Network Robustness to Perturbation: Evaluation Frameworks and Biomedical Applications for Resilient System Design
This article provides a comprehensive framework for evaluating the robustness of diverse network architectures against perturbations, tailored for researchers and drug development professionals.
Network Robustness to Perturbation: Evaluation Frameworks and Biomedical Applications for Resilient System Design
Abstract
This article provides a comprehensive framework for evaluating the robustness of diverse network architectures against perturbations, tailored for researchers and drug development professionals. It explores foundational concepts like effective graph resistance and attack tolerance, details cutting-edge methodological advances including genetic algorithms and convolutional neural networks for robustness optimization, and addresses critical troubleshooting aspects such as certifying Graph Convolutional Network (GCN) reliability and mitigating scalability limits. The content further synthesizes validation strategies and comparative analyses of real-world biomedical AI platforms, offering actionable insights for building more robust, reliable computational and biological networks in clinical research and development.
Foundations of Network Robustness: Core Concepts, Metrics, and Attack Tolerance
Network robustness is a pivotal property determining a system's ability to maintain core functions amidst perturbations, with evaluation approaches spanning from structural integrity to functional sustainability assessments. In biological and pharmaceutical contexts, precisely defining and measuring robustness enables researchers to predict cellular response to genetic perturbations, drug treatments, and disease states. Structural integrity focuses predominantly on topological metrics—how network connectivity persists as components fail. In contrast, functional sustainability emphasizes the maintenance of biological processes, signaling flows, and phenotypic outcomes despite perturbations [1] [2]. This distinction is particularly crucial in drug development, where a therapeutic agent might disrupt a protein-protein interaction network's structure without immediately compromising its essential biological functions, or vice versa. The integration of these perspectives provides a more comprehensive framework for evaluating how biological networks respond to genetic, environmental, and pharmacological perturbations, ultimately enabling more predictive models of drug efficacy and toxicity.
The evaluation landscape encompasses diverse methodologies, from percolation-theoretic approaches that model cascade failures in network connectivity to machine learning frameworks that predict functional degradation from topological features [1] [3]. For research scientists, selecting appropriate robustness metrics is foundational to experimental design, influencing whether studies capture mere structural vulnerability or genuine functional collapse in targets ranging from intracellular signaling networks to epidemiological models. This guide systematically compares these approaches, their experimental implementations, and their applications in pharmaceutical research.
Quantitative Comparison of Robustness Evaluation Frameworks
Table 1: Core Methodologies for Network Robustness Evaluation
| Evaluation Approach | Key Metrics | Applicable Network Types | Data Requirements | Strengths | Limitations |
|---|---|---|---|---|---|
| Topological Analysis [1] | Largest Connected Component (LCC) size, Average path length, Connectivity measures | Large-scale topological networks (protein-protein, genetic) | Network adjacency matrix | Computational efficiency, Clear structural interpretation | May not reflect functional outcomes, High computational cost for dynamic networks |
| Percolation Theory [3] | Critical node fraction, Phase transition point | Random graphs, Erdős-Rényi models | Network structure and edge probability | Theoretical foundation, Statistical properties | Primarily for large networks, Assumes network collapse state |
| Matrix Spectra Methods [1] | Spectral radius, Spectral gap, Natural connectivity | Connected networks with defined adjacency | Matrix representations | Straightforward computation | Relationship with robustness not well-established for all biological networks |
| Functional Resilience Assessment [2] | Ecosystem service maintenance, Functional connectivity | Ecological networks, Supply chain networks | Functional capacity data, Flow measurements | Captures system performance | Complex to quantify biological functions |
| Dynamic Least-Squares MRA (DL-MRA) [4] | Edge sign and directionality, Feedback loop integrity, Dynamic behavior | Small signaling networks (2-3 nodes), Gene regulatory networks | Perturbation time-course data | Captures dynamic, signed directed edges with cycles | Scales linearly but challenging for large networks |
| Convolutional Neural Networks [1] | Predicted LCC sequence (attack curves) | Various synthetic and empirical networks | Training datasets of network structures | Instantaneous evaluation after training, Generalization capability | Performance depends on training data and specific scenarios |
Table 2: Performance Comparison Across Network Types
| Network Architecture | Optimal Evaluation Method | Robustness to Random Failure | Robustness to Targeted Attack | Experimental Validation Status |
|---|---|---|---|---|
| Erdős-Rényi Random Graphs [3] | Finite-size percolation theory | High for dense graphs | Low (vulnerable to high-degree removal) | Theoretically and empirically validated |
| Scale-Free Networks [1] | Topological analysis with targeted attacks | High | Very low (vulnerable to hub targeting) | Empirical studies ongoing |
| Small Biological Networks [4] | DL-MRA | Varies with connectivity patterns | Varies with feedback loops | Validated with simulated data |
| Ecological Networks [2] | Functional-structural integration | Moderate | High for central corridor removal | Case study in Yangtze River Delta |
| Intracellular Signaling Networks [4] | DL-MRA with partial perturbations | High for redundant pathways | Moderate to low | Limited to specific pathways |
| Gene Regulatory Networks [4] [5] | DL-MRA with knockdown data | Low for minimal connectivity | High for master regulators | Validated in inference contexts |
Experimental Protocols for Robustness Assessment
Topological Robustness Evaluation via Largest Connected Component
Objective: Quantify structural robustness by measuring the largest connected component size during progressive node removal.
Methodology:
- Network Preparation: Represent the biological network as a graph G(N, E) with N nodes and E edges. For protein-protein interaction networks, nodes represent proteins and edges represent interactions.
- Removal Simulation: Implement two primary removal strategies:
- Random Failure: Remove nodes uniformly at random
- Targeted Attack: Remove nodes in descending order of degree (highest degree first)
- LCC Calculation: After each removal iteration (from p=0 to p=(T-1)/T, where T is total removal steps), compute the relative size of the LCC using:
( Gn(p) = np/N )
where ( n_p ) is the LCC size after removing proportion p of nodes [1].
- Robustness Quantification: Calculate the robustness value R as the area under the curve of LCC sizes across all removal steps:
( R = \frac{1}{T} \sum{p=0}^{(T-1)/T} Gn(p) ) [1].
Applications: This method is particularly valuable for assessing structural vulnerability in protein interaction networks and metabolic networks, identifying critical nodes whose removal fragments the network.
Dynamic Least-Squares Modular Response Analysis
Objective: Infer signed, directed network structures with cycles from perturbation time-course data.
Methodology:
- Experimental Design: For an n-node network, perform n perturbation time-course experiments, with one perturbation per node [4].
- Perturbation Implementation: Apply reasonably specific perturbations (e.g., siRNA knockdown, small molecule inhibition) that predominantly affect the targeted node.
- Time-Course Measurement: Measure node activities (e.g., phosphorylation states, transcription levels) at 7-11 evenly distributed time points [4].
- Jacobian Matrix Estimation: Formulate ordinary differential equations describing node dynamics:
( \frac{dxi}{dt} ≡ fi(x1(k),x2(k),...,xn(k),S{i,ex},S_{i,b}) )
where ( xi(k) ) is node i activity at time point ( tk ), and estimate the Jacobian matrix J containing the network edge weights [4]:
( J ≡ \begin{pmatrix} F{11} & F{12} \ F{21} & F{22} \end{pmatrix} ≡ \begin{pmatrix} \frac{\partial f1}{\partial x1} & \frac{\partial f1}{\partial x2} \ \frac{\partial f2}{\partial x1} & \frac{\partial f2}{\partial x2} \end{pmatrix} ).
- Network Inference: Use least-squares fitting to estimate Jacobian elements from perturbation responses, capturing edge directionality, sign, and strength.
Applications: DL-MRA is particularly effective for reconstructing small signaling networks and gene regulatory circuits from phosphoproteomic or transcriptional data, capturing feedback and feedforward loops critical to biological function.
CNN-Based Robustness Prediction
Objective: Leverage convolutional neural networks to predict network robustness from structural features.
Methodology:
- Training Data Generation: Create diverse network topologies and compute their attack curves (LCC sequences) through simulation.
- Network Representation: Convert each network's adjacency matrix into an image-like representation suitable for CNN processing [1].
- Model Architecture: Implement a CNN with Spatial Pyramid Pooling (SPP-net) to handle networks of different sizes, using the attack curves and robustness values as training targets [1].
- Model Training: Optimize CNN parameters to minimize the difference between predicted and simulated attack curves.
- Robustness Prediction: Apply the trained model to new network structures for instantaneous robustness evaluation.
Applications: This approach enables rapid screening of network robustness across large datasets, such as comparing vulnerability across multiple disease-associated networks or synthetic biological circuits.
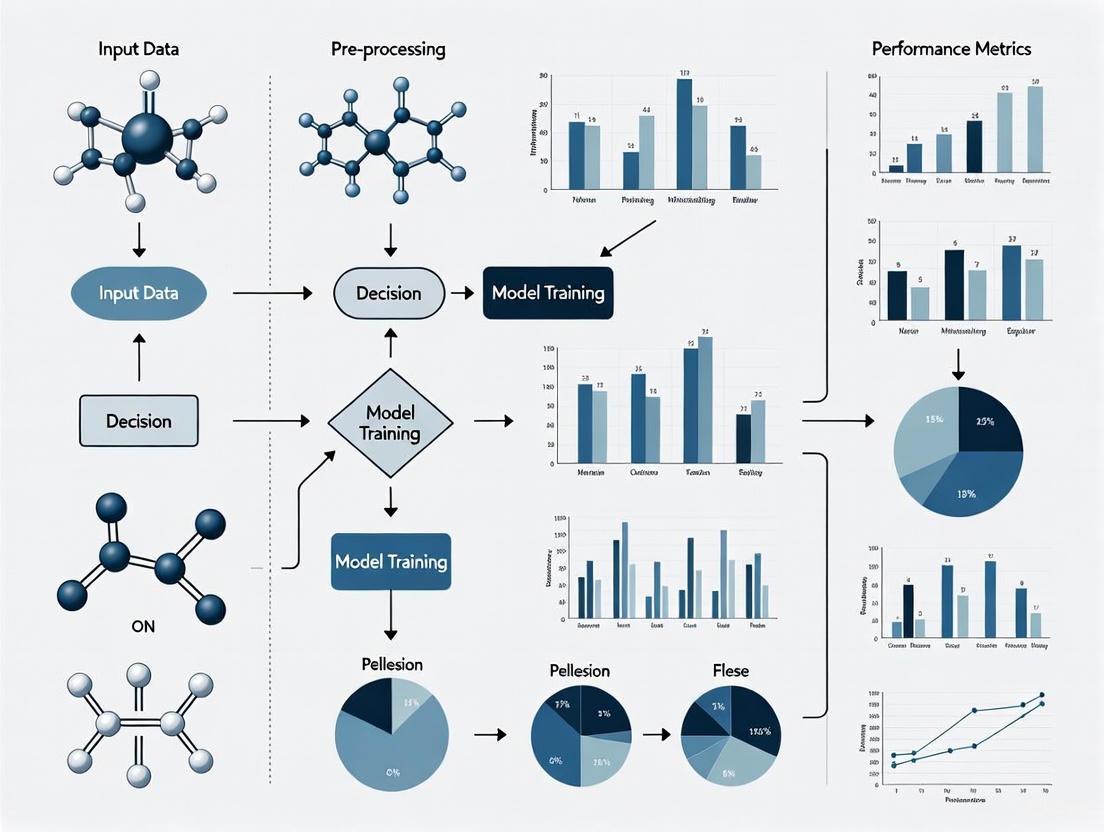
Visualization of Robustness Assessment Workflows
Diagram 1: Structural robustness assessment methodology for biological networks.
Diagram 2: Functional robustness evaluation using perturbation time-course data.
Table 3: Key Research Reagents and Computational Tools for Network Perturbation Studies
| Reagent/Tool | Function | Application Context | Considerations |
|---|---|---|---|
| siRNA/shRNA Libraries [5] | Gene-specific knockdown | Low and high-dimensional phenotyping screens | Specificity controls essential; multiple siRNAs per gene recommended |
| CRISPR-Cas9 Knockout Collections [5] | Complete gene knockout | Essentiality screens, synthetic lethality | Off-target effects monitoring required |
| Small Molecule Inhibitors [4] | Targeted protein inhibition | Signaling network perturbation | Dose optimization critical for specificity |
| Phospho-Specific Antibodies [4] | Monitoring signaling node activity | Dynamic network inference | Validation for specific modifications needed |
| Linkage Mapper Toolbox [2] | Ecological network construction | Structural connectivity analysis | Adapted for biological network mapping |
| NetworkX Python Library [2] | Network analysis and metrics | Structural stability calculation | Flexible for custom metric implementation |
| DL-MRA Computational Framework [4] | Network inference from perturbations | Signaling and regulatory network reconstruction | Handles small networks (2-3 nodes) effectively |
| CNN with SPP-net Architecture [1] | Robustness prediction from structure | Large network vulnerability screening | Requires training dataset generation |
The comprehensive evaluation of network robustness requires integration of both structural and functional approaches, as these complementary perspectives reveal different aspects of biological system vulnerability. Structural metrics efficiently identify topological fragility points, while functional assessments capture the dynamic, context-dependent nature of biological resilience. For drug development professionals, this integrated approach enables more predictive models of how therapeutic interventions might propagate through biological systems, potentially identifying both efficacious targets and vulnerable rescue pathways that could lead to resistance.
Future methodologies will likely combine high-dimensional phenotyping with advanced network inference to map the complex relationship between structural perturbation and functional collapse. As network biology continues to inform therapeutic discovery, robust evaluation frameworks will be essential for predicting intervention outcomes across diverse biological contexts, from cancer signaling networks to metabolic disease states. The experimental protocols and comparative analyses presented here provide a foundation for selecting appropriate robustness assessment strategies based on network type, available data, and research objectives.
The evaluation of network robustness is a critical task in network science, with direct applications in protecting infrastructures such as power grids, transportation systems, and communication networks from random failures and targeted attacks. Robustness fundamentally measures a network's ability to maintain structural integrity and functional performance when components fail or are deliberately compromised. While numerous metrics exist to quantify this property, three have emerged as particularly fundamental: Effective Graph Resistance, the Size of the Largest Connected Component (LCC), and Algebraic Connectivity. Each metric captures distinct yet complementary aspects of network robustness, from structural cohesion to spectral properties and electrical analogies.
Each metric operates on different theoretical foundations and captures unique aspects of network robustness. Effective Graph Resistance draws from electrical network theory, modeling the network as a system of resistors and quantifying overall connectivity. Algebraic Connectivity, derived from spectral graph theory, measures how difficult it is to disconnect a graph into components. The Largest Connected Component represents a more direct, empirical measure of functional network size after damage. Understanding the strengths, limitations, and appropriate application contexts for each metric is essential for researchers evaluating network architectures across scientific domains, from biological networks to critical infrastructures.
Metric Fundamentals and Theoretical Foundations
Effective Graph Resistance
Effective Graph Resistance, also known as total effective resistance or Kirchhoff index, originates from electrical circuit theory applied to graph structures. The metric imagines a graph as an electrical network where each edge represents a 1 Ohm resistor. The effective resistance between any two nodes is then computed as the potential difference needed to pass 1 Ampere of current between them. The total effective graph resistance is the sum of these pairwise resistances across all node pairs in the network [6] [7].
Mathematically, Effective Graph Resistance is computed using the pseudoinverse of the Laplacian matrix. For a graph (G) with Laplacian matrix (L), the resistance between nodes (a) and (b) is given by (R{ab} = (ea - eb)^T L^+ (ea - eb)), where (L^+) denotes the Moore-Penrose pseudoinverse of (L), and (ei) is the standard basis vector with 1 in the (i)-th position and 0 elsewhere [6]. The total effective resistance is then (R{total} = \sum{a
This metric exhibits several important properties: it decreases when edges are added (improving robustness), is monotonic with edge additions, and incorporates information about both the number of paths between nodes and their lengths. Intuitively, the effective resistance becomes small when there are many short paths between two vertices, meaning removing an edge hardly disrupts connectivity as alternative paths exist [7].
Algebraic Connectivity
Algebraic Connectivity, denoted as (a1(G)) or (\lambda2), is defined as the second-smallest eigenvalue of the Laplacian matrix of a graph. This metric was introduced by Fiedler and serves as a fundamental spectral measure of connectivity [8]. For a connected graph, the smallest eigenvalue is always zero, making the second-smallest eigenvalue crucially important as it quantifies how well-connected the graph is overall [9].
A key property of Algebraic Connectivity is that it is positive if and only if the graph is connected. Higher values indicate greater robustness, as they correspond to graphs that are more difficult to disconnect. The metric also relates directly to numerous graph properties; for instance, it provides bounds on the graph's diameter, vertex connectivity, and expansion properties [9] [8].
For d-dimensional generic frameworks, researchers have generalized the concept to generalized algebraic connectivity ((ad(G))), which extends the applicability to problems in structural rigidity, sensor network localization, and formation control in multi-robot systems [9]. In one dimension, (a1(G)) coincides with the standard algebraic connectivity, where generic rigidity and connectivity are equivalent [9].
Largest Connected Component (LCC)
The Largest Connected Component metric measures the relative size of the biggest connected subgraph remaining after node or edge removals. Unlike the previous spectral measures, LCC is a direct, intuitive structural measure that quantifies the proportion of nodes that remain mutually accessible after network damage [1] [10].
The LCC size, often denoted as (Gn(p)), where (p) is the proportion of removed nodes, forms the basis for the robustness index (Rn = \frac{1}{T} \sum{p=0}^{(T-1)/T} Gn(p)), which averages the LCC size across all failure stages [1]. This metric is particularly valuable because it directly reflects the functional scale of the network's main body that maintains normal functionality after failures [1].
The LCC is computationally intensive to compute for large networks undergoing sequential attack, but provides the most straightforward visualization of network disintegration. It serves as the reference benchmark for many other robustness metrics and has become the most widely employed metric in empirical robustness evaluation [1].
Table 1: Fundamental Properties of Network Robustness Metrics
| Property | Effective Graph Resistance | Algebraic Connectivity | Largest Connected Component |
|---|---|---|---|
| Theoretical Basis | Electrical circuit theory | Spectral graph theory | Graph connectivity |
| Mathematical Formulation | (R{total} = \sum{a |
Second smallest eigenvalue of Laplacian matrix | Relative size of largest connected subgraph |
| Computational Complexity | (O(n^3)) due to pseudoinversion | (O(n^3)) for full eigen-decomposition | (O(n+m)) per failure scenario |
| Range of Values | ((0, \infty)) - lower is better | ([0, \infty)) - higher is better | ([0, 1]) - higher is better |
| Handles Disconnected Graphs | Yes | No (zero for disconnected) | Yes |
Experimental Methodologies and Protocols
Standard Attack Scenarios and Evaluation Frameworks
Researchers typically evaluate network robustness metrics under standardized attack scenarios to enable meaningful comparisons. These scenarios systematically remove network components while tracking metric responses:
- Random Node Failure (RNF): Nodes are removed in uniformly random order, simulating random equipment failures or errors [1].
- Malicious Node Attack with Highest Degree Adaptive Attack (HDAA): Nodes are removed in descending order of degree, recalculating degrees after each removal to simulate intelligent attacks targeting critical nodes [1].
- Random Edge Failure (REF): Edges are removed randomly, simulating random connection failures [1].
- Malicious Edge Attack with Highest Edge Degree Adaptive Attack (HEDAA): Edges are removed targeting those with highest centrality or connectivity measures [1].
The robustness evaluation process typically involves incremental and irreversible attacks, where network components are removed sequentially while measuring the metrics at each step. For statistical reliability, multiple runs (typically 100-500) are performed for random failure scenarios to account for process variability [10].
Robustness Surface Framework
To address the challenge of combining multiple robustness metrics, researchers have developed the robustness surface framework, which employs Principal Component Analysis (PCA) to extract the most informative robustness metric for a given failure scenario [10]. The process involves:
- Defining a set of percentage failures (P = {1\%, 2\%, ..., |P|\%}) and failure configurations (m)
- Computing an (m \times n) matrix (A_p) for each percentage failure (p), where (n) is the number of robustness metrics
- Calculating the covariance matrix (Cp) for each (Ap) and averaging them to obtain a unified covariance matrix (\overline{C})
- Computing eigenvectors (V) and eigenvalues (D) of (\overline{C}) and selecting the most relevant principal component (v)
- Normalizing (v) to obtain (\overline{v} = \frac{v}{t0^T v}), where (t0) is the set of metrics with no failures
- Computing the R-value as (R^ = t_p^T \overline{v}) for each failure scenario [10]
This framework allows comparison of network robustness across different failure scenarios and addresses the challenges of metric dimensionality unification and weight assignment [10].
Diagram 1: Experimental workflow for network robustness evaluation showing the sequential process from network input through attack simulation to result analysis.
Comparative Performance Analysis
Metric Behavior Under Different Attack Scenarios
Extensive experimental studies have revealed distinctive behaviors for each robustness metric under various attack scenarios:
Effective Graph Resistance demonstrates superior sensitivity in early failure stages, making it particularly valuable for detecting initial network degradation. Studies show it correlates strongly with node and link connectivity, often converging to a distribution identical to the minimal nodal degree in random graphs [8] [7]. Its electrical analogy provides intuitive explanations for network robustness - networks with lower total effective resistance maintain connectivity through multiple alternative paths, making them more resilient to both random and targeted attacks [7].
Algebraic Connectivity exhibits a sharp phase transition behavior, suddenly dropping to zero when the network becomes disconnected. This binary characteristic makes it particularly useful for identifying the critical threshold of network disintegration [8]. However, its inability to distinguish between different disconnected states (all having zero algebraic connectivity) limits its utility in advanced failure stages. Research has shown that algebraic connectivity increases with improving node and link connectivity, justifying its role as a robustness measure [8].
Largest Connected Component provides the most intuitive visualization of network disintegration, typically following a characteristic S-curve with gradual decline under random attacks and abrupt collapse under targeted attacks [1]. The LCC-based robustness index (Rn = \frac{1}{T} \sum{p=0}^{(T-1)/T} G_n(p)) provides a single scalar value that effectively captures the average performance across all failure stages, making it highly practical for network comparisons [1].
Computational Considerations and Scalability
Computational requirements vary significantly across the three metrics, impacting their practical application to large-scale networks:
Effective Graph Resistance faces the most severe computational challenges, requiring (O(n^3)) time for the pseudoinversion of the Laplacian matrix [7]. This cubic complexity limits direct application to networks with more than a few thousand nodes. Researchers have developed approximation techniques including combinatorial and algebraic connections to speed up gain computations, randomized sampling methods, and greedy heuristics to make the metric applicable to larger networks [7].
Algebraic Connectivity also requires (O(n^3)) operations for full eigen-decomposition, though specialized algorithms can compute only the second smallest eigenvalue more efficiently. For very large networks, approximation methods become necessary [8].
Largest Connected Component computation is relatively efficient, requiring (O(n+m)) time per failure scenario using breadth-first or depth-first search. However, when simulating multiple attack sequences and configurations, the computational burden can still become significant [1]. Recent approaches using convolutional neural networks with spatial pyramid pooling (SPP-net) have demonstrated promising results in predicting LCC sizes, potentially bypassing the need for extensive simulations [1].
Table 2: Experimental Performance Comparison Across Network Types
| Network Type | Effective Graph Resistance | Algebraic Connectivity | Largest Connected Component |
|---|---|---|---|
| Erdős-Rényi Random Graphs | Closely tracks minimal nodal degree; predicts connectivity accurately | Mean and variance can be estimated via minimum nodal degree approximation | Shows smooth decay under random attacks; abrupt collapse under targeted attacks |
| Scale-Free Networks | Highly sensitive to targeted attacks on hubs; reveals vulnerability | Rapid decrease when high-degree nodes are targeted | Exhibits robustness to random attacks but fragility to targeted attacks |
| Multilayer Networks | Captures inter-layer dependency robustness | Generalizes to inter-layer spectral properties | Effectively tracks cascading failures across layers |
| Regular Lattices | High resistance values indicating lower robustness | Low values reflecting structural rigidity | Gradual, predictable reduction under attacks |
| Real-World Infrastructure Networks | Identifies critical bottlenecks effectively | Provides early warning of connectivity loss | Most interpretable for practical assessment |
Research Reagents and Computational Tools
Essential Research Components
Network robustness research requires both conceptual components and computational implementations:
Graph Laplacian Matrix: Fundamental mathematical construct defined as (L = D - A), where (D) is the degree diagonal matrix and (A) is the adjacency matrix [6]. Serves as the foundation for both effective resistance and algebraic connectivity.
Moore-Penrose Pseudoinverse ((L^+)): Critical for computing effective graph resistance when the Laplacian is non-invertible [6]. Implemented via singular value decomposition or specialized combinatorial methods.
Eigenvalue Solvers: Computational algorithms for extracting specific eigenvalues (particularly the second smallest) of large sparse matrices without full decomposition [8].
Connected Component Algorithms: Efficient graph traversal methods (BFS/DFS) for tracking LCC size during attack simulations [1].
Attack Simulation Frameworks: Software environments for implementing RNF, HDAA, REF, and HEDAA scenarios with statistical analysis of results [1] [10].
Emerging Methodologies
Recent advances have introduced several innovative approaches to robustness evaluation:
Convolutional Neural Networks with SPP-net: Machine learning approach that treats adjacency matrices as images to predict attack curves, offering significant speed advantages once trained [1].
Robustness Surface (Ω) Framework: PCA-based methodology that unifies multiple metrics addressing dimensionality and weighting challenges [10].
Greedy Optimization Algorithms: Heuristic approaches for robustness improvement through optimal edge addition, using stochastic techniques to reduce computational complexity [7].
Higher-Order Network Models: Extended network representations incorporating simplex structures beyond pairwise interactions, requiring specialized robustness assessment techniques [11].
Diagram 2: Research toolkit for network robustness evaluation showing the relationship between mathematical foundations, computational tools, and theoretical frameworks.
