulation Environment: Use a dynamic simulation software (e.g., EnergyPlus) to model a building's HVAC system and a cold-water thermal storage tank [135].
- Controller Implementation:
- Online DRL: Train a DRL agent (e.g., using PPO or SAC) directly in the simulation, allowing it to interact and learn online [135].
- Offline DRL: Pre-train a DRL agent on a surrogate model or historical data, then deploy it without further learning [135].
- MPC: Implement a model-based controller that uses a physics-based model to optimize a cost function over a future horizon [135].
- RBC: Implement a standard, reactive rule-based controller as a baseline [135].
- Evaluation: Run a simulation over a representative period (e.g., one week). Compare controllers based on total operational cost, energy consumption, and maintenance of thermal comfort constraints [135].
- Expected Outcome: The online DRL and MPC controllers are expected to significantly outperform the RBC baseline. The online DRL controller should achieve performance competitive with or superior to the offline DRL agent, demonstrating the value of online adaptation [135].
RL System Workflows
The Scientist's Toolkit: Research Reagents & Solutions
This table lists key computational "reagents" and their functions for implementing RL in DBTL research.
| Item | Function / Explanation | Example Use Case |
|---|---|---|
| Static Historical Dataset | A fixed, pre-collected dataset of state-action-reward transitions used to train Offline RL agents without interaction [134]. | Training a policy on past high-throughput screening data. |
| Reward Model | A proxy model trained on human or experimental feedback (e.g., pairwise preferences) to score policy outputs in place of a real, expensive evaluation [134]. | Aligning molecule generators with multi-property objectives (e.g., potency, solubility). |
| Surrogate Model (Simulator) | A computationally efficient approximation of a complex system (e.g., a molecular dynamics simulator or building energy model) used for training agents, especially in online RL [135]. | Pre-training and debugging an RL agent before costly wet-lab experiments. |
| Replay Buffer | A memory that stores past experiences (state, action, reward, next state) for off-policy RL algorithms. It allows for sample reuse, breaking temporal correlations [136]. | Improving the sample efficiency of online RL algorithms like DQN and DDPG. |
| Target Network | A slowly updated copy of the main Q-network used to generate stable learning targets, preventing divergence and overestimation in value-based methods [136]. | A core component of DQN and its variants (e.g., Double DQN) to stabilize training. |
| KL Divergence Constraint | A mathematical constraint that prevents the RL-optimized policy from drifting too far from a reference policy, controlling the optimization budget and stabilizing training [134]. | The core mechanic in algorithms like PPO and TRPO, and a key metric for comparing alignment algorithms [134]. |
Scalability and Convergence Analysis Across Multiple DBTL Iterations
Frequently Asked Questions
This section addresses common technical challenges encountered when running machine learning experiments across multiple Design-Build-Test-Learn (DBTL) cycles, with a specific focus on managing the exploration-exploitation trade-off.
FAQ 1: My distributed model's performance is unstable, and the final model varies significantly between training sessions. How can I ensure more reliable convergence?
Answer: This is a classic sign of unstable last-iterate convergence, common in distributed non-convex optimization. To address this:
- Implement Momentum SGD: Use distributed momentum Stochastic Gradient Descent (mSGD) with a classical Robbins-Monro step-size schedule. This has been proven to enhance the last-iterate convergence behavior, leading to more stable final models [139].
- Analyze Convergence Metrics: Don't rely solely on the final performance metric. Monitor the $L_2$ convergence of the last iterate throughout training. Theoretical guarantees show that momentum can significantly accelerate early-stage convergence, which contributes to final model stability [139].
- Validate with Adaptive Methods: For non-convex objectives, you can use adaptive gradient-based methods like RMSprop or Adam. Research has provided almost sure convergence guarantees for these methods toward a critical point, which can lead to more reproducible results [140].
FAQ 2: As my DBTL iterations progress, the computational cost of exploring new chemical spaces becomes prohibitive. How can I scale exploration efficiently?
Answer: This directly relates to the exploration-exploitation trade-off. Instead of purely random exploration, use smarter, more scalable strategies.