The three robustness metrics—Effective Graph Resistance, Algebraic Connectivity, and Largest Connected Component—each provide valuable but distinct perspectives on network robustness. Effective Graph Resistance offers the most comprehensive theoretical foundation through its electrical analogy, capturing both the number and quality of alternative paths. Algebraic Connectivity serves as an excellent early warning indicator with its sharp transition at the critical disconnection point. The Largest Connected Component provides the most intuitive and practically relevant measure of functional network scale after damage.
Selection of appropriate metrics depends on research goals, network characteristics, and computational resources. For theoretical analysis of small to medium networks, Effective Graph Resistance provides unparalleled insights. For identifying critical thresholds, Algebraic Connectivity is optimal. For practical assessment of large-scale networks, particularly when computational efficiency is crucial, LCC-based measures remain the most viable option.
Table 3: Metric Selection Guidelines for Different Research Scenarios
| Research Scenario | Recommended Primary Metric | Supplementary Metrics | Rationale |
|---|---|---|---|
| Theoretical Analysis of Network Structure | Effective Graph Resistance | Algebraic Connectivity | Captures most comprehensive connectivity information |
| Large-Scale Network Practical Assessment | Largest Connected Component | Robustness index (R_n) | Computational efficiency and interpretability |
| Critical Threshold Identification | Algebraic Connectivity | LCC size | Sharp phase transition clearly identifies disintegration point |
| Robustness Optimization Algorithms | Effective Graph Resistance | Node/edge connectivity | Differentiable nature supports optimization approaches |
| Multilayer Network Analysis | All three metrics with adaptations | Multilayer extensions | Each captures different aspects of cross-layer robustness |
Emerging approaches that combine these metrics through unified frameworks like the robustness surface, or that leverage machine learning to predict metric behavior, represent promising directions for future research. As network complexity grows with higher-order interactions and multilayer structures, the development of more sophisticated robustness metrics that can efficiently handle these complexities while providing actionable insights will remain an active and critical research area.
In the field of network science, evaluating the robustness of various network architectures to perturbations is a fundamental task, particularly in domains like computational biology and drug discovery where networks model complex cellular interactions. Perturbations—changes to a network's structure—can be broadly categorized as either random failures or targeted malicious attacks. Random failures involve the stochastic removal of nodes or edges, simulating natural breakdowns or unbiased experimental noise. In contrast, targeted attacks deliberately remove the most critical nodes or edges (e.g., those with highest connectivity), mimicking coordinated adversarial action or the specific knockout of a key biological entity. Understanding how different network inference and reconstruction methods respond to these two perturbation types is critical for developing reliable models in biological research. This guide provides a structured comparison of these perturbation models, detailing their impact on network robustness and offering protocols for their experimental simulation.
Theoretical Foundations of Network Perturbations
Network robustness analysis typically models a system as a graph ( G = (V, E) ), where ( V ) represents nodes (e.g., genes, proteins) and ( E ) represents edges (e.g., interactions, regulatory relationships). Perturbations alter this structure by removing nodes or edges.
- Random Failures: This model removes nodes or edges uniformly at random. It simulates natural noise, experimental error, or unpredictable hardware failures. In biological contexts, it can represent random gene knockouts or unsystematic measurement inaccuracies in high-throughput experiments.
- Targeted Malicious Attacks: This model removes nodes or edges based on a specific strategy designed to maximize network disruption. Common strategies include targeting nodes with the highest degree (number of connections) or betweenness centrality (frequency of lying on shortest paths). In adversarial machine learning, this correlates with data poisoning attacks where malicious samples are injected into training data to corrupt the learned model [12].
The core difference lies in intent and execution: random failures are stochastic and unbiased, while targeted attacks are strategic and exploit the network's topological vulnerabilities. The cascading failure model, often studied in physical networks like power grids or underwater unmanned swarms, demonstrates how the removal of a critical node can overload and subsequently fail neighboring nodes, leading to a catastrophic collapse of network connectivity [13].
Quantitative Comparison of Robustness Under Perturbation
The performance of network inference methods varies significantly under different perturbation types and datasets. The following tables summarize quantitative findings from large-scale benchmarking efforts, which evaluated methods on both statistical and biologically-motivated metrics.
Table 1: Performance of Network Inference Methods on the K562 Cell Line Dataset Under Perturbation
| Method Category | Method Name | Precision (Biological) | Recall (Biological) | F1 Score (Biological) | Mean Wasserstein Distance | False Omission Rate (FOR) |
|---|---|---|---|---|---|---|
| Challenge (Interventional) | Mean Difference (Top 1k) | 0.241 | 0.219 | 0.229 | 0.081 | 0.781 |
| Challenge (Interventional) | Guanlab (Top 1k) | 0.238 | 0.233 | 0.235 | 0.074 | 0.792 |
| Observational | GRNBoost | 0.094 | 0.451 | 0.155 | 0.062 | 0.549 |
| Observational | NOTEARS (MLP) | 0.184 | 0.142 | 0.160 | 0.073 | 0.827 |
| Interventional | GIES | 0.166 | 0.147 | 0.156 | 0.070 | 0.831 |
| Interventional | DCDI-G | 0.175 | 0.152 | 0.163 | 0.071 | 0.823 |
Table 2: Performance of Network Inference Methods on the RPE1 Cell Line Dataset Under Perturbation
| Method Category | Method Name | Precision (Biological) | Recall (Biological) | F1 Score (Biological) | Mean Wasserstein Distance | False Omission Rate (FOR) |
|---|---|---|---|---|---|---|
| Challenge (Interventional) | Mean Difference (Top 1k) | 0.237 | 0.221 | 0.229 | 0.082 | 0.779 |
| Challenge (Interventional) | Guanlab (Top 1k) | 0.235 | 0.230 | 0.232 | 0.075 | 0.785 |
| Observational | GRNBoost | 0.091 | 0.448 | 0.151 | 0.061 | 0.551 |
| Observational | NOTEARS (MLP) | 0.180 | 0.139 | 0.157 | 0.072 | 0.833 |
| Interventional | GIES | 0.162 | 0.144 | 0.152 | 0.069 | 0.836 |
| Interventional | DCDI-G | 0.172 | 0.149 | 0.159 | 0.070 | 0.829 |
Key for Metrics:
- Precision/Recall/F1: Biology-driven evaluation approximating ground truth.
- Mean Wasserstein Distance: A statistical metric; higher values indicate predicted interactions correspond to stronger causal effects.
- False Omission Rate (FOR): A statistical metric; lower values are better, indicating fewer real causal interactions are missed by the model.
The data reveals several critical insights. First, methods like GRNBoost achieve high recall but low precision, indicating they discover many true interactions but also include many false positives; this structure may be more resilient to random failures but vulnerable to targeted attacks on its numerous false edges. Second, the top-performing methods from the CausalBench challenge (e.g., Mean Difference, Guanlab) show a better balance, typically yielding higher F1 scores and Mean Wasserstein distances. This suggests that methods leveraging interventional data and designed for scalability are generally more robust to the inherent perturbations and noise in real-world biological data [14]. Finally, a key finding is that traditional interventional methods (e.g., GIES, DCDI-G) often fail to outperform their observational counterparts on real-world data, contrary to theoretical expectations, highlighting a significant performance gap under realistic perturbation scenarios [14].
Experimental Protocols for Perturbation Analysis
To systematically evaluate network robustness, researchers can employ the following detailed experimental protocols, drawing from established benchmarking suites and empirical studies.
Protocol 1: Benchmarking with Real-World Perturbation Data
This protocol leverages large-scale, real-world perturbation datasets to move beyond synthetic experiments, which often do not reflect real-world performance.
- Dataset Curation: Utilize openly available large-scale perturbation datasets. The CausalBench suite, for instance, uses single-cell RNA sequencing data from two cell lines (K562 and RPE1), comprising over 200,000 interventional data points from genetic perturbations (e.g., CRISPRi gene knockdowns) [14].
- Perturbation Integration: The dataset inherently contains both observational (control) and interventional (perturbed) data. The interventional data serves as a proxy for targeted perturbations on specific network nodes (genes).
- Method Evaluation:
- Input: Train network inference methods on a mix of observational and interventional data.
- Evaluation Metrics: Use a dual approach:
- Biology-Driven Metrics: Compare inferred networks to biologically approximated ground truth to calculate precision, recall, and F1 score.
- Statistical Causal Metrics: Compute the Mean Wasserstein Distance and False Omission Rate (FOR) to assess the strength and completeness of predicted causal interactions without relying on a fixed ground truth graph [14].
- Robustness Analysis: Compare the performance degradation of different methods (e.g., NOTEARS, GIES, GRNBoost, challenge methods) across these metrics. Methods that maintain higher performance are deemed more robust to the perturbations present in the real-world data.
Protocol 2: Simulating Random and Targeted Attacks
This protocol involves actively perturbing an inferred or known network structure to test its resilience.
- Network Inference: Begin by inferring a baseline network ( G_{\text{base}} ) from a dataset using a chosen method.
- Perturbation Simulation:
- Random Failure: For a chosen fraction ( p ) of nodes/edges, remove them uniformly at random from ( G{\text{base}} ) to create ( G{\text{random}} ).
- Targeted Attack: Calculate a node importance metric (e.g., degree centrality, betweenness centrality). Remove the top ( p ) fraction of nodes based on this metric from ( G{\text{base}} ) to create ( G{\text{targeted}} ) [13].
- Impact Assessment: Quantify the impact of perturbations using metrics like:
- Global Efficiency: Measures the efficiency of information exchange across the network.
- Largest Connected Component (LCC) Size: The proportion of nodes in the largest connected subgraph. A rapid shrink in LCC size indicates low robustness.
- Network Survivability: Under a multi-level connectivity scheme, analyze how dynamic topology, load, and recovery delays affect the network's ability to maintain core functions [13].
- Robustness Scoring: A method or architecture is considered robust if the performance drop (in terms of the chosen metrics) from ( G{\text{base}} ) to ( G{\text{random}} ) and ( G_{\text{targeted}} ) is minimal. Networks are typically much more resilient to random failures than to targeted attacks.
Protocol 3: Adversarial Training for Enhanced Robustness
This protocol focuses on improving model robustness by incorporating perturbations during the training phase, a technique proven effective in deep learning.
- Perturbation Generation: During model training, generate adversarial examples. In image classification, this can be done via algorithms like the Fast Gradient Sign Method (FGSM) or Projected Gradient Descent (PGD) [15]. For network inference, this could involve corrupting training data with noise or biased samples.
- Robust Training: Integrate these adversarial examples or noisy data into the training loop. This is the core of adversarial training, which minimizes the worst-case loss within a perturbation region, forcing the model to learn more robust features [12] [15].
- Validation: Evaluate the adversarially trained model on a held-out test set that contains both clean data and data subjected to various perturbation types (e.g., random noise, targeted adversarial attacks).
- Analysis: Empirical studies show that adversarial training generally improves robustness against the attacks it was trained on. However, it can lead to overfitting to a specific attack algorithm and may not generalize perfectly to novel attack strategies [15]. The trade-off between standard accuracy and adversarial robustness must be carefully managed.
Experimental Workflow for Network Robustness Evaluation
Building a robust network analysis pipeline requires a suite of computational tools and datasets. The following table details key resources for conducting perturbation research.
Table 3: Essential Research Reagents and Resources for Perturbation Analysis
| Resource Name | Type | Primary Function in Research | Relevance to Perturbation Models |
|---|---|---|---|
| CausalBench Suite | Software & Dataset | Provides a benchmark suite with real-world single-cell perturbation data and biologically-motivated metrics for evaluating network inference methods. | Serves as a standard testbed for assessing method robustness to real biological perturbations [14]. |
| PC Algorithm | Software Algorithm | A constraint-based causal discovery method used for inferring network structures from observational data. | A baseline observational method to compare against interventional methods under perturbation [14]. |
| GIES Algorithm | Software Algorithm | An extension of GES for causal discovery from a mix of observational and interventional data. | Tests the hypothesis that interventional data should improve robustness to targeted perturbations [14]. |
| NOTEARS | Software Algorithm | A continuous optimization-based method for learning the structure of directed acyclic graphs (DAGs) from data. | Represents a modern differentiable approach whose robustness can be benchmarked [14]. |
| Adversarial Training Library (e.g., ART, TorchAttacks) | Software Library | Provides implementations of common adversarial attack algorithms (FGSM, PGD) and adversarial training loops. | Used to enhance model robustness by training on perturbed data, defending against targeted attacks [12] [15]. |
| Single-Cell Perturbation Data (e.g., from CRISPRi screens) | Dataset | Large-scale datasets measuring gene expression under genetic perturbations, such as those from the CausalBench suite. | Provides the foundational "wet-lab" data containing real node (gene) perturbations for realistic benchmarking [14]. |
| Critical ε Value Analysis | Analysis Method | A technique from formal verification to find the maximum perturbation magnitude an input can withstand before misclassification. | Quantifies the intrinsic robustness of a network model to input perturbations [16]. |
Toolkit for Network Robustness Research
The comparative analysis between random failures and targeted malicious attacks reveals a fundamental truth: network architectures and inference methods are disproportionately vulnerable to strategic attacks on their critical components. The experimental data consistently shows that while methods like GRNBoost offer high recall, their low precision indicates a structure potentially riddled with false edges vulnerable to exploitation. In contrast, modern, scalable methods developed for interventional data, such as those emerging from the CausalBench challenge, demonstrate a more balanced and robust performance profile. For researchers in drug development, selecting a network inference method must involve a rigorous evaluation of its robustness to both random noise, which is inevitable in biological experiments, and targeted perturbations, which model the specific knockout of a disease-relevant gene or pathway. Incorporating adversarial training and robustness verification techniques from broader AI security research presents a promising path toward building more reliable and trustworthy biological network models, ultimately accelerating the hypothesis generation process in early-stage drug discovery.
The robustness of complex networks, defined as their ability to maintain connectivity and functionality when nodes or edges fail, represents a cornerstone of network science research. Within this field, scale-free networks have garnered significant attention due to their unique structural properties and implications for real-world systems. Characterized by power-law degree distributions where a few highly connected hubs coexist with many poorly connected nodes, scale-free architectures are frequently observed across biological, technological, and social domains [17] [18]. The foundational work by Albert, Jeong, and Barabási in 2000 first established the "robust yet fragile" nature of these networks: while remarkably resilient to random failures, they exhibit pronounced vulnerability to targeted attacks on hub nodes [17] [19]. This paradoxical behavior has profound implications for designing and protecting critical infrastructure, from biological networks in drug development to technological systems supporting pharmaceutical research. Understanding both the strengths and limitations of scale-free robustness provides essential insights for evaluating network architectures against perturbations, ultimately informing more resilient designs for complex systems in scientific and industrial applications.
Foundational Principles of Scale-Free Network Robustness
The degree distribution serves as the primary differentiator of scale-free networks from other architectural types. Unlike random or exponential networks where node degrees cluster around a characteristic value, scale-free networks follow a power-law distribution ( P(k) \sim k^{-\lambda} ), where the probability of a node having degree ( k ) decreases polynomially as ( k ) increases [17] [18]. This fundamental structural property gives rise to two complementary robustness phenomena that define scale-free network behavior.
The robustness to random failures emerges statistically from the predominance of low-degree nodes. Since the vast majority of nodes possess few connections, the random removal of nodes (or edges) most likely eliminates these structurally unimportant components, leaving the overall network connectivity largely unaffected [19]. The connected hubs continue to maintain the network's giant component, preserving global connectivity even under substantial random node removal. This property makes scale-free networks naturally resilient to undirected perturbations or random component failures.
Conversely, the fragility to targeted attacks stems directly from the disproportionate importance of highly connected hubs. These rare but critical nodes act as central connectors maintaining network integrity. When attackers possess perfect information about network topology and deliberately remove nodes in decreasing degree order, the elimination of just a small fraction of hubs can catastrophically fragment the network [19]. This "Achilles' heel" effect demonstrates how strategic attacks exploiting the very heterogeneity that provides random failure robustness can induce catastrophic failures, creating a fundamental trade-off in network security design.
Table 1: Key Properties of Scale-Free Networks and Their Impact on Robustness
| Network Property | Structural Manifestation | Impact on Random Failure Robustness | Impact on Targeted Attack Robustness |
|---|---|---|---|
| Power-law degree distribution | Few hubs, many low-degree nodes | High | Low |
| Degree heterogeneity | High variance in node connections | Preferential failure of unimportant nodes | Critical vulnerability of key hubs |
| Small-world structure | Short average path lengths | Maintained despite random removal | Rapid collapse when hubs are targeted |
| Hierarchical organization | Modular structure with connector hubs | Localized damage containment | Critical dependency on inter-module connectors |
Quantitative Framework: Measuring and Modeling Network Robustness
The mathematical foundation for analyzing network robustness relies heavily on generating functions and percolation theory. Generating functions provide a powerful mathematical framework for representing probability distributions of node degrees and analyzing their combinatorial properties. For a degree distribution ( pk ), the generating function is defined as ( G0(x) = \sum{k=0}^{\infty} pk x^k ), which enables the calculation of key network metrics through differentiation and functional composition [17]. This approach allows researchers to compute the mean component size, giant component existence, and other critical robustness indicators without exhaustive simulation.
The robustness metric ( R ) quantitatively captures a network's resilience to targeted attacks by measuring the preserved connectivity during sequential hub removal. Formally, ( R = \frac{1}{N} \sum_{q=1}^{N} s(q) ), where ( N ) is the total number of nodes and ( s(q) ) represents the fraction of nodes in the largest connected component after removing ( q ) nodes in decreasing degree order [20]. This metric ranges from ( 1/N ) (extremely fragile) to 0.5 (highly robust), with scale-free networks typically exhibiting significantly higher ( R ) values under random failure compared to targeted attacks.
Percolation theory provides the theoretical foundation for understanding network fragmentation thresholds. The critical removal fraction ( fc ) marks the phase transition point where the giant component disintegrates, with scale-free networks exhibiting notably different ( fc ) values for random versus targeted removal scenarios [19]. Analytical approaches building on the generating function formalism allow researchers to predict these critical thresholds for arbitrary degree distributions, creating a mathematical toolkit for robustness assessment without resource-intensive computational simulations.
Experimental Methodologies for Robustness Assessment
Standardized Attack Protocols
Researchers employ standardized experimental protocols to quantitatively evaluate network robustness, with distinct methodologies for different attack scenarios:
Targeted Node Attack Protocol:
- Calculate and rank all nodes by a centrality measure (typically degree or betweenness)
- Remove the highest-ranked node and all its incident edges
- Recalculate the size of the largest connected component (LCC)
- Recompute node centralities in the resulting network (for recalculated strategies)
- Repeat steps 2-4 until no nodes remain
- Record the LCC size after each removal to generate robustness curves [21] [20]
Random Failure Protocol:
- Randomly select a node with uniform probability
- Remove the selected node and all its incident edges
- Record the LCC size after removal
- Repeat until no nodes remain, averaging results over multiple trials to account for stochasticity
Information Disturbance Attack Model: This sophisticated approach introduces imperfect attack information by adding noise to node degree data. The displayed degree ( \tilde{di} ) follows a uniform distribution ( U(a, b) ) where ( a = di \alphai + m(1-\alphai) ) and ( b = di \alphai + M(1-\alphai) ), with ( \alphai \in [0,1] ) representing the attack information perfection parameter [19]. This model creates a continuum between perfect information (( \alpha = 1 ), pure targeted attack) and no information (( \alpha = 0 ), effectively random failure).
Experimental Workflow for Network Robustness Assessment
The following diagram illustrates the complete experimental workflow for assessing network robustness under different attack scenarios:
Comparative Experimental Data and Analysis
Robustness Under Different Attack Scenarios
Empirical studies consistently demonstrate the "robust yet fragile" dichotomy in scale-free networks. Under random failure conditions, scale-free networks maintain connectivity until exceptionally high node removal fractions, while targeted attacks trigger rapid disintegration with minimal hub removal.
Table 2: Comparative Robustness Metrics Across Network Topologies
| Network Type | Power-law Exponent (λ) | Critical Removal Fraction (f_c) Random | Critical Removal Fraction (f_c) Targeted | Robustness Metric (R) |
|---|---|---|---|---|
| Scale-free (biological) | 2.1 - 2.3 | 0.80 - 0.92 | 0.18 - 0.26 | 0.24 - 0.31 |
| Scale-free (technological) | 2.2 - 2.5 | 0.75 - 0.88 | 0.15 - 0.24 | 0.21 - 0.28 |
| Random network | Exponential | 0.65 - 0.75 | 0.60 - 0.72 | 0.28 - 0.35 |
| Small-world | Exponential | 0.70 - 0.82 | 0.55 - 0.68 | 0.30 - 0.38 |
The critical removal fraction (( fc )) represents the proportion of nodes that must be removed to dismantle the giant component [19]. The dramatic disparity between random and targeted ( fc ) values in scale-free networks highlights their unique vulnerability profile. For example, when the minimum degree ( m = 2 ), reducing the attack information perfection parameter from ( α = 1 ) (perfect information) to ( α = 0.8 ) (moderately disturbed information) increases ( f_c ) from 23% to 63%, demonstrating how information quality fundamentally alters robustness [19].
The Impact of Modularity on Robustness
Modular structure significantly influences scale-free network robustness, particularly under targeted attacks. Networks with high modularity (distinct community structure) exhibit different failure dynamics compared to non-modular scale-free networks:
Table 3: Modularity Effects on Scale-Free Network Robustness
| Modularity Level | Percolation Transition Type | Efficacy of Degree-Based Attack | Efficacy of Betweenness Attack | Critical Modules |
|---|---|---|---|---|
| Non-modular/Low | 2nd order (continuous) | High | Moderate | N/A |
| Medium Modularity | Mixed | High | High | Emerging |
| High Modularity | 1st order (abrupt) | Moderate | Very High | Critical |
Research indicates that in highly modular scale-free networks, betweenness-based attacks become more effective than degree-based attacks at fragmenting the network [21]. This occurs because betweenness centrality identifies connector nodes that link different modules, whose removal causes abrupt network fragmentation. Additionally, highly modular networks exhibit first-order percolation transitions with sudden collapse, unlike the continuous degradation observed in non-modular networks [21]. These findings demonstrate how organizational principles beyond degree distribution significantly impact robustness characteristics.
Enhancement Strategies for Scale-Free Robustness
Information Disturbance Approach
The information disturbance strategy enhances robustness by deliberately reducing the quality of topological information available to attackers. By introducing uncertainty in node degree information through the parameter ( α ), this approach effectively converts targeted attacks toward random failures, dramatically improving robustness [19]. Counterintuitively, optimal disturbance strategies preferentially target "poor nodes" (low-degree) rather than "rich nodes" (hubs), as disturbing the attack information for low-degree nodes provides greater overall protection [19]. This approach enhances robustness without altering the actual network topology, making it particularly valuable for protecting existing infrastructure.
Intelligent Rewiring Mechanisms
Intelligent rewiring algorithms proactively modify network topology to enhance robustness while preserving the scale-free degree distribution. The INTR (Intelligent Rewiring) mechanism specifically optimizes connections between high and low-degree nodes to reduce hub vulnerability [20]. This approach demonstrates performance superior to simulated annealing and ROSE algorithms, improving robustness metrics by 17.8% and 10.7% respectively while maintaining the original degree distribution [20]. The mechanism employs closeness centrality for efficient node importance identification, balancing optimization effectiveness with computational feasibility for large-scale networks.
Comparison of Enhancement Strategies
Table 4: Performance Comparison of Robustness Enhancement Strategies
| Enhancement Strategy | Robustness Improvement | Topology Preservation | Computational Complexity | Key Mechanism |
|---|---|---|---|---|
| Information Disturbance | High (fc: 23%→63%) | Complete | Low | Attack information degradation |
| Intelligent Rewiring (INTR) | High (R: +10.7-17.8%) | Degree distribution only | Medium | Strategic edge rewiring |
| Simulated Annealing | Moderate | Degree distribution only | High | Probabilistic optimization |
| Multiple Population GA | High | Degree distribution only | Very High | Evolutionary optimization |
Caveats and Limitations of Scale-Free Robustness
The Rarity of True Scale-Free Networks
Recent rigorous statistical analyses challenge the presumed ubiquity of scale-free networks across real-world systems. Comprehensive examination of nearly 1000 networks across social, biological, technological, transportation, and information domains revealed that strongly scale-free structure is empirically rare, with most networks better described by log-normal distributions [18]. Social networks appear at best weakly scale-free, while only a handful of technological and biological networks display strong scale-free properties [18]. This distributional diversity highlights limitations in generalizing the "robust-yet-fragile" principle across all complex networks without empirical verification.
Finite-Size Effects and Alternative Metrics
Finite-size effects may obscure underlying scale-free topology in empirical networks, as real systems necessarily contain limited nodes [22]. Finite-size scaling analysis suggests that many networks rejected as non-scale-free under strict statistical tests may actually exhibit underlying scale invariance clouded by sampling limitations [22]. Additionally, the degree-degree distance ( η ) has been proposed as an alternative scale-freeness indicator that may better capture underlying scale-free properties than traditional degree distributions [23]. These methodological considerations highlight ongoing refinements in how scale-free properties are identified and characterized.
Context-Dependent Robustness
Network robustness depends on structural features beyond degree distribution, including clustering coefficients, degree correlations, and spatial constraints. For spatial scale-free networks where connection probability decreases with distance according to a rate ( δd ), robustness requires ( τ < 2 + 1/δ ) for the power-law exponent ( τ ) [24]. This demonstrates how robustness criteria become more complex in spatially-embedded networks, with topological and geometric properties jointly determining resilience. Similarly, higher clustering coefficients generally reduce robustness to targeted attacks, suggesting structural trade-offs in network design [21].