- Adopt Inference-Time Scaling: For generative models (e.g., for molecular design), leverage methods like Sequential Monte Carlo (SMC). These methods globally fit a reward-tilted distribution, preserving diversity during multi-modal search without a linear increase in computational cost [141].
- Optimize the Trade-off with Adaptive Schedules: Implement strategies like the Funnel Schedule, which progressively reduces the number of maintained particles during a search, and Adaptive Temperature, which down-weights the influence of early-stage rewards. These methods are tailored to the phase-transition behavior of diffusion models and enhance sample quality without increasing the total number of noise function evaluations [141].
- Leverage Hybrid Quantum-Classical Approaches: For molecular simulation, use quantum-informed AI. Platforms like QUELO use quantum-enabled simulation to explore chemical space more efficiently, potentially reducing the number of physical experiments needed [142].
FAQ 3: My machine learning system's performance degrades as we scale the number of models and datasets. What are the key architectural pitfalls?
Answer: This indicates a collision of scalability and maintainability challenges.
- Avoid the "Changing Anything Changes Everything" (CACE) Principle: ML systems often have entangled signals. Improve system modularity to isolate components, preventing a scenario where improving one part inadvertently decreases the accuracy of another, leading to improvement deadlocks [143].
- Manage Artefacts Rigorously: As the number of models grows, manual monitoring and updates become impossible. Implement robust automation for tracking model versions, managing inferences, and ensuring reproducibility across hundreds or thousands of models [143].
- Address Data Dependency: Data dependency is often more costly than code dependency. Actively monitor for and manage "undeclared consumers" and data dependencies, as these complicate maintenance and increase the cost of changes as the system scales [143].
FAQ 4: How do I quantitatively balance the choice between exploring a new, uncertain drug target versus exploiting a known, promising one?
Answer: Frame this decision as a Multi-Armed Bandit (MAB) problem, a classic setting for the exploration-exploitation trade-off [1] [90].
- Define Metrics: Calculate the expected regret, which is the difference between the reward of the best possible action (the optimal drug target) and the reward of your chosen action. The goal of your strategy is to minimize the total expected regret over time [90].
- Implement a Strategic Policy: Instead of ad-hoc choices, use a formal strategy:
- ε-greedy: With probability ε, explore a random target; otherwise, exploit the best-known target. This is simple but can be inefficient [90].
- Upper Confidence Bound (UCB): Prefer actions with high uncertainty (high potential), formalized by choosing the action that maximizes the sum of the current estimated reward and a confidence-bound term [1] [90].
- Thompson Sampling: Choose an action based on its probability of being optimal, given the current state of knowledge. This is a powerful Bayesian approach [90].
Data Presentation: Convergence Rates & Scalability Strategies
The tables below summarize key quantitative findings and strategies from recent research to aid in experimental planning and comparison.
Table 1: Convergence Rates for Optimization Algorithms
This table consolidates proven convergence rates for various algorithms, which can serve as a benchmark for your own experiments.
| Algorithm | Problem Context | Convergence Rate | Key Assumptions |
|---|---|---|---|
| Distributed mSGD [139] | Non-convex, Last-Iterate | Almost sure & $L_2$ convergence | Robbins-Monro step-size |
| Adaptive Methods (RMSprop, Adam, etc.) [140] | Non-convex | $o(1/k^{1/2-\theta})$ for $\theta \in (0, 1/2)$ | Smooth objective functions |
| RMSprop & Adadelta [140] | Strongly Convex | $o(1/k^{1-\theta})$ for $\theta \in (0, 1/2)$ | Strong convexity |
| Hogwild! (Parallel SGD) [140] | Strongly Convex | Matches optimal SGD rate |
Table 2: Scalability Challenges & Mitigations in ML Systems
This table maps common scalability challenges to practical solutions, based on a systematic literature review [143].