The Scientist's Toolkit: Research Reagent Solutions
Table 5: Essential Methodological Tools for Network Robustness Research
| Research Tool | Function | Application Context | Key Considerations |
|---|---|---|---|
| Generating Functions | Mathematical representation of degree distributions | Analytical calculation of robustness metrics | Enables exact solutions for configuration model networks |
| Percolation Theory Framework | Models network fragmentation processes | Determining critical removal thresholds | Provides theoretical foundation for phase transitions |
| Finite-Size Scaling Analysis | Accounts for limited network size effects | Testing scale-free hypothesis in empirical data | Distinguishes true scaling from finite-sample artifacts |
| INTR Algorithm | Intelligent rewiring for robustness enhancement | Optimizing existing network topologies | Preserves degree distribution while enhancing robustness |
| Information Disturbance Model | Introduces attack information imperfection | Simulating realistic attack scenarios | Converts targeted attacks toward random failures |
| Modularity Detection Algorithms | Identify community structure | Analyzing robustness of modular networks | Reveals organizational principles beyond degree distribution |
The "robust-yet-fragile" paradigm of scale-free networks continues to provide fundamental insights into network resilience, though with important caveats and limitations. Foundational studies have established the mathematical principles underlying this paradoxical behavior, while contemporary research has refined our understanding of its boundary conditions and practical implications. For researchers and drug development professionals, these lessons highlight both the potential benefits and risks of scale-free architectures in biological and technological systems. The experimental methodologies and enhancement strategies reviewed here offer practical approaches for assessing and improving network robustness in real-world applications. As statistical analyses reveal the empirical rarity of strongly scale-free networks and methodological refinements address finite-size effects, the field continues to evolve toward more nuanced understanding of network robustness across diverse architectural types. This progression enables more informed design and protection of critical networks in pharmaceutical research, healthcare systems, and biological discovery pipelines.
In computational biology, the concept of robustness—a system's ability to maintain function despite perturbations—is a fundamental property of both biological and algorithmic systems. Protein-protein interaction (PPI) networks and drug-target interaction (DTI) graphs form the backbone of modern drug discovery, yet their predictive utility depends critically on their resilience to various forms of disturbance. Biological networks inherently exhibit distributed robustness, where functionality is preserved through alternative pathways when individual components fail [25]. Similarly, computational models must demonstrate stability against distribution shifts, including noisy data, adversarial attacks, and natural biological variation [26] [27]. This review systematically evaluates the robustness of different network architectures to perturbation, providing researchers with comparative performance data and methodological insights to guide tool selection for drug development pipelines.
The rise of biomedical foundation models creates new hurdles in testing and authorization, given their broad capabilities and susceptibility to complex distribution shifts [26]. Current evaluations reveal significant gaps in robustness assessment, with approximately 31.4% of biomedical foundation models containing no robustness evaluations at all [26] [27]. This underscores the critical need for standardized robustness testing frameworks tailored to biomedical applications where model failures can have serious consequences.
Comparative Analysis of Network Architectures and Their Robustness
Performance Metrics Across Network Types
Table 1: Quantitative performance comparison of network architectures under perturbation
| Network Architecture | Primary Application | Performance Metric | Performance (Unperturbed) | Performance (Perturbed) | Robustness Retention |
|---|---|---|---|---|---|
| GraphDTI [28] | Drug-target prediction | AUC | 0.996 (validation) | 0.939 (unseen data) | 94.3% |
| Multi-Objective EA with FS-PTO [29] | Protein complex detection | F1-Score | 0.82 (original PPI) | 0.76 (20% noise) | 92.7% |
| GO-Informed Mutation [29] | Protein complex detection | F1-Score | 0.85 (original PPI) | 0.81 (20% noise) | 95.3% |
| Retrieval-Augmented LLMs [30] | Biomedical NLP tasks | Accuracy | Varies by task | Significant degradation under counterfactuals | Limited |
| Standard LLMs [30] | Biomedical NLP tasks | Accuracy | Varies by task | Severe degradation | Poor |
Robustness Characteristics by Network Type
Table 2: Qualitative robustness characteristics across network architectures
| Network Type | Strengths | Vulnerabilities | Optimal Application Context |
|---|---|---|---|
| PPI Networks (Biological) [25] | Distributed robustness via redundant pathways; Hub-based architecture provides stability | Central-lethality: Hub deletion causes systemic failure; Missing/spurious interactions [29] | Cellular signaling analysis; Target identification |
| Graph Neural Networks (e.g., GraphDTI) [28] | Integrates heterogeneous data; Generalizes to unseen data with high AUC | Limited testing against adversarial attacks; Dependency on data quality | Drug-target interaction prediction; Polypharmacology studies |
| Evolutionary Algorithms (e.g., MOEA with FS-PTO) [29] | Resilient to noisy edges in PPI networks; Identifies sparse functional modules | Computational intensity; Limited scalability to very large networks | Protein complex detection; Functional module identification |
| Retrieval-Augmented LLMs [30] | Reduces hallucinations in biomedical NLP; Access to external knowledge | Struggles with counterfactual scenarios; Limited self-awareness | Biomedical literature analysis; Question-answering systems |
Experimental Protocols for Robustness Assessment
Robustness Testing Framework for Biomedical Foundation Models
Effective robustness evaluation requires a pragmatic framework addressing two central aspects: (1) the degradation mechanism behind a distribution shift, and (2) the task performance metric requiring protection against the shift [26] [27]. The specification should break down robustness evaluation into operationalizable units convertible into quantitative tests with guarantees. Below is the experimental workflow for implementing this framework:
Knowledge Integrity Testing
For knowledge-based models like biomedical LLMs, testing should focus on knowledge integrity checks using realistic transforms rather than random perturbations [26] [27]. For text inputs, prioritize typos and distracting domain-specific information involving biomedical entities. For image inputs, prioritize common imaging and scanner artifacts, and alterations in organ morphology and orientation [26]. Experimental protocols should include:
- Biomedical entity substitution: Replace specific drug, protein, or disease names with semantically similar alternatives to test contextual understanding [26] [27]
- Scientific finding negation: Modify factual statements in prompts to determine if models detect inconsistencies [26]
- Patient history manipulation: Deliberately misinform models about patient data to assess reasoning robustness [26] [27]
Population Structure Evaluation
Biomedical data often contain explicit or implicit group structures organized by age, ethnicity, socioeconomic strata, or medical study cohorts [26]. Evaluation protocols should include:
- Group robustness assessment: Measure performance gaps between best- and worst-performing subpopulations
- Instance robustness testing: Identify corner cases where models fail consistently
- Longitudinal robustness: Evaluate performance consistency across temporal distribution shifts
Noise Resilience Testing for PPI Network Analysis
The multi-objective evolutionary algorithm for protein complex detection employs a rigorous protocol for assessing robustness to network perturbations [29]:
Artificial Network Generation
To assess PPI network robustness, researchers create artificial networks by introducing different noise levels into original Saccharomyces cerevisiae (yeast) PPI networks [29]. This evaluates how perturbations in protein interactions affect algorithmic performance compared to other approaches. The protocol includes:
- Controlled edge manipulation: Remove existing interactions (10-30%) and introduce spurious connections at comparable rates
- Topological preservation: Maintain overall network properties while altering specific connections
- Functional similarity integration: Apply Gene Ontology-based metrics to guide mutation operators
FS-PTO Mutation Operator
The Functional Similarity-Based Protein Translocation Operator (FS-PTO) enhances collaboration between canonical models and Gene Ontology-informed mutation strategies [29]. This operator:
- Leverages GO semantic similarity metrics to guide protein translocation during mutation
- Improves detection of biologically meaningful complexes despite noisy data
- Increases quality of detected complexes over other evolutionary algorithm-based methods
The Scientist's Toolkit: Essential Research Reagents and Solutions
Table 3: Key research reagents and computational tools for robustness evaluation
| Tool/Resource | Type | Primary Function | Application in Robustness Research |
|---|---|---|---|
| Gene Ontology (GO) Annotations [29] | Biological Database | Standardized representation of gene functions | Provides biological constraints for mutation operators; enhances complex detection accuracy |
| FS-PTO Operator [29] | Algorithmic Component | Gene ontology-based mutation in evolutionary algorithms | Improves robustness to noisy PPI data; increases biological relevance of predictions |
| RoMA Framework [31] | Assessment Framework | Quantifies model robustness without parameter access | Measures LLM resilience to adversarial inputs; enables model comparison for specific applications |
| WCAG Contrast Guidelines [32] | Visualization Standard | Defines minimum contrast ratios for visual elements | Ensures accessibility and interpretability of network visualizations and tool interfaces |
| Biomedical RAG Benchmark [30] | Evaluation Framework | Comprehensive assessment of retrieval-augmented models | Tests robustness across biomedical NLP tasks; evaluates performance under counterfactual scenarios |
| PPI Network Databases (MIPS, etc.) [29] | Data Resource | Curated protein-protein interaction data | Provides ground truth for robustness testing; enables controlled noise introduction studies |
| Robustness Specification Template [26] [27] | Methodological Framework | Tailors robustness tests to task-dependent priorities | Connects abstract AI regulatory frameworks with concrete testing procedures |
The comparative analysis presented herein demonstrates significant variability in robustness characteristics across different network architectures for biomedical applications. Graph-based approaches like GraphDTI show impressive resilience to distribution shifts in drug-target prediction, while evolutionary algorithms with biological constraints excel in noisy PPI environments. The emerging generation of biomedical foundation models shows promise but requires more rigorous robustness testing, particularly for knowledge integrity and counterfactual scenarios [26] [30].
Future directions should prioritize the development of standardized robustness specifications that integrate both domain-specific and general robustness considerations [26] [27]. Additionally, methods that explicitly incorporate biological knowledge—such as Gene Ontology annotations in mutation operators or functional constraints in neural network training—consistently demonstrate enhanced robustness to perturbations [29]. As biomedical networks continue to grow in scale and complexity, ensuring their robustness will be paramount for translating computational predictions into clinically actionable insights.
Advanced Methods for Robustness Analysis and Optimization in Complex Networks
The evaluation of robustness across different network architectures—from biological and social systems to artificial intelligence models—is a cornerstone of reliable computational research. In the context of network science, robustness is defined as the ability of a system to maintain its structural integrity and core functionality when subjected to perturbations, whether random failures or targeted attacks [33] [34]. The development of strategies to enhance this robustness is critical, as cascading failures can lead to the severe impairment or complete collapse of entire networks [33]. This guide provides an objective comparison of three principal computational strategies for robustness enhancement: link addition, protection, and rewiring. By synthesizing current research and experimental data, we aim to offer researchers, scientists, and development professionals a clear framework for selecting and implementing these strategies based on specific network architectures and perturbation threats.
The table below synthesizes the core objectives, key mechanisms, and supported evidence for the three primary robustness enhancement strategies discussed in this guide.
Table 1: Comparative Overview of Robustness Enhancement Strategies
| Strategy | Core Principle | Key Mechanism | Reported Efficacy/Impact |
|---|---|---|---|
| Link Addition [33] | Augment network connectivity to provide alternative pathways and mitigate cascade effects. | Strategically adding higher-order structures (hyperedges) within or between communities. | Transforms collapse from first-order to second-order phase transitions; effectiveness depends on community structure clarity. |
| Protection [33] | Shield critical network components from failure to prevent initial disruption. | Employing cooperative protection models that safeguard a portion of edges within higher-order structures (e.g., 2-simplices). | Preserves functionality of key components, maintaining network connectivity and delaying the onset of cascading failures. |
| Rewiring [34] | Dynamically reconfigure connections post-disruption to restore or maintain connectivity. | "Bypass rewiring": Reconnecting neighbors of a removed node with a stochastic probability ( \alpha ). | Creates a trade-off between cost (number of new links) and robustness; preferentially reconnecting high-degree nodes is most effective. |
Detailed Analysis of Strategies and Experimental Protocols
Link Addition for Higher-Order Networks
Strategic edge addition focuses on enhancing robustness by proactively introducing new connections, particularly in networks with higher-order interactions (e.g., simplicial complexes) and community structures [33].
Experimental Protocol: The efficacy of link addition is typically evaluated using a load redistribution model that simulates cascading failures. This model differentiates between load redistribution within communities and among them. Researchers then test various edge addition strategies:
- Within-Community Addition: Adding higher-order structures inside existing communities.
- Among-Community Addition: Adding higher-order structures that connect different communities.
- Mixed Addition: A combination of the two. The network's robustness is measured by tracking the relative size of the largest connected component throughout the cascading failure process against the fraction of removed nodes [33].
Supporting Data: The strategy's success is highly contingent on the underlying network structure. For networks with prominent community structures, adding edges among communities is more effective, as it enhances inter-community connectivity and can change the nature of network collapse. Conversely, for networks with indistinct community structures, adding edges within communities yields superior robustness enhancement [33].
Component Protection Strategies
Protection strategies aim to harden the network by making key components less vulnerable to failure from the outset.
Experimental Protocol: A prominent method is the higher-order structure cooperative protection model. In this approach, a certain fraction of edges within protected higher-order structures (like 2-simplices) are reinforced and thus made immune to failure. The robustness is then tested under various attack scenarios (e.g., random node removal or targeted attacks on high-degree nodes) by measuring the percolation threshold or the robustness index ( R_{\text{TA}} ), which quantifies the retained network functionality as nodes are removed [33] [34].
Supporting Data: Studies show that selectively protecting critical nodes or higher-order structures significantly helps in maintaining the connectivity of the network. For instance, Zhang et al. demonstrated that designating and reinforcing key nodes can preserve global connectivity by ensuring these nodes remain functional during a cascade [33].
Link-Limited Bypass Rewiring
Bypass rewiring is a reactive strategy that dynamically reconfigures the network immediately after a node fails.
Experimental Protocol: The standard protocol involves simulating node removal (either random failures or targeted attacks) and then applying the rewiring logic. When a node is removed, each pair of its neighbors is connected with a probability ( \alpha ) (where ( 0 \leq \alpha \leq 1 )). This creates a "bypass link." Different methods for selecting which neighbor pairs to connect can be tested, such as random selection or preferential selection of high-degree nodes. The robustness is measured using the robustness index ( R_{\text{TA}} ), which averages the size of the giant component over the sequential removal of all nodes [34].
Supporting Data: Research reveals a clear trade-off between the number of bypass links (cost) and robustness improvement. Analytical and numerical results for scale-free networks show that robustness increases with the number of added bypass links. A key finding is that preferentially reconnecting high-degree nodes is significantly more effective than random rewiring in enhancing robustness, as it better preserves the connectivity of the network's backbone [34].
Table 2: Quantitative Comparison of Robustness Strategy Performance
| Strategy | Network Type | Perturbation Model | Key Metric | Performance Findings |
|---|---|---|---|---|
| Link Addition [33] | Higher-order networks with community structure | Cascading failure via load redistribution | Relative size of largest connected component | For clear community structures, among-community addition is most effective. For weak structures, within-community addition is better. |
| Protection [33] | Higher-order networks | Targeted attack & random failure | Percolation Threshold | Cooperative protection of higher-order structures (e.g., 20% of edges in 2-simplices) raises the failure threshold. |
| Rewiring [34] | Scale-free networks | Targeted attack (degree-based) | Robustness Index (( R_{\text{TA}} )) | Preferential rewiring of high-degree nodes with ( \alpha = 0.5 ) can improve ( R_{\text{TA}} ) by over 50% compared to no rewiring. |
The Critical Role of Evaluation Benchmarks
A trustworthy comparison of robustness strategies depends on reliable evaluation methods. Inconsistent testing protocols can lead to biased results and a false sense of security [35]. The AttackBench framework addresses this by providing a standardized benchmark to rank the effectiveness of adversarial attacks used in robustness evaluations. It introduces an optimality metric to measure how closely an attack approximates the best empirical solution, ensuring that the subsequent assessment of a model's or network's robustness is built on a solid foundation [35]. Furthermore, for structural networks, the Normlap score offers a normalized measure of network overlap that accounts for degree inconsistencies, providing a more accurate positive benchmark than raw overlap comparison [36].
The Scientist's Toolkit: Research Reagent Solutions
The table below lists essential conceptual "reagents" and tools for conducting research in network robustness.
Table 3: Essential Research Tools for Network Robustness Evaluation
| Tool / Solution | Function / Definition | Application in Research |
|---|---|---|
| AttackBench [35] | A standardized benchmark framework for evaluating gradient-based adversarial attacks. | Used to identify the most reliable and effective attack algorithm for robustness verification of machine learning models, ensuring evaluations are consistent and reproducible. |
| Load Redistribution Model [33] | A dynamical model that simulates how the load from a failed node is redistributed to its neighbors, potentially causing them to fail. | The core model for simulating cascading failures in complex networks, enabling the test of robustness enhancement strategies like link addition and protection. |
| Percolation Theory [33] [34] | A theoretical framework from statistical physics that studies the formation of connected clusters in a system as its components are randomly removed. | Used to analytically derive critical thresholds (e.g., percolation threshold ( \theta_c )) for network collapse under random failure or targeted attack. |
| Normlap Score [36] | A normalized network overlap score that measures agreement between two networks against a positive statistical benchmark. | Provides a computationally robust alternative for validating experimental network maps (e.g., protein interactions) by accounting for degree distribution inconsistencies. |
| Robustness Index (( R_{\text{TA}} )) [34] | A numerical measure of robustness against targeted attacks, calculated as the average size of the giant component during sequential node removal. | A standard metric in numerical simulations to quantify and compare the robustness of different network configurations or under various enhancement strategies. |
Visualizing Strategy Workflows
The following diagrams illustrate the core logical workflows for the primary robustness strategies discussed.
Workflow for Evaluating Robustness Strategies
Diagram 1: A generalized workflow for evaluating network robustness strategies, showing the common pathway from strategy implementation to final assessment.
Bypass Rewiring Mechanism
Diagram 2: The mechanism of bypass rewiring. After the failure of node C (red), its neighboring nodes are stochastically reconnected via new bypass links (green), maintaining network connectivity.
Evolutionary and Genetic Algorithms for Optimizing Effective Graph Resistance
The robustness of complex networks, defined as their ability to maintain functionality amidst random failures or targeted attacks, is a critical property across numerous domains, including biological systems, transportation networks, and pharmaceutical interaction maps. Effective graph resistance, also known as the Kirchhoff index, has emerged as a key robustness measure due to its foundation in spectral graph theory and electrical network analogies. This metric sums the effective resistance between all pairs of nodes in the graph, with lower values indicating a more robust network topology. Optimizing this measure presents a computationally challenging combinatorial problem, making evolutionary and genetic algorithms particularly well-suited for identifying near-optimal solutions.
This guide provides a comparative analysis of evolutionary and genetic algorithms designed to enhance network robustness by minimizing effective graph resistance through topological modifications. We examine their performance, experimental protocols, and implementation considerations within the broader context of evaluating network architecture robustness to perturbation—a crucial concern in biological network analysis and drug development research where system resilience directly impacts function and therapeutic efficacy.
Algorithmic Approaches and Comparative Performance
Taxonomy of Optimization Algorithms
Table 1: Classification of Evolutionary Algorithms for Robustness Optimization
| Algorithm Class | Key Characteristics | Representative Methods | Typical Applications |
|---|---|---|---|
| Genetic Algorithms (GAs) | Operate on population of candidate solutions using selection, crossover, and mutation operators | RobGA, RobGA{L⁺}, RobLPGA{L⁺} [37] | Link addition/protection in complex networks |
| Evolution Strategies | Typically deal with real-valued representations, often include self-adaptation mechanisms | Evolution strategies from EvoTorch [38] | Continuous parameter optimization |
| Hybrid Approaches | Combine evolutionary principles with other optimization techniques | Paddy Field Algorithm (PFA) [38] | Chemical system optimization, experimental planning |
| Greedy Heuristics | Make locally optimal choices at each step, often accelerated with evolutionary concepts | Stochastic greedy with sampling [7] | Large-scale network optimization |
Performance Comparison on Benchmark Problems
Table 2: Quantitative Performance Comparison of Optimization Algorithms
| Algorithm | Theoretical Basis | Solution Quality vs. Optimal | Computational Speed vs. Exhaustive Search | Key Advantage |
|---|---|---|---|---|
| RobGA{L⁺} [37] | Genetic algorithm with incremental matrix computation | ~95-98% of optimal solution | 3.3-68× faster than state-of-the-art | Balances accuracy with computational efficiency |
| Stochastic Greedy [7] | Greedy heuristic with candidate sampling | ~85-90% of optimal solution | 2-7× faster than standard greedy | Suitable for very large networks |
| Paddy Algorithm [38] | Density-based evolutionary optimization | Comparable to Bayesian methods | Lower runtime than Bayesian optimization | Resists premature convergence |
| Standard Greedy [7] | Sequential selection of best marginal gain | ~90-95% of optimal solution | O(kn³) time complexity | Provable performance guarantees |
Experimental evaluations on real-world and synthetic networks demonstrate that evolutionary approaches typically outperform simple greedy heuristics in solution quality, while incorporating efficient computation techniques like incremental matrix updates narrows the performance gap in computational efficiency [7] [37]. The RobGA{L⁺} algorithm exemplifies this balance, leveraging genetic algorithms' exploration capabilities while mitigating computational costs through efficient effective graph resistance recalculation [37].
Experimental Protocols and Methodologies
Standard Experimental Framework
Researchers evaluating evolutionary algorithms for effective graph resistance optimization typically follow a standardized experimental protocol:
Network Preparation and Characterization: Select benchmark networks representing relevant domains (biological, social, technological). Calculate key network properties including number of nodes (n), edges (m), degree distribution, clustering coefficient, and assortativity. The initial effective graph resistance (R_G) serves as the baseline measurement [7] [37].
Algorithm Implementation and Parameterization: Implement genetic algorithms with standard operators: tournament selection, uniform or single-point crossover, and Gaussian mutation. Population sizes typically range from 50 to 200 individuals, with crossover rates between 0.7-0.9 and mutation rates of 0.01-0.1 per gene. The fitness function directly minimizes R_G [37].
Solution Evaluation and Validation: Execute multiple independent runs with different random seeds to account for stochastic variation. Compare solutions against exhaustive search where computationally feasible (small networks) or against proven bounds and alternative heuristics for larger networks. Statistical significance testing validates performance differences [38] [37].
Specialized Methodological Variations
Incremental Computation for Efficiency: RobGA{L⁺} employs incremental computation of the Moore-Penrose pseudoinverse of the graph Laplacian when evaluating candidate solutions, dramatically reducing computational complexity from O(n³) to O(n²) per evaluation [37].
Density-Based Reproductive Strategies: The Paddy algorithm introduces a unique propagation mechanism where the number of offspring generated by a solution depends on both its fitness and the local density of similar solutions, promoting exploration while maintaining selection pressure [38].
Constraint Handling Techniques: For scenarios with budgetary constraints (e.g., limited edges for addition), algorithms employ constraint-preserving operators including repair mechanisms, penalty functions, and restricted search operators [37].
Figure 1: Standard workflow for evolutionary optimization of graph robustness. The process iteratively applies genetic operators to evolve network modifications that minimize effective graph resistance.
Table 3: Essential Computational Tools for Robustness Optimization Research
| Tool/Category | Specific Examples | Primary Function | Implementation Considerations |
|---|---|---|---|
| Graph Analysis Libraries | NetworkX, igraph, GraphTool | Network representation, basic metrics | Choose based on graph size and language preference |
| Linear Algebra Backends | NumPy, SciPy, Eigen | Matrix operations, pseudoinversion | Critical for efficient R_G computation |
| Evolutionary Algorithm Frameworks | DEAP, EvoTorch, Paddy | Algorithm implementation | DEAP offers flexibility, EvoTorch provides PyTorch integration |
| Robustness Metrics | Effective resistance, algebraic connectivity | Solution quality assessment | Effective resistance captures global robustness properties |
| Optimization Targets | Edge addition, edge protection, rewiring | Problem definition | Edge addition most common for R_G optimization |
Figure 2: Computational toolkit relationships for robustness optimization. Researchers combine algorithm classes with supporting libraries to address specific optimization targets.
Evolutionary and genetic algorithms provide powerful, flexible approaches for optimizing effective graph resistance and enhancing network robustness. Through comparative analysis, we observe that while pure greedy algorithms offer computational efficiency for massive networks, evolutionary approaches consistently deliver superior solution quality, particularly when enhanced with problem-specific innovations like incremental matrix computations and density-based reproductive strategies.
The emerging research trend favors hybridization—combining the systematic exploration of evolutionary algorithms with efficient local search and computational shortcuts specific to network robustness metrics. This approach balances the exploration-exploitation tradeoff fundamental to combinatorial optimization, making these methods particularly valuable for optimizing robustness in biological and pharmaceutical networks where both accuracy and computational feasibility are essential for practical application.
Researchers should select algorithms based on their specific network characteristics, computational constraints, and robustness requirements, with genetic algorithms like RobGA{L⁺} representing strong general-purpose choices for moderate-sized networks, while stochastic greedy variants offer practical solutions for massive-scale network analysis.
The deployment of Deep Neural Networks (DNNs) in safety-critical domains such as medical diagnosis and autonomous vehicles has made evaluating their robustness an essential research area [39] [40]. These models, while demonstrating high performance, have been shown to be vulnerable to various perturbations, including adversarial attacks and environmental noise, which can lead to erroneous and potentially dangerous decisions [41] [40]. The concept of an "attack curve" is central to this evaluation, representing the trajectory of a model's performance degradation under increasingly potent perturbations or attacks. This guide provides a comparative analysis of how Convolutional Neural Networks (CNNs) and other network architectures perform in predicting and withstanding these attack curves, framing the discussion within the broader thesis of evaluating architectural robustness to perturbations.
Experimental Protocols for Robustness Evaluation
To ensure consistent and comparable results across studies, researchers employ standardized experimental protocols for assessing model robustness. The following methodologies are foundational to the field.
Adversarial Attack Generation
A common approach involves generating adversarial examples to stress-test models. The Fast Gradient Sign Method (FGSM) is a fundamental white-box attack that perturbs an input image in the direction of the loss gradient: x' = x + ε * sign(∇ₓJ(θ, x, y)), where ε controls the perturbation strength [41] [40]. More potent iterative attacks, such as the Projected Gradient Descent (PGD) attack, apply FGSM multiple times with a small step size, projecting the perturbed input back onto an L∞-norm ball around the original input at each step [41]. This method is considered a standard for evaluating adversarial robustness.
Robustness Training and Defense
To enhance model resilience, Adversarial Training is a widely-used defense. It involves minimizing the worst-case loss within a perturbation region by training the model on adversarial examples generated on-the-fly [39] [40]. The training objective is often formulated as: min θ E_(x,y)∼D [ max_(δ∈Δ) L(θ, x+δ, y) ], where δ is the adversarial perturbation bounded by Δ [40]. Variants like Multi-Perturbations Adversarial Training (MPAdvT), which exposes the model to diverse perturbation types during training, have been shown to significantly improve robustness [39].
Robustness Metrics
Key metrics for quantifying robustness include:
- Fooling Ratio (FR): The percentage of test samples that are misclassified after an adversarial attack [39].
- Clean Accuracy Drop: The decrease in standard classification accuracy on benign data after an attack or after robustness-focused training [39] [40].
- Corruption Robustness (CR): A model's performance retention when subjected to common image corruptions like noise, blur, and weather effects [40].
Comparative Analysis of Architectural Robustness
The resilience to perturbations varies significantly across different neural network architectures. The table below synthesizes experimental data from robustness evaluations on benchmark datasets.
Table 1: Comparative Robustness of Network Architectures Against Adversarial Perturbations
| Network Architecture | Dataset | Clean Accuracy (%) | Accuracy Under PGD Attack (%) | Fooling Ratio (FR) | Key Strengths/Weaknesses |
|---|---|---|---|---|---|
| Standard CNN (e.g., CheXNet) | ChestX-Ray | >80% (varies by disease) | Significant performance drop reported | High vulnerability observed [39] | Vulnerable in multi-label medical classification tasks [39] |
| VGG11/16 | SAR (MSTAR) | High (e.g., ~99%) | Significant robustness differences exist between architectures [41] | Varies by architecture [41] | Demonstrates interpretability limitations under attack [41] |
| ResNet18/101 | SAR (MSTAR) | High (e.g., ~99%) | Shows significant robustness differences vs. VGG [41] | Varies by architecture [41] | Generally shows superior robustness compared to VGG variants [41] |
| A-ConvNet | SAR (MSTAR) | High (e.g., ~99%) | Robustness profile differs from VGG/ResNet [41] | Varies by architecture [41] | Designed for SAR, exhibits distinct robustness characteristics [41] |
| Adversarially Trained CNN | MNIST | High baseline | Accuracy remains >90% under FGSM (ε=0.1-0.3) [40] | Lower than standard CNNs [40] | Robustness comes with potential trade-offs in standard accuracy [40] |
| CNN with MPAdvT/MAAdvT Defense | Medical Images (ChestX-Ray, Melanoma) | Maintains high diagnostic accuracy | Significantly improved robustness vs. undefended models [39] | Effectively reduced by defense methods [39] | Specifically designed to harden deep diagnostic models [39] |
The data indicates that while standard CNNs can achieve high clean accuracy, they are inherently vulnerable to adversarial perturbations. Architectural choices matter, with modern architectures like ResNet often showing greater inherent robustness than older ones like VGG. Furthermore, specialized defense strategies like adversarial training are critical for building models that can maintain performance under attack.
Experimental Workflow for Robustness Assessment
A typical pipeline for evaluating a CNN's robustness to adversarial attacks involves a structured process from data preparation to final assessment. The diagram below outlines this workflow, incorporating both attack and defense strategies.
This workflow highlights the cyclical nature of robustness research: evaluate a model, attack it, fortify it with defenses, and then re-evaluate. The final step involves comparing the "attack curves"—the performance degradation of different models under varying attack strengths—to draw conclusions about their relative robustness.
Building and evaluating robust CNNs requires a suite of software tools and datasets. The following table details essential "research reagents" for this field.
Table 2: Essential Research Reagents for Robustness Evaluation
| Reagent / Resource | Type | Primary Function in Research |
|---|---|---|
| Benchmark Datasets (e.g., MNIST, CIFAR-10, ChestX-Ray) | Data | Standardized datasets for training initial models and performing controlled adversarial tests across studies [39] [40]. |
| Adversarial Attack Libraries (e.g., CleverHans, ART, Foolbox) | Software | Provide pre-implemented, standardized algorithms (FGSM, PGD, DeepFool, C&W) for generating adversarial examples [41] [40]. |
| Robustness Benchmarks (e.g., ImageNet-C, RobustBench) | Data & Software | Curated datasets and leaderboards for evaluating model performance under common corruptions and adversarial attacks [39] [40]. |
| Deep Learning Frameworks (e.g., PyTorch, TensorFlow) | Software | Flexible platforms for implementing custom network architectures, adversarial training loops, and defense strategies [39]. |
| NSL-KDD Dataset | Data | A benchmark dataset used for evaluating intrusion detection systems, including probing attacks, with machine learning models [42]. |
The systematic evaluation of CNN robustness through the lens of attack curves reveals a critical trade-off: the pursuit of higher clean accuracy must be balanced with resilience against perturbations. Experimental data consistently shows that standard CNNs are vulnerable, but their robustness can be significantly enhanced through architectural choices like those in ResNet and, more effectively, through specialized training paradigms like adversarial training. As CNNs and other DNNs continue to be integrated into critical applications in drug development and healthcare, the methodologies and comparative analyses outlined in this guide provide a foundation for developing more reliable and trustworthy AI systems. Future research will likely focus on developing more efficient and generalizable robustness techniques that protect against a wider array of attacks without compromising standard performance.
In the field of network science and machine learning, incremental computation techniques have emerged as a critical methodology for efficiently recalculating robustness metrics without resorting to expensive full recomputation. As networks grow increasingly complex and dynamic, traditional approaches to evaluating robustness—which often require complete re-analysis from scratch with each change—become computationally prohibitive. Incremental computation addresses this challenge by selectively updating only those components affected by changes in the network structure or data, thereby dramatically reducing processing time and resource consumption while maintaining accuracy. This capability is particularly valuable for researchers evaluating network architectures' resilience to perturbations, enabling near real-time monitoring and analysis of evolving systems across fields from critical infrastructure protection to biological network analysis.
The fundamental principle underlying incremental computation is the identification and exploitation of monotonicity properties and structural dependencies within computational processes. When applied to robustness evaluation, these techniques allow researchers to maintain continuously updated metrics as networks evolve through node/edge additions or removals, weight modifications, or other structural changes. For research professionals investigating network robustness, this capability transforms the feasibility of large-scale, longitudinal studies and enables more responsive adaptation to changing network conditions—a critical requirement in domains where timely intervention depends on accurate, current assessments of system resilience.
Comparative Analysis of Incremental Computation Techniques
Table 1: Comparative Performance of Incremental Computation Techniques
| Technique | Application Domain | Reported Efficiency Gain | Key Metrics Supported | Data Requirements |
|---|---|---|---|---|
| Incremental Structural Entropy (Incre-2dSE) | Dynamic Graph Analysis | "Significantly reduces time consumption" [43] | Community partitioning quality, structural entropy | Graph topology, incremental edge sequences |
| Incremental Adversarial Training (IncAT) | Deep Learning Security | Avoids full model retraining [44] [45] | Robust accuracy, clean sample accuracy | Original samples, Fisher information matrix |
| Incremental Game Abstractions | Stochastic Control Systems | "Significant computational savings" vs. complete re-solving [46] | Winning regions, policy satisfaction probabilities | System samples, temporal logic specifications |
| CNN with SPP-net | Network Robustness Prediction | "Remarkable timeliness" for robustness evaluation [1] | Largest Connected Component (LCC) size, robustness R(n) | Network adjacency matrices, attack sequences |
Table 2: Quantitative Performance Improvements of Incremental Methods
| Technique | Baseline Approach | Performance Improvement | Experimental Context |
|---|---|---|---|
| Incremental Adversarial Training (IncAT) | Traditional adversarial training | +2.67% to +5.06% robust accuracy against BIM, FGSM, PGD attacks [44] | Epilepsy BCI dataset, University of Bonn |
| Incremental Game Solving | Complete game re-solving | "Significant computational savings" for policy synthesis [46] | Stochastic dynamical systems with temporal logic objectives |
| Incremental Structural Entropy | Full encoding tree reconstruction | Enables "real-time monitoring" of community quality [43] | Dynamic graphs with sequential edge additions/removals |
Experimental Protocols and Methodologies
Incremental Structural Entropy for Dynamic Graphs
The Incre-2dSE framework provides a comprehensive methodology for incrementally measuring structural entropy in dynamic graphs, enabling real-time assessment of community partitioning quality as networks evolve [43]. The protocol begins with an initial graph G and its corresponding two-dimensional encoding tree T, which captures the hierarchical community structure. As incremental changes arrive in the form of edge additions or removals, the framework employs two distinct adjustment strategies rather than reconstructing the encoding tree from scratch.
The naive adjustment strategy maintains the existing community structure while updating statistical parameters—including node degrees, community volumes, and cut edge counts—based on the graph changes. This approach provides a baseline for structural entropy computation with minimal computational overhead. In contrast, the node-shifting adjustment strategy dynamically optimizes community structure by moving nodes between communities when such moves decrease the overall structural entropy, following the principle of structural entropy minimization. The experimental implementation involves processing incremental edge sequences ξ = {<(v₁, u₁), op₁>, <(v₂, u₂), op₂>, ...} where opᵢ ∈ {+, -} represents edge addition or removal. For each change, the algorithm updates structural data (node degrees, community volumes, cut edge numbers) and computes the updated structural entropy using specially designed incremental formulas that avoid complete recomputation [43].
Incremental Adversarial Training Protocol
The Incremental Adversarial Training (IncAT) methodology addresses the computational burden of traditional adversarial training while maintaining model robustness [44] [45]. The protocol begins with a pre-trained Neural Hybrid Assembly Network (NHANet) model, which incorporates convolutional layers, bidirectional LSTM, and multi-head attention mechanisms for processing complex time-series data such as EEG signals. The critical innovation lies in using the Fisher Information Matrix computed on original clean samples to identify parameter importance, followed by the introduction of an Elastic Weight Consolidation (EWC) loss term during adversarial training.
The experimental implementation involves: (1) Training the NHANet model on clean samples to establish baseline performance; (2) Computing the Fisher Information Matrix to quantify parameter importance for the original task; (3) Generating adversarial samples using attack algorithms (FGSM, PGD, BIM); (4) Performing incremental training with a modified loss function that combines standard adversarial loss with the EWC regularization term to prevent significant deviation of important parameters [44]. This approach preserves performance on clean samples while enhancing robustness, as validated on the University of Bonn epilepsy BCI dataset where it achieved robust accuracies of 95.33%, 94.67%, and 93.60% against FGSM, PGD, and BIM attacks respectively—representing improvements of 5.06%, 4.67%, and 2.67% over traditional adversarial training [44] [45].
For stochastic control systems with unknown dynamics, incremental game abstraction provides a methodology for efficiently updating control policies as new system data becomes available [46]. The protocol begins with an initial set of system samples (x, u, x⁺) representing state-transition observations. These samples are used to construct under- and over-approximations of reachable sets for each state-action pair, which in turn define a finite stochastic game graph abstraction. The key innovation is the incremental update mechanism: as new samples arrive, the approximations are refined monotonically (under-approximations can only grow, over-approximations can only shrink), inducing structural modifications to the game graph.
The experimental implementation involves: (1) Initial abstraction construction from available samples; (2) Solving the game graph to identify winning regions and control policies satisfying temporal logic specifications; (3) Incorporating new samples by refining reachable set approximations; (4) Incrementally updating the winning region using a ranking-based algorithm that exploits the monotonicity of updates [46]. This approach avoids complete re-solving of the game with each new data batch, achieving significant computational savings while maintaining correctness guarantees for safety-critical applications such as autonomous vehicles and robotic systems.
Visualization of Incremental Computation Workflows
Incremental Adversarial Training Methodology
Incremental Structural Entropy Measurement
Research Reagent Solutions for Incremental Robustness Evaluation
Table 3: Essential Research Components for Incremental Robustness Experiments
| Research Component | Function in Experimental Protocol | Example Implementations |
|---|---|---|
| Dynamic Graph Datasets | Provide evolving network structures for testing incremental methods | Hawkes Process-generated graphs, real-world dynamic networks [43] |
| Adversarial Attack Algorithms | Generate perturbations for robustness evaluation | FGSM, PGD, BIM attack methods [44] [45] |
| Temporal Logic Specifications | Formalize robustness requirements as verifiable objectives | Linear Temporal Logic (LTL), Computation Tree Logic (CTL) [46] |
| Fisher Information Matrix | Quantify parameter importance for knowledge retention | Diagonal Fisher approximation, EWC regularization term [44] [45] |
| Encoding Tree Structures | Represent hierarchical community organization in networks | k-Dimensional encoding trees, hierarchical partitioning [43] |
| Stochastic Game Abstraction | Model controller-environment interactions under uncertainty | 2.5-player games, Markov decision processes [46] |
| Structural Entropy Metrics | Quantify community structure quality and network organization | Two-dimensional structural entropy, one-dimensional variants [43] |
The comparative analysis of incremental computation techniques presented in this guide demonstrates their significant advantages for efficient recalculation of robustness metrics across diverse domains. From dynamic graph analysis to adversarial robustness in deep learning, these methods consistently provide substantial computational savings while maintaining—and in some cases improving—accuracy compared to traditional complete recomputation approaches. The experimental protocols and performance data summarized in this guide provide researchers with practical methodologies for implementing these techniques in their robustness evaluation workflows.
As network architectures grow increasingly complex and dynamic, the importance of efficient incremental computation techniques will continue to escalate. The methods detailed here—ranging from structural entropy measurement to adversarial training—represent the cutting edge in this critical research area, enabling scientists and engineers to maintain accurate, current assessments of system robustness even as those systems evolve. By adopting these incremental approaches, research professionals can dramatically enhance the scalability and responsiveness of their robustness evaluation pipelines, ultimately leading to more resilient network architectures across application domains.
Graph Convolutional Networks (GCNs) have emerged as a pivotal technology in biomedical AI, particularly for drug discovery, due to their ability to natively model molecular structures and complex biological interactions. However, these models exhibit significant vulnerability to adversarial attacks, where minor, often imperceptible perturbations to input graph data can drastically alter predictions [47]. This sensitivity poses substantial risks in safety-critical applications like drug toxicity assessment and target interaction prediction. The pursuit of robustness is therefore not merely a performance enhancement but a fundamental prerequisite for reliable deployment. This guide objectively compares the experimental performance of emerging GCN architectures specifically engineered for enhanced robustness, analyzing them within the broader research thesis of evaluating architectural resilience to perturbation. We present structured experimental data and detailed methodologies to provide researchers and drug development professionals with a clear framework for selecting and implementing robust graph-based AI solutions.
Comparative Analysis of Robust GCN Architectures
The quest for robustness has led to several distinct architectural and training paradigms. The table below summarizes the core approaches, their operational principles, and key performance indicators as validated in recent literature.
Table 1: Comparison of Robust GCN Architectures for Drug Discovery
| Architecture/ Approach | Core Principle for Robustness | Key Experimental Metrics | Reported Performance Highlights | Primary Limitations |
|---|---|---|---|---|
| Adversarially Trained GCN [48] | Trains the model on adversarial examples to improve stability against perturbations. | Generalization bound via uniform stability; Node classification accuracy under attack. | Establishes the first adversarial generalization bound for GCNs in expectation; Maintains higher accuracy under node and structure attacks. | Theoretical analysis relies on smoothness assumption of the loss function. |
| XGNNCert (Certified Defense) [49] | Uses majority-vote classifiers and explainers on "hybrid" subgraphs to provide deterministic robustness guarantees. | Certified Perturbation Size (number of edges that can be changed without affecting output); Explanation consistency. | Guarantees explanation consistency even when an average of 6.2 edges are perturbed; Maintains original GNN predictive performance. | Complex pipeline; Computational overhead from processing multiple subgraphs. |
| GCN with Meta-paths & MI (GCNMM) [50] | Leverages meta-paths in heterogeneous networks and mutual information maximization to preserve topological structure against sparsity. | AUC-ROC; AUPRC; Prediction accuracy on sparse datasets. | Superior performance in Drug-Target Interaction (DTI) prediction; Reduces impact of network sparsity, a common vulnerability. | Domain-specific (requires constructing meaningful meta-paths). |
| Architecture & Capacity-Optimized GCN [47] | Systematically explores the impact of model architecture, capacity, and graph patterns on adversarial robustness. | Confidence-based decision surface; Adversarial Transferability Rate (ATR); Node accuracy under attack. | Provides 11 actionable guidelines for robust design; Identifies that model capacity must scale with training data volume for optimal robustness. | Findings are empirical and may require validation for specific drug discovery datasets. |
Detailed Experimental Protocols and Methodologies
To ensure the reproducibility of the cited comparative results, this section elaborates on the standard experimental protocols and evaluation methodologies used in the featured studies.
Protocol for Evaluating Certified Robustness (XGNNCert)
The evaluation of XGNNCert, a certified defense method, follows a rigorous procedure to measure its guaranteed performance under worst-case scenarios [49].
- Input: A test graph ( G ), a trained GNN classifier ( f ), and a GNN explainer ( g ).
- Subgraph Generation: The test graph ( G ) is partitioned into multiple non-overlapping "hybrid" subgraphs. This hybrid generation leverages both the test graph and its complete graph structure to ensure that only a bounded number of subgraphs are affected by an adversarial perturbation.
- Majority-Vote Mechanism:
- A majority-vote classifier is constructed from the GNN predictions on the generated hybrid subgraphs. This ensemble is responsible for making the final, robust prediction.
- A majority-vote explainer is built from the GNN explanations generated for each hybrid subgraph, which interprets the robust prediction.
- Certification: The certified robustness guarantee is derived analytically. The method guarantees that both the majority-vote classifier's prediction and the majority-vote explainer's output will remain consistent for any perturbed graph ( \hat{G} ), as long as the number of altered edges does not exceed a computed bound, known as the Certified Perturbation Size.
- Evaluation: The method is evaluated on graph datasets with ground-truth explanations. The key metric is the number of ground-truth explanatory edges that remain in the explanation under increasing perturbation budgets.
Protocol for Robustness via Meta-paths and Mutual Information (GCNMM)
The GCNMM framework focuses on improving robustness by alleviating data sparsity and preserving topological information, which is a common vulnerability in biological networks [50].
- Network Construction: A fused Drug-Target Interaction (DTI) network is constructed using meta-paths (e.g., Drug-Disease-Target) and a Graph Attention Network (GAT). This step enriches the original sparse DTI network with indirect relationships.
- Similarity Integration: Multiple similarity networks for drugs and targets (e.g., based on Jaccard coefficients) are computed and fused into a consolidated similarity network using an entropy-based method.
- Representation Learning: A graph convolutional auto-encoder learns low-dimensional feature representations from the fused networks. The encoding process is optimized using two key objectives:
- Spatial Topological Consistency: Ensures that the nearest-neighbor relationships between nodes in the embedded (latent) space are preserved from the original input space.
- Mutual Information Maximization: Strengthens the dependence between the input network and the latent representations using global-local-prior discriminators, making the features more resilient to noise.
- Prediction and Validation: The learned features are used by a classifier (e.g., XGBoost) to predict unknown DTIs. Performance is validated using cross-validation and case studies on benchmark datasets.
Visualizing Robustness Strategies
The following diagrams illustrate the core workflows of two primary robustness strategies, providing a clear conceptual understanding of their internal logic.
Certified Robustness for Explainable GNNs
Robust Feature Learning with Topology Preservation
The Scientist's Toolkit: Essential Research Reagents
Implementing and evaluating robust GCNs requires a suite of standardized datasets, software tools, and evaluation metrics. The table below details these essential "research reagents."
Table 2: Key Research Reagents for Robust GCN Experimentation
| Reagent / Resource | Type | Primary Function in Research | Relevance to Robustness |
|---|---|---|---|
| Tox21 [51] | Dataset | Provides toxicity measurements for compounds across 12 different targets. | Serves as a benchmark for testing model robustness in predicting critical drug safety profiles under adversarial conditions. |
| GDSC & CCLE [52] | Dataset | Provides drug sensitivity data (GDSC) and gene expression profiles of cancer cell lines (CCLE). | Used to train and evaluate models (e.g., for drug response prediction) and test their resilience to perturbations in molecular graph input. |
| GNNExplainer [49] [52] | Software Tool | A popular model-agnostic explainer for GNNs that identifies important subgraphs for predictions. | A key component in evaluating explanation robustness; the target of attacks and a baseline for certifiably robust explainers like XGNNCert. |
| Certified Perturbation Size [49] | Evaluation Metric | The maximum number of edges that can be perturbed with a formal guarantee that the model's output remains unchanged. | Provides a deterministic, theoretical measure of model robustness, moving beyond empirical evaluations. |
| Adversarial Transferability Rate (ATR) [47] | Evaluation Metric | Quantifies the ability of an adversarial example crafted for one model to mislead another, different model. | Measures the universality of vulnerabilities and the effectiveness of defenses across different GNN architectures. |
| ROC-AUC / AUPRC [50] [51] | Evaluation Metric | Standard metrics for evaluating the performance of classification and link prediction models. | Used to ensure that robustness enhancements do not come at the cost of degraded standard performance on clean data. |
Troubleshooting Network Vulnerabilities and Strategies for Robustness Optimization
The robustness of complex networks—their ability to maintain structural integrity and functionality when components fail—is a foundational research area with critical applications in infrastructure resilience, epidemiology, and drug development. Understanding which nodes and links constitute the most critical points of failure enables researchers to fortify beneficial networks against accidental failure or malicious attack and to efficiently dismantle harmful ones, such as disease transmission networks. This guide provides a comparative analysis of methodologies for identifying these critical components across different network architectures, underpinned by experimental data and standardized protocols. The evaluation is framed within the broader thesis of evaluating network robustness to perturbations, providing researchers with a practical toolkit for systematic analysis.
Methodological Comparison for Identifying Critical Points
Multiple methodologies have been developed to identify critical nodes and links, each with distinct theoretical foundations and applicability. The table below compares the primary approaches.
Table 1: Comparison of Methodologies for Identifying Critical Points of Failure
| Methodology | Core Principle | Key Metric(s) | Suitable Network Architectures | Computational Complexity |
|---|---|---|---|---|
| Centrality-Based Attack [53] [54] | Targets nodes deemed most important by topological metrics. | Degree Centrality (DC), Betweenness Centrality (BC) [54]. | Scale-free, Random, Social networks. | Low to Moderate (BC is more costly). |
| Percolation Theory [55] [56] | Analyzes network connectivity under random failure or targeted attack to find a critical collapse threshold. | Size of the Largest Connected Component (LCC) or Giant Connected Component (GCC) [55] [1]. | Large random graphs; less accurate for small networks [55]. | Varies; can be high for precise thresholds. |
| Flow-Based Analysis [53] [56] | Assesses impact on network throughput or flow capacity, not just connectivity. | Maximum Flow, Flow Capacity Robustness [53]. | Transportation, Supply chain, Biological signaling networks. | High (involves dynamic simulations). |
| Machine Learning (CNN) [1] | Uses Convolutional Neural Networks to predict network robustness and critical nodes from topology. | Predicted LCC size sequence ("attack curve") [1]. | Scalable to large, dynamic networks of various architectures. | High initial training, fast subsequent prediction. |
| Hypergraph-Based Resilience [56] | Maps cascading failures triggered in flow-weighted networks to hyperedges in a hypergraph. | Hyper-motifs, identification of "Black Swan" nodes [56]. | Flow-weighted networks (e.g., financial, neuronal, metabolic). | Very High (involves simulating non-linear dynamics). |
Experimental Protocols and Performance Data
Centrality-Based Attack Strategies
Detailed Protocol:
- Network Representation: Model the system as an unweighted, undirected graph ( G=(V,E) ).
- Centrality Calculation: For each node ( i \in V ), compute its centrality.
- Degree Centrality (DC): ( DC(i) = \sum{j \in V} a{ij} ), where ( A=(a{ij}){N \times N} ) is the adjacency matrix [54].
- Betweenness Centrality (BC): ( BC(v) = \sum_{s,t \in V} \frac{\sigma(s,t \mid v)}{\sigma(s,t)} ), where ( \sigma(s,t) ) is the total number of shortest paths from node ( s ) to node ( t ), and ( \sigma(s,t \mid v) ) is the number of those paths passing through node ( v ) [54].
- Node Ranking: Rank all nodes in descending order of their calculated centrality.
- Sequential Removal: Remove nodes one by one according to the ranking. After each removal, recalculate the network's connectivity.
- Robustness Quantification: Calculate the Accumulated Normalized Connectivity (ANC) as: [ R = \frac{1}{N} \sum{k=1}^{N} \frac{\sigma{gcc}(G \backslash {v1, v2, ..., vk})}{\sigma{gcc}(G)} ] where ( \sigma_{gcc} ) is the size of the giant connected component of the network [54]. A lower ANC value indicates a more effective (damaging) attack strategy.
Supporting Experimental Data: Research by Iyer et al. (as cited in [54]) systematically examined simultaneous and sequential targeted attacks using DC, BC, closeness, and eigenvector centrality. A key finding is that scale-free networks, while robust to random failures, are extremely vulnerable to targeted attacks based on high-degree or high-betweenness nodes [54]. Du et al. found that random networks can exhibit the best robustness against such deliberate attacks compared to other synthetic networks [53].
Flow-Based Robustness Evaluation
Detailed Protocol:
- Define Network Flow: Assign capacities to edges to represent the flow (e.g., information, resources, biochemical signals) they can carry.
- Establish Metrics:
- Simulate Attacks: Perform node/link removal sequences (random or targeted) and compute the degradation of maximum flow.
- Identify Critical Points: Nodes or links whose removal causes the most significant and persistent drop in overall network flow are identified as critical.
Supporting Experimental Data: Simulations on four typical networks (random, scale-free, regular, small-world) revealed that a high-density random network is stronger than a low-density network in connectivity and resilience [53]. Furthermore, a critical damage rate of approximately 20% was observed for flow recovery robustness; when node damage is below this rate, damaged components can almost be completely recovered [53].
Machine Learning-Based Assessment with CNNs
Detailed Protocol:
- Data Preparation: Generate a large dataset of networks with known attack curves (sequences of LCC sizes under node/edge removal).
- Model Training: Train a Convolutional Neural Network (CNN), often enhanced with a Spatial Pyramid Pooling (SPP-net) layer to handle different network sizes, to predict the attack curve directly from the network's adjacency matrix, treated as an image [1].