| System Challenge | Impacted Workflow | Recommended Solution |
|---|---|---|
| Data Volume & Variety [144] | Data Engineering | Data parallelism, incremental learning, distributed file systems (HDFS) [144]. |
| Model Complexity [144] | Model Engineering | Model compression (pruning, quantization), hardware acceleration (GPUs/TPUs) [144]. |
| Proliferation of Models | System Deployment | Automated artifact management, versioning, and reproducibility pipelines [143]. |
| Training-Serving Skew | System Deployment | Robust data validation and monitoring to detect "model staleness" [143]. |
Experimental Protocols
Protocol 1: Analyzing Last-Iterate Convergence in Distributed mSGD
Objective: To empirically validate the almost sure and $L_2$ convergence of the last iterate in a distributed, non-convex setting (e.g., training a deep neural network for molecular property prediction).
Methodology:
- Setup: Configure a distributed computing cluster with multiple worker nodes. Initialize your model with the same weights on all nodes.
- Training with Momentum: Use a distributed mSGD optimizer. Adhere to a classical Robbins-Monro step-size schedule (e.g., $\etat = \eta0 / t^{\alpha}$ with $\alpha \in (0.5, 1]$) [139].
- Data Partitioning: Distribute the training data across worker nodes in a non-IID fashion to simulate real-world data distribution.
- Tracking: At the end of each training epoch, record the model's last iterate (the final weights after the update) and compute its $L_2$ norm. Simultaneously, track the training loss to monitor almost sure convergence.
- Analysis: Plot the $L2$ norm of the last iterate over time. The curve should decay and converge, providing evidence of $L2$ convergence. The training loss should converge almost surely to a critical point.
Protocol 2: Implementing Inference-Time Scaling for Exploration
Objective: To enhance the diversity and quality of generated molecules (exploration) in a diffusion model without increasing the computational budget.
Methodology:
- Baseline: Run your standard text-to-image or molecular graph diffusion model and record the quality/diversity metrics and number of Noise Function Evaluations (NFEs).
- Integrate Sequential Monte Carlo (SMC): Modify the inference process to use an SMC-based method, which maintains a population of particles (candidate samples) [141].
- Apply Funnel Schedule: Implement a schedule that progressively reduces the number of maintained particles as the diffusion generation process continues. This focuses computational resources on the most promising candidates [141].
- Apply Adaptive Temperature: Dynamically adjust the temperature parameter to down-weight the influence of rewards computed in the early, noisier stages of the diffusion process. This prevents the model from being misled by high-variance early signals [141].
- Validation: Compare the quality and diversity of the molecules generated by the enhanced method against the baseline, ensuring the total NFEs remain constant.
Mandatory Visualizations
Exploration-Exploitation in DBTL
Scalable ML System Architecture
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools for Scalable & Convergent ML in Drug Discovery
| Tool / Resource | Function | Application Context |
|---|---|---|
| Apache Spark MLlib [144] | A distributed computing framework for large-scale data processing and machine learning. | Enables data parallelism for training on massive chemical datasets. |
| Horovod [144] | A distributed deep learning framework for TensorFlow, PyTorch, and Apache MXNet. | Facilitates efficient distributed training of complex models using data parallelism. |
| SMMRNA Database [145] | A database of small molecule modulators of RNA, with binding data (Kd, Ki, IC50). | Provides critical ground-truth data for training and validating models that predict RNA-ligand interactions. |
| QUELO (QSimulate) [142] | A quantum-enabled molecular simulation platform. | Provides high-accuracy, quantum-informed data for training AI models or validating generated molecules, enhancing exploration fidelity. |
| TensorFlow/PyTorch (Distributed) [144] | Machine learning libraries with native support for distributed training and inference. | The foundation for implementing and scaling custom model architectures. |
Conclusion
The strategic integration of machine learning to balance exploration and exploitation presents a paradigm shift for accelerating DBTL cycles in biomedical research. By leveraging foundational principles, robust methodological implementations, proactive troubleshooting, and rigorous validation, researchers can dramatically reduce experimental costs and iteration times in areas like metabolic engineering and drug discovery. Future directions point toward more scalable self-improvement algorithms, the application of multi-agent systems for complex biological optimization, meta-learning for adaptive strategy selection, and a heightened focus on the ethical considerations of automated experimental design. These advances promise to unlock new frontiers in efficient bioprocess development and personalized therapeutic creation.
References
- 1. Exploration–exploitation dilemma [https://en.wikipedia.org/wiki/Exploration%E2%80%93exploitation_dilemma]
- 2. Reinforcement Learning – Exploration vs Exploitation ... [https://ai-ml-analytics.com/reinforcement-learning-exploration-vs-exploitation-tradeoff/]
- 3. Exploration versus exploitation in space, mind, and society [https://pmc.ncbi.nlm.nih.gov/articles/PMC4410143/]
- 4. Exploitation and Exploration in Machine Learning [https://www.geeksforgeeks.org/machine-learning/exploitation-and-exploration-in-machine-learning/]
- 5. What is the role of exploration and exploitation in AI agents? [https://milvus.io/ai-quick-reference/what-is-the-role-of-exploration-and-exploitation-in-ai-agents]
- 6. What is the exploration-exploitation tradeoff in ... [https://milvus.io/ai-quick-reference/what-is-the-explorationexploitation-tradeoff-in-reinforcement-learning]
- 7. [2509.23808] Beyond the Exploration-Exploitation Trade-off [https://arxiv.org/abs/2509.23808]
- 8. Rethinking exploration–exploitation trade-off in ... [https://www.sciencedirect.com/science/article/pii/S0893608025002217]
- 9. The knowledge driven DBTL cycle provides mechanistic ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12084978/]
- 10. Machine Learning Guided Batched Design of a Bacterial ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9295160/]
- 11. Energy deficiency promotes rhythmic foraging behavior by ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10600490/]
- 12. Balancing exploration and exploitation with information ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7654823/]
- 13. Humans use directed and random exploration to solve the ... [https://pubmed.ncbi.nlm.nih.gov/25347535/]
- 14. A causal role for right frontopolar cortex in directed, but not ... [https://elifesciences.org/articles/27430]
- 15. The effect of atomoxetine on random and directed exploration ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5405969/]
- 16. balancing exploration and exploitation in deep recurrent ... [https://arxiv.org/abs/2310.08331]
- 17. Activity-directed synthesis: a structure-blind, function-driven ... [https://www.drugtargetreview.com/article/107311/activity-directed-synthesis-a-structure-blind-function-driven-molecular-discovery-approach/]
- 18. Computational Intractability → Area [https://lifestyle.sustainability-directory.com/area/computational-intractability/]
- 19. Intractability [https://algs4.cs.princeton.edu/66intractability/]
- 20. Time-series machine-learning error models for ... [https://www.sciencedirect.com/science/article/pii/S0045782520301742]
- 21. Balancing exploration and exploitation in de novo drug ... [https://pubs.rsc.org/en/content/articlelanding/2024/dd/d4dd00105b]
- 22. Effects of exploration-exploitation strategies in dynamic ... [https://repository.tudelft.nl/record/uuid:cdbd7908-b970-4fc4-8159-03a541681ffe]
- 23. Exploration Strategies in Deep Reinforcement Learning | Lil'Log [https://lilianweng.github.io/posts/2020-06-07-exploration-drl/]
- 24. Machine-learning error models for approximate solutions to ... [https://arxiv.org/abs/1808.02097]
- 25. Strategic exploitation in Boltzmann Q-learning in the ... [https://www.sciencedirect.com/science/article/abs/pii/S0960077925012561]
- 26. DBTL Approach in Synthetic Biology [https://www.moleculardevices.com/applications/synthetic-biology/dbtl-approach]
- 27. Learning the way toward high-precision biological design [https://pmc.ncbi.nlm.nih.gov/articles/PMC10231942/]
- 28. DBTL Cycle Advancement: Software Elevates Biotech R&D [https://teselagen.com/blog/revolutionizing-rd-dbtl-cycle/]
- 29. Balancing exploration and exploitation with information ... [https://www.sciencedirect.com/science/article/abs/pii/S2352154620301467]