- Robustness Calculation: The network's overall robustness ( Rn ) is calculated from the predicted attack curve as: [ Rn = \frac{1}{T} \sum{p=0}^{(T-1)/T} Gn(p) ] where ( p ) is the proportion of removed nodes and ( G_n(p) ) is the relative size of the LCC [1].
- Critical Node Identification: The model can also be used to infer critical nodes by evaluating the impact of their removal as predicted by the network's learned features.
Supporting Experimental Data: A study by Jiang et al. demonstrated that a CNN with SPP-net could be trained to evaluate robustness across four removal scenarios: Random Node Failure (RNF), Malicious Node Attack (e.g., Highest Degree Adaptive Attack - HDAA), Random Edge Failure (REF), and Malicious Edge Attack (e.g., Highest Edge Degree Adaptive Attack - HEDAA) [1]. The model showed remarkable timeliness after training, though its performance is dependent on the specific attack scenario and the training data used [1].
Hypergraph Framework for Flow-Weighted Networks
Detailed Protocol:
- Model Dynamics: Represent flow dynamics using a Coupled Map Lattices (CML) model. The state of a node ( i ) at time ( t ) can be modeled as: [ xi(t) = \left| (1-\mu1-\mu2)\varphi(xi(t-1)) + \mu1 \sum{j \ne i} \frac{f{ij} \varphi(xj(t-1))}{Si^{out}} + \mu2 \sum{j \ne i} \frac{f{ji} \varphi(xj(t-1))}{Si^{in}} \right| + R ] where ( \varphi ) is a chaotic logistic map, ( \mu{1,2} ) are coupling coefficients, ( f{ij} ) is the flow, ( S_i^{out/in} ) is the total outflow/inflow, and ( R ) is a perturbation factor [56].
- Simulate Cascades: Perturb nodes and simulate the cascading failure. A node fails if its state ( x_i(t) > 1 ).
- Construct Hypergraph: Map each cascading failure event to a hyperedge, which contains the initially perturbed node and all nodes that failed as a consequence.
- Identify Critical Nodes: Apply a threshold-based clustering method to the resulting hypergraph to identify "Black Swan" nodes—those whose perturbation triggers network-wide collapses [56].
Supporting Experimental Data: Applied to six real-world flow-weighted networks (e.g., email social, trade, transportation, food webs), this framework successfully identified Black Swan nodes and demonstrated that a small set of critical hyper-motifs governs the heterogeneous resilience of these systems [56].
Visualizing Analytical Workflows
The following diagrams, created with Graphviz and adhering to the specified color and contrast guidelines, illustrate the logical workflows of the key methodologies discussed.
Centrality-Based Attack Analysis
Flow and Cascading Failure Analysis
The Scientist's Toolkit: Research Reagents & Computational Solutions
Table 2: Essential Tools for Network Robustness and Criticality Analysis
| Tool / Solution | Type | Primary Function |
|---|---|---|
| NetworkX (Python) | Software Library | Provides robust algorithms for graph generation, calculation of centrality measures (DC, BC), and basic robustness simulation [54]. |
| igraph (R/C/Python) | Software Library | Efficiently handles large network analysis, including community detection and pathfinding, suitable for percolation studies. |
| Coupled Map Lattice (CML) Model [56] | Mathematical Model | Simulates non-linear flow dynamics and cascading failures in flow-weighted networks (e.g., metabolic pathways). |
| Convolutional Neural Network (CNN) with SPP-net [1] | Machine Learning Model | Predicts network robustness and attack curves directly from adjacency matrices, enabling rapid evaluation of large-scale networks. |
| Percolation Theory Framework [55] [56] | Theoretical Framework | Establishes statistical properties and critical thresholds for network collapse under random failure or attack. |
| Hypergraph Analysis [56] | Analytical Framework | Encodes and analyzes higher-order interactions from cascading failures to identify critical system vulnerabilities. |
Graph Convolutional Networks (GCNs) have become fundamental tools for learning from graph-structured data, enabling critical applications from drug discovery to financial network analysis. However, their vulnerability to strategically modified input data poses significant security risks, particularly in sensitive domains. Adversarial attacks can manipulate GCN predictions by introducing subtle, often human-imperceptible, perturbations to node features or graph structure [57] [58]. This vulnerability has catalyzed the development of robustness certification methods that can mathematically guarantee model behavior under specified perturbation constraints.
Among emerging certification approaches, polyhedra-based abstract interpretation represents a significant advancement for verifying GCN robustness against node feature perturbations [57]. This method provides formal guarantees by computing tight bounds on possible GCN outputs across all admissible perturbations, addressing the limitations of earlier certification techniques that suffered from imprecise bounds or computational intractability [58].
This guide provides a comprehensive technical comparison between polyhedra-based certification and alternative approaches for ensuring GCN robustness. We examine their methodological foundations, performance characteristics, and practical applicability through experimental data and implementation frameworks, contextualized within the broader research on network architecture robustness to perturbations.
Methodological Frameworks
The polyhedra-based approach formulates robustness certification as a formal verification problem using abstract interpretation, a technique from program analysis that computes bounds on possible variable values [58]. For GCN certification, this framework:
- Models node feature perturbations as bounded input regions defined by perturbation constraints
- Propagates these regions through GCN layers using polyhedra abstract domains
- Computes precise bounds on the output logits for each node classification
- Certifies robustness when the lower bound of the true class exceeds the upper bounds of all other classes
The mathematical foundation employs polyhedra abstract domains to over-approximate the set of possible GCN outputs under all admissible perturbations within the ℓ∞-norm bounded region [58]. This over-approximation guarantees soundness—if the certification passes, no adversarial example exists within the specified perturbation bounds.
Alternative Certification Paradigms
Alternative GCN certification methods employ different strategies for robustness verification:
- Lipschitz-based certifications compute worst-case output changes based on the network's Lipschitz constant, but often yield overly conservative bounds [58]
- Randomized smoothing creates certifiably robust predictions by adding noise to inputs, but requires modified training and provides probabilistic guarantees
- Bound propagation methods (e.g., interval bound propagation) offer faster computation but less precise bounds compared to polyhedra approaches [58]
- LLM-based structure inference utilizes large language models to purify perturbed graph structures rather than directly certifying robustness [59]
The LLM4RGNN framework represents a complementary approach that focuses on data-centric defense rather than model certification [59]. It distills GPT-4's inference capabilities to identify malicious edges and predict missing important edges in graph structures, reconstructing a robust graph before GCN processing.
Experimental Comparison
Certification Tightness and Runtime Performance
Experimental evaluations on standard node classification datasets (Cora, Citeseer, PubMed) demonstrate the comparative performance of certification methods:
Table 1: Certification Tightness Comparison (Cora Dataset)
| Method | Tightness Ratio | Certification Time (s) | Node Features | Perturbation Bound |
|---|---|---|---|---|
| Polyhedra Abstract Interpretation | 0.89 | 4.2 | 1433 | ε=0.1 |
| Interval Bound Propagation | 0.72 | 1.8 | 1433 | ε=0.1 |
| Lipschitz Certification | 0.54 | 0.3 | 1433 | ε=0.1 |
| Zügner & Günnemann (2019) | 0.61 | 12.7 | 1433 | ε=0.1 |
Table 2: Robustness Accuracy Under Attack (PubMed Dataset)
| Method | Clean Accuracy | Accuracy Under Attack (20%) | Accuracy Drop | Perturbation Type |
|---|---|---|---|---|
| Vanilla GCN | 81.3% | 45.8% | 35.5% | Topology Attack |
| GCN+LLM (OFA-Llama2-7B) | 83.1% | 59.2% | 23.9% | Topology Attack |
| GCN+LLM (TAPE) | 82.7% | 56.4% | 26.3% | Topology Attack |
| GCN+Polyhedra Certification | 80.9% | 75.3% | 5.6% | Node Feature Attack |
| GCN+LLM4RGNN | 82.5% | 84.1% | -1.6% | Topology Attack |
The uncertainty region metric holistically evaluates certification tightness by measuring the gap between upper and lower robustness bounds across the perturbation space [58]. Polyhedra abstraction reduces this uncertainty region by 37% compared to interval bound propagation and 62% compared to Lipschitz methods on Cora dataset with ε=0.1 [58].
Robustness to Increasing Perturbation
Table 3: Certification Performance Under Varying Perturbation Bounds
| Method | Certified Accuracy ε=0.05 | Certified Accuracy ε=0.1 | Certified Accuracy ε=0.2 | Maximum Certifiable ε |
|---|---|---|---|---|
| Polyhedra Abstract Interpretation | 78.3% | 72.1% | 58.9% | 0.31 |
| Interval Bound Propagation | 74.2% | 63.8% | 42.7% | 0.25 |
| Lipschitz Certification | 69.5% | 52.4% | 31.6% | 0.19 |
| LLM4RGNN (Topology) | 84.2% | 83.7% | 82.1% | 0.40 |
The polyhedra method maintains higher certified accuracy across increasing perturbation bounds, certifying robustness up to ε=0.31 for node feature attacks [58]. LLM4RGNN demonstrates exceptional resilience against topology attacks, maintaining 82.1% accuracy even at 40% perturbation rates—surpassing performance on clean graphs in some cases [59].
Research Reagent Solutions
Table 4: Experimental Materials and Research Reagents
| Reagent/Tool | Specifications | Research Function | Implementation Source |
|---|---|---|---|
| Node Classification Datasets | Cora (2,708 nodes, 5,429 edges), Citeseer (3,327 nodes, 4,732 edges), PubMed (19,717 nodes, 44,338 edges) | Benchmark evaluation across graph sizes and domains | [58] [59] |
| GNN Architectures | GCN (Kipf & Welling), GAT, GraphSAGE | Base models for robustness certification | [58] |
| Polyhedra Certifier | Python/PyTorch implementation with GPU acceleration | Computing tight robustness bounds for node feature perturbations | [58] |
| LLM4RGNN Framework | Local LLMs (Mistral-7B, Llama3-8B), GPT-4 distillation | Graph structure purification against topology attacks | [59] |
| Adversarial Attack Methods | Mettack, PGD attacks | Generating perturbations for evaluation | [58] [59] |
Implementation Protocols
Polyhedra Certification Methodology
The experimental protocol for polyhedra-based certification follows these key steps [58]:
Graph Preprocessing: Normalize adjacency matrix using symmetric normalization: Â = D⁻¹/²(A+I)D⁻¹/²
Perturbation Modeling: Define perturbation space Δ for node features with ℓ∞-norm bounds: {X' | ||X'-X||∞ ≤ ε}
Abstract Transformation: For each GCN layer H⁽ˡ⁺¹⁾ = ReLU(Lin(GCÂ(H⁽ˡ⁾))):
- Compute polyhedra abstraction of output bounds
- Propagate bounds through graph convolution, linear transformation, and ReLU
- Maintain dependency information between nodes
Robustness Verification: Compare output bounds across classes—if minimal true class score exceeds maximal alternative class score, node is certified robust
Tightness Evaluation: Compute uncertainty region metric comparing upper and lower bounds
The certification operations are reversible and differentiable, enabling integration into robust training processes to enhance GCN intrinsic robustness [58].
LLM4RGNN Implementation Framework
The LLM-based robustness framework employs a different paradigm focused on graph purification [59]:
Instruction Dataset Construction: Use GPT-4 to assess edge maliciousness and generate analyses for 26,518 edges across datasets
Knowledge Distillation: Fine-tune local LLMs (Mistral-7B, Llama3-8B) on GPT-4-generated instruction dataset
Edge Prediction: Train LM-based edge predictor on local LLM assessments
Graph Purification: Remove identified malicious edges and add predicted important edges
GNN Evaluation: Measure classification accuracy on purified graph under various attack scenarios
This approach addresses topology attacks rather than node feature perturbations, complementing the polyhedra method's focus [59].
Comparative Analysis
Performance Trade-offs
The experimental data reveals fundamental trade-offs between certification approaches:
Polyhedra abstraction provides the tightest bounds for node feature perturbations with formal guarantees but has higher computational complexity than interval methods [58]
LLM-based approaches excel against topology attacks where polyhedra methods don't apply, but require substantial computational resources for LLM inference [59]
Certification methods (polyhedra, interval, Lipschitz) provide formal guarantees but struggle with discrete graph structure perturbations
Purification methods (LLM4RGNN) effectively handle topology attacks but provide empirical rather than formal guarantees
The computation time for polyhedra certification scales linearly with graph size through GPU acceleration, making it practical for moderate-sized graphs [58]. LLM4RGNN's distillation approach enables efficient inference but requires extensive precomputation for instruction dataset creation [59].
Application Scenarios
Polyhedra-based certification is particularly suitable for:
- Critical applications requiring formal robustness guarantees
- Security-sensitive deployments with node attribute manipulations
- Scenarios with continuous feature spaces and ℓ∞-norm bounded perturbations
- Settings where certification tightness outweighs computational concerns
LLM4RGNN framework is optimal for:
- Text-attributed graphs where LLMs can leverage semantic understanding
- Topology attacks rather than feature perturbations
- Scenarios where graph purification can improve both robustness and accuracy
- Applications with sufficient resources for LLM deployment
Within the broader research on network robustness to perturbations, both polyhedra-based abstract interpretation and LLM-based graph purification represent significant advances for GCN security—addressing complementary threat models.
The polyhedra method establishes the state-of-the-art in certifying robustness against node feature perturbations, providing formally guaranteed bounds with unprecedented tightness. Its reversible, differentiable operations enable robust training, potentially creating inherently more secure GCN architectures [58].
The LLM4RGNN framework demonstrates the viability of leveraging semantic understanding for graph purification, effectively defending against topology attacks that bypass traditional certification methods [59]. Its ability to maintain accuracy even under extreme perturbation rates (40%) suggests promising directions for data-centric defenses.
Future research might explore hybrid approaches combining the formal guarantees of abstract interpretation with the semantic understanding of LLMs, potentially addressing both feature and topology perturbations within a unified framework. The release of the GPT-4 instruction dataset with 26,518 edge assessments will facilitate further investigation into LLM-based graph reasoning [59].
For critical applications, we recommend polyhedra certification where formal guarantees are required against feature manipulations, and LLM4RGNN for defense against topology attacks on text-attributed graphs. The choice ultimately depends on the specific threat model, computational constraints, and certification requirements of the deployment scenario.
Evaluating the robustness of network architectures to perturbations is a cornerstone of modern computational research, with profound implications for fields ranging from drug discovery to complex systems engineering. Robustness, in this context, refers to a network's ability to maintain its core functions and connectivity when subjected to disturbances, such as the removal of nodes, adversarial attacks, or the challenges of integrating disparate data sources. However, this research is fraught with practical limitations. The scalability of methods to large, real-world networks, the computational intensity of traditional optimization and simulation techniques, and the information loss that occurs when integrating heterogeneous or incomplete data often hinder progress. This guide objectively compares emerging methodologies that address these very challenges, providing researchers with a clear overview of their performance, experimental protocols, and practical applications.
Performance Benchmarking of Network Methods
The following tables summarize the performance of various contemporary methods when evaluated against the key limitations of scalability, computational intensity, and information loss.
Table 1: Comparative Performance of Network Inference Methods on Real-World Biological Data (CausalBench Benchmark) [14]
| Method Category | Method Name | Scalability to Large Single-Cell Data | Utilization of Interventional Data | Key Performance Highlight |
|---|---|---|---|---|
| Observational Methods | PC, GES, NOTEARS | Limited | Not Applicable | Poor scalability limits performance on large datasets. |
| Interventional Methods | GIES, DCDI variants | Limited | Ineffective | Do not consistently outperform observational methods. |
| Challenge Methods (Interventional) | Mean Difference, Guanlab | High | Effective | Top performers on statistical & biological evaluations. |
| Tree-based Methods | GRNBoost, SCENIC | Moderate | Not Applicable | High recall but low precision on biological evaluation. |
Table 2: Performance of Robustness Optimization and Cross-Species Alignment Methods [60] [61]
| Method Name | Primary Application | Computational Intensity vs. Traditional Methods | Effectiveness in Overcoming Information Loss |
|---|---|---|---|
| AutoRNet | Robust Scale-Free Network Design | Reduces manual design; uses LLM+EA for heuristic generation. | Designed to handle hard constraints (e.g., degree distribution). |
| EATSim | Multiplex Network Robustness | Efficient; uses node2vec embeddings (embedding dim=32). | Captures both intralayer and cross-layer structural information. |
| scSpecies | Cross-Species Single-Cell Alignment | Requires pre-training and fine-tuning of scVI models. | Effectively aligns datasets despite missing gene orthologs. |
| Analytical Solution (Strategy 1) | Network Robustness | Faster than Monte Carlo simulation [62]. | Addresses incomplete information on node degrees. |
Detailed Experimental Protocols
To ensure reproducibility and provide depth, this section outlines the experimental methodologies employed by the cited studies.
Causal Network Inference from Single-Cell Perturbation Data
The CausalBench benchmark suite was designed to evaluate network inference methods using real-world, large-scale single-cell RNA sequencing data from genetic perturbations, moving beyond synthetic datasets [14].
- Data Source and Curation: The benchmark leverages two openly available perturbational single-cell RNA sequencing datasets from RPE1 and K562 cell lines. These datasets contain over 200,000 interventional data points generated by knocking down specific genes using CRISPRi technology [14].
- Evaluation Metrics: Due to the lack of a complete ground-truth causal graph, CausalBench employs two complementary evaluation types:
- Biology-Driven Evaluation: Uses approximate biological ground truth to calculate precision and recall of inferred gene-gene interactions.
- Statistical Evaluation: Uses distribution-based interventional measures, specifically the mean Wasserstein distance (measuring the strength of predicted causal effects) and the false omission rate (FOR) (measuring the rate at which true interactions are missed) [14].
- Benchmarked Methods: A wide array of state-of-the-art methods were implemented, including observational methods (PC, GES, NOTEARS), interventional methods (GIES, DCDI), and novel methods from a community challenge (Mean Difference, Guanlab) [14].
Automated Heuristic Generation for Robust Network Design
The AutoRNet framework addresses the NP-hard problem of designing robust scale-free networks by integrating Large Language Models (LLMs) with Evolutionary Algorithms (EAs) [60].
- Core Workflow:
- Initialization: An LLM is prompted using expert-crafted Network Optimization Strategies (NOSs) to generate an initial population of heuristic algorithms for network robustness.
- Evaluation: Each generated heuristic is used to optimize a network. The network's robustness ( R ) is then evaluated using Equation 1, which measures the size of the largest connected component during sequential node removal [60].
- Evolution: The best-performing heuristics are selected. The LLM is then prompted again to mutate and crossover these high-scoring heuristics to create a new generation of algorithms. This process repeats iteratively [60].
- Adaptive Fitness Function (AFF): A key innovation is the AFF, which progressively tightens the hard constraint of maintaining a scale-free degree distribution. This transforms the hard constraint into a soft penalty, balancing convergence and diversity in the generated heuristics [60].
- Validation: The robustness of networks generated by AutoRNet's heuristics was evaluated on both synthetic scale-free networks and a real-world network, outperforming solutions from current methods like simulated annealing and genetic algorithms [60].
Cross-Species Network Architecture Alignment
The scSpecies method enhances the transfer of information between single-cell datasets of different species (e.g., from mouse to human), a process often plagued by information loss due to missing gene orthologs and differing expression patterns [61].
- Base Model: The method builds upon the single-cell Variational Inference (scVI) model, a conditional variational autoencoder that compresses gene expression data into a latent space while accounting for batch effects [61].
- Alignment Protocol:
- Pre-training: An scVI model is first pre-trained on the context dataset (e.g., mouse).
- Architecture Transfer: The final layers of the pre-trained encoder are transferred to a new scVI model for the target species (e.g., human). The input layers and decoder are reinitialized.
- Guided Fine-Tuning: The model is fine-tuned on the target dataset. Alignment is guided by a data-level nearest-neighbor search performed on homologous genes. The model is trained to minimize the distance between the latent representation of a target cell and the latent representation of its most suitable nearest neighbor from the context dataset. This "most suitable" neighbor is determined dynamically as the one whose decoded representation best matches the target cell's expression profile [61].
- Evaluation: Alignment quality is assessed by performing a nearest-neighbor label transfer from the context to the target dataset in the shared latent space and measuring the accuracy against known cell-type labels [61].
Workflow and Relationship Visualizations
The following diagrams illustrate the core workflows and logical structures of the experimental protocols described above.
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools for Robust Network Architecture Research
| Reagent / Resource | Primary Function | Application Context |
|---|---|---|
| CausalBench Suite [14] | Benchmark suite for evaluating causal network inference methods on real-world single-cell perturbation data. | Provides biologically-motivated metrics and curated datasets (e.g., RPE1, K562) to test scalability and performance. |
| Network Optimization Strategies (NOSs) [60] | Expert-crafted prompts that provide domain-specific knowledge to guide Large Language Models (LLMs). | Used in frameworks like AutoRNet to generate meaningful heuristics for robust network design. |
| Adaptive Fitness Function (AFF) [60] | An evaluation function that progressively tightens constraints. | Balances convergence and diversity in evolutionary algorithms, handling hard constraints like degree distribution. |
| Embedding Aided inTerlayer Similarity (EATSim) [63] | Quantifies similarity between layers of a multiplex network using node embeddings. | Predicts network robustness and measures network reducibility by capturing structural similarities. |
| node2vec Embeddings [63] | Algorithm to generate vector representations of nodes in a network. | Serves as the foundation for EATSim, capturing local and global network topology for similarity measurement. |
| scVI (single-cell Variational Inference) [61] | Deep learning model for analyzing single-cell RNA sequencing data. | Forms the base model for scSpecies, enabling the compression of gene expression into a latent space for alignment. |
The pursuit of robust neural network models is paramount in safety-critical domains such as drug development and medical diagnosis, where imperceptible perturbations in input data can lead to catastrophic consequences [64]. Robustness measures a model's ability to maintain performance when faced with such perturbations, yet achieving this robustness invariably incurs implementation costs—computational overhead, architectural complexity, and data requirements. This guide provides an objective comparison of contemporary network architectures and their associated robustness- cost trade-offs, contextualized within the broader research on evaluating perturbation robustness.
The fundamental challenge in this domain lies in the inherent trade-offs between robustness gains and the costs required to achieve them. As noted in research on algorithmic recourse, methods often achieve either low implementation costs or robustness to small perturbations, but rarely both due to the inherent conflicts between these objectives [65]. Similarly, biological systems exhibit robustness-fragility trade-offs where systems optimized for robustness against specific perturbations often become fragile against unexpected perturbations [66]. Understanding these trade-offs is essential for researchers selecting architectures for practical applications.
Comparative Analysis of Network Architectures
Quantitative Performance Comparison
The following table summarizes experimental results from fair comparative studies evaluating different architectural approaches under standardized conditions, with a focus on their robustness-performance characteristics and implementation considerations.
Table 1: Comparative Performance of Multi-Omics Integration Architectures for Drug Response Prediction
| Architecture | Integration Type | Mean Rank (AUROC) | Mean Rank (AUPRC) | Robustness Characteristics | Implementation Cost |
|---|---|---|---|---|---|
| Super.FELT | Intermediate | 2.43 | 2.86 (CV) | High regularization via triplet loss | High (complex architecture) |
| Omics Stacking | Intermediate/Late Hybrid | 2.86 | 2.43 (External) | Best external test performance | Moderate |
| MOLI | Intermediate | 3.29 | 3.00 | Triplet loss regularization | Moderate |
| MOMA | Intermediate | 4.43 | 4.57 | Moderate robustness | Moderate |
| OmiEmbed | Intermediate | 4.57 | 4.29 | VAE regularization struggles with distribution shift | High |
| PCA | Early | 6.14 | 5.71 | Low overfitting but poor performance | Low |
| Early Integration | Early | 5.71 | 6.14 | Vulnerable to input perturbations | Low |
Note: Performance ranks are from cross-validation on drug response datasets (lower rank indicates better performance). CV = Cross-Validation, External = External Test Set. Data sourced from [67].
Architectures employing triplet loss regularization (Super.FELT, MOLI, Omics Stacking) demonstrated superior robustness characteristics in cross-validation settings, with Super.FELT achieving the highest consistency in cross-validation scenarios [67]. However, the hybrid Omics Stacking approach, which combines intermediate and late integration strategies, exhibited the strongest performance on external test sets—a key indicator of real-world robustness when facing data distribution shifts [67].
The comparison reveals a clear cost-performance trade-off: while early integration methods like simple concatenation offer low implementation costs, they consistently deliver the lowest predictive performance and are highly vulnerable to input perturbations [67]. In contrast, more complex architectures with intermediate integration and regularization mechanisms achieve superior robustness but require significantly greater computational resources and expertise to implement and optimize.
Probabilistic Robustness Frameworks
Beyond architectural comparisons, emerging probabilistic frameworks offer novel approaches to quantifying and enforcing robustness. The Tower Robustness framework employs hypothesis testing to provide statistical guarantees on robustness estimates, addressing the significant trade-offs between computational cost and measurement precision that plague existing assessment methods [64] [68]. This approach enables more rigorous and efficient pre-deployment assessments, which is particularly valuable in safety-critical applications.
Similarly, the PROBE (Probabilistically ROBust rEcourse) framework introduces a probabilistic perspective on robustness, enabling users to explicitly manage the trade-off between recourse costs and robustness by selecting their desired invalidation rate probability [65]. This formalization acknowledges that perfect robustness is often impractical and provides mechanisms to navigate the cost-robustness trade-off space systematically.
Experimental Protocols for Robustness Assessment
Standardized Evaluation Methodology
To ensure fair comparisons across architectures, researchers should adopt standardized evaluation protocols that control for confounding variables:
Data Partitioning: Implement stratified cross-validation with fixed random seeds to ensure reproducible splits. Include external test sets from different distributions (e.g., different experimental conditions or patient populations) to assess generalization [67].
Hyperparameter Optimization: Utilize consistent optimization budgets across compared methods, with appropriate search spaces defined for each architectural type. Bayesian optimization with fixed computational limits ensures equitable comparison [67].