- 30. The knowledge driven DBTL cycle provides mechanistic ... [https://microbialcellfactories.biomedcentral.com/articles/10.1186/s12934-025-02729-6]
- 31. balancing exploration and exploitation in deep recurrent ... [https://arxiv.org/html/2310.08331v2]
- 32. Engineering Success | TJI-Seoul - iGEM 2025 [https://2025.igem.wiki/tji-seoul/engineering]
- 33. Balancing exploration and exploitation with information and randomization - PubMed [https://pubmed.ncbi.nlm.nih.gov/33184605/]
- 34. Learning the value of information and reward over time when solving exploration-exploitation problems | Scientific Reports [https://www.nature.com/articles/s41598-017-17237-w]
- 35. combining machine learning and rapid cell-free testing [https://www.nature.com/articles/s41467-025-65281-2]
- 36. A Guide to Effective Troubleshooting in Experimental Design ... [https://www.bioprecisioncrafted.ca/post/uncovering-the-root-causes-a-guide-to-effective-troubleshooting-in-experimental-design-failures]
- 37. How to be a Better Troubleshooter in Your Laboratory [https://www.goldbio.com/blogs/articles/how-to-be-a-better-troubleshooter?srsltid=AfmBOopUraKZ4utREAQCqF5c0PRu29PGq5DnEy9dpTpj5ncSG1ef25yY]
- 38. Experimental design: Learn how to solve problems like a ... [https://www.labster.com/blog/experimental-design-learn-how-to-solve-problems-like-a-real-scientist]
- 39. A Contextual-Bandit-Based Approach for Informed ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9410371/]
- 40. Reinforcement Machine Learning for Effective Clinical Trials [https://www.infoq.com/articles/multi-armed-bandits-reinforcement-learning/]
- 41. A Comparison of Bandit Algorithms [https://towardsdatascience.com/a-comparison-of-bandit-algorithms-24b4adfcabb/]
- 42. A Bio-Inspired Minimal Model for Non-Stationary K-Armed ... [https://arxiv.org/html/2509.22209v1]
- 43. Adaptive designs for best treatment identification with top ... [https://pubmed.ncbi.nlm.nih.gov/37571869/]
- 44. A handy guide to UCB algorithm in reinforcement learning. [https://www.turing.com/kb/guide-on-upper-confidence-bound-algorithm-in-reinforced-learning]
- 45. Machine learning-led semi-automated medium optimization ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12008372/]
- 46. Using Bayesian Optimization to reduce the time spent on ... [https://medium.com/vantageai/bringing-back-the-time-spent-on-hyperparameter-tuning-with-bayesian-optimisation-2e21a3198afb]
- 47. Bayesian Optimization for Beginners - Emma Benjaminson [https://sassafras13.github.io/BayesianOptimization/]
- 48. Exploring Bayesian Optimization [https://distill.pub/2020/bayesian-optimization]
- 49. Mastering the exploration-exploitation trade-off in Bayesian ... [https://arxiv.org/abs/2305.08624]
- 50. Simulated Design–Build–Test–Learn Cycles for Consistent ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10510747/]
- 51. Diagnosing and fixing common problems in Bayesian ... [https://arxiv.org/html/2406.07709v1]
- 52. Acquisition functions in Bayesian Optimization [https://ekamperi.github.io/machine%20learning/2021/06/11/acquisition-functions.html]
- 53. Task-Targeted Exploration for Scientific Decision-Making [https://mit.whoi.edu/academics/fields/aope/aope-recent-dissertations-and-theses/balancing-exploration-and-exploitation-task-targeted-exploration-for-scientific-decision-making/]
- 54. Troubleshooting and FAQ [https://www.elastic.co/docs/explore-analyze/machine-learning/anomaly-detection/ml-ad-troubleshooting]
- 55. The Lazy Data Scientist's Guide to AI/ML Troubleshooting [https://odsc.medium.com/the-lazy-data-scientists-guide-to-ai-ml-troubleshooting-abaf20479317?source=post_internal_links---------0----------------------------]
- 56. Center for Data-Driven Drug Development and Treatment ... [https://midas.umich.edu/collaboration/data/]
- 57. What is Multi-Armed Bandit(MAB) Testing? [https://vwo.com/blog/multi-armed-bandit-algorithm/]