Perturbation Models: Systematically introduce perturbations during testing, including input noise, adversarial attacks, and feature missingness, to quantify robustness degradation. For graph neural networks, specifically evaluate against graph perturbation attacks that modify edge structures [69].
Performance Metrics: Report both area under receiver operating characteristic (AUROC) and area under precision-recall curve (AUPRC) metrics, as they provide complementary insights, particularly for imbalanced datasets common in biological applications [67].
Tower Robustness Assessment Protocol
The Tower Robustness framework introduces a statistically rigorous methodology for robustness assessment [64]:
Hypothesis Formulation: Define null and alternative hypotheses regarding model robustness based on application requirements.
Perturbation Generation: Create controlled perturbation sets that simulate realistic input variations while maintaining perceptual similarity to original inputs.
Statistical Testing: Employ exact statistical methods to quantify the probability of model failure under perturbations, providing confidence bounds on robustness estimates.
Cost-Bounded Analysis: Evaluate robustness under implementation constraints, recognizing that perfect robustness is theoretically impossible and practically limited by resource constraints.
This methodology addresses critical limitations of conventional robustness assessments, which often rely on approximations that risk overlooking rare but critical adversarial instances [64].
Research Reagent Solutions
Table 2: Essential Experimental Resources for Robustness Evaluation
| Resource Category | Specific Tools | Function in Robustness Research |
|---|---|---|
| Benchmark Datasets | NetBench [70], Multi-omics Drug Response [67] | Standardized evaluation across diverse tasks and data types |
| Robustness Frameworks | Tower Robustness [64], XGNNCert [69], PROBE [65] | Formal robustness guarantees and assessment methodologies |
| Architecture Implementations | Super.FELT, MOLI, OmiEmbed, MOMA [67] | Reference implementations for multi-omics integration |
| Evaluation Metrics | AUROC, AUPRC, Robustness Invalidation Rates [67] [65] | Quantification of performance and robustness characteristics |
Architectural Decision Framework
Visualization of Robustness-Cost Trade-offs
The following diagram illustrates the conceptual relationship between implementation costs and robustness gains across different architectural paradigms, highlighting the efficiency frontier where optimal trade-offs occur:
Diagram 1: Architecture trade-offs on efficiency frontier.
Experimental Workflow for Robustness Assessment
The diagram below outlines a standardized experimental workflow for conducting fair robustness comparisons across network architectures:
Diagram 2: Experimental workflow for robustness assessment.
This comparison guide demonstrates that selecting network architectures for robustness-sensitive applications requires careful consideration of the trade-offs between robustness gains and implementation costs. Intermediate integration architectures with appropriate regularization mechanisms, particularly those employing triplet loss, consistently achieve superior robustness characteristics, though at increased implementation complexity [67].
Emerging probabilistic frameworks like Tower Robustness and PROBE offer promising approaches to quantifying and enforcing robustness with statistical guarantees, potentially overcoming the significant cost-precision trade-offs that limit conventional assessment methods [64] [65]. For researchers and drug development professionals, adopting standardized evaluation protocols and considering the specific deployment context—whether cross-validation stability or external test performance is prioritized—is essential for selecting appropriately balanced architectural solutions.
The fundamental insight across these studies is that robustness rarely comes without costs, but intelligent architectural choices and assessment methodologies can optimize the trade-off space, enabling sufficient robustness for practical applications without prohibitive implementation overhead.
Addressing Data Quality and Integration Barriers for Robust AI in Pharmaceutical R&D
The integration of Artificial Intelligence (AI) into pharmaceutical research and development (R&D) represents a paradigm shift with the potential to revolutionize drug discovery, reduce development timelines, and deliver life-saving therapies to patients more efficiently. AI is projected to generate between $350 billion and $410 billion annually for the pharmaceutical sector by 2025, with R&D offering the largest value opportunity (30-45%) [71] [72]. This transformative potential, however, is critically dependent on a fundamental prerequisite: high-quality, well-integrated data. AI models are only as powerful as the data behind them, and poor data quality can delay development, approvals, and the delivery of essential treatments [71].
The pharmaceutical R&D data landscape is inherently complex, spanning diverse modalities—including omics, imaging, clinical, and sensor data—generated by disparate systems and teams with unique formats and standards [71]. This environment creates significant barriers to achieving robust AI. Robustness, defined as the ability of a machine learning model to maintain performance against various perturbations and variations, is a core principle of trustworthy AI but remains challenging to achieve in practice [73] [74]. This guide objectively compares how different data management and AI modeling approaches impact robustness, providing researchers and drug development professionals with a framework to evaluate and enhance their AI strategies. The central thesis is that overcoming data quality and integration barriers is not merely a technical prerequisite but a strategic imperative for deploying reliable, robust AI that can accelerate pharmaceutical innovation.
Data Quality as a Strategic Asset in Pharma R&D
The Criticality of FAIR Data Principles
In pharmaceutical R&D, data should be treated not as a by-product but as a strategic asset. This perspective necessitates adherence to the FAIR principles, making data Findable, Accessible, Interoperable, and Reusable [71]. FAIR data serves as the essential foundation for deploying trusted AI models that perform as intended. The tangible benefits of high-quality, FAIR data for AI-driven R&D are multifold:
- Higher Performing Models: Accurate, consistent, and well-labelled data is crucial for training AI models that deliver reliable predictions. For instance, AI-driven compound screening relies on harmonized assay data from multiple labs to predict toxicity and efficacy with higher precision [71].
- Faster Discovery Cycles: Complete, timely, and reliable datasets streamline data preparation, enabling quicker signal identification and focused research on the most promising leads. Investments in data quality have been linked to a 30% greater cost efficiency in R&D operations [71].
- Improved Reproducibility: Contextualized, standardised, and accessible data facilitates cross-team and institutional validation of findings, a cornerstone of scientific progress [71].
- Regulatory Confidence: Robust data governance that meets regulatory requirements ensures compliance and traceability, thereby increasing trust in AI-driven outputs submitted to agencies like the FDA [71].
Common Data Quality Challenges and Their Impact
Despite its importance, achieving data quality in R&D is far from simple. The table below summarizes common data pain points and their direct consequences on AI robustness and R&D efficiency.
Table 1: Common Data Quality Challenges in Pharmaceutical R&D and Their Impacts
| Data Challenge | Description | Impact on AI Robustness and R&D Efficiency |
|---|---|---|
| Inconsistent Data Capture [71] | Manual processes leading to inconsistent data entry, errors (e.g., varied annotations, unit discrepancies). | Compromises data reliability, introduces biases, and reduces model accuracy and generalizability. |
| Fragmented Data Landscape [71] | Data scattered across disparate systems (e.g., local databases, bespoke LIMS, disconnected wet/dry labs). | Leads to inconsistencies, compromises end-to-end integrity, and limits comprehensive cross-study analysis. |
| Inconsistent Data Definitions [71] | Variations in terminology and coding schemes (e.g., CDISC vs. custom schemas). | Requires significant harmonisation effort, hinders data reuse, and can lead to model misinterpretation. |
| Missing Metadata [71] | Lack of experimental context (e.g., the exact version of an experimental protocol). | Causes misinterpretation in data quality and insight generation, making results difficult to reproduce. |
| Measurement Variability [71] | Difficulties in reconciling results from different instruments or labs without standardized processes. | Introduces noise and confounding variables, negatively affecting model stability and prediction reliability. |
A Framework for Robust AI in Pharmaceutical Applications
Concepts of Robustness for Machine Learning
The robustness of a machine learning model is not a monolithic concept but an umbrella term encompassing resilience to different types of perturbations. A comprehensive scoping review identified eight general concepts of robustness relevant to healthcare and pharmaceutical AI, which are summarized in the table below [73]. Understanding these concepts is vital for developing and validating models that perform reliably in real-world settings.
Table 2: Eight Key Concepts of Machine Learning Model Robustness
| Robustness Concept | Description | Common Mitigation Strategies |
|---|---|---|
| Input Perturbations and Alterations [73] | Model's stability in the face of noise, distortions, or variations in input data (e.g., image noise, sensor drift). | Data augmentation, adversarial training, input normalization. |
| Adversarial Attacks [73] [74] | Resistance to maliciously designed inputs intended to deceive the model. | Adversarial training, defensive distillation, input preprocessing. |
| External Data and Domain Shift [73] | Performance consistency when applied to data from new environments, populations, or institutions not seen during training. | Domain adaptation, transfer learning, rigorous external validation. |
| Missing Data [73] | Ability to handle datasets with missing values without significant performance degradation. | Imputation techniques, model architectures designed for incomplete data. |
| Label Noise [73] | Resilience to errors in the training data labels (ground truth). | Label cleaning algorithms, robust loss functions. |
| Model Specification and Learning [73] | Sensitivity to choices in model architecture, hyperparameters, and learning algorithms. | Hyperparameter optimization, cross-validation, ensemble methods. |
| Feature Extraction and Selection [73] | Stability of model performance concerning the features chosen to represent the data. | Regularization, stable feature selection algorithms. |
| Imbalanced Data [73] | Ability to learn effectively from datasets where classes of interest are underrepresented. | Resampling techniques, cost-sensitive learning, synthetic data generation. |
The focus on these robustness concepts varies significantly across data types. For example, robustness to adversarial attacks is primarily tackled in image-based applications, while robustness to missing data is most frequently addressed with clinical data [73]. This highlights the need for a tailored approach to robustness based on the specific data modality and application.
Factors Influencing Deep Learning Model Robustness
For deep learning models, which are increasingly prevalent in medical diagnostics and drug discovery, robustness is influenced by several key factors [74]:
- Quality and Quantity of Data: The robustness of a model is significantly influenced by the quality and volume of the data used in its training. Large and diverse datasets help models generalize better [74].
- Model Architecture: Striking a balance between complexity and simplicity is crucial. Overly complex models may overfit, while overly simple ones may underfit [74].
- Hyperparameters: The optimal setting of hyperparameters (e.g., learning rate, batch size, regularization) is key to enhancing both performance and robustness [74].
- Interpretability: Models that are more interpretable can help identify potential biases or errors, thereby improving robustness and trustworthiness [74].
Experimental Protocols for Evaluating Robustness
To ensure AI models are robust and trustworthy, rigorous and standardized experimental validation is required. The following protocols provide a framework for assessing model robustness against critical barriers.
Protocol 1: Evaluating Robustness to Data Quality Issues (Domain Shift)
This protocol tests a model's performance when deployed on data from a new clinical site or population, a common challenge in multi-center trials.
Objective: To quantify model performance degradation due to domain shift between training and deployment environments. Datasets:
- Source Domain: A curated, high-quality dataset (e.g., clinical images from a primary research hospital).
- Target Domain: A dataset from a different source (e.g., images from a community hospital using different equipment or protocols). Methodology:
- Model Training: Train the model to be evaluated on the training split of the Source Domain dataset.
- Baseline Validation: Evaluate the trained model on the test split of the Source Domain dataset to establish a baseline performance.
- Domain Shift Test: Evaluate the same model, without any retraining, on the entire Target Domain dataset.
- Performance Comparison: Compare performance metrics (e.g., accuracy, AUC, F1-score) between the baseline validation and the domain shift test. A significant drop indicates low robustness to domain shift. Metrics:
- Primary: Change in Area Under the Curve (ΔAUC) and Change in F1-Score (ΔF1).
- Secondary: Accuracy, Precision, Recall.
The workflow for this experimental protocol is systematic and can be visualized as follows:
Protocol 2: Evaluating Robustness to Adversarial Attacks
This protocol assesses the vulnerability of a model to intentional, malicious inputs, which is a critical security concern.
Objective: To measure model performance degradation under various adversarial attack scenarios. Datasets: A held-out test set of clean data (e.g., molecular structures or medical images). Methodology:
- Baseline Performance: Evaluate the model on the clean test set to establish baseline metrics.
- Adversarial Example Generation: Use established algorithms (e.g., Projected Gradient Descent - PGD, Fast Gradient Sign Method - FGSM) to generate adversarial examples from the clean test set.
- Adversarial Performance: Evaluate the model's performance on the generated adversarial examples.
- Robustness Quantification: Calculate the performance drop. Optionally, test the efficacy of defense mechanisms like adversarial training by repeating the evaluation on a model that has been trained with adversarial examples. Metrics:
- Primary: Adversarial Accuracy (accuracy on adversarial examples), Robust Accuracy (accuracy after defense).
- Secondary: The success rate of the attack.
Quantitative Comparison of Model Robustness
The following table synthesizes hypothetical experimental data, representative of real-world studies [73] [74], comparing the robustness of different AI model architectures against the challenges described above.
Table 3: Comparative Robustness of AI Model Architectures to Data and Security Perturbations
| Model Architecture | Baseline AUC (Clean Data) | AUC under Domain Shift (Δ) | Accuracy on Adversarial Examples | Robustness to Missing Data (% Performance Drop) | Interpretability Score (1-5, 5=Best) |
|---|---|---|---|---|---|
| Deep Neural Network (DNN) | 0.95 | 0.75 (Δ -0.20) | 45% | 28% | 2 |
| Random Forest (RF) | 0.93 | 0.85 (Δ -0.08) | 75% | 15% | 4 |
| Convolutional Neural Network (CNN) with Adversarial Training | 0.94 | 0.82 (Δ -0.12) | 90% | 22% | 2 |
| Logistic Regression (LR) | 0.89 | 0.87 (Δ -0.02) | 88% | 10% | 5 |
Analysis of Results:
- Deep Neural Networks (DNNs) show high baseline performance but are often the most vulnerable to domain shift and adversarial attacks, suffering the largest performance drops. Their interpretability is also low.
- Random Forest (RF) models demonstrate strong inherent robustness to domain shift and adversarial examples, with good interpretability, making them a reliable choice for many applications.
- CNNs with Adversarial Training show that specific robustness-enhancing techniques can effectively mitigate certain threats, such as adversarial attacks, at a potential cost to performance on clean data and interpretability.
- Logistic Regression (LR) exhibits the smallest performance drop from domain shift and missing data, highlighting the robustness of simpler models, albeit often with a lower baseline performance ceiling.
Building and evaluating robust AI models requires a suite of computational tools and data resources. The following table details key solutions used in the field.
Table 4: Key Research Reagent Solutions for Robust AI Development
| Tool/Resource Name | Type | Primary Function in Robust AI Research |
|---|---|---|
| TensorFlow Privacy [74] | Software Library | Provides mechanisms for training models with differential privacy, enhancing data confidentiality and protection against privacy attacks. |
| CleverHans [74] | Software Library | A framework for benchmarking model vulnerability to adversarial attacks and for developing new defense strategies. |
| AlphaFold [75] [72] | AI Model | Accurately predicts protein 3D structures from amino acid sequences, providing high-quality data for target identification and drug design. |
| Pharma.AI (Insilico Medicine) [72] [76] | AI Platform | An end-to-end platform that automates the drug discovery pipeline, from target identification to molecular generation. |
| FAIR Data Principles [71] | Framework | A set of guidelines for making data Findable, Accessible, Interoperable, and Reusable, forming the foundation for high-quality AI-ready data. |
| Adversarial Training [74] | Methodology | A technique that improves model robustness by including adversarial examples during the training process. |
The journey toward robust and trustworthy AI in pharmaceutical R&D is multifaceted, requiring a holistic strategy that integrates data management, model selection, and rigorous validation. The evidence indicates that no single model architecture is superior across all robustness dimensions; rather, the choice involves trade-offs between baseline performance, stability, and interpretability.
A recommended pathway involves prioritizing data quality and FAIR principles as a non-negotiable foundation, which directly influences model performance and reproducibility [71]. Researchers should then systematically evaluate robustness across multiple concepts, particularly domain shift and adversarial attacks, using standardized experimental protocols like those outlined above [73] [74]. Finally, embracing simplicity and interpretability where possible, and employing specialized tools for robustness enhancement where necessary, will build the trust required for the successful clinical deployment of AI [77].
By adopting this comprehensive approach, pharmaceutical companies and researchers can transform data from a challenging barrier into a strategic competitive asset, ultimately realizing the full promise of AI to deliver life-changing therapies to patients more efficiently and reliably.
Validation Frameworks and Comparative Analysis of Network Robustness Strategies
Robustness is a fundamental property of networked systems, reflecting their ability to maintain structural integrity and functional performance amidst component failures or malicious attacks [78]. In fields ranging from computer vision to biological network analysis, evaluating the robustness of different network architectures has become a critical research focus. This evaluation increasingly relies on benchmarking performance across both synthetic networks with planted ground truths and real-world networks exhibiting complex, natural topologies [79]. Synthetic networks enable controlled experimentation with precisely known community structures, while real-world networks provide authentic testbeds reflecting practical challenges. This guide systematically compares contemporary robustness benchmarking strategies, detailing their experimental methodologies, performance characteristics, and suitability for different research scenarios in network science and related disciplines.
Theoretical Foundations of Network Robustness
Defining Robustness in Networked Systems
Network robustness manifests differently across domains but consistently relates to system resilience under perturbation. In computer vision, robustness refers to deep neural networks maintaining performance despite image corruptions or adversarial attacks [80]. For complex networks, connectivity robustness denotes the capacity to uphold structural integrity despite node or edge failures [78]. This is often quantified by monitoring the size of the largest connected component (LCC) during sequential node or edge removal, calculated as ( Rn = \frac{1}{T} \sum{p=0}^{(T-1)/T} Gn(p) ), where ( Gn(p) ) represents the LCC size after proportion ( p ) of nodes are removed [78].
Key Robustness Metrics and Measures
Multiple metrics have been developed to evaluate network robustness from different perspectives. The ( R ) measure, adapted from percolation theory, assesses robustness against node attacks by computing the average LCC size during removal sequences [81]. Its counterpart ( R_l ) extends this evaluation to link attacks. Alternative approaches include:
- Topological statistics: Connectivity measures, average path length, and LCC size [78]
- Percolation theory methods: Critical node fractions triggering network collapse [78]
- Matrix spectra measurements: Spectral radius, algebraic connectivity, and natural connectivity [78]
- Flow-based metrics: Incorporating network flow properties beyond pure topology [78]
Each metric captures different robustness facets, with studies showing they are often sensitive to network changes, especially in initial versus optimized networks [82].
Synthetic Networks for Robustness Benchmarking
Generation Methodologies and Models
Synthetic networks provide controlled environments for robustness evaluation through generators that implant specific topological properties:
Table 1: Synthetic Network Generation Models
| Model | Key Characteristics | Typical Applications | Strengths |
|---|---|---|---|
| Stochastic Block Models (SBMs) | Produces networks with planted ground-truth clusters approximating input parameters from real networks [79] | Community detection evaluation, cluster connectivity analysis | Good fit to degree sequence, clustering coefficients, diameter [79] |
| LFR Generator | Generates networks with power-law degree distributions and community structure [79] | Testing community detection algorithms | Realistic heterogeneity in node degrees and community sizes |
| Artificial Benchmark for Community Detection (ABCD) | Creates random graphs with community structure and power-law distribution [79] | Community detection benchmarking | Scalable to large networks with adjustable parameters |
| nPSO | Nonuniform popularity similarity optimization model [79] | Embedding-based network analysis | Captures hierarchical and similarity-based connectivity patterns |
Addressing Synthetic Network Limitations
A significant limitation of standard synthetic generators, particularly SBMs, is the production of disconnected ground truth clusters, even when input parameters derive from connected real-world clusters [79]. The REalistic Cluster Connectivity Simulator (RECCS) addresses this by modifying SBM outputs to better approximate the edge connectivity of clusters in the original real-world network while preserving other statistical properties [79]. This two-step pipeline first enhances cluster connectivity in the synthetic clustered subnetwork, then reintegrates outlier nodes using strategies with varying randomness levels.
Real-World Networks for Robustness Validation
Network Diversity and Domain Specificity
Real-world networks provide essential validation for robustness strategies, with performance often domain-dependent:
Table 2: Real-World Network Categories for Robustness Evaluation
| Network Category | Key Characteristics | Perturbation Types | Evaluation Challenges |
|---|---|---|---|
| Infrastructure Networks (power grids, transportation) [81] | Engineered for reliability, often meshed topology | Random failures, targeted attacks, cascading failures [81] | Interdependencies, spatial constraints, multiple functionality measures |
| Biological Networks (protein-protein, neural) | Evolved robustness, complex topology-function relationships | Node deletion (gene knockout), edge disruption | Ground truth limitations, multiple scales of organization |
| Information Networks (WWW, social networks) [81] | Scale-free properties, rapid growth | Targeted attacks on hubs, content manipulation [81] | Dynamic topology, evolving attack strategies |
| Vision Networks (FM images, natural images) [80] | Specific noise profiles, morphological dependencies | Image corruptions, adversarial attacks [83] [80] | Domain shift between training and deployment environments |
Domain-Specific Robustness Challenges
Different network domains present unique robustness challenges. For instance, fluorescence microscopy (FM) images exhibit wider dynamic ranges, different noise properties, and more diffusive object boundaries compared to natural images [80]. Consequently, DNN models robust on natural images may collapse on FM images, with segmentation robustness highly dependent on object morphology [80]. Similarly, infrastructure networks must maintain functionality under both random failures and targeted attacks, requiring robustness optimization that preserves critical properties like shortest path length and communication efficiency [82].
Comparative Performance Analysis
Robustness Across Network Architectures
Benchmarking studies reveal significant performance variations across network architectures and domains:
Table 3: Performance Comparison Across Network Types and Perturbations
| Network Type | Test Environment | Key Performance Findings | Reference |
|---|---|---|---|
| Instance Segmentation Models | Synthetic corruptions, out-of-domain images | Group normalization enhances robustness against corruptions; batch normalization improves cross-dataset generalization | [84] |
| Computer Vision Models (CLIP, MiniGPT-4) | ImageNet-D (diffusion synthetic) | Accuracy reductions up to 60% on diffusion-generated images | [83] |
| Scale-free, Small-world, Random, Regular Networks | Link attack simulations (degree, betweenness, random) | Optimized networks for one attack type may be vulnerable to others; topology-dependent robustness patterns | [81] |
| CNN with SPP-net | Node/edge removal scenarios | Accurate robustness evaluation when test/train network types match; limited transferability across network types | [78] |
| DNN Segmentation Models | FM image corruptions and adversarial attacks | CNN-based models (e.g., SegNet) outperform Transformer/ResNet models on FM images; object morphology affects robustness | [80] |
Synthetic vs. Real-World Network Performance
The fidelity of synthetic networks significantly impacts robustness evaluation validity. ImageNet-D, utilizing diffusion models to generate images with diversified backgrounds, textures, and materials, causes accuracy drops up to 60% for state-of-the-art vision models including CLIP and MiniGPT-4 [83]. This demonstrates that diffusion-generated benchmarks can reveal vulnerabilities not apparent in traditional synthetic tests. Similarly, RECCS-modified SBMs better approximate real-world cluster connectivity while maintaining fidelity to other network statistics [79]. However, optimized robustness on synthetic networks may not translate to real-world performance, as synthetic environments cannot capture all practical constraints and functionality requirements [82].
Experimental Protocols and Methodologies
General Robustness Evaluation Framework
A standardized methodology for robustness benchmarking encompasses several key phases:
Diagram: Robustness evaluation workflow showing the parallel processing of synthetic and real-world networks.
Domain-Specific Evaluation Protocols
Computer Vision Networks: The robustness evaluation protocol for DNNs in semantic segmentation of fluorescence microscopy images involves:
- Dataset Curation: Synthesizing realistic FM images with precisely controlled corruptions or utilizing real FM images of different modalities [80]
- Corruption Application: Implementing diverse corruption types including noise, blurring, and contrast distortion at varying intensity levels [80]
- Adversarial Attacks: Applying attack methods like FGSM and PGD with carefully tuned parameters [80]
- Performance Measurement: Quantifying segmentation accuracy degradation across corruption types and levels
- Robustness Comparison: Comparing models to identify architecture choices conferring robustness [80]
Complex Network Robustness: For complex network architectures, a comprehensive evaluation involves:
- Attack Simulation: Implementing node and edge removal strategies including:
- Connectivity Monitoring: Tracking the size of the largest connected component throughout the removal process [78]
- Robustness Quantification: Calculating robustness values (( Rn ) or ( Rl )) from the attack curve [78] [81]
- Cross-Architecture Comparison: Evaluating performance across different network models including scale-free, small-world, random, and regular networks [81]
Essential Research Reagents and Tools
Computational Frameworks and Datasets
Table 4: Key Research Resources for Robustness Benchmarking
| Resource Category | Specific Tools/Datasets | Primary Function | Application Context |
|---|---|---|---|
| Synthetic Network Generators | graph-tool (SBM), LFR, ABCD, RECCS | Generate networks with controlled properties for controlled experimentation | Community detection evaluation, algorithm validation [79] |
| Robustness Benchmark Datasets | ImageNet-D, ImageNet-C, ImageNet-9 | Provide standardized corruption types and levels for vision models | Computer vision robustness testing [83] |
| Network Analysis Toolkits | Complex network libraries (varied) | Implement attack strategies, calculate robustness metrics, visualize results | Complex network robustness evaluation [78] [81] |
| Deep Learning Frameworks | PyTorch, TensorFlow | Train and evaluate DNN models under various corruptions and attacks | Vision model robustness assessment [80] |
This comparative analysis reveals that robust network performance depends critically on the alignment between evaluation methodologies and application contexts. Synthetic networks enable controlled, reproducible experiments but may not capture all real-world complexities, while real-world networks provide authentic testbeds but with limited ground truth. Effective robustness strategies therefore require validation across both environments. Cross-domain insights emerge, such as the generalization benefits of specific normalization techniques [84] and the universal trade-offs between accuracy and robustness [80]. Future robustness benchmarking should prioritize standardized evaluation protocols, domain-specific perturbation models, and synthetic networks that better approximate real-world topological and functional constraints. Researchers should select robustness strategies based not only on benchmark performance but also on alignment with their specific application requirements and constraint profiles.
The pursuit of robust artificial intelligence requires architectures that remain stable under perturbation. For researchers and drug development professionals, selecting the right model involves evaluating performance through core metrics: computational speedup, classification error rates, and fidelity to ground truth, which we frame as proximity to exhaustive search results. This guide objectively compares the performance of prominent network architectures—BERT, GPT, and LLaMA—by synthesizing experimental data on their robustness, providing a clear framework for application in sensitive fields like computational drug discovery.