- 58. The Complete Guide To Multi-Armed Bandit Testing [https://guessthetest.com/the-complete-guide-to-multi-armed-bandit-testing/]
- 59. High-throughput screening of catalytically active inclusion ... [https://microbialcellfactories.biomedcentral.com/articles/10.1186/s12934-024-02319-y]
- 60. Phenotypic Profiling of Selected Cellulolytic Strains to ... [https://www.mdpi.com/2076-2607/13/1/193]
- 61. High-Throughput Screening [https://hudsonlabautomation.com/applications/high-throughput-screening/]
- 62. Combinatorial vs Sequential Optimization for Metabolic ... [https://www.genscript.com/synthetic-biology-news/combinatorial-vs-sequential-optimization-for-metabolic-pathway-engineering.html]
- 63. Application of combinatorial optimization strategies in ... [https://www.nature.com/articles/s41467-020-16175-y]
- 64. Combinatorial pathway optimization for streamlined ... [https://pubmed.ncbi.nlm.nih.gov/28750202/]
- 65. Dynamic control in metabolic engineering: Theories, tools ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8015268/]
- 66. Customized optimization of metabolic pathways by ... [https://pubmed.ncbi.nlm.nih.gov/22718979/]
- 67. Direct Combinatorial Pathway Optimization [https://pubmed.ncbi.nlm.nih.gov/27672702/]
- 68. Towards a fully automated algorithm driven platform for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC6853954/]
- 69. Closing the loop: establishing an autonomous test-learn ... [https://www.frontiersin.org/journals/bioengineering-and-biotechnology/articles/10.3389/fbioe.2024.1528224/full]
- 70. Strain design optimization using reinforcement learning [https://journals.plos.org/ploscompbiol/article?id=10.1371/journal.pcbi.1010177]
- 71. STELLA provides a drug design framework enabling ... [https://www.nature.com/articles/s41598-025-12685-1]
- 72. Automating the design-build-test-learn cycle towards next- ... [https://www.sciencedirect.com/science/article/pii/S187167842300002X]
- 73. teemi: An open-source literate programming approach for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10954146/]
- 74. Min P Sampling: Balancing Creativity and Coherence at ... [https://arxiv.org/html/2407.01082v1]
- 75. Min-p sampling for LLMs - Thoughtworks - Medium [https://thoughtworks.medium.com/min-p-sampling-for-llms-cf1655928796]
- 76. Generation configurations: temperature, top-k, top-p, and ... [https://huyenchip.com/2024/01/16/sampling.html]
- 77. Widespread false negatives in DNA-encoded library data [https://pubs.rsc.org/en/content/articlehtml/2025/sc/d5sc00844a]
- 78. DAGIP: alleviating cell-free DNA sequencing biases with ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11887355/]
- 79. Systematic Review of Approaches to Preserve Machine ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8410238/]
- 80. B-STaR: Monitoring and Balancing Exploration ... [https://arxiv.org/html/2412.17256v2]
- 81. AI and machine learning: Revolutionising drug discovery ... [https://www.roche.com/stories/ai-revolutionising-drug-discovery-and-transforming-patient-care]
- 82. Balancing Exploration and Exploitation in Self-imitation ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7206262/]
- 83. In-depth Guide to ML Model Debugging and Tools You ... [https://neptune.ai/blog/ml-model-debugging-and-tools]
- 84. B-STaR: Monitoring and Balancing Exploration ... [https://arxiv.org/abs/2412.17256]
- 85. Heteroscedasticity Explained | Main Causes & Easy Fixes [https://www.displayr.com/what-is-heteroscedasticity/]
- 86. Model: Bayesian Optimisation for Biology | Imperial - iGEM 2025 [https://2025.igem.wiki/imperial/Model]
- 87. Characterization of heteroscedastic measurement noise in ... [https://www.sciencedirect.com/science/article/abs/pii/S0003267014009726]