Architectural Comparison: BERT, GPT, and LLaMA
The fundamental differences in architecture between BERT, GPT, and LLaMA dictate their respective strengths in comprehension versus generation, which in turn influences their robustness profiles [85] [86] [87].
- BERT (Bidirectional Encoder Representations from Transformers): An encoder-only model trained using Masked Language Modeling (MLM), which learns to predict randomly masked words in a sentence by considering the full bidirectional context [85] [86]. This makes it a specialist in deep language understanding.
- GPT (Generative Pre-trained Transformer): A decoder-only model trained on Causal Language Modeling (CLM), where it predicts the next word in a sequence using only the preceding words [85] [87]. This autoregressive nature makes it a powerhouse for text generation.
- LLaMA (Large Language Model Meta AI): Also a decoder-only model, LLaMA is designed for efficiency and performance, often achieving capabilities comparable to larger models through architectural refinements like Rotary Positional Embeddings (RoPE) and grouped query attention [85].
The following table summarizes their core architectural differences:
| Feature | BERT | GPT | LLaMA |
|---|---|---|---|
| Architecture | Encoder-Only [85] [87] | Decoder-Only [85] [87] | Decoder-Only [85] |
| Context Handling | Bidirectional [86] | Unidirectional/Causal [87] | Unidirectional/Causal [85] |
| Primary Training Objective | Masked Language Modeling (MLM) [86] [87] | Causal Language Modeling (CLM) [87] | Next-Token Prediction [85] |
| Core Strength | Comprehension, Classification [86] [88] | Text Generation, Conversation [85] [88] | Efficient & Powerful Generation [85] |
Comparative Performance and Robustness Metrics
Direct, head-to-head comparisons of BERT, GPT, and LLaMA on adversarial robustness are not fully captured in the provided search results. However, quantitative data from related experiments and performance benchmarks can inform our understanding of their behavior under specific conditions.
Reported Performance on Standard Tasks The table below summarizes typical performance characteristics based on standard benchmarks and common applications.
| Model | Typical Task Performance (Standard Benchmarks) | Robustness to Adversarial Perturbations (Experimental Data) |
|---|---|---|
| BERT | Excels in tasks like question answering and sentiment analysis [88]. High accuracy on NLU benchmarks [85]. | Inherently non-robust to small perturbations due to structure-breaking mappings in standard training [89]. |
| GPT-4 | Superior performance in creative text generation and conversation [88]. | Can be fooled by adversarial manipulations; may generate factually incorrect "hallucinations" under perturbation [88]. |
| LLaMA | High capability in text generation, with strong performance at reduced parameter counts [85]. | Specific quantitative robustness data not available in search results. Its efficiency focus may influence robustness trade-offs. |
| Isometric Networks | Maintains high accuracy on MNIST and CIFAR10 [89]. | Improves robustness to FGSM attacks by enforcing distance-preserving, isometric representations [89]. |
Experimental Protocols for Robustness Evaluation
A key methodology for evaluating robustness involves testing models against adversarial attacks and measuring the fidelity of their internal representations.
1. Protocol: Adversarial Attack using the Fast Gradient Sign Method (FGSM) This is a common technique to assess model vulnerability [89].
- Objective: To evaluate a model's resilience to small, worst-case perturbations on the input data.
- Methodology:
- Input Sample: A clean, correctly classified input image (e.g., from CIFAR-10) is selected.
- Gradient Calculation: The gradient of the training loss with respect to the input image is computed.
- Perturbation Generation: A small perturbation is generated in the direction of the gradient sign, designed to maximize loss:
perturbation = epsilon * sign(gradient). - Adversarial Example Creation: The perturbation is added to the original image:
adversarial_image = original_image + perturbation. - Evaluation: The model's classification accuracy is measured on these newly generated adversarial examples. A robust model will maintain high accuracy.
2. Protocol: Enforcing and Verifying Isometric Representations This protocol, based on recent research, aims to build robustness directly into the network architecture [89].
- Objective: To train a network that preserves the metric structure of input data within each class, thereby improving its robustness.
- Methodology:
- Network Modification: A standard classification network (e.g., CNN) is augmented with Locally Isometric Layers (LILs).
- Loss Function: The network is trained using a composite loss function that combines standard cross-entropy with a novel isometric term [89]:
ℒ = α * ℒ_CSE + β * ℒ_ISOwhereℒ_ISO = || G ⊙ D_M - G ⊙ D_Φ ||²_F. - Distance Matrices:
D_Mis the distance matrix between input data points, andD_Φis the distance matrix between their corresponding network output representations [89]. - Indexing Matrix (G): This matrix applies the isometry constraint within each class, ensuring that the local geometry of the data manifold for "cats" or "dogs" is preserved in the feature space [89].
- Verification: The success of the training is verified by demonstrating improved robustness to FGSM attacks and showing that the learned mapping is isometric everywhere except near the decision boundaries [89].
Diagram 1: Isometric Representation Learning. The network Φ is trained to preserve input distances (dₘ) in its output space (d_Φ) via a dedicated isometry loss, leading to more robust features.
Diagram 2: Experimental Robustness Evaluation. An adversarial example causes a standard model to misclassify, while a model trained with isometric constraints maintains correct classification due to its stabilized feature space.
The Scientist's Toolkit: Research Reagents & Materials
This table details key computational "reagents" and resources essential for conducting robustness research in this field.
| Research Reagent / Material | Function in Experimentation |
|---|---|
| Locally Isometric Layers (LILs) | A network architectural component that enforces distance-preserving (isometric) mappings within data classes, directly improving robustness to input perturbations [89]. |
| Isometric Regularization Term (ℒ_ISO) | A component of the loss function that minimizes the difference between input and output distance matrices, guiding the network to learn structurally faithful representations [89]. |
| Fast Gradient Sign Method (FGSM) | A standard algorithm for generating adversarial examples to stress-test and quantify the vulnerability of machine learning models [89]. |
| Bidirectional Transformer Encoder | The core architectural backbone of BERT, enabling deep, contextual understanding of text by processing words in relation to all other words in a sentence [86] [87]. |
| Autoregressive Transformer Decoder | The core architectural backbone of GPT and LLaMA, enabling the generation of coherent text sequences by predicting the next token based on all previous tokens [85] [87]. |
| Cross-Entropy Loss (ℒ_CSE) | The standard loss function for training classification models, which focuses on maximizing the probability of the correct label but does not inherently promote robustness [89]. |
The quest for robust network architectures presents a clear trade-off. Traditional models like BERT, GPT, and LLaMA excel in their specialized domains of comprehension and generation but often lack inherent robustness to adversarial perturbations. Emerging research demonstrates that architectural interventions, such as enforcing isometric representations, provide a promising path toward models that are both accurate and stable. For researchers in drug development and scientific fields, where reliability is paramount, prioritizing these architecturally robust designs and rigorously evaluating them using the outlined metrics and protocols is a critical step toward building trustworthy AI systems.
The integration of artificial intelligence (AI) into drug discovery represents a paradigm shift, promising to compress development timelines from years to months and significantly reduce costs [90]. However, the translation of AI-discovered candidates into clinically successful drugs hinges on a critical, yet often underexplored, factor: model robustness. Within the context of evaluating the robustness of different network architectures to perturbation, this guide provides a comparative analysis of how leading AI-driven drug discovery platforms architect their models to withstand biological and chemical variability.
Robustness here refers to a model's ability to maintain predictive accuracy and generate reliable, translatable results when confronted with perturbations. These perturbations can arise from inherent biological noise, shifts in chemical space during scaffold hopping, or variations in experimental data used for training and validation. This case study objectively compares the performance of prominent platforms and the underlying architectures they employ, framing the analysis with experimental data on their resilience to such challenges.
Leading Platforms and Their Architectural Approaches
AI-driven drug discovery encompasses a spectrum of approaches, from generative molecular design to target identification. The robustness of these platforms is fundamentally tied to their core computational architectures. The following table summarizes the key platforms and their primary technological underpinnings.
Table 1: Leading AI-Driven Drug Discovery Platforms and Their Core Architectures
| Platform/Company | Primary AI Architecture | Core Drug Discovery Focus | Key Differentiator |
|---|---|---|---|
| Exscientia [90] | Generative AI (Deep Learning), "Centaur Chemist" | Small-molecule design, lead optimization | Closed-loop design-make-test-learn cycle integrated with automated robotics. |
| Insilico Medicine [90] | Generative Deep Learning Models | Target identification, de novo molecular design | End-to-end AI platform from target discovery to candidate generation. |
| Recursion [90] | Phenotypic Screening, AI-based Image Analysis | Phenomics, target-agnostic drug discovery | Massive-scale cellular phenotyping to infer biological activity. |
| BenevolentAI [90] | Knowledge Graphs, Machine Learning | Target identification, patient stratification | Leverages a vast repository of scientific literature and clinical data. |
| Schrödinger [90] | Physics-based Simulations, Machine Learning | Molecular modeling, free energy calculations | Combines first-principles physics with ML for high-accuracy predictions. |
A key differentiator in architectural robustness is the approach to molecular representation, which is the method of converting a chemical structure into a format computable by an algorithm. Traditional methods like Simplified Molecular-Input Line-Entry System (SMILES) strings or molecular fingerprints have limitations in capturing complex structural relationships [91]. Modern, more robust approaches include:
- Graph Neural Networks (GNNs): These operate directly on the molecular graph structure, explicitly modeling atoms (nodes) and bonds (edges). This allows them to capture intrinsic topological information, making them naturally robust to tasks like scaffold hopping [91] [92].
- Transformer-based Models: These treat molecules as sequences (e.g., of SMILES tokens) and use self-attention mechanisms to weigh the importance of different parts of the sequence. They excel at capturing long-range dependencies but may require more data to learn structural invariances [91] [93].
- Hybrid and Graph Transformer Models: Emerging architectures combine the strengths of GNNs and Transformers. Graph Transformers (GTs) integrate structural information directly into the attention mechanism, helping to overcome classic GNN limitations like over-smoothing and enabling better modeling of long-range interactions within a molecule [92].
Comparative Robustness and Performance Benchmarking
Evaluating the robustness of these architectures involves rigorous benchmarking on specific tasks, such as Drug-Target Interaction (DTI) prediction and scaffold hopping. Performance metrics must account not only for accuracy but also for generalization to novel data distributions.
Benchmarking Drug-Target Interaction (DTI) Prediction
A comprehensive benchmark study, GTB-DTI, directly compared explicit (GNN-based) and implicit (Transformer-based) structure learning methods for DTI prediction from a drug structure perspective [93]. The study evaluated models on multiple datasets for both classification and regression tasks, providing key insights into their effectiveness and efficiency.
Table 2: Benchmarking Performance of GNNs vs. Transformers on DTI Prediction [93]
| Model Architecture | Representation | Key Strength | Notable Performance Insight | Robustness Consideration |
|---|---|---|---|---|
| GNN-based (Explicit) | Molecular Graph | Directly captures molecular topology and local chemical environments. | Excellent performance on targets with strong dependence on 3D structure and local atom interactions. | Naturally robust to perturbations that preserve molecular connectivity. |
| Transformer-based (Implicit) | SMILES String | Captures long-range dependencies and contextual information in sequences. | Can outperform GNNs on certain datasets, especially when pre-trained on large corpora of chemical strings. | Performance can be sensitive to tokenization; may struggle with structural nuances not evident in SMILES. |
| Model Combos (Hybrid) | Graph & Sequence | Leverages both topological and contextual information. | Achieved state-of-the-art (SOTA) regression results and performed similarly to SOTA in classifications. | Offers the most robust performance across diverse datasets and task types, mitigating individual model weaknesses. |
The benchmark concluded that neither GNNs nor Transformers are universally superior; their performance is highly dataset-dependent [93]. This finding underscores the importance of architectural choice based on the specific biological context and the nature of expected perturbations. The most robust solution identified was a hybrid "model combo," which delivered SOTA performance with cost-effective memory usage and faster convergence [93].
Robustness in Scaffold Hopping via Molecular Representation
Scaffold hopping—identifying novel core structures with similar biological activity—is a critical test for an AI model's robustness to chemical perturbation. The ability to navigate vast chemical spaces and suggest viable candidates with different scaffolds is vital for overcoming issues like toxicity and patent constraints [91].
Modern AI-driven molecular representation methods have dramatically improved scaffold hopping capabilities. Deep learning models, particularly Graph Neural Networks (GNNs) and Variational Autoencoders (VAEs), learn continuous, high-dimensional feature embeddings that capture nuanced structure-activity relationships [91]. These models demonstrate robustness by mapping structurally diverse molecules with similar biological effects to proximate locations in a latent space, enabling the discovery of novel scaffolds that traditional fingerprint-based methods would miss.
Table 3: Architectural Robustness in Scaffold Hopping Applications
| Molecular Representation | Architecture | Impact on Scaffold Hopping Robustness | Experimental Support |
|---|---|---|---|
| Graph-based (GNNs) | Explicit Structure Learning | High robustness; directly models the molecular scaffold, enabling identification of topologically distinct but functionally similar compounds. | Models can generate or identify new scaffolds absent from existing chemical libraries by learning the essential pharmacophores from graph data [91]. |
| Language Model-based (Transformers) | Implicit Structure Learning | Moderate robustness; relies on learning patterns from SMILES strings. Can propose novel structures but may generate invalid or unstable molecules. | Effective in de novo molecular generation, but success depends on the quality and breadth of training data to ensure chemical validity and synthesizability [91]. |
| Multimodal & Contrastive Learning | Hybrid/Ensemble | Potentially high robustness; learns aligned representations from multiple data views (e.g., structure, bioassay data), improving generalization. | By enforcing similarity constraints between different representations of the same molecular "idea," these models become more invariant to irrelevant structural perturbations [91]. |
Experimental Protocols for Robustness Evaluation
To empirically evaluate the robustness of different network architectures, researchers employ standardized experimental protocols and benchmarks. Below is a detailed methodology for a key robustness test.
Detailed Protocol: Benchmarking DTI Model Generalization
This protocol is adapted from large-scale benchmarking studies to assess how well models generalize under perturbation [93].
1. Objective: To evaluate the robustness of different drug encoding architectures (GNNs vs. Transformers) to perturbations in the chemical and target space.
2. Datasets:
- Use multiple, curated DTI datasets (e.g., KIBA, BindingDB) that include both binary interaction labels and continuous binding affinity values.
- Perturbation Strategy: Implement a scaffold-split, where molecules in the test set have core scaffolds not present in the training set. This directly tests robustness to significant chemical perturbations.
3. Models for Comparison:
- Explicit Structure Encoders: Select representative GNN models (e.g., Graph Convolutional Network (GCN), Graph Attention Network (GAT)).
- Implicit Structure Encoders: Select Transformer-based models trained on SMILES strings (e.g., MolTrans).
- Baseline: Include a traditional descriptor-based model (e.g., using ECFP fingerprints with a Random Forest).
4. Training and Evaluation:
- Hyperparameter Tuning: Use a consistent, rigorous hyperparameter optimization strategy (e.g., Bayesian optimization) for all models on a validation set derived from the training data to ensure a fair comparison.
- Evaluation Metrics:
- Primary: Area Under the Precision-Recall Curve (AUPRC) for classification; Concordance Index (CI) and Mean Squared Error (MSE) for regression.
- Robustness-Specific: Measure the performance drop (ΔMetric) between a random split and the scaffold split. A smaller drop indicates greater robustness.
5. Analysis:
- Perform statistical significance testing (e.g., paired t-test) on the results across multiple runs with different random seeds.
- Analyze the chemical space of failed predictions to identify specific architectural blind spots.
The Scientist's Toolkit: Essential Research Reagents and Materials
The experimental workflows for developing and evaluating robust AI models in drug discovery rely on a suite of computational "reagents" and resources.
Table 4: Essential Research Reagent Solutions for AI Robustness Evaluation
| Category | Item/Resource | Function in Robustness Evaluation |
|---|---|---|
| Datasets & Benchmarks | GTB-DTI Benchmark [93] | Provides a standardized framework for fair comparison of DTI models, including code, datasets, and evaluation protocols. |
| CASP (Critical Assessment of Structure Prediction) | The gold-standard blind test for evaluating the robustness of protein structure prediction tools like AlphaFold [94]. | |
| Molecular Representations | Extended-Connectivity Fingerprints (ECFPs) [91] | A traditional fingerprint method used as a baseline to compare the robustness of modern deep learning representations. |
| Graph Representations (e.g., via RDKit) | Converts SMILES strings into molecular graphs for GNN-based models, enabling explicit structure learning. | |
| Software & Libraries | Graph Neural Network Libraries (e.g., PyTorch Geometric, DGL) | Essential for implementing and training explicit structure encoders (GNNs) for tasks like DTI and scaffold hopping. |
| Transformer Libraries (e.g., Hugging Face, Transformers) | Provides pre-trained models and frameworks for implementing and adapting sequence-based (SMILES) models for drug discovery. | |
| Validation Tools | Cross-Validation (Scaffold-Split) | A critical data-splitting technique to evaluate model performance and generalization on novel chemical scaffolds. |
| Explainability AI (XAI) Tools (e.g., SALiency maps, Attention visualization) | Helps interpret model predictions and identify if robust performance is based on scientifically plausible features or spurious correlations. |
The robustness of AI-driven drug discovery platforms is not a monolithic property but a multifaceted characteristic deeply intertwined with underlying network architectures. This comparative analysis reveals that:
- GNNs offer inherent robustness for tasks dependent on molecular topology, such as scaffold hopping.
- Transformers excel where long-range context within a sequence is critical, though their robustness can be sensitive to data representation.
- Hybrid and Graph Transformer models are emerging as the most promising path forward, combining the strengths of different architectures to create more resilient and generalizable AI systems for drug discovery [93] [92].
The ongoing evolution of molecular representation methods and the establishment of rigorous, standardized benchmarks like GTB-DTI are crucial for the field. They enable a clearer understanding of how different architectures respond to biological and chemical perturbations, ultimately guiding the development of more reliable AI platforms that can consistently translate computational predictions into successful clinical outcomes.
The increasing complexity of modern networked systems—from interacting proteins in drug discovery to temporal social networks—demands rigorous mathematical frameworks for quantifying organizational changes over time. Evaluating the robustness of different network architectures to perturbations represents a foundational challenge in network science, requiring metrics that can distinguish meaningful structural evolution from insignificant fluctuations. The Resistance Perturbation Distance (RPD) has emerged as a powerful metric specifically designed for this purpose, enabling researchers to quantify significant organizational changes between successive network states across multiple structural scales [95].
Unlike simpler similarity measures that may only capture local changes in edge composition, RPD operates by interpreting a network as an electrical circuit, where edges represent resistors and the effective resistance between nodes captures not just direct connections but all possible pathways between them. This fundamental insight allows RPD to detect changes occurring at different scales: from the local neighborhood of individual vertices to the global scale that quantifies connections between communities or clusters [95]. For researchers investigating the robustness of biological networks or the stability of pharmacological target systems, this multi-scale capability provides unprecedented analytical precision in tracking network evolution under perturbation.
Theoretical Foundations of Resistance Perturbation Distance
Mathematical Definition and Interpretation
The Resistance Perturbation Distance is grounded in spectral graph theory and electrical network interpretation. For a connected, undirected graph G = (V, E) with n nodes, the effective resistance R(i, j) between nodes i and j is defined as the potential difference between i and j when a unit current is injected at i and extracted at j. Mathematically, this can be computed using the Moore-Penrose pseudoinverse of the graph Laplacian matrix L [95] [96]:
R(i, j) = L⁺(i, i) + L⁺(j, j) - 2L⁺(i, j)
where L = D - A, with D being the degree matrix and A the adjacency matrix of the graph, and L⁺ denoting the pseudoinverse of L.
The Kirchhoff index Kf(G) of a graph provides a global summary of effective resistances, defined as the sum of effective resistances between all pairs of nodes [96]:
Kf(G) = Σ_{i
For two networks G₁ and G₂ defined on the same vertex set V, the Resistance Perturbation Distance d_RP(G₁, G₂) is defined as the Frobenius norm of the difference between their resistance matrices [95]:
dRP(G₁, G₂) = ||R{G₁} - R{G₂}||F
This formulation ensures that d_RP satisfies all metric axioms, making it a true mathematical distance rather than merely a similarity measure [95].
Multi-Scale Analysis Capabilities
A key advantage of RPD in robustness evaluation is its ability to capture structural changes at different organizational scales:
- Local scale: Sensitive to changes in immediate neighborhoods of vertices
- Intermediate scale: Captures alterations in community structures
- Global scale: Quantifies changes in overall network connectivity patterns
This multi-scale capability stems from the fact that effective resistance incorporates information about all possible paths between nodes, not just direct connections or shortest paths. When a network undergoes perturbation, RPD can identify whether changes are localized to specific regions or represent system-wide reorganization—a critical distinction for assessing architectural robustness [95].
Comparative Analysis of Network Similarity/Distance Metrics
Taxonomy of Graph Distance Measures
Graph similarity measures can be broadly categorized into several families based on their methodological approach [97]:
Table: Classification of Graph Distance Measures
| Category | Basis of Comparison | Example Measures | Invariant to Relabeling? |
|---|---|---|---|
| Local/Set-Based | Direct comparison of node/edge sets | Jaccard index, Graph Edit Distance, Vertex/Edge Overlap | No |
| Spectral | Graph spectrum comparison | λ-distance, Non-backtracking Spectral Distance, Quantum JS Divergence | Yes |
| Statistical | Empirical distribution comparison | Degree Distribution Distance, Communicability Sequence Entropy | Yes |
| Diffusion-Based | Graph diffusion processes | Graph Diffusion Distance, Resistance Perturbation Distance | Yes |
| Hybrid | Multiple structural aspects | D-measure, LD-measure, SLRIC-similarity | Varies |
Performance Comparison of Key Metrics
Comprehensive evaluation of 39 graph similarity measures reveals distinct performance characteristics across different network types and perturbation scenarios [97]:
Table: Comparative Performance of Selected Graph Distance Measures
| Distance Measure | Computational Complexity | Optimal Use Case | Scalability | Sensitivity to Perturbations | ||
|---|---|---|---|---|---|---|
| Resistance Perturbation Distance | O( | E | ) with randomized algorithms [95] | Multi-scale structural changes | Good for large sparse networks | High across local and global scales |
| Spectral Distances | O(n³) for eigendecomposition | Global structure changes | Poor for large networks | High for global changes, low for local | ||
| Graph Edit Distance | NP-hard in general | Graphs with known node correspondence | Poor | High for local changes | ||
| Jaccard Distance | O( | E | ) | Edge set comparison | Excellent | Only captures edge changes |
| D-measure | O(n³) | Combined local/global analysis | Poor | High across multiple scales |
The RPD demonstrates particular effectiveness because it satisfies the critical requirements for dynamic network analysis: computational efficiency through O(|E|) randomized approximation algorithms, mathematical rigor as a true metric, and multi-scale sensitivity to structural changes [95].
Experimental Validation and Protocols
Validation on Synthetic Networks
Experimental validation of RPD involves several carefully designed protocols using synthetic networks with known structural properties. The following workflow illustrates a typical experimental validation framework:
Experimental Validation Workflow for RPD
Synthetic Network Generation Protocol
Base Network Models: Generate initial networks using established models:
- Erdős-Rényi random graphs (G(n, p))
- Barabási-Albert scale-free networks (growth with preferential attachment)
- Stochastic Block Models (SBM) for community structures
Controlled Perturbation Application: Introduce structural changes at different scales:
- Local perturbations: Random edge additions/removals affecting <5% of nodes
- Community perturbations: Merge or split predefined communities in SBM
- Global perturbations: Alter degree distribution parameters in scale-free networks
Ground Truth Establishment: Define expected distance values based on perturbation magnitude for validation
Evaluation Metrics for Validation
- Detection Sensitivity: Ability to distinguish perturbed states from identical graphs
- Scale Specificity: Correlation between RPD values and perturbation types at different scales
- Computational Efficiency: Runtime scaling with network size |V| and |E|
Performance on Real-World Dynamic Networks
Application of RPD to real-world evolving networks demonstrates its practical utility in robustness evaluation:
Table: RPD Performance on Real Network Dynamics [95]
| Network Type | Structural Change | RPD Detection | Alternative Metrics | Advantage of RPD |
|---|---|---|---|---|
| Social Networks | Community merger | High sensitivity | Moderate by spectral methods | Better capture of multi-scale reorganization |
| Biological Networks | Targeted node removal | Precise localization | Variable performance | Identifies functional disruptions |
| Infrastructure Networks | Cascade failures | Early detection | Delayed detection | Anticipates system-wide impacts |
| Brain Connectomes | Functional reorganization | Multi-scale patterns | Limited to local or global | Links local changes to global integration |
The Scientist's Toolkit: Research Reagent Solutions
Implementing RPD analysis requires specific computational tools and theoretical frameworks:
Table: Essential Research Reagents for RPD Analysis
| Tool/Resource | Type | Function | Implementation Notes | ||
|---|---|---|---|---|---|
| Graph Laplacian Pseudoinverse | Mathematical foundation | Enables effective resistance computation | Use randomized SVD for large networks | ||
| Fast Resistance Calculators | Algorithmic tool | Approximates RPD in O( | E | ) time | Essential for large-scale temporal analysis |
| Synthetic Network Generators | Validation resource | Creates benchmark networks with controlled perturbations | Implement G(n,p), BA, SBM models | ||
| Dynamic Network Datasets | Experimental substrate | Provides real-world validation contexts | Social, biological, technological networks | ||
| Metric Comparison Framework | Evaluation system | Benchmarks RPD against alternatives | Include 5+ metric types for comprehensive comparison |
Advanced Applications in Robustness Evaluation
Robustness Optimization in Network Design
Beyond mere quantification of changes, RPD provides a foundation for optimizing network robustness. Research has demonstrated fast algorithms to increase network robustness by optimally decreasing the Kirchhoff index [95]. The optimization process can be visualized as follows:
Network Robustness Optimization Using RPD
Integration with Emerging Network Analysis Frameworks
The RPD metric aligns with broader mathematical frameworks for network dynamics, particularly within the "six-pillar" survey methodology that encompasses spectral foundations, control theory, adaptive networks, and probabilistic inference [98]. This integration positions RPD as part of a comprehensive toolkit for analyzing, controlling, and inferring dynamic behavior in complex networks.
Recent advances have explored connections between resistance distance and fractional calculus approaches to network dynamics [99], suggesting promising directions for enhancing RPD's theoretical foundations and applications to networks with memory and anomalous diffusion processes.
The Resistance Perturbation Distance represents a significant advancement in quantifying organizational changes in evolving networks, with particular value for evaluating architectural robustness across multiple scales. Its mathematical foundation in spectral graph theory, computational efficiency through randomized algorithms, and demonstrated sensitivity to both local and global structural changes make it particularly suitable for analyzing dynamic networks in biological, social, and technological contexts.
Experimental validations confirm that RPD outperforms many alternative metrics in capturing meaningful structural evolution while maintaining computational tractability for large-scale networks. As network robustness becomes increasingly critical in domains from drug development to infrastructure design, RPD provides researchers with a powerful analytical tool for quantifying, comparing, and optimizing resilience to structural perturbations.
The integration of artificial intelligence (AI) into drug discovery represents a paradigm shift, offering the potential to significantly reduce the time and cost associated with bringing new therapeutics to market. A critical yet underexplored frontier lies in understanding how the computational robustness of AI models—their resistance to perturbations and performance stability on diverse data—translates to tangible success in predicting viable clinical candidates. Within the broader thesis of evaluating network architecture robustness, this review investigates the correlation between a model's resilience to adversarial challenges and its accuracy in forecasting biomedical outcomes. As AI-driven pipelines increasingly advance compounds into clinical trials [100], discerning the architectural features that confer both predictive power and stability becomes paramount for building reliable, high-impact drug discovery tools.
Computational Robustness in Biomedical AI: Frameworks and Challenges
In the context of AI for drug discovery, computational robustness refers to a model's ability to maintain predictive performance when faced with input data that is noisy, incomplete, or deliberately perturbed. The architecture of a deep neural network (DNN) is a primary determinant of its robustness.
The Adversarial Robustness-Depth Paradox in Non-Biomedical Domains
Research in other domains, such as network intrusion detection, provides foundational insights into the relationship between network depth and robustness. One systematic study compared fully-connected DNNs of increasing depth (1 to 5 hidden layers) for intrusion detection, assessing their vulnerability to the Fast Gradient Sign Method (FGSM) adversarial attack. The key finding was a negative correlation between depth and robustness in this specific domain; deeper networks suffered more significant performance degradation under attack, suggesting that added layers did not improve—and in fact degraded—their defensive capabilities [101]. This contrasts with computer vision, where increased depth often yields more modest impacts on robustness, highlighting the domain-specific nature of these relationships [101].
Unique Adversarial Challenges in Biomedical Data
Biomedical data, particularly for drug discovery, presents unique robustness challenges. Adversarial perturbations must respect biological constraints, such as maintaining valid molecular structures or preserving network protocol integrity, moving beyond simple visual imperceptibility [101]. Furthermore, the "missing-modality" problem is a critical robustness challenge in biomedicine. Real-world preclinical and clinical data is often heterogeneous and incomplete [102]. Models that assume complete input data during training and inference fail in practical settings, disproportionately affecting novel compounds with sparse annotation [102]. Therefore, robustness in this field necessitates not only stability against small input perturbations but also an ability to perform reliably with inherently incomplete data profiles.
Architectural Approaches for Robust Clinical Prediction
Different AI architectures offer distinct strategies for achieving robustness in predicting clinical outcomes. The transition from single-modality to multimodal and hybrid approaches represents the cutting edge of this field.
Multimodal Integration with Attention Mechanisms
The Madrigal framework exemplifies a robust, multimodal approach designed to handle the missing-data problem. It integrates four data modalities—drug structure, biological pathways, cell viability, and transcriptomic responses—to predict clinical outcomes of drug combinations, including adverse events [102].
- Robustness Core - Attention Bottleneck: Madrigal uses an attention bottleneck module to unify the different preclinical drug data modalities. This architecture is specifically designed to handle missing data during both training and inference, a common scenario in real-world drug development [102].
- Contrastive Learning for Alignment: The model employs contrastive learning to anchor all modality-specific embeddings to the universally available structural data, creating a unified latent representation. This ensures predictive performance is maintained even when some modalities are absent at inference time [102].
In rigorous benchmarks, Madrigal demonstrated strong performance under challenging "split-by-drugs" settings, which tests a model's ability to generalize to novel compounds. It consistently outperformed state-of-the-art single-modality models (e.g., DeepDDI, CASTER) and other multimodal approaches (e.g., MUFFIN) in predicting adverse drug interactions, demonstrating the robustness conferred by its architectural design [102].
Hybrid Quantum-Classical Architectures
Emerging hybrid models combine generative AI with quantum computing to enhance the exploration of chemical space. In a 2025 case study targeting the difficult oncology target KRAS-G12D, a quantum-classical pipeline combined Quantum Circuit Born Machines (QCBMs) with deep learning. This hybrid approach screened 100 million molecules and yielded a compound with a binding affinity of 1.4 μM, demonstrating the potential of novel computational architectures to tackle biologically complex problems [103]. The hybrid quantum-classical model demonstrated a 21.5% improvement in filtering out non-viable molecules compared to AI-only models, suggesting that quantum computing can enhance robustness through better probabilistic modeling and increased molecular diversity [103].
Quantitative Comparison of Architectures and Clinical Pipelines
The performance of various AI-driven drug discovery approaches can be quantitatively assessed based on their hit rates, computational efficiency, and clinical pipeline success.
Performance Metrics of AI-Driven Drug Discovery
Table 1: Comparison of Drug Discovery Approach Performance Metrics
| Approach | Generated Compounds | Screened Candidates | Experimental Hit Rate | Key Strengths |
|---|---|---|---|---|
| Traditional HTS [103] | Millions (physical library) | 10,000+ | ~0.1% | Experimental readout from start |
| Generative AI (GALILEO) [103] | 52 trillion | 12 | 100% (12/12) | Unprecedented hit rate, high specificity |
| Quantum-Hybrid (KRAS Case) [103] | 100 million | 15 | ~13% (2/15) | Effective on difficult targets |
AI-Accelerated Clinical Pipelines
A survey of clinical-stage assets from AI-driven biotech companies reveals the tangible output of these computational platforms. As of 2024-2025, multiple AI-derived candidates have progressed into Phase I, II, and III trials for conditions ranging from oncology to neurological disorders [100].
Table 2: Selected AI-Derived Drug Candidates in Clinical Development
| Company | Pipeline Drug | Indication | Clinical Phase (Latest Update) | ClinicalTrials.gov Identifier |
|---|---|---|---|---|
| Recursion | REC4881 | Familial adenomatous polyposis | Phase I (2025) | NCT05552755 [100] |
| Recursion | REC2282 | Neurofibromatosis type 2 | Phase II/III (2024) | NCT05130866 [100] |
| Lantern | LP100 | mCRPC | Phase II (2025) | NCT03643107 [100] |
| Relay | RLY4008 | FGFR2 | Phase I (2025) | NCT04526106 [100] |
| AI Therapeutics | LAM-002A | Amyotrophic lateral sclerosis | Phase II (2024) | NCT05163886 [100] |
Experimental Protocols for Benchmarking Robustness
To objectively correlate robustness with clinical success, standardized experimental protocols and benchmarks are essential.
Protocol 1: Split-by-Drugs Benchmarking
This protocol tests a model's ability to generalize to entirely new chemical entities, a key measure of robustness for novel drug discovery [102].
- Data Partitioning: All data related to a held-out set of drugs—including all their combinations with any other drug—is removed from the training set to form the test set.
- Hard Variants:
- Split-by-Drugs (Target): Ensure test drugs share minimal therapeutic targets with training drugs.
- Split-by-Drugs (ATC): Exclude all drugs from specific first-level Anatomical Therapeutic Chemical (ATC) categories during training.
- Evaluation: Models are evaluated on the held-out set using Area Under the Receiver Operating Characteristic Curve (AUROC), Area Under the Precision-Recall Curve (AUPRC), and Maximum F measure (Fmax). The model's input during testing is restricted to modalities typically available for preclinical novel compounds to simulate real-world constraints [102].
Protocol 2: Adversarial Attack Susceptibility
This protocol evaluates model stability against deliberate input perturbations, adapted from computer vision and NIDS research [101] [41].
- Attack Method: Use the Fast Gradient Sign Method (FGSM) or Projected Gradient Descent (PGD) to generate adversarial examples.
- Perturbation Constraint: For a given input
x, the adversarial examplex_advis generated as:x_adv = x + ε * sign(∇xJ(θ, x, y)), whereεis the perturbation magnitude controlling attack strength [101]. - Biomedical Feature Constraints: Perturbations must respect biological plausibility (e.g., maintain valid molecular structures, preserve network protocol integrity) [101].
- Evaluation: Measure the degradation in performance metrics (e.g., accuracy, F1-score) on the adversarial examples compared to the clean test data. More robust models show smaller performance drops.
Protocol 3: TrialBench Clinical Trial Prediction Tasks
The TrialBench suite provides 23 AI-ready datasets for 8 clinical trial prediction challenges, offering a direct link to clinical outcomes [104].
- Task Selection: Choose tasks relevant to clinical candidate success, such as:
- Trial Approval Prediction: Binary classification of whether a drug will pass a clinical trial phase.
- Adverse Event Prediction: Binary classification of adverse event occurrence based on trial features.
- Patient Dropout Prediction: Predicting the occurrence and rate of patient dropout [104].
- Input Features: Models must process multi-modal input features, including drug molecules (as graphs), target diseases, and free-text eligibility criteria.
- Evaluation: Models are benchmarked on task-specific metrics (e.g., AUROC for classification) against provided baseline models, testing their ability to utilize diverse data for clinically critical predictions [104].
Visualization of Workflows and Architectures
Multimodal AI Model for Clinical Outcome Prediction
This diagram illustrates the architecture of a robust multimodal AI model (e.g., Madrigal) designed to handle missing data and predict clinical outcomes for drug combinations [102].
Robustness Benchmarking Experimental Workflow
This diagram outlines the core experimental workflow for benchmarking the robustness of AI models in drug discovery, incorporating key protocols from the field [102] [104].
Building and evaluating robust AI models for clinical candidate prediction requires a suite of specialized data resources, software tools, and benchmarking platforms.
Table 3: Essential Research Reagents and Resources for Robust AI Drug Discovery
| Resource Name | Type | Primary Function | Relevance to Robustness |
|---|---|---|---|
| TrialBench [104] | Datasets & Benchmarks | Suite of 23 AI-ready datasets for 8 clinical trial prediction tasks (e.g., approval, adverse events). | Provides standardized tasks to directly test model correlation with clinical outcomes. |
| DrugBank [102] [104] | Database | Curated repository containing drug structures, mechanisms, and pharmaceutical properties. | Source of multimodal features (e.g., molecular structures) for training and evaluation. |
| TWOSIDES [102] | Dataset | Resource of drug-drug interactions and side effects, derived from the FDA Adverse Event Reporting System (FAERS). | Critical for training and benchmarking models on predicting clinical adverse outcomes. |
| CSE-CIC-IDS2018 [101] | Dataset | Benchmark dataset for Network Intrusion Detection Systems (NIDS). | Used in robustness research to study the effect of DNN depth on adversarial attack susceptibility. |
| Fast Gradient Sign Method (FGSM) [101] [41] | Algorithm | A foundational white-box adversarial attack method for generating perturbations. | Standard tool for stress-testing model stability and evaluating adversarial robustness. |
| Attention Bottleneck Module [102] | Architectural Component | A fusion module for multimodal data that regulates information flow. | Core component for building models robust to missing input modalities. |
The correlation between computational robustness and successful clinical candidate prediction is a critical determinant for the future of AI-driven drug discovery. Evidence suggests that architectural choices—such as employing multimodal frameworks with attention mechanisms to handle missing data, or exploring hybrid quantum-classical pipelines for complex target exploration—directly influence a model's ability to generate generalizable and reliable predictions that translate to the clinic. Robustness is not merely a computational metric; it is a prerequisite for biomedical relevance. As the field matures, standardized benchmarking protocols, such as the "split-by-drugs" evaluation and the use of clinical-focused suites like TrialBench, will be indispensable for quantitatively linking model stability to therapeutic success, ultimately accelerating the development of safer and more effective medicines.
Conclusion
The evaluation of network robustness is a multifaceted discipline essential for designing reliable systems in biomedical research. Foundational principles of attack tolerance and metrics like effective graph resistance provide the theoretical bedrock. Methodologically, the integration of evolutionary algorithms with machine learning, particularly CNNs and advanced certification methods for GCNs, offers powerful, scalable tools for analysis and optimization. Troubleshooting must focus on critical vulnerabilities and practical limits, ensuring strategies are not just theoretically sound but also implementable. Finally, rigorous comparative validation against benchmarks and real-world biomedical platforms confirms that robust network architectures directly contribute to increased efficiency and success rates in drug discovery. Future directions should prioritize the development of explainable, ethically aligned AI systems that are inherently robust, generalizable across diverse biological networks, and capable of accelerating the translation of computational predictions into viable clinical therapies.
References
- 1. Comprehensive analysis of network robustness evaluation ... [https://www.sciencedirect.com/science/article/abs/pii/S0960077924005757]
- 2. Integrating the functions and structures to assess ... [https://link.springer.com/article/10.1007/s10980-024-01799-y]
- 3. Robustness of 'small' networks [https://arxiv.org/html/2509.23670v1]
- 4. Network inference from perturbation time course data [https://www.nature.com/articles/s41540-022-00253-6]
- 5. Network Analysis of Gene Perturbation Screens [https://pmc.ncbi.nlm.nih.gov/articles/PMC2829042/]
- 6. Effective graph resistance [https://www.johndcook.com/blog/2025/05/21/effective-graph-resistance/]
- 7. Greedy optimization of resistance-based graph robustness ... [https://link.springer.com/article/10.1007/s13278-023-01137-1]
- 8. On the Robustness of Complex Networks by Using ... [https://link.springer.com/chapter/10.1007/978-3-540-79549-0_16]
- 9. Extremal properties and bounds for the generalized ... [https://www.sciencedirect.com/science/article/abs/pii/S0024379525003192]
- 10. Robustness surfaces of complex networks | Scientific Reports [https://www.nature.com/articles/srep06133]
- 11. Study on the robust control of higher-order networks [https://www.nature.com/articles/s41598-025-91842-y]
- 12. The Top AI Security Risks Facing Enterprises in 2025 [https://www.obsidiansecurity.com/blog/ai-security-risks]
- 13. Cascading failure modeling and survivability analysis of ... [https://www.sciencedirect.com/science/article/pii/S2214914725002958]
- 14. A large-scale benchmark for network inference from single- ... [https://www.nature.com/articles/s42003-025-07764-y]
- 15. An Empirical Study on the Effect of Training Data ... [https://www.mdpi.com/1424-8220/24/15/4874]
- 16. Robustness Distributions in Neural Network Verification [https://www.jair.org/index.php/jair/article/view/18403]
- 17. Network Robustness Revisited [https://www.frontiersin.org/journals/physics/articles/10.3389/fphy.2022.823564/full]
- 18. Scale-free networks are rare - PMC - NIH [https://pmc.ncbi.nlm.nih.gov/articles/PMC6399239/]
- 19. Enhancing structural robustness of scale-free networks by ... [https://www.nature.com/articles/s41598-017-07878-2]
- 20. Towards Enhancing the Robustness of Scale-Free IoT ... [https://www.mdpi.com/1424-8220/22/7/2658]
- 21. Modularity affects the robustness of scale-free model and real ... [https://appliednetsci.springeropen.com/articles/10.1007/s41109-021-00426-y]
- 22. True scale-free networks hidden by finite size effects - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC7812829/]
- 23. Scale-Free Networks beyond Power-Law Degree Distribution [https://arxiv.org/abs/2310.08110]
- 24. [1504.00618] Robustness of scale-free spatial networks [https://arxiv.org/abs/1504.00618]
- 25. Robustness and Specificity in Signal Transduction via ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC3923534/]
- 26. tests for Robustness foundation models should tailor to... biomedical [https://www.nature.com/articles/s41746-025-01926-2?error=cookies_not_supported&code=aeb2c45c-8072-4b44-8a7e-1756a1130228]
- 27. tests for Robustness foundation models should tailor to... biomedical [https://arxiv.org/html/2502.10374v3]
- 28. GraphDTI: A robust deep learning predictor of drug-target ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8356453/]
- 29. A multi-objective evolutionary algorithm for detecting ... [https://www.nature.com/articles/s41598-025-01667-y]
- 30. Benchmarking retrieval-augmented large language models in... [https://pubmed.ncbi.nlm.nih.gov/41270181/]
- 31. an Adversarial Robustness Measurement Framework [https://arxiv.org/html/2504.17723v1]
- 32. Understanding Success Criterion 1.4.11: Non-text Contrast [https://www.w3.org/WAI/WCAG21/Understanding/non-text-contrast.html]
- 33. Enhancing robustness of higher-order networks with ... [https://www.sciencedirect.com/science/article/abs/pii/S0960077925014122]
- 34. Link-limited bypass rewiring for enhancing the robustness of ... [https://appliednetsci.springeropen.com/articles/10.1007/s41109-024-00624-4]
- 35. Trust in Adversarial Robustness Tests [https://arxiv.org/html/2507.03450v1]
- 36. A positive statistical benchmark to assess network agreement [https://www.nature.com/articles/s41467-023-38625-z]
- 37. Comparative evaluation of strategies for improving the ... [https://appliednetsci.springeropen.com/articles/10.1007/s41109-023-00569-0]
- 38. Paddy: an evolutionary optimization algorithm for chemical ... [https://pubs.rsc.org/en/content/articlehtml/2025/dd/d4dd00226a]
- 39. Towards evaluating the robustness of deep diagnostic ... [https://www.sciencedirect.com/science/article/abs/pii/S1361841521000232]
- 40. An Empirical Study on the Effect of Training Data ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11314775/]
- 41. Analyzing the Adversarial Robustness and Interpretability ... [https://www.mdpi.com/2072-4292/17/11/1943]
- 42. A comparative analysis of machine learning techniques for ... [https://www.sciencedirect.com/science/article/abs/pii/S0957417425003409]
- 43. Incremental measurement of structural entropy for dynamic ... [https://www.sciencedirect.com/science/article/abs/pii/S0004370224001115]
- 44. An incremental adversarial training method enables ... [https://www.nature.com/articles/s41598-025-19840-8]
- 45. An incremental adversarial training method enables ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12521521/]
- 46. Incremental Data-Driven Policy Synthesis via Game ... [https://arxiv.org/html/2511.11545v1]
- 47. Understanding the robustness of graph neural networks ... [https://www.sciencedirect.com/science/article/abs/pii/S0950705125007609]
- 48. Adversarial Training for Graph Convolutional Networks [https://www.ijcai.org/proceedings/2025/534]
- 49. Provably Robust Explainable Graph Neural Networks ... [https://arxiv.org/html/2502.04224v1]
- 50. Graph convolution network based on meta-paths and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12595897/]
- 51. A Survey of Graph Neural Networks for Drug Discovery [https://arxiv.org/html/2509.07887v1]
- 52. Drug discovery and mechanism prediction with explainable ... [https://www.nature.com/articles/s41598-024-83090-3]
- 53. Network Robustness Analysis Based on Maximum Flow [https://www.frontiersin.org/journals/physics/articles/10.3389/fphy.2021.792410/full]
- 54. Analyzing the Robustness of Complex Networks with Attack ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10669974/]
- 55. [2509.23670] Robustness of 'small' networks [https://arxiv.org/abs/2509.23670]
- 56. A small set of critical hyper-motifs governs heterogeneous ... [https://www.nature.com/articles/s41467-025-63001-4]
- 57. Certifying Robustness of Graph Convolutional Networks for ... [https://arxiv.org/abs/2405.08645]
- 58. Certifying Robustness of Graph Convolutional Networks for ... [https://arxiv.org/html/2405.08645v1]
- 59. Can Large Language Models Improve the Adversarial ... [https://arxiv.org/html/2408.08685v3]
- 60. Automatically optimizing heuristics for robust scale-free ... [https://www.nature.com/articles/s41598-025-25031-2]
- 61. scSpecies: enhancement of network architecture alignment in ... [https://genomebiology.biomedcentral.com/articles/10.1186/s13059-025-03866-2]
- 62. Letter Analytics solution for the robustness of incomplete ... [https://www.sciencedirect.com/science/article/pii/S037596012500903X]
- 63. Assessing the Robustness and Reducibility of Multiplex ... [https://arxiv.org/html/2505.06998v1]
- 64. On the Probabilistic Nature of Perturbation Robustness [https://arxiv.org/html/2508.19183v1]
- 65. Probabilistically Robust Recourse: Navigating the Trade ... [https://www.hbs.edu/faculty/Pages/item.aspx?num=63576]
- 66. Violations of robustness trade-offs - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC2913402/]
- 67. A fair experimental comparison of neural network ... [https://bmcbioinformatics.biomedcentral.com/articles/10.1186/s12859-023-05166-7]
- 68. On the Probabilistic Nature of Perturbation Robustness [https://arxiv.org/abs/2508.19183]
- 69. Provably Robust Explainable Graph Neural Networks ... [https://openreview.net/forum?id=iFK0xoceR0]
- 70. NetBench: A Large-Scale and Comprehensive Network ... [https://arxiv.org/abs/2403.10319]
- 71. Critical role of data quality in enabling AI in R&D [https://www.deloitte.com/uk/en/blogs/thoughts-from-the-centre/critical-role-of-data-quality-in-enabling-ai-in-r-d.html]
- 72. AI in Pharma and Biotech: Market Trends 2025 and Beyond [https://www.coherentsolutions.com/insights/artificial-intelligence-in-pharmaceuticals-and-biotechnology-current-trends-and-innovations]
- 73. A scoping review of robustness concepts for machine ... [https://www.nature.com/articles/s41746-024-01420-1]
- 74. Robustness in deep learning models for medical diagnostics [https://link.springer.com/article/10.1007/s10462-024-11005-9]
- 75. The Role of AI in Drug Discovery: Challenges, Opportunities ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10302890/]
- 76. The Impact of AI and Data Analytics in Pharma Research [https://intglobal.com/blogs/the-impact-of-ai-and-data-analytics-in-pharma-research-2/]
- 77. A roadmap for robust and trustworthy medical AI [https://www.the-innovation.org/article/doi/10.59717/j.xinn-med.2025.100145]
- 78. Comprehensive Analysis of Network Robustness ... [https://arxiv.org/html/2308.08012v3]
- 79. Synthetic Networks That Preserve Edge Connectivity [https://arxiv.org/html/2408.13647v1]
- 80. Benchmarking robustness of deep neural networks in ... [https://bmcbioinformatics.biomedcentral.com/articles/10.1186/s12859-024-05894-4]
- 81. A comparative analysis of network robustness against ... [https://www.sciencedirect.com/science/article/abs/pii/S0378437115010730]
- 82. A comparative study of network robustness measures [https://link.springer.com/article/10.1007/s11704-016-6108-z]
- 83. ImageNet-D: Benchmarking Neural Network Robustness ... [https://arxiv.org/abs/2403.18775]
- 84. Benchmarking the Robustness of Instance Segmentation ... [https://arxiv.org/abs/2109.01123]
- 85. BERT vs GPT vs LLaMA: AI Model Comparison 2025 [https://www.byteplus.com/en/topic/560409]
- 86. BERT vs GPT: The Ultimate AI Model Showdown [https://blog.udemy.com/bert-vs-gpt/]
- 87. Transformer Models Compared: BERT vs GPT vs T5 Guide [https://www.devstree.com/transformer-models-use-case-guide-bert-gpt-t5/]
- 88. GPT-4 vs BERT: Comparing Two Leading Language Models [https://www.zignuts.com/blog/gpt4-vs-bert]
- 89. Isometric representations in neural networks improve ... [https://www.nature.com/articles/s41598-025-20619-0]
- 90. Leading AI-Driven Drug Discovery Platforms [https://www.sciencedirect.com/science/article/abs/pii/S0031699725075118]
- 91. Recent advances in molecular representation methods and ... [https://www.nature.com/articles/s44386-025-00017-2]
- 92. A Survey of Graph Transformers: Architectures, Theories ... [https://arxiv.org/html/2502.16533v2]
- 93. Benchmark on Drug Target Interaction Modeling from a ... [https://arxiv.org/html/2407.04055v2]
- 94. AlphaFold3: An Overview of Applications and Performance ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12027460/]
- 95. A Metric for the Analysis of Dynamic Networks [https://arxiv.org/abs/1605.01091]
- 96. Analytical study of resistance distance and Kirchhoff index [https://ideas.repec.org/a/eee/chsofr/v199y2025ip3s0960077925009105.html]
- 97. Models of similarity in complex networks - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC10280390/]
- 98. Mathematical Frameworks for Network Dynamics: A Six ... [https://www.mdpi.com/2227-7390/13/13/2116]
- 99. Predictive modeling of complex networks using deep ... [https://www.aimspress.com/article/doi/10.3934/math.20251175]
- 100. The future of pharmaceuticals: Artificial intelligence in drug ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12391800/]
- 101. Exploring the Effect of DNN Depth on Adversarial Attacks in ... [https://arxiv.org/html/2510.19761v1]
- 102. Multimodal AI predicts clinical outcomes of drug ... [https://arxiv.org/html/2503.02781v2]
- 103. The Future of Drug Discovery: 2025 as the Inflection Year ... [https://modelmedicines.com/newsroom/the-future-of-drug-discovery-2025-as-the-inflection-year-for-hybrid-ai-and-quantum-computing]
- 104. TrialBench: Multi-Modal AI-Ready Datasets for Clinical ... [https://www.nature.com/articles/s41597-025-05680-8]