- 88. Orbitrap noise structure and method for noise unbiased ... [https://www.nature.com/articles/s41467-025-61542-2]
- 89. Navigating Through the Noise: A Roadmap for Combining ... [https://link.springer.com/article/10.1007/s11692-025-09655-w]
- 90. The exploration-exploitation trade-off: intuitions and ... [https://medium.com/data-science/the-exploration-exploitation-dilemma-f5622fbe1e82]
- 91. Adaptive Optimization in ML [https://www.geeksforgeeks.org/machine-learning/adaptive-optimization-in-ml/]
- 92. Adaptive Parameters Methods for Machine Learning [https://medium.com/data-science/adaptive-parameters-methods-for-machine-learning-6f7101a9a71]
- 93. How do you balance exploration and exploitation in ... [https://milvus.io/ai-quick-reference/how-do-you-balance-exploration-and-exploitation-in-recommendations]
- 94. Exploitation and Exploration in Machine Learning [https://www.tutorialspoint.com/machine_learning/machine_learning_exploitation_and_exploration.htm]
- 95. Exploration and Exploitation: Optimize Your Machine Learning Strategy [https://www.linkedin.com/advice/1/how-do-you-optimize-your-strategy-exploration]
- 96. How can we balance exploration and exploitation? [https://milvus.io/ai-quick-reference/how-can-we-balance-exploration-and-exploitation]
- 97. Biology-aware machine learning for culture medium ... [https://www.sciencedirect.com/science/article/pii/S1871678425000731]
- 98. Balancing exploitation and exploration: A novel hybrid ... [https://www.sciencedirect.com/science/article/pii/S1364815222000470]
- 99. Machine learning-enabled globally guaranteed ... [https://www.nature.com/articles/s42256-023-00642-4]
- 100. Bio inspired optimization techniques for disease detection ... [https://www.nature.com/articles/s41598-025-02846-7]
- 101. A machine learning Automated Recommendation Tool for ... [https://www.nature.com/articles/s41467-020-18008-4]
- 102. Systems biology informed deep learning for inferring ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7710119/]
- 103. In silico biological discovery with large perturbation models [https://www.nature.com/articles/s43588-025-00870-1]
- 104. A large-scale optimization algorithm based on variable ... [https://www.sciencedirect.com/science/article/abs/pii/S2210650225000215]
- 105. Text has enhanced contrast | ACT Rule | WAI [https://www.w3.org/WAI/standards-guidelines/act/rules/09o5cg/]
- 106. Text color must provide high contrast with its background [https://docs.acquia.com/web-governance/text-color-must-provide-high-contrast-its-background]
- 107. Contrast requirements for WCAG 2.2 Level AA [https://www.makethingsaccessible.com/guides/contrast-requirements-for-wcag-2-2-level-aa/]
- 108. Benchmarking optimization methods for parameter estimation ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC6394396/]
- 109. Gradient Boosting vs. Random Forest: Which Ensemble ... [https://medium.com/@hassaanidrees7/gradient-boosting-vs-random-forest-which-ensemble-method-should-you-use-9f2ee294d9c6]
- 110. Gradient Boosting vs Random Forest [https://www.geeksforgeeks.org/machine-learning/gradient-boosting-vs-random-forest/]
- 111. Comparison of Random Forest and Gradient Boosting ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8392226/]
- 112. Improving random forest predictions in small datasets from two ... [https://bmcmedinformdecismak.biomedcentral.com/articles/10.1186/s12911-021-01688-3]
- 113. Practical guidelines for the use of gradient boosting for ... [https://jcheminf.biomedcentral.com/articles/10.1186/s13321-023-00743-7]
- 114. balancing the exploration-exploitation tradeoff via double ... [https://arxiv.org/abs/1709.03162]
- 115. Minimize your errors by learning Gradient Boosting ... [https://medium.com/analytics-vidhya/minimize-your-errors-by-learning-gradient-boosting-regression-2c002c65a064]
- 116. Computational models of exploration and exploitation ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC9286537/]
- 117. Drug discovery: are productivity metrics inhibiting ... [https://www.sciencedirect.com/science/article/abs/pii/S1359644608002419]
- 118. Balancing exploration and exploitation in deep recurrent ... [https://www.sciencedirect.com/science/article/pii/S0950705124002983]
- 119. Exploitation Is All You Need… for Exploration [https://arxiv.org/html/2508.01287v1]
- 120. Enhanced limonene by production the expression of... optimizing [https://bioresourcesbioprocessing.springeropen.com/articles/10.1186/s40643-014-0010-z]
- 121. Systematic Optimization of Limonene in Engineered... Production [https://pubmed.ncbi.nlm.nih.gov/31199132/]
- 122. Studies on optimization of nitrogen sources for astaxanthin ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC1859879/]
- 123. High-yield astaxanthin production process development ... [https://www.frontiersin.org/journals/microbiology/articles/10.3389/fmicb.2025.1667396/full]
- 124. Retrospective validation study of a machine learning-based ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11460031/]
- 125. Bias–Variance Tradeoff in Machine Learning: Concepts & ... [https://www.bmc.com/blogs/bias-variance-machine-learning/]
- 126. Bias in machine learning | How to identify and mitigate ... [https://lumenalta.com/insights/bias-in-machine-learning]
- 127. What is Noise in Machine Learning? Types & Strategies [https://dagshub.com/glossary/noise-in-machine-learning/]
- 128. Fairness: Identifying bias | Machine Learning [https://developers.google.com/machine-learning/crash-course/fairness/identifying-bias]
- 129. How To Mitigate Bias in Machine Learning Models [https://encord.com/blog/reducing-bias-machine-learning/]
- 130. Improving Noise Robustness through Abstractions and its ... [https://arxiv.org/abs/2406.08428]
- 131. Improving Noise Robustness through Abstractions and its ... [https://arxiv.org/html/2406.08428v1]
- 132. Who Is to Blame for Bias in Machine Learning? [https://labelyourdata.com/articles/bias-in-machine-learning]
- 133. Data Noise and Label Noise in Machine Learning [https://towardsdatascience.com/data-noise-and-label-noise-in-machine-learning-98c8a3c8322e/]
- 134. Understanding the performance gap between online and ... [https://arxiv.org/html/2405.08448v1]
- 135. Comparison of online and offline deep reinforcement ... [https://www.sciencedirect.com/science/article/abs/pii/S0926580522000012]
- 136. Three Fundamental Flaws In Common Reinforcement ... [https://towardsdatascience.com/three-fundamental-flaws-in-common-reinforcement-learning-algorithms-and-how-to-fix-them-951160b7a207/]
- 137. Reinforcement Learning Tips and Tricks - Stable Baselines [https://stable-baselines.readthedocs.io/en/master/guide/rl_tips.html]
- 138. Debugging Reinforcement Learning Systems [https://andyljones.com/posts/rl-debugging.html]
- 139. Convergence Analysis of the Last Iterate in Distributed ... [https://arxiv.org/abs/2505.10889]
- 140. On Convergence Analysis of Stochastic and Distributed ... [https://uwspace.uwaterloo.ca/items/ce6e3b35-50f8-40da-93ed-80d5403304b3]
- 141. Navigating the Exploration-Exploitation Tradeoff in ... [https://arxiv.org/abs/2508.12361]
- 142. Quantum techniques offer a glimpse of next-generation ... [https://www.drugdiscoverynews.com/quantum-techniques-offer-a-glimpse-of-next-generation-medicine-16815]
- 143. Scalability and Maintainability Challenges and Solutions in ... [https://arxiv.org/html/2504.11079v1]
- 144. Scalability in Machine Learning Systems: Challenges ... [https://medium.com/@amirsina.torfi/scalability-in-machine-learning-systems-challenges-strategies-and-best-practices-231cc2fb2889]
- 145. SMMRNA: a database of small molecule modulators of RNA [https://pmc.ncbi.nlm.nih.gov/articles/PMC3965028/